Bumpy Road Towards Iphone 5C NAND Mirroring
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Neal Notes - Home
WEBINARS WHITEPAPERS SOLUTION CENTERS JOBS BOARD WHAT'S NEW EDUCATION NEWS MAGAZINES JOURNALS CONFERENCES SUBMISSIONS ABOUT HOME CLOUD BIG DATA MOBILE NETWORKING SECURITY SOFTWARE INSIGHTSINSIGHTS HOT TOPICS Neal Notes - Home Latest Posts Israeli Semiconductor Industry Continues to Thrive, but Some Clouds May Be on Horizon Neal Leavitt MAY 30, 2014 14:58 PM A- A A+ Back in 1974, Dov Frohman, one of Intel’s first employees and the inventor of EPROM, erasable programmable read only memory, decided to leave Silicon Valley and return to Israel, his adopted home since 1949. Frohman was charged with helping Intel establish a small chip design center in Haifa, which at the time, was Intel’s first outside the U.S. The rest, as the cliché goes, is history. In a little over a generation, the Israeli semiconductor industry has grown to now employ more than 20,000; annual revenues are about US $5 billion. Intel, for instance, now has about 9,900 employees in Israel and is planning to invest almost $6 billion in upgrading its Kiryat Gat fab facility. In fact, since 1974, Intel has invested about $10.8 billion in the Israeli semiconductor industry. “We’ve exported goods worth $35 billion most from our production centers in Kiryat Gat and Jerusalem,” said Intel VP and Intel Israel CEO Maxine Fassberg. Sol Gradman is editor of TapeOut, a publication covering the semiconductor industry, and also chairs ChipEx, the country’s largest annual semiconductor/microelectronics conference. Gradman said Israel’s semiconductor industry today comprises three types of companies – fabless, multinational design centers, and fabs. -
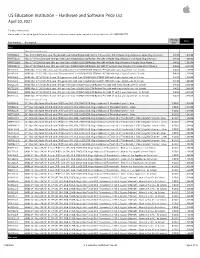
Apple US Education Price List
US Education Institution – Hardware and Software Price List April 30, 2021 For More Information: Please refer to the online Apple Store for Education Institutions: www.apple.com/education/pricelists or call 1-800-800-2775. Pricing Price Part Number Description Date iMac iMac with Intel processor MHK03LL/A iMac 21.5"/2.3GHz dual-core 7th-gen Intel Core i5/8GB/256GB SSD/Intel Iris Plus Graphics 640 w/Apple Magic Keyboard, Apple Magic Mouse 2 8/4/20 1,049.00 MXWT2LL/A iMac 27" 5K/3.1GHz 6-core 10th-gen Intel Core i5/8GB/256GB SSD/Radeon Pro 5300 w/Apple Magic Keyboard and Apple Magic Mouse 2 8/4/20 1,699.00 MXWU2LL/A iMac 27" 5K/3.3GHz 6-core 10th-gen Intel Core i5/8GB/512GB SSD/Radeon Pro 5300 w/Apple Magic Keyboard & Apple Magic Mouse 2 8/4/20 1,899.00 MXWV2LL/A iMac 27" 5K/3.8GHz 8-core 10th-gen Intel Core i7/8GB/512GB SSD/Radeon Pro 5500 XT w/Apple Magic Keyboard & Apple Magic Mouse 2 8/4/20 2,099.00 BR332LL/A BNDL iMac 21.5"/2.3GHz dual-core 7th-generation Core i5/8GB/256GB SSD/Intel IPG 640 with 3-year AppleCare+ for Schools 8/4/20 1,168.00 BR342LL/A BNDL iMac 21.5"/2.3GHz dual-core 7th-generation Core i5/8GB/256GB SSD/Intel IPG 640 with 4-year AppleCare+ for Schools 8/4/20 1,218.00 BR2P2LL/A BNDL iMac 27" 5K/3.1GHz 6-core 10th-generation Intel Core i5/8GB/256GB SSD/RP 5300 with 3-year AppleCare+ for Schools 8/4/20 1,818.00 BR2S2LL/A BNDL iMac 27" 5K/3.1GHz 6-core 10th-generation Intel Core i5/8GB/256GB SSD/RP 5300 with 4-year AppleCare+ for Schools 8/4/20 1,868.00 BR2Q2LL/A BNDL iMac 27" 5K/3.3GHz 6-core 10th-gen Intel Core i5/8GB/512GB -

Apple Strategy Teardown
Apple Strategy Teardown The maverick of personal computing is looking for its next big thing in spaces like healthcare, AR, and autonomous cars, all while keeping its lead in consumer hardware. With an uphill battle in AI, slowing growth in smartphones, and its fingers in so many pies, can Apple reinvent itself for a third time? In many ways, Apple remains a company made in the image of Steve Jobs: iconoclastic and fiercely product focused. But today, Apple is at a crossroads. Under CEO Tim Cook, Apple’s ability to seize on emerging technology raises many new questions. Primarily, what’s next for Apple? Looking for the next wave, Apple is clearly expanding into augmented reality and wearables with the Apple Watch AirPods wireless headphones. Though delayed, Apple’s HomePod speaker system is poised to expand Siri’s footprint into the home and serve as a competitor to Amazon’s blockbuster Echo device and accompanying virtual assistant Alexa. But the next “big one” — a success and growth driver on the scale of the iPhone — has not yet been determined. Will it be augmented reality, healthcare, wearables? Or something else entirely? Apple is famously secretive, and a cloud of hearsay and gossip surrounds the company’s every move. Apple is believed to be working on augmented reality headsets, connected car software, transformative healthcare devices and apps, as well as smart home tech, and new machine learning applications. We dug through Apple’s trove of patents, acquisitions, earnings calls, recent product releases, and organizational structure for concrete hints at how the company will approach its next self-reinvention. -

Comparing Iphone 5S and 5C with Their Predecessors
PREVIEW Scan this code for more info. To download a barcode app, SMS <f2k> to 56677 from a mobile phone with Internet access and camera. SMARTPHONE Comparing iPhone 5S and 5C with their Predecessors Fingerprint scanner, slo-mo video, faster 64-bit A7 processor, a new motion processor chip called M7, improved camera are the highlights of the new iPhone — Mastufa Ahmed & S. Aadeetya utting an Touch ID brings biometrics into end to all the mainstream Pthe rumors The big highlight of 5S model is the much talked about and speculations, one which they call Touch ID. This reads your fingerprint Apple finally takes thus making your device even more secure. By adding a the wraps off the fingerprint scanner to its newest mobile iPhone 5 successor phone, Apple brings biometrics into at an event held mainstream. at the company’s The Touch ID fingerprint sensor Cupertino, CA is capacitive, 170 microns thin, has a headquarters. 500 ppi resolution, scans sub-epider- Powered by A6 mal skin layers, and has 360 degree chip, the iPhone 5C model has 4-inch retina display and readability. No matter how you train also has a higher-capacity battery than previous iPhones. the sensor to read your finger, it can The entire back and sides are made from a single part, you read it from any rotation, says Apple. won’t see any joints. It’s got a 8mp camera on the rear, and The Touch ID sensor will be built into comes in Blue/white/red/yellow/green colors. the home button. The home button The new iPhone 5S comes with 64-bit A7 chip and is made of laser-cut sapphire crystal, Apple describes the phone as “the first 64-bit smartphone surrounded by a stainless steel detec- in the world”. -

Startups of David WHY HAS ISRAEL BECOME a KEY MARKET for EARLY-STAGE INNOVATION?
PROFESSIONAL PRACTICE PORTFOLIO PERFORMANCE STARtups of David WHY HAS ISRAEL BECOME A KEY MARKET FOR EARLY-STAGE INNOVATION? By Sherree DeCovny Israel has produced so many successful technology start- Forces (IDF), which happens to be a surprising advantage ups that Tel Aviv is now considered the Silicon Valley of the for some entrepreneurs. The military is the great leveler: Middle East. Venture capital funds from around the world No one cares about your socioeconomic background, and are flocking to the country in search of the next big inno- everyone has an opportunity to build a network of talented vation. Several companies have been bought out by global friends and acquaintances. The IDF is also a technology- giants, and scores of Israeli companies are listed on major intensive organization, providing a pathway for Israelis to foreign exchanges. So what is Israel’s secret? develop skills in such key areas as cybersecurity. Israel is a small country A case in point is serial entrepreneur Ariel Maislos. Fol- with hostile neighbors and lowing a 10-year stint in the IDF, Maislos began developing Israel attracts more ven- limited natural resources, so technology for Israel’s equivalent of the US National Secu- tures per capita than any Israelis are creative at find- rity Agency. In 2001, he founded Passave, which offered other country, and 85% of ing workarounds and ways fiber-to-the-home broadband communication technology. the funding for Israeli high to scale globally. Out-of-the- Passave was sold to PMC-Sierra in 2006, which was then tech comes from abroad. box thinking is so ingrained acquired by Microsemi in 2016. -

|||GET||| M: Finance with Connect Plus 1St Edition
M: FINANCE WITH CONNECT PLUS 1ST EDITION DOWNLOAD FREE Marcia Cornett | 9780077506056 | | | | | iOS 14 and iPadOS 14 upgrade checklist: Here's how to get your iPhone and iPad ready Go to Wish List. However, many features like MMSappsand copy and paste were not supported at release, leading hackers jailbreaking their phones to add these features. We delete comments that violate our policywhich we encourage you to read. Messier Jr, Steven M. Retrieved March 31, Jason Cipriani. Always collect your card and transaction slip once you have completed your transaction. You will be taken to our partner Chegg. Prevent unauthorized Transactions in your demat account. Speed up the process by plugging your phone or tablet in to a charger and connecting it to a Wi-Fi network to prevent mobile data use and killing your battery in the process. The device broke with prevailing mobile phone designs by eliminating most physical hardware buttons, and eschewing a stylus for its screen-based interface, instead featuring only a few physical buttons and a touch screen. View All. Blackjack vs. Iconia Amex Credit Card A credit card designed specially to cater to your lifestyle requirements with tailor-made privilegeson golf, travel, lifestyle and more. Enjoy endless benefits and privileges on saving account programmes for you and your family with IndusInd Bank. JavaScript seems to be disabled in your browser. Current Arthur D. Now that you have your phone backed up and all of the random junk and clutter removed, install iOS 14 or iPadOS Italics indicate discontinued products, servicesor defunct companies. No worries for refund as the money remain in investor's account. -

Apple Inc's Marketing Plan
University of Puthisastra Faculty of Economic and Business Marketing Research Topic: Apple Inc.’s Marketing Strategies Lecturer: Sreang Kimlee Group Members: Yorn Sophearith Kong Veasna Khan Sokna Academic Year: 2011-2012 Semester I:Y4 Contents I. Introduction to Apple Inc. II. Marketing Strategies of Apple III. Conclusion I. Introduction to Apple inc Apple is a multinational corporation designing and selling consumer electronics, computer’s software and personal computers It was established on April 1, 1976 and became Apple Computer Inc. on January 3, 1977 then changed to Apple Inc in 2007 Founders: Steve Jobs, Steve Wozniak and Ronald Wayne with the start-up cost was only $1300 I. Introduction to Apple inc Apple has: Staff: 60,400 Retailed stores: 357 (Oct 2011) Subsidiaries: Braeburn Capital, FileMaker Inc., and Anobit Revenues:$108.249 billion (2011) Asset: $116.371 billion (2011) Profit: $25.922 billion (2011) International Rank: The Most Value Company (2010) I. Introduction to Apple inc Apple’s products: Hardware products: Macintosh line of computers, iPod (iPod Nana, iPod Touch), iPhone, and iPad Software products: Mac OS X operating system, iTune media browser, the iLife, the iWork, Aperture, Final Cut Studio, Logic Studio, Safari browser and iOS I. Introduction to Apple Inc I. Introduction to Apple inc Apple’s progressions: 1976-1980: Apple I introduced in1976, and Apple II in 1977. 1981-1985: Lisa and Mocintosh era and Management conflict. 1986-1993: Rise and Fall. Apple introduced Power Book that brought success and increased revenue. Then Apple failed consumer targeted some products. 1994-1997: Attempts at reinvention. 1998-2004: Return to profitability I. -

Analysis of the Impact of Public Tweet Sentiment on Stock Prices
Claremont Colleges Scholarship @ Claremont CMC Senior Theses CMC Student Scholarship 2020 A Little Birdy Told Me: Analysis of the Impact of Public Tweet Sentiment on Stock Prices Alexander Novitsky Follow this and additional works at: https://scholarship.claremont.edu/cmc_theses Part of the Business Analytics Commons, Portfolio and Security Analysis Commons, and the Technology and Innovation Commons Recommended Citation Novitsky, Alexander, "A Little Birdy Told Me: Analysis of the Impact of Public Tweet Sentiment on Stock Prices" (2020). CMC Senior Theses. 2459. https://scholarship.claremont.edu/cmc_theses/2459 This Open Access Senior Thesis is brought to you by Scholarship@Claremont. It has been accepted for inclusion in this collection by an authorized administrator. For more information, please contact [email protected]. Claremont McKenna College A Little Birdy Told Me Analysis of the Impact of Public Tweet Sentiment on Stock Prices Submitted to Professor Yaron Raviv and Professor Michael Izbicki By Alexander Lisle David Novitsky For Bachelor of Arts in Economics Semester 2, 2020 May 11, 2020 Novitsky 1 Abstract The combination of the advent of the internet in 1983 with the Securities and Exchange Commission’s ruling allowing firms the use of social media for public disclosures merged to create a wealth of user data that traders could quickly capitalize on to improve their own predictive stock return models. This thesis analyzes some of the impact that this new data may have on stock return models by comparing a model that uses the Index Price and Yesterday’s Stock Return to one that includes those two factors as well as average tweet Polarity and Subjectivity. -

December 18, 2020 VIA EDIS the Honorable Lisa R. Barton Secretary
Troutman Pepper Hamilton Sanders LLP High Street Tower, 125 High Street, 19th Floor Boston, MA 02110-2736 troutman.com Gwendolyn Tawresey D 617.204.5132 F 866.851.6572 [email protected] December 18, 2020 VIA EDIS The Honorable Lisa R. Barton Secretary to the Commission U.S. International Trade Commission 500 E Street, S.W. Washington, D.C. 20436 Re: Certain Integrated Circuits and Products Containing the Same Dear Secretary Barton: Enclosed for filing on behalf of Tela Innovations, Inc. (“Tela”), please find the following documents in support of Tela’s request that the Commission commence an Investigation pursuant to Section 337 of the Tariff Act of 1930, as amended. Pursuant to the Commission Rules of Practice and Procedure, a request for confidential treatment of Confidential Exhibits 6- 9 are included with this submission. Pursuant to the Commission’s current rules, Tela submits the following: 1. The Complaint (Rule 210.8(a)(1)(ii)); 2. The accompanying Non-Confidential Exhibit Nos. 1-5, 10-14, Confidential Exhibit Nos. 6- 9, and public versions of Confidential Exhibit Nos. 6-9 (Rules 201.6(c) and 210.8(a)(1)(i)); 3. A certified copy of U.S. Patent No. 10,186,523, included with the Complaint as Exhibit No. 1 (Rule 210.12(a)(9)(i)); 4. A certified copy of the assignment records for the asserted U.S. Patent No. 10,186,523, included with the Complaint as Exhibit 2 (Rule 210.12(a)(9)(ii)); 5. A certified copy of the U.S. Patent and Trademark Office prosecution history of U.S. -

The Massachusetts-Israel Economic Impact Study
The Massachusetts-Israel Economic Impact Study 2016 Edition: The Boston-Israel Power Partnership An expanding relationship that generates revenue, jobs, and investment for the benefit of both economies Boston Tel Aviv June 2016 Prepared for the New England-Israel Business Council With support from CJP of Greater Boston Based on research by Stax, Inc. With additional research by TAMID @ Boston University by David Goodtree Table of Contents » Executive Summary ....................................................................................................... 4 » Israeli Innovation Is a Major Driver of the Massachusetts Economy ............................4 » About the Title of This Whitepaper .....................................................................................5 » Israeli Entrepreneurs Choose Boston To Build Global Businesses ..................... 6 » Boston is a Gateway for Israel to U.S. and Global Markets ............................................6 » Revenue ...................................................................................................................................7 » Jobs ...........................................................................................................................................8 » Capital ......................................................................................................................................8 » Acquisitions .............................................................................................................................10 -

Quick Guide to Connectivity and the Resound Smart™ App for Ios Introduction to Resound Smart Hearing™ Aids
Quick guide to connectivity and the ReSound Smart™ app for iOS Introduction to ReSound Smart Hearing™ aids WHICH RESOUND HEARING AIDS ARE SMART HEARING™ AIDS? Here is a list of Smart Hearing aids from ReSound that work with the ReSound Smart™ app. If you’re not sure, please ask your hearing care professional. ReSound LiNX2™ ReSound LiNX™ ReSound LiNX TS™ ReSound ENZO2™ ReSound Up Smart™ ™ 2 ReSound ENZO Apple devices that work with ReSound Smart Hearing aids ReSound Smart Hearing aids support Made for iPhone (MFi) functionality with the following Apple devices. iPhone 7 Plus iPad Pro (12.9-inch) iPod touch iPhone 7 iPad Pro (9.7-inch) (6th generation) iPhone 6s Plus iPad Air 2 iPod touch iPhone 6s iPad Air (5th generation) iPhone 6 Plus iPad mini 4 iPhone 6 iPad mini 3 iPhone SE iPad mini 2 iPhone 5s iPad mini iPhone 5c iPad (4th generation) iPhone 5 SUPPORT AND UPDATES FOR IOS ReSound Smart Hearing aids require iOS 8 or later. Make sure that the latest version of iOS is installed on the Apple device for best performance. For use with the Apple Watch extension, min. watchOS 2 is required for Apple Watch and iPhone must be running iOS 9 or newer. For the most up-to-date information visit www.resound.com/smartapp 3 Pair with your iPhone, iPad or iPod touch HOW TO PAIR YOUR RESOUND SMART HEARING™ AIDS TO YOUR iPhone, iPad OR iPod touch Check battery Turn on Bluetooth Insert a fresh battery in your ReSound Smart Hearing aid. Keep the battery door open so the Swipe upwards from the bottom of the screen to reveal hearing aid cannot power up. -

Foreign Innovators Generators of Open Innovation
American Journal of Innovative Research and Applied Sciences. ISSN 2429-5396 I www.american-jiras.com REVIEW ARTICLE FOREIGN INNOVATORS GENERATORS OF OPEN INNOVATION | llan Bijaoui *1 | *1. Graduate School of Business Management | Bar Ilan University | Ramat Gan | Israel | | Received | 25 November 2017 | | Accepted | 30 December 2018 | | Published 08 January 2019 | | ID Article | Bijaoui-ManuscriptRef.1-ajira251218 | Abstract Background: Immigrant innovators come to the host country with a different cultural background and have to adapt themselves to the local needs and behavior. Other foreign innovators cooperating with MNCs have also to find the way to be integrated and not to be classified as outsiders. Aims: We intend to prove that immigrant and other foreign innovators carry with them inflow of outside knowledge and change the outpourings of knowledge in host countries into discontinuous and disruptive open innovations. Our Method: Patents or diploma statistics cannot express the impact of foreign innovators on innovation processes. A case by case analysis is necessary in order to evaluate the impact of their researches. Results and Conclusion: The commitment of immigrant and other foreign innovators is greater and more diversified than inborn innovators due to the discontinuous and disruptive innovation processes they generate. Their contribution is in an extensive variety of key segments. A positive ecosystem around cooperation with foreign innovators could contribute to a more valuable development for home and host countries. Keywords: disruptive, discontinuous, immigration, foreigners, BoP, MNCs. 1. INTRODUCTION Lundvall (1992) [1] considers innovation to be an on-going procedure of getting the hang of, seeking and investigating, which result in innovative items and new or improved markets [1].