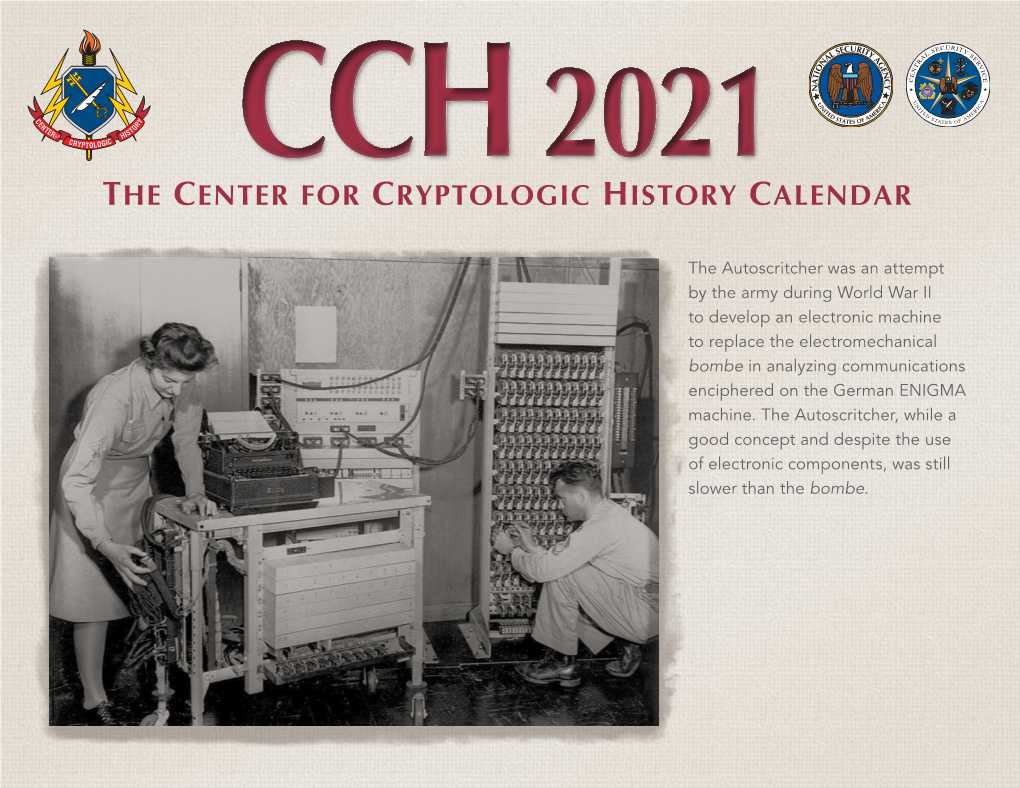
The Center for Cryptologic History Calendar
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Georgetown University in Partial Fulfillment of the Requirements for the Degree of Master of Arts in Security Studies
THE BATTLE FOR INTELLIGENCE: HOW A NEW UNDERSTANDING OF INTELLIGENCE ILLUMINATES VICTORY AND DEFEAT IN WORLD WAR II A Thesis submitted to the Faculty of the Graduate School of Arts and Sciences of Georgetown University in partial fulfillment of the requirements for the degree of Master of Arts in Security Studies By Edward J. Piotrowicz III, B.A. Washington, DC April 15, 2011 Copyright 2011 by Edward J. Piotrowicz III All Rights Reserved ii THE BATTLE FOR INTELLIGENCE: HOW A NEW UNDERSTANDING OF INTELLIGENCE ILLUMINATES VICTORY AND DEFEAT IN WORLD WAR II Edward J. Piotrowicz III, B.A. Thesis Advisor: Jennifer E. Sims, PhD. ABSTRACT Does intelligence make a difference in war? Two World War II battles provide testing grounds for answering this question. Allied intelligence predicted enemy attacks at both Midway and Crete with uncanny accuracy, but the first battle ended in an Allied victory, while the second finished with crushing defeat. A new theory of intelligence called “Decision Advantage,”a illuminates how the success of intelligence helped facilitate victory at Midway and how its dysfunction contributed to the defeat at Crete. This view stands in contrast to that of some military and intelligence scholars who argue that intelligence has little impact on battle. This paper uses the battles of Midway and Crete to test the power of Sims‟s theory of intelligence. By the theory‟s standards, intelligence in the case of victory outperformed intelligence in the case of defeat, suggesting these cases uphold the explanatory power of the theory. Further research, however, could enhance the theory‟s prescriptive power. -

The Moorer Commission
The Moorer Commission 1 Findings of the Independent Commission of Inquiry into the Israeli Attack on USS Liberty, the Recall of Military Rescue Support Aircraft while the Ship was Under Attack, and the Subsequent Cover - up by the United States Government October 22, 2003 Admiral Thomas H. Moorer, U.S. Navy (deceased) Former Chairman, Joint Chiefs of Staff General Raymond G. Davis, U.S. Marine Corps (deceased) (MOH)*, Former Assistant Commandant of the Marine Corps Rear Admiral Merlin Staring, U.S. Navy (deceased) Former Judge Advocate of the Navy (73 - 75) Ambassador James Akins (deceased) Former U.S. Ambassador to Saudi Arabia (73 - 76) We, the undersigned having undertaken an independent investigation of Israel’s attack on USS Liberty , including eyewit ness testimony from surviving crewmembers, a review of naval and other official records, an examination of official statements by the Israeli and American governments, a study of the conclusions of all previous official inquiries, and a consideration of im portant new evidence and recent statements from individuals having direct knowledge of the attack or the cover up, hereby find the following:** 1. That on June 8, 1967, after eight hours of aerial surveillance, Israel launched a two - hour air and naval attack against USS Liberty, the world’s most sophisticated intelligence ship, inflicting 34 dead, and 173 wounded American servicemen (a casualty rate of 70%, in a crew of 294).; 2 2. That the Israeli air attack lasted approximately 25 minutes, during which time un marked Israeli aircraft dropped napalm canisters on USS Liberty’s bridge, and fired 30mm cannons and rockets into our ship, causing 821 holes, more than 100 of which were rocket - size; survivors estimate 30 or more sorties were flown over the ship by minimu m of 12 attacking Israeli planes which were jamming all 5 American emergency radio channels; 3. -

Deception, Disinformation, and Strategic Communications: How One Interagency Group Made a Major Difference by Fletcher Schoen and Christopher J
STRATEGIC PERSPECTIVES 11 Deception, Disinformation, and Strategic Communications: How One Interagency Group Made a Major Difference by Fletcher Schoen and Christopher J. Lamb Center for Strategic Research Institute for National Strategic Studies National Defense University Institute for National Strategic Studies National Defense University The Institute for National Strategic Studies (INSS) is National Defense University’s (NDU’s) dedicated research arm. INSS includes the Center for Strategic Research, Center for Complex Operations, Center for the Study of Chinese Military Affairs, Center for Technology and National Security Policy, Center for Transatlantic Security Studies, and Conflict Records Research Center. The military and civilian analysts and staff who comprise INSS and its subcomponents execute their mission by conducting research and analysis, publishing, and participating in conferences, policy support, and outreach. The mission of INSS is to conduct strategic studies for the Secretary of Defense, Chairman of the Joint Chiefs of Staff, and the Unified Combatant Commands in support of the academic programs at NDU and to perform outreach to other U.S. Government agencies and the broader national security community. Cover: Kathleen Bailey presents evidence of forgeries to the press corps. Credit: The Washington Times Deception, Disinformation, and Strategic Communications: How One Interagency Group Made a Major Difference Deception, Disinformation, and Strategic Communications: How One Interagency Group Made a Major Difference By Fletcher Schoen and Christopher J. Lamb Institute for National Strategic Studies Strategic Perspectives, No. 11 Series Editor: Nicholas Rostow National Defense University Press Washington, D.C. June 2012 Opinions, conclusions, and recommendations expressed or implied within are solely those of the contributors and do not necessarily represent the views of the Defense Department or any other agency of the Federal Government. -
THE-POLISH-TRACE-Ebook.Pdf
8 THE POLISH TRACE COMPOSED FROM COMMONLY AVAILABLE SOURCES BY LECH POLKOWSKI FOR IJCRS2017 FOREWORD It is a desire of many participants of conferences to learn as much as possible about the history and culture of he visited country and place and organizers try to satisfy this desire by providing excursions into attractive places and sites. IJCRS2017 also tries to take participants to historic sites of Warmia and Mazury and to show elements of local culture. As an innovation, we propose a booklet showing some achievements of Polish scientists and cryptographers, no doubt many of them are known universally, but some probably not. What bounds all personages described here is that they all suffered due to world wars, th efirst and the second. These wars ruined their homes, made them refugees and exiles, destroyed their archives and libraries, they lost many colleagues, friends and students but were lucky enough to save lives and in some cases to begin the career overseas. We begin with the person of Jan Czochralski, world famous metallurgist, discoverer of the technique of producing metal monocrystals `the Czochralski methode’ and inventor of duraluminum and the `bahnalloy’ who started his career and obtained its heights in Germany, later returned to Poland, became a professor at the Warsaw Polytechnical, played an important role in cultural life of Warsaw, lived in Warsaw through the second world war and the Warsaw Uprising of August-September 1944 and after the war was accused of cooperating ith occupying German forces and though judged innocent was literally erased from the public life and any information about him obliterated. -

Polska Myśl Techniczna W Ii Wojnie Światowej
CENTRALNA BIBLIOTEKA WOJSKOWA IM. MARSZAŁKA JÓZEFA PIŁSUDSKIEGO POLSKA MYŚL TECHNICZNA W II WOJNIE ŚWIATOWEJ W 70. ROCZNICĘ ZAKOŃCZENIA DZIAŁAŃ WOJENNYCH W EUROPIE MATERIAŁY POKONFERENCYJNE poD REDAkcJą NAUkoWą DR. JANA TARCZYńSkiEGO WARSZAWA 2015 Konferencja naukowa Polska myśl techniczna w II wojnie światowej. W 70. rocznicę zakończenia działań wojennych w Europie Komitet naukowy: inż. Krzysztof Barbarski – Prezes Instytutu Polskiego i Muzeum im. gen. Sikorskiego w Londynie dr inż. Leszek Bogdan – Dyrektor Wojskowego Instytutu Techniki Inżynieryjnej im. profesora Józefa Kosackiego mgr inż. Piotr Dudek – Prezes Stowarzyszenia Techników Polskich w Wielkiej Brytanii gen. dyw. prof. dr hab. inż. Zygmunt Mierczyk – Rektor-Komendant Wojskowej Akademii Technicznej im. Jarosława Dąbrowskiego płk mgr inż. Marek Malawski – Szef Inspektoratu Implementacji Innowacyjnych Technologii Obronnych Ministerstwa Obrony Narodowej mgr inż. Ewa Mańkiewicz-Cudny – Prezes Federacji Stowarzyszeń Naukowo-Technicznych – Naczelnej Organizacji Technicznej prof. dr hab. Bolesław Orłowski – Honorowy Członek – założyciel Polskiego Towarzystwa Historii Techniki – Instytut Historii Nauki Polskiej Akademii Nauk kmdr prof. dr hab. Tomasz Szubrycht – Rektor-Komendant Akademii Marynarki Wojennej im. Bohaterów Westerplatte dr Jan Tarczyński – Dyrektor Centralnej Biblioteki Wojskowej im. Marszałka Józefa Piłsudskiego prof. dr hab. Leszek Zasztowt – Dyrektor Instytutu Historii Nauki Polskiej Akademii Nauk dr Czesław Andrzej Żak – Dyrektor Centralnego Archiwum Wojskowego im. -

Historical Ciphers • A
ECE 646 - Lecture 6 Required Reading • W. Stallings, Cryptography and Network Security, Chapter 2, Classical Encryption Techniques Historical Ciphers • A. Menezes et al., Handbook of Applied Cryptography, Chapter 7.3 Classical ciphers and historical development Why (not) to study historical ciphers? Secret Writing AGAINST FOR Steganography Cryptography (hidden messages) (encrypted messages) Not similar to Basic components became modern ciphers a part of modern ciphers Under special circumstances modern ciphers can be Substitution Transposition Long abandoned Ciphers reduced to historical ciphers Transformations (change the order Influence on world events of letters) Codes Substitution The only ciphers you Ciphers can break! (replace words) (replace letters) Selected world events affected by cryptology Mary, Queen of Scots 1586 - trial of Mary Queen of Scots - substitution cipher • Scottish Queen, a cousin of Elisabeth I of England • Forced to flee Scotland by uprising against 1917 - Zimmermann telegram, America enters World War I her and her husband • Treated as a candidate to the throne of England by many British Catholics unhappy about 1939-1945 Battle of England, Battle of Atlantic, D-day - a reign of Elisabeth I, a Protestant ENIGMA machine cipher • Imprisoned by Elisabeth for 19 years • Involved in several plots to assassinate Elisabeth 1944 – world’s first computer, Colossus - • Put on trial for treason by a court of about German Lorenz machine cipher 40 noblemen, including Catholics, after being implicated in the Babington Plot by her own 1950s – operation Venona – breaking ciphers of soviet spies letters sent from prison to her co-conspirators stealing secrets of the U.S. atomic bomb in the encrypted form – one-time pad 1 Mary, Queen of Scots – cont. -
Pioneers in U.S. Cryptology Ii
PIONEERS IN U.S. CRYPTOLOGY II This brochure was produced by the Center for Cryptologic History Herbert 0. Yardley 2 Herbert 0. Yardley Herbert 0 . Yardley was born in 1889 in Worthington, Indiana. After working as a railroad telegrapher and spending a year taking an English course at the University of Chicago, he became a code clerk for the Department of State. In June 1917, Yardley received a commission in the Signal Officers Reserve Corps; in July Colonel Ralph Van Deman appointed him chief of the new cryptanalytic unit, MI-8, in the Military Intelligence division. MI-8, or the Cipher Bureau, consisted of Yardley and two clerks. At MI-8's peak in November 1918, Yardley had 18 officers, 24 civilians, and 109 typists. The section had expanded to include secret inks, code and cipher compilation, communications, and shorthand. This was the first formally organized cryptanalytic unit in the history of the U.S. government. When World War I ended, the Army was considering disbanding MI-8. Yardley presented a persuasive argument for retaining it for peacetime use. His plan called for the permanent retention of a code and cipher organization funded jointly by the State and War Departments. He demonstrated that in the past eighteen months MI-8 had read almost 11,000 messages in 579 cryptographic systems. This was in addition to everything that had been examined in connection with postal censorship. On 17 May Acting Secretary of State Frank L. Polk approved the plan, and two days later the Army Chief of Staff, General Peyton C. -

Rochefort Vinse a Midway, Fu Sconfitto a Washington
StO ROCHEFORT VINSE A MIDWAY, FU SCONFITTO A WASHINGTON ALAIN CHARBONNIER «Si può raggiungere qualsiasi risultato, purché nessuno badi a chi va il merito», era scritto alle spalle del capitano di vascello Joseph J. Rochefort nel Dungeon, il seminterrato di Pearl Harbour, dove i decrittatori della stazione ‘Hypo’ che lavoravano sui codici della Marina giapponese misero l’ammiraglio Nimitz in grado di vincere a Midway. Ma c’era chi al merito badava, e come, e voleva appropriarsene. Rochefort era approdato alla crittoanalisi quando negli Stati Uniti era considerata quasi una stregoneria. Sedici anni dopo, nonostante i brillanti risultati, ne fu estromesso dai burocrati di Washington. «Un ex studente di giapponese non può comandare un centro dell’intelligence navale», dissero. La vittoria di Midway fu ascritta a suo merito soltanto nel 1985, nove anni dopo la morte. Impianto desalinizzazione in avaria. Riserva acqua potabile prevista in 14 giorni con razionamento. Provvedere rifornimento». Il 20 maggio 1942 il Comando della Marina americana a Pearl Harbour, nelle isole Hawaii, ricevette il messaggio ‘flash’ tramesso dalla guarnigione di Midway, un atollo distante quasi 2000 chilometri, da poco tempo rinforzata dal Comando del Pacifico. I centri d’ascolto giapponesi intercettarono la comunicazione e avvertirono il Co - mando Generale della Nihon Kaigun , la flotta imperiale, che ‘l’unità aerea AF’ aveva chiesto un immediato rifornimento idrico. Il messaggio giapponese, criptato nel codice JN-25, fu captato e decodificato anche dalla stazione ‘Hypo’, di Honolulu, alle Hawaii, dove il capitano di vascello Joseph J. Rochefort lo stava aspettando. Per lui era la conferma che la sigla ‘AF’ indicava Midway, come aveva intuito nelle settimane precedenti, quando si era delineata l’ipotesi che i Giapponesi stessero preparando una nuova offensiva. -
Corp Bro Inside Layout
Message from the Director, NSA The National Security Agency’s rich legacy of cryptologic success serves not only as a reminder of our past triumphs, but also as an inspiration for our future. Harry Truman, the man responsible for signing the legislation that brought our Agency into existence, was once quoted as saying, “There is nothing new in the world except the history you do not know.” Like all truisms, it is only partially accurate. Each generation of Americans must at some point deal with unforeseen problems and issues that transcend the status quo. Most would agree that the challenges faced by NSA in today’s war against terrorism are far different from those of World War II, Vietnam, or Desert Storm. Even so, President Truman was correct in his assertion that there is much to be learned from the past. The history of the National Security Agency has in many respects been based on and characterized by feats of intellectual brilliance. Pioneers like William Friedman, Frank Rowlett, Dr. Louis Tordella, and Agnes Meyer Driscoll, to name but a few, were able to build on past successes and do whatever was necessary to meet the challenges of their time. We should not forget, however, that NSA’s success is due not just to the efforts of the well- known legends of the cryptologic past, but also to the dedicated work of thousands of men and women whose names will never be noted in any history book. History tells us that both genius and hard work are required to ensure success. -

Breaking Japanese Diplomatic Codes David Sissons and D Special Section During the Second World War
Breaking Japanese Diplomatic Codes David Sissons and D Special Section during the Second World War Breaking Japanese Diplomatic Codes David Sissons and D Special Section during the Second World War Edited by Desmond Ball and Keiko Tamura ASIAN STUDIES SERIES MONOGRAPH 4 Published by ANU E Press The Australian National University Canberra ACT 0200, Australia Email: [email protected] This title is also available online at http://epress.anu.edu.au National Library of Australia Cataloguing-in-Publication entry Title: Breaking Japanese diplomatic codes : David Sissons and D Special Section during the Second World War / edited by Desmond Ball and Keiko Tamura. ISBN: 9781925021073 (paperback) 9781925021080 (ebook) Subjects: Sissons, D. C. S. (David Carlisle Stanley), 1925-2006. Allied Forces. Southwest Pacific Area. Allied Intelligence Bureau World War, 1939-1945--Cryptography. World War, 1939-1945--Secret service--Australia. World War, 1939-1945--Electronic intelligence--Australia. World War, 1939-1945--Military intelligence--Australia. World War, 1939-1945--Japan. Cryptography--Australia--History. Military intelligence--Australia--History--20th century. Other Authors/Contributors: Ball, Desmond, 1947- editor. Tamura, Keiko, editor. Dewey Number: 940.548694 All rights reserved. No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying or otherwise, without the prior permission of the publisher. Cover design and layout by ANU E Press Cover image: David Sissons about 18 years old before joining the Army in 1944. Photo courtesy of Mrs Bronwen Sissons. Printed by Griffin Press This edition © 2013 ANU E Press Contents Preface . ix Acknowledgements . xi Acronyms and Abbreviations . -

Considering the Creation of a Domestic Intelligence Agency in the United States
HOMELAND SECURITY PROGRAM and the INTELLIGENCE POLICY CENTER THE ARTS This PDF document was made available CHILD POLICY from www.rand.org as a public service of CIVIL JUSTICE the RAND Corporation. EDUCATION ENERGY AND ENVIRONMENT Jump down to document6 HEALTH AND HEALTH CARE INTERNATIONAL AFFAIRS The RAND Corporation is a nonprofit NATIONAL SECURITY research organization providing POPULATION AND AGING PUBLIC SAFETY objective analysis and effective SCIENCE AND TECHNOLOGY solutions that address the challenges SUBSTANCE ABUSE facing the public and private sectors TERRORISM AND HOMELAND SECURITY around the world. TRANSPORTATION AND INFRASTRUCTURE Support RAND WORKFORCE AND WORKPLACE Purchase this document Browse Books & Publications Make a charitable contribution For More Information Visit RAND at www.rand.org Explore the RAND Homeland Security Program RAND Intelligence Policy Center View document details Limited Electronic Distribution Rights This document and trademark(s) contained herein are protected by law as indicated in a notice appearing later in this work. This electronic representation of RAND intellectual property is provided for non-commercial use only. Unauthorized posting of RAND PDFs to a non-RAND Web site is prohibited. RAND PDFs are protected under copyright law. Permission is required from RAND to reproduce, or reuse in another form, any of our research documents for commercial use. For information on reprint and linking permissions, please see RAND Permissions. This product is part of the RAND Corporation monograph series. RAND monographs present major research findings that address the challenges facing the public and private sectors. All RAND mono- graphs undergo rigorous peer review to ensure high standards for research quality and objectivity. -

Polish Mathematicians Finding Patterns in Enigma Messages
Fall 2006 Chris Christensen MAT/CSC 483 Machine Ciphers Polyalphabetic ciphers are good ways to destroy the usefulness of frequency analysis. Implementation can be a problem, however. The key to a polyalphabetic cipher specifies the order of the ciphers that will be used during encryption. Ideally there would be as many ciphers as there are letters in the plaintext message and the ordering of the ciphers would be random – an one-time pad. More commonly, some rotation among a small number of ciphers is prescribed. But, rotating among a small number of ciphers leads to a period, which a cryptanalyst can exploit. Rotating among a “large” number of ciphers might work, but that is hard to do by hand – there is a high probability of encryption errors. Maybe, a machine. During World War II, all the Allied and Axis countries used machine ciphers. The United States had SIGABA, Britain had TypeX, Japan had “Purple,” and Germany (and Italy) had Enigma. SIGABA http://en.wikipedia.org/wiki/SIGABA 1 A TypeX machine at Bletchley Park. 2 From the 1920s until the 1970s, cryptology was dominated by machine ciphers. What the machine ciphers typically did was provide a mechanical way to rotate among a large number of ciphers. The rotation was not random, but the large number of ciphers that were available could prevent depth from occurring within messages and (if the machines were used properly) among messages. We will examine Enigma, which was broken by Polish mathematicians in the 1930s and by the British during World War II. The Japanese Purple machine, which was used to transmit diplomatic messages, was broken by William Friedman’s cryptanalysts.