Thriving Beyond the Operating System: Financial Home � Fireeye Blogs � Research � Th
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Operating System Boot from Fully Encrypted Device
MASARYK UNIVERSITY FACULTY OF INFORMATICS Operating system boot from fully encrypted device BACHELOR'S THESIS Daniel Chromik Brno, Fall 2016 Replace this page with a copy of the official signed thesis assignment and the copy of the Statement of an Author. Declaration Hereby I declare that this paper is my original authorial work, which I have worked out by my own. All sources, references and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Daniel Chromik Advisor: ing. Milan Brož i Acknowledgement I would like to thank my advisor, Ing. Milan Brož, for his guidance and his patience of a saint. Another round of thanks I would like to send towards my family and friends for their support. ii Abstract The goal of this work is description of existing solutions for boot• ing Linux and Windows from fully encrypted devices with Secure Boot. Before that, though, early boot process and bootloaders are de• scribed. A simple Linux distribution is then set up to boot from a fully encrypted device. And lastly, existing Windows encryption solutions are described. iii Keywords boot process, Linux, Windows, disk encryption, GRUB 2, LUKS iv Contents 1 Introduction 1 1.1 Thesis goals 1 1.2 Thesis structure 2 2 Boot Process Description 3 2.1 Early Boot Process 3 2.2 Firmware interfaces 4 2.2.1 BIOS - Basic Input/Output System 4 2.2.2 UEFI - Unified Extended Firmware Interface . 5 2.3 Partitioning tables 5 2.3.1 MBR - Master Boot Record 5 2.3.2 GPT - GUID Partition Table 7 2.4 -

Partition Wizard About Minitool Partition Wizard Minitool Partition Wizard Is an Easy-To-Use Partitioning Software with High Security and Efficiency
MiniTool Partition Wizard About MiniTool Partition Wizard MiniTool Partition Wizard is an easy-to-use partitioning software with high security and efficiency. Due of its simple user interface, you can create, delete, format, move, and resize partitions with ease. What’s more, your data will always be protected when using MiniTool Partition Wizard to move and resize partitions. Main Functions of MiniTool Partition Wizard: Resize/ Move partitions Merge Partitions Create partitions Delete partitions Change Partition Label Delete all partitions Format partitions Change Cluster Size Convert file system Convert FAT to NTFS Convert NTFS to FAT Explore Partition Check Partitions Recovery Partition Wipe disk Wipe partition Copy partition Copy disks Initialize to MBR disk Initialize to GPT disk Align All Partitions Align Partition Convert MBR Disk to GPT Disk Convert GPT Disk to MBR Disk Dynamic Disk Create volume Delete Volume Format Volume Move/Resize Volume Wipe Volume Explore Volume Check File System Change Volume Label Change Volume Letter Change Volume Cluster Size Volume Properties MiniTool Partition Wizard Staring MiniTool Partition Wizard You can start MiniTool Partition Wizard from the Start menu in Windows Click Start menu > All Programs > MiniTool Partition Wizard xxx Edition > MiniTool Partition Wizard xxx Edition Xxx is your present edition of MiniTool Partition Wizard, Such as Home, Professional, Server, and Enterprise MiniTool Partition Wizard Hardware Requirements Minimum Hardware requirements: 500 MHz x86 or compatible CPU. 256mb RAM memory. Mouse and Keyboard. Recommended Hardware requirements: 1 GHz x86 or compatible CPU. 512mb RAM memory. Mouse and Keyboard. MiniTool Partition Wizard System Requirements Note: you should have access to administration while using Partition Wizard. -

Computer Hardware
Chapter Computer Hardware ENCE EXAM TOPICS COVERED IN 1 THIS CHAPTER: ✓ Computer hardware components ✓ The boot process ✓ Partitions ✓ File systems COPYRIGHTED MATERIAL Computer forensics examiners deal most often with the media on which evidentiary data is stored. This includes, but is not lim- ited to, hard drives, CDs, DVDs, fl ash memory devices, smart phones, tablets, and even legacy fl oppies and tapes. Although these devices might be the bane of the examiner’s existence, media devices don’t exist in a void, and knowledge of a computer’s various components and functions is a must for the competent examiner. As an examiner, you may be called upon to explain how a computer functions to a jury. Doing so requires you know a computer’s function from a technical standpoint and that you can translate those technical concepts into real-world, easy-to-understand terms. As an examiner, you may also be subjected to a voir dire examination by opposing coun- sel to challenge your competence to testify. Acronyms are hardly in short supply in the fi eld of computing—some well-known and meaningful, others more obscure. Imagine being asked during such an examination to explain several of the common acronyms used with computers, such as RAM, CMOS, SCSI, BIOS, and POST. If you were to draw a blank on some obscure or even common acronym, picture its impact on your credibility. Some acronyms are difficult to remember because their meaning is often obscure or meaningless. A good example is TWAIN, which stands for T ech- nology W ithout a n I nteresting N ame. -

Wikipedia: Design of the FAT File System
Design of the FAT file system A FAT file system is a specific type of computer file system architecture and FAT a family of industry-standard file systems utilizing it. Developer(s) Microsoft, SCP, IBM, [3] The FAT file system is a legacy file system which is simple and robust. It Compaq, Digital offers good performance even in very light-weight implementations, but Research, Novell, cannot deliver the same performance, reliability and scalability as some Caldera modern file systems. It is, however, supported for compatibility reasons by Full name File Allocation Table: nearly all currently developed operating systems for personal computers and FAT12 (12- many home computers, mobile devices and embedded systems, and thus is a bit version), well suited format for data exchange between computers and devices of almost FAT16 (16- any type and age from 1981 through the present. bit versions), Originally designed in 1977 for use on floppy disks, FAT was soon adapted and FAT32 (32-bit version used almost universally on hard disks throughout the DOS and Windows 9x with 28 bits used), eras for two decades. Today, FAT file systems are still commonly found on exFAT (64- floppy disks, USB sticks, flash and other solid-state memory cards and bit versions) modules, and many portable and embedded devices. DCF implements FAT as Introduced 1977 (Standalone the standard file system for digital cameras since 1998.[4] FAT is also utilized Disk BASIC-80) for the EFI system partition (partition type 0xEF) in the boot stage of EFI- FAT12: August 1980 compliant computers. (SCP QDOS) FAT16: August 1984 For floppy disks, FAT has been standardized as ECMA-107[5] and (IBM PC DOS 3.0) ISO/IEC 9293:1994[6] (superseding ISO 9293:1987[7]). -
Exploration of Windows Vista Advanced Forensic Topics – Day 1
Windows Vista and NTFS File System Internals Exploration of Windows Vista Advanced Forensic Topics – Day 1 LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Windows Client Forensics (Windows Vista Advanced Topics) Transactional NTFS and Registry Explained LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved New Features Important Changes of Interest LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Vista includes a “self-healing” function which can correct certain errors in the system • Vista maintains a list of hashes of known files and checks the hashes periodically • On non-system files Vista will validate the file metadata • Files whose hashes do not match or metadata is not valid will be replaced the next time the system is rebooted LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Equivalent to Chkdsk and defrag processes constantly running in the background • This has the potential to decrease the usefulness of the free space and slack space on the disk as well as limit the ability to recover deleted files LAW ENFORCEMENT SENSITIVE INFORMATION – DO NOT SHARE THESE MATERIALS ©2007 Microsoft Corporation – All Rights Reserved Self-Healing File System • Healed files can be identified by an examination of the event -
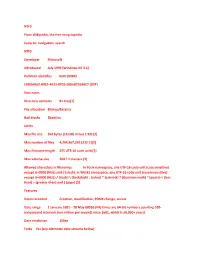
NTFS from Wikipedia, the Free Encyclopedia Jump To: Navigation, Search NTFS Developer Microsoft Introduced July 1993 (Windows
NTFS From Wikipedia, the free encyclopedia Jump to: navigation, search NTFS Developer Microsoft Introduced July 1993 (Windows NT 3.1) Partition identifier 0x07 (MBR) EBD0A0A2-B9E5-4433-87C0-68B6B72699C7 (GPT) Structures Directory contents B+ tree[1] File allocation Bitmap/Extents Bad blocks $badclus Limits Max file size 264 bytes (16 EiB) minus 1 KiB [2] Max number of files 4,294,967,295 (232-1)[2] Max filename length 255 UTF-16 code units[3] Max volume size 264 ? 1 clusters [2] Allowed characters in filenames In Posix namespace, any UTF-16 code unit (case sensitive) except U+0000 (NUL) and / (slash). In Win32 namespace, any UTF-16 code unit (case insensitive) except U+0000 (NUL) / (slash) \ (backslash) : (colon) * (asterisk) ? (Question mark) " (quote) < (less than) > (greater than) and | (pipe) [3] Features Dates recorded Creation, modification, POSIX change, access Date range 1 January 1601 ʹ 28 May 60056 (File times are 64-bit numbers counting 100- nanosecond intervals (ten million per second) since 1601, which is 58,000+ years) Date resolution 100ns Forks Yes (see Alternate data streams below) Attributes Read-only, hidden, system, archive, not content indexed, off-line, temporary File system permissions ACLs Transparent compression Per-file, LZ77 (Windows NT 3.51 onward) Transparent encryption Per-file, DESX (Windows 2000 onward), Triple DES (Windows XP onward), AES (Windows XP Service Pack 1, Windows Server 2003 onward) Single Instance Storage Yes Supported operating systems Windows NT family (Windows NT 3.1 to Windows NT 4.0, Windows 2000, Windows XP, Windows Server 2003, Windows Vista, Windows Server 2008) NTFS is the standard file system of Windows NT, including its later versions Windows 2000, Windows XP, Windows Server 2003, Windows Server 2008, and Windows Vista.[4] NTFS supersedes the FAT file system as the preferred file system for Microsoft͛s ͞Windows͟-branded operating systems. -

UEFI, Booting & Partition Management
UEFI, Booting & Partition Management Kelvin Cording July 2018 Unified Extendible Interface (UEFI) • Modern computer and Windows are moving away from the traditional MBR based boot- up processes to hardware and software using UEFI • Win 8 introduced UEFI • If Windows 8 is already installed using Legacy BIOS, it can't be converted to UEFI. A new OS installation is required. Understanding a computer boot up process When you hit the power button of your PC, an execution begins that will eventually load the Operating System into memory. This first execution depends on the partition structure of your hard disk. We have two types of partition structures (or formats): MBR and GPT. The partition structure on a drive defines three things: • The structure of data on the drive. • The code used during startup if a partition is bootable. • Where a partition begins and ends. MBR -Master Boot Record GPT Globally Unique Identifier Partition Table = GUID Partition A comparison of GPT and MBR partition structures A comparison of GPT and MBR partition structures (2) Max partition size in MBR is ~2TB whereas in UEFI it is ~9 ZetaBytes One zettabyte (1021) is approximately equal to a thousand exabytes or a billion terabytes. MBR can have at max 4 primary partition whereas GPT can have 128. MBR can store only one bootloader whereas GPT has a separate dedicated EFI System Partition(ESP) for storing multiple bootloaders. The MBR Boot Process Before the BIOS can detect the boot device, it goes through a sequence of system configuration functions starting with: • Power-on-self-test. • Detecting and initializing the video card. -

FAT32 File Structure Prof
FAT32 File Structure Prof. James L. Frankel Harvard University Version of 9:45 PM 24-Mar-2021 Copyright © 2021 James L. Frankel. All rights reserved. FAT32 Source Documentation • The reference document you should use is the Microsoft Extensible Firmware Initiative FAT32 File System Specification • On class web site under The NXP/Freescale ARM -> microSDHC Card • It is available on the class web site at https://cscie92.dce.harvard.edu/spring2021/Microsoft%20Extensible%20Firmware%20Initiative%20FAT32%2 0File%20System%20Specification,%20Version%201.03,%2020001206.pdf under Online Papers Used in Class • Important correction to this document concerns the DIR_CrtTimeTenth field in the FAT 32 Byte Directory Entry Structure • The name and description of this field is incorrect • Instead of DIR_CrtTimeTenth, we will use the name DIR_CrtTimeHundth • Here is the correct description of this field (to update the text on page 23): • Hundredths of a second time at file creation time. This field contains a count of hundredths of a second. Because the seconds portion of the DIR_CrtTime field denotes a creation time with a granularity of 2 seconds, this field contains a number of hundredths of a second (0 to 199, inclusively) that denotes a number of seconds from 0 to 1.99, inclusively, that may increment the number of seconds in addition to supplying the number of hundredths of a second. • There is also a typo on page 25 where a field is referred to as DIR_CrtTimeMil (which does not exist), and, as corrected here, should be DIR_CrtTimeHundth 2 SD Documentation • Documentation for the SD controller in the K70 • K70 Sub-Family Reference Manual, Rev. -

Initial Bootloader Introduction
initial bootloader Initial Bootloader Introduction On power-up, when a computer is turned on, the following operations are performed: 1. The computer performs a power on self test (POST) to ensure that it meets the necessary requirements and that the hardware is functioning properly. 2. A program located in the ROM BIOS, called the bootstrap loader, is executed. 3. When the bootstrap loader starts it searches for a boot sector and passes control to the boot sector's code area. A boot sector is the first sector of a disk and has a small program in its code area, known as the initial bootstrap program, that can load an operating system. The hardware can recognise a boot sector by hexadecimal signature number AA55 which marks the last two bytes of the sector. The bootstrap loader searches for boot sectors on a number of storage devices, including: ● floppy drives ● CD-ROM drives ● hard drives ● flash drives In almost all computers, the BIOS can be configured to change the order storage devices are searched to control their priority. For example, floppy drives normally have higher priority than hard drives, so if a bootable floppy disk is in the drive when the computer is switched on the computer will boot from the floppy disk; otherwise it will boot from media in another storage device, such as a hard disk. When booting from a hard disk or flash drive, the machine code in the master boot record normally examines the partition table (also in the master boot record), identifies the active partition (the partition that is marked as bootable), reads the boot sector, containing the volume boot record (VBR), from that partition, and then runs the machine code in the volume boot record in the same way code would be run from the boot sector in a floppy disk. -

Computer Science. Worksheet #2
IES Adormideras Bilingual Sections Computer Science. Worksheet #2 Name: Gabriela Beade Couceiro Class: 4ºA Date: 11-10-08 Use information gathered from textbooks, encyclopedias, internet, wikipedia, etc, to write a brief summary of what the following things are and what they are used for. Insert your answers after each concept using openOffice. Use a different font color for your answers. Email me your worksheet indicating in the subject “INF. Worksheet #2. <Your name>'” 1. Partition: A disk partition is the creation of separate divisions of a hard disk drive. 2. Hard disk drive (HDD): is a non-volatile storage device which stores digitally encoded data 3. File system: is a method for storing and organizing computer files and the data they contain to make it easy to find and access them 4. Device: any device attached to a computer that expands its functionality 5. BIOS: is an acronym that stands for the Basic Input/Output System. 6. MBR (Master Boot Record): is the 512-byte boot sector that is the first sector of a partitioned data storage device such as a hard disk. 7. VBR (Volume Boot Record): is a type of boot sector, stored in a disc volume on a hard disk, floppy disk, or similar data storage device, that contains code for booting programs (usually, but not necessarily, operating systems) stored in other parts of the volume. On non-partitioned storage devices, it is the first sector of the device 8. Operating system: is the software component of a computer system that is responsible for the management and coordination of activities and the sharing of the resources of the computer. -

Mbrwizard User Guide
FIRESAGE SOLUTIONS MBRWizard Suite User Guide 2012 Firesage Solutions, LLC All Rights Reserved http://firesage.com This document is provided by Firesage Solutions for informational purposes only, and is provided on an ‘as is’ basis without any warranties expressed or limited. Information in this document is subject to change without notice and does not represent a commitment on the part of Firesage Solutions. The software described in this document is provided under a license agreement. The software may only be used in accordance with the terms of that license agreement. It is unlawful to copy or use the software except as specifically allowed in the license It is the responsibility of the user to ensure the suitability of MBRWizard before installing or using. Under no circumstance will Firesage Solutions be responsible for any loss or damage resulting from MBRWizard. Your use of programs in MBRWizard Suite implies acceptance of these terms. ii Table of Contents Introduction ................................................................................ 1 What is MBRWizard Suite? ............................................................. 1 What is the MBR? ............................................................................ 1 Partition Table .......................................................................................... 1 Boot Code ................................................................................................. 1 Disk Signature ......................................................................................... -

Advanced Computer Forensics
Advanced Computer Forensics EnCE EnCase Forensics: The Official EnCase Certified Examiner Study Guide Chapter 2 File Systems Disk Basics - 1 • Hard Disk • Physical Device • Referred to as a numeric value (0, 1, 2 etc) • Logical Volume • Referred to by letters A: floppy and C etc. volumes on physical disk • Disk Preparation • Partition – create partition table • MBR – Master Boot Record • 4 partition limit • Disk size to 2 TB • No backup copy of partition table • GPT – GUID Partition Table • 128 partitions • 8 ZB hard drive • Has a copy of the partition table Disk Basics - 2 • Disk Preparation • Partition – create partition table • Right Click -> choose partition style • Creates a new blank partition table in the first sector of the hard drive • Create a new Volume • Right Click -> “unallocated” NEW VOLUME • Specify volume size • VBR – will be created • Format the Volume • Choose file system – Structure of how information will be written and recalled • FAT, NTFS, ExFAT • Sectors and Clusters • Based on File Systems used • Allocation blocks or clusters will be established with groupings of sectors • Sectors are commonly 512 bytes • Clusters keep addressing manageable in very large drives • Windows default – 8 sectors per cluster – 4096 bytes FAT Basics - 1 • Directory Entry • Directory Entries do NOT contain any data • Data is contained in Data allocation units or Clusters • Clusters • 1 or more sectors • Smallest unit in which a file or directory can be stored • If a file is bigger than 1 cluster than it is allocated more than one • Directory