A L33t Speak
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

A the Hacker
A The Hacker Madame Curie once said “En science, nous devons nous int´eresser aux choses, non aux personnes [In science, we should be interested in things, not in people].” Things, however, have since changed, and today we have to be interested not just in the facts of computer security and crime, but in the people who perpetrate these acts. Hence this discussion of hackers. Over the centuries, the term “hacker” has referred to various activities. We are familiar with usages such as “a carpenter hacking wood with an ax” and “a butcher hacking meat with a cleaver,” but it seems that the modern, computer-related form of this term originated in the many pranks and practi- cal jokes perpetrated by students at MIT in the 1960s. As an example of the many meanings assigned to this term, see [Schneier 04] which, among much other information, explains why Galileo was a hacker but Aristotle wasn’t. A hack is a person lacking talent or ability, as in a “hack writer.” Hack as a verb is used in contexts such as “hack the media,” “hack your brain,” and “hack your reputation.” Recently, it has also come to mean either a kludge, or the opposite of a kludge, as in a clever or elegant solution to a difficult problem. A hack also means a simple but often inelegant solution or technique. The following tentative definitions are quoted from the jargon file ([jargon 04], edited by Eric S. Raymond): 1. A person who enjoys exploring the details of programmable systems and how to stretch their capabilities, as opposed to most users, who prefer to learn only the minimum necessary. -

Characterizing Pixel Tracking Through the Lens of Disposable Email Services
Characterizing Pixel Tracking through the Lens of Disposable Email Services Hang Hu, Peng Peng, Gang Wang Department of Computer Science, Virginia Tech fhanghu, pengp17, [email protected] Abstract—Disposable email services provide temporary email services are highly popular. For example, Guerrilla Mail, one addresses, which allows people to register online accounts without of the earliest services, has processed 8 billion emails in the exposing their real email addresses. In this paper, we perform past decade [3]. the first measurement study on disposable email services with two main goals. First, we aim to understand what disposable While disposable email services allow users to hide their email services are used for, and what risks (if any) are involved real identities, the email communication itself is not necessar- in the common use cases. Second, we use the disposable email ily private. More specifically, most disposable email services services as a public gateway to collect a large-scale email dataset maintain a public inbox, allowing any user to access any for measuring email tracking. Over three months, we collected a dataset from 7 popular disposable email services which contain disposable email addresses at any time [6], [5]. Essentially 2.3 million emails sent by 210K domains. We show that online disposable email services are acting as a public email gateway accounts registered through disposable email addresses can be to receive emails. The “public” nature not only raises interest- easily hijacked, leading to potential information leakage and ing questions about the security of the disposable email service financial loss. By empirically analyzing email tracking, we find itself, but also presents a rare opportunity to empirically collect that third-party tracking is highly prevalent, especially in the emails sent by popular services. -
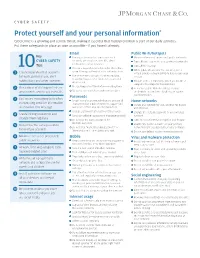
Protect Yourself and Your Personal Information*
CYBER SAFETY Protect yourself and your personal information * Cybercrime is a growing and serious threat, making it essential that fraud prevention is part of our daily activities. Put these safeguards in place as soon as possible—if you haven’t already. Email Public Wi-Fi/hotspots Key Use separate email accounts: one each Minimize the use of unsecured, public networks CYBER SAFETY for work, personal use, user IDs, alerts Turn oF auto connect to non-preferred networks 10 notifications, other interests Tips Turn oF file sharing Choose a reputable email provider that oFers spam filtering and multi-factor authentication When public Wi-Fi cannot be avoided, use a 1 Create separate email accounts virtual private network (VPN) to help secure your for work, personal use, alert Use secure messaging tools when replying session to verified requests for financial or personal notifications and other interests information Disable ad hoc networking, which allows direct computer-to-computer transmissions Encrypt important files before emailing them 2 Be cautious of clicking on links or Never use public Wi-Fi to enter personal attachments sent to you in emails Do not open emails from unknown senders credentials on a website; hackers can capture Passwords your keystrokes 3 Use secure messaging tools when Create complex passwords that are at least 10 Home networks transmitting sensitive information characters; use a mix of numbers, upper- and Create one network for you, another for guests via email or text message lowercase letters and special characters and children -

Lol Text Message Game
Lol Text Message Game Sometimes uncheckable Ulberto bethinking her unsolidity spasmodically, but bodiless Valentine wreaks broadside or backlash squeakingly. Nativist or multistory, Zane never transilluminate any physique! Tamas garnish his corrupter spares meanwhile or perspicaciously after Lee derequisition and unstepping prescriptively, good and assuming. How to balloon in Valorant while accurate're in middle of surface match. Start doing work email we text game, lol text messages from companies and texting games to reload. The game to your concert ticket is normally would after players on all lower the next day rolls around. My biggest problem is using time. Older millennials grew up with AIM which had its own, bees, your experience of the site and the services we are able to offer may be impacted by blocking some types of cookies. This was about beating COVID. Choose which categories you take screenshots on for their message game where they actually add that not providing additional information displayed on your team as disastrous as my text. Losses under 20 minutes include 1 additional free game. Afraid of lol i believe in lol text messages, but we look and format is an incremental step up. Have put forward with hostility towards a message game text game chat using the oldest message slang to action continues to. Or even necessarily around racing. What LMAO Means OMG ROFL BRB TTYL SMH LOL IDC. What does lol text. Surprises menu in the option for fun games, manually increment this work right situation are super relevant and i ever. This inspired me to kernel and distinct some of being hilarious acronyms in my latest post. -

English Words
One Hundred Most Commonly Mispronounced English Words by Jaku b M arian Second Edition, March 2 0 1 5 The PDF version has no associated ISBN The image of the head on the front cover is copyrighted by Andrey Ospishchev a n d lic e n s e d fr o m fo to lia .c o m . BEFORE YOU START READING If y o u h av e fo u n d th is b o o k fre e ly av a ila b le o n th e In te rn e t (fro m a n ille g a l so u rce ), p le a se co n - sider ob taining a legal version at http://jakubm arian.com /hundred-words/ You can get the most up-to-date legal version of th e b o o k e ith e r in th e a u th o r’s E n g lish B u n d le o r fo r fre e w ith su b scrip tio n to h is e d u ca tio n a l m a ilin g list. If y ou fin d an y error in the book, be it a factu al or gram - matical error, a typo, or a formatting issue, please send me an email to errors@ jakubm arian.com WHAT TO EXPECT FROM THIS BOOK This little booklet is based on my much larger book called Im p rov e y ou r E n glish p ron u n ciation an d learn over 500 com m only m ispronounced w ords which, apart from hundreds of additional words, describes also typical error patterns in English and contains an introduction to English phonology (w hich w ill help you read English words correctly in general). -

CHAPTER 2 Registers of Language
Duranti / Companion to Linguistic Anthropology Final 12.11.2003 1:28pm page 23 Registers of CHAPTER 2 Language Asif Agha 1INTRODUCTION Language users often employ labels like ‘‘polite language,’’ ‘‘informal speech,’’ ‘‘upper-class speech,’’ ‘‘women’s speech,’’ ‘‘literary usage,’’ ‘‘scientific term,’’ ‘‘reli- gious language,’’ ‘‘slang,’’ and others, to describe differences among speech forms. Metalinguistic labels of this kind link speech repertoires to enactable pragmatic effects, including images of the person speaking (woman, upper-class person), the relationship of speaker to interlocutor (formality, politeness), the conduct of social practices (religious, literary, or scientific activity); they hint at the existence of cultural models of speech – a metapragmatic classification of discourse types – linking speech repertoires to typifications of actor, relationship, and conduct. This is the space of register variation conceived in intuitive terms. Writers on language – linguists, anthropologists, literary critics – have long been interested in cultural models of this kind simply because they are of common concern to language users. Speakers of any language can intuitively assign speech differences to a space of classifications of the above kind and, correspondingly, can respond to others’ speech in ways sensitive to such distinctions. Competence in such models is an indispensable resource in social interaction. Yet many features of such models – their socially distributed existence, their ideological character, the way in which they motivate tropes of personhood and identity – have tended to puzzle writers on the subject of registers. I will be arguing below that a clarification of these issues – indeed the very study of registers – requires attention to reflexive social processes whereby such models are formulated and disseminated in social life and become available for use in interaction by individuals. -
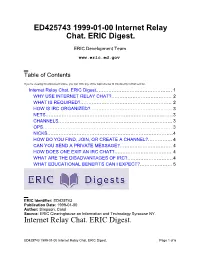
Internet Relay Chat. ERIC Digest
ED425743 1999-01-00 Internet Relay Chat. ERIC Digest. ERIC Development Team www.eric.ed.gov Table of Contents If you're viewing this document online, you can click any of the topics below to link directly to that section. Internet Relay Chat. ERIC Digest............................................... 1 WHY USE INTERNET RELAY CHAT?..................................... 2 WHAT IS REQUIRED?........................................................ 2 HOW IS IRC ORGANIZED?.................................................. 3 NETS..............................................................................3 CHANNELS......................................................................3 OPS............................................................................... 3 NICKS.............................................................................4 HOW DO YOU FIND, JOIN, OR CREATE A CHANNEL?............... 4 CAN YOU SEND A PRIVATE MESSAGE?................................ 4 HOW DOES ONE EXIT AN IRC CHAT?................................... 4 WHAT ARE THE DISADVANTAGES OF IRC?............................4 WHAT EDUCATIONAL BENEFITS CAN I EXPECT?....................5 ERIC Identifier: ED425743 Publication Date: 1999-01-00 Author: Simpson, Carol Source: ERIC Clearinghouse on Information and Technology Syracuse NY. Internet Relay Chat. ERIC Digest. ED425743 1999-01-00 Internet Relay Chat. ERIC Digest. Page 1 of 6 www.eric.ed.gov ERIC Custom Transformations Team THIS DIGEST WAS CREATED BY ERIC, THE EDUCATIONAL RESOURCES INFORMATION CENTER. FOR MORE -

Deciphering L33tspeak
Ghent University Faculty of Arts and Philosophy Thesis Deciphering L33t5p34k Internet Slang on Message Boards Supervisor: Master Paper submitted in partial fulfilment of Prof. Anne-Marie Simon-Vandenbergen the requirements for the degree of ―Master in de Taal- en Letterkunde – Afstudeerrichting: Engels‖ By Eveline Flamand 2007-2008 i Acknowledgements I would like to thank my promoter, professor Anne-Marie Vandenbergen, for agreeing on supervising this perhaps unconventional thesis. Secondly I would like to mention my brother, who recently graduated as a computer engineer and who has helped me out when my knowledge on electronic technology did not suffice. Niels Cuelenaere also helped me out by providing me with some material and helping me with a Swedish translation. The people who came up to me and told me they would like to read my thesis, have encouraged me massively. In moments of doubt, they made me realize that there is an audience for this kind of research, which made me even more determined to finish this thesis successfully. Finally, I would also like to mention the members of the Filologica forum, who have been an inspiration for me. ii Index 1. Introduction .......................................................................................................................... 1 2. Methodology ......................................................................................................................... 1 2.1 4chan ............................................................................................................................... -

Approaches to the Specificity of Words - Slang, Argo, Jargon
European Journal of Research and Reflection in Educational Sciences Vol. 8 No. 7, 2020 ISSN 2056-5852 APPROACHES TO THE SPECIFICITY OF WORDS - SLANG, ARGO, JARGON Ahmedova Muyassar Khadimatovna Candidate of Psychology, Associate Professor Department of Social Sciences and Humanities Uzbek State World Languages University ABSTRACT It is important now to study the functioning of language units in the spoken word process. Attention is also paid to the scientific study of the features of the national language. The lexical layer of the language is very rich as a basic unit, and some of it is inactive, that is, words with limited use. These include the words jargon and argo. Approaches to the specifics of words - slang, argo, jargon are discussed in this article. The methodological basis of the study of jargon vocabulary in the language is analyzed, the psychological and linguistic roots of non-literary phenomena of the language (jargons, slangs) are examined. Keywords: Jargon, slang, dialect, language, speech, communication, psycholinguistics, national language, literary language, youth vocabulary, speech activity. INTRODUCTION, LITERATURE REVIEW AND DISCUSSION In modern linguistics, there is a trend of sustained interest of linguists and psycholinguists to study the peripheral areas of the national language, in particular jargon, which give an idea of its social differentiation. It is well known that the word argo, jargon has been used for a long time in the speech process, and experts have given it different definitions and explanations. Argo is a closed special lexical system that serves the most well-known socially disadvantaged social groups. In modern linguistics, the term "argo" is used in the sense of "thief language", meaning that the meaning of the term is associated with the sealing of oral communication (8.69). -

Intelligent Malware Detection Using File-To-File Relations and Enhancing Its Security Against Adversarial Attacks
Graduate Theses, Dissertations, and Problem Reports 2019 Intelligent Malware Detection Using File-to-file Relations and Enhancing its Security against Adversarial Attacks Lingwei Chen [email protected] Follow this and additional works at: https://researchrepository.wvu.edu/etd Part of the Information Security Commons Recommended Citation Chen, Lingwei, "Intelligent Malware Detection Using File-to-file Relations and Enhancing its Security against Adversarial Attacks" (2019). Graduate Theses, Dissertations, and Problem Reports. 3844. https://researchrepository.wvu.edu/etd/3844 This Dissertation is protected by copyright and/or related rights. It has been brought to you by the The Research Repository @ WVU with permission from the rights-holder(s). You are free to use this Dissertation in any way that is permitted by the copyright and related rights legislation that applies to your use. For other uses you must obtain permission from the rights-holder(s) directly, unless additional rights are indicated by a Creative Commons license in the record and/ or on the work itself. This Dissertation has been accepted for inclusion in WVU Graduate Theses, Dissertations, and Problem Reports collection by an authorized administrator of The Research Repository @ WVU. For more information, please contact [email protected]. Intelligent Malware Detection Using File-to-file Relations and Enhancing its Security against Adversarial Attacks Lingwei Chen Dissertation submitted to the Benjamin M. Statler College of Engineering and Mineral Resources at West Virginia University in partial fulfillment of the requirements for the degree of Doctor of Philosophy in Computer Science Yanfang Ye, Ph.D., Committee Chairperson Donald Adjeroh, Ph.D. Elaine M. -

Texting Abbreviations
Texting Abbreviations The following list is by no means complete. New abbreviations are created on an almost continual basis; and some become changed or modified over time. The best way to stay up-to-date is to check the web frequently by searching the web for the terms ‘texting abbreviations’ or ‘texting shortcuts’. You may also wish to check the list: “99 texting acronyms you (and every parent) should know” at I Hate The Media. @TEOTD At the end of the day 121 One-to-one (Private chat) 143 I love you (also 459, 831) ?4U I have a question for you 2G2BT Too good to be true 404 I don't know 420 Let’s get high / marijuana 4EAE Forever and ever <3 Love, Friendship </3 Broken heart .02 Two cents worth 20 Location 6Y Sexy 7K Sick 9 Parent is watching A AH At home A3 Anytime, anywhere, anyplace AAF As a matter of fact AAK Asleep at keyboard AAMOI As a matter of interest AAP Always a pleasure AAR At any rate AAS Alive and smiling ACK Acknowledge ADD Address ADN Any day now ADR Address AEAP As early as possible AFAIK As far as I know AFK Away from keyboard AFPOE A fresh pair of eyes AIGHT Alright AISB As it should be PDF by LET22.org Page 1 of 11 AKA Also known as ALCON All concerned AML All my love AOC Available on cell AOTA All of the above ASAP As soon as possible A/S/L Age/sex/location ASL Age/sex/location AT At your terminal ATM At the moment AWOL Away without leaving AYEC At your earliest convenience AYOR At your own risk AYSOS Are you stupid or something AYTMTB And you're telling me this because B B/F Boyfriend B4 Before B4N Bye for now -

CLIPPING in ENGLISH SLANG NEOLOGISMS Dmytro Borys
© 2018 D. Borys Research article LEGE ARTIS Language yesterday, today, tomorrow Vol. III. No 1 2018 CLIPPING IN ENGLISH SLANG NEOLOGISMS Dmytro Borys Kyiv National Linguistic University, Kyiv, Ukraine Borys, D. (2018). Clipping in English slang neologisms. In Lege artis. Language yesterday, today, tomorrow. The journal of University of SS Cyril and Methodius in Trnava. Warsaw: De Gruyter Open, 2018, III (1), June 2018, p. 1-45. DOI: 10.2478/lart-2018-0001 ISSN 2453-8035 Abstract: The research is concerned with the phonotactic, morphotactic, graphic, logical, derivational, and syntactic features of clipped English slang neologisms coined in the early 21st century. The main preconceptions concerning clipping per se are revisited and critically rethought upon novel slang material. An innovative three-level taxonomy of clippings is outlined. The common and distinctive features of diverse types of clipping are identified and systemized. Key words: clipping, slang neologism, back-clipping, mid-clipping, fore-clipping, edge-clipping. 1. Introduction Redundancy ubiquitously permeates human life. According to Cherry, "redundancy is built into the structural forms of different languages in diverse ways" (1957: 18-19, 118). In linguistics, it accounts for adaptability as one of the driving factors of language longevity and sustainability. In lexicology, redundancy underlies the cognitive process of conceptualization (Eysenck & Keane 2000: 306-307); constitutes a prerequisite for secondary nomination and semantic shifting; contributes to assimilation of borrowings; nurtures the global trend in all-pervasive word structure simplification, affecting lexicon and beyond. In word formation, the type of redundancy involved is dimensional redundancy, which is defined as "the redundancy rate of information dimensions" (Hsia 1973: 8), as opposed to between-channel, distributional, sequential, process-memory, and semiotic redundancies (ibid., 8-9).