26 Disk Space Management
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Chrooting All Services in Linux
LinuxFocus article number 225 http://linuxfocus.org Chrooting All Services in Linux by Mark Nielsen (homepage) About the author: Abstract: Mark works as an independent consultant Chrooted system services improve security by limiting damage that donating time to causes like someone who broke into the system can possibly do. GNUJobs.com, writing _________________ _________________ _________________ articles, writing free software, and working as a volunteer at eastmont.net. Introduction What is chroot? Chroot basically redefines the universe for a program. More accurately, it redefines the "ROOT" directory or "/" for a program or login session. Basically, everything outside of the directory you use chroot on doesn't exist as far a program or shell is concerned. Why is this useful? If someone breaks into your computer, they won't be able to see all the files on your system. Not being able to see your files limits the commands they can do and also doesn't give them the ability to exploit other files that are insecure. The only drawback is, I believe it doesn't stop them from looking at network connections and other stuff. Thus, you want to do a few more things which we won't get into in this article too much: Secure your networking ports. Have all services run as a service under a non-root account. In addition, have all services chrooted. Forward syslogs to another computer. Analyze logs files Analyze people trying to detect random ports on your computer Limit cpu and memory resources for a service. Activate account quotas. The reason why I consider chroot (with a non-root service) to be a line of defense is, if someone breaks in under a non-root account, and there are no files which they can use to break into root, then they can only limit damage to the area they break in. -

The Linux Kernel Module Programming Guide
The Linux Kernel Module Programming Guide Peter Jay Salzman Michael Burian Ori Pomerantz Copyright © 2001 Peter Jay Salzman 2007−05−18 ver 2.6.4 The Linux Kernel Module Programming Guide is a free book; you may reproduce and/or modify it under the terms of the Open Software License, version 1.1. You can obtain a copy of this license at http://opensource.org/licenses/osl.php. This book is distributed in the hope it will be useful, but without any warranty, without even the implied warranty of merchantability or fitness for a particular purpose. The author encourages wide distribution of this book for personal or commercial use, provided the above copyright notice remains intact and the method adheres to the provisions of the Open Software License. In summary, you may copy and distribute this book free of charge or for a profit. No explicit permission is required from the author for reproduction of this book in any medium, physical or electronic. Derivative works and translations of this document must be placed under the Open Software License, and the original copyright notice must remain intact. If you have contributed new material to this book, you must make the material and source code available for your revisions. Please make revisions and updates available directly to the document maintainer, Peter Jay Salzman <[email protected]>. This will allow for the merging of updates and provide consistent revisions to the Linux community. If you publish or distribute this book commercially, donations, royalties, and/or printed copies are greatly appreciated by the author and the Linux Documentation Project (LDP). -
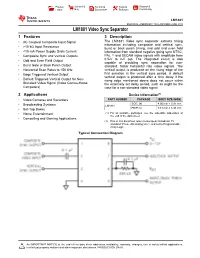
LM1881 Video Sync Separator Datasheet
Product Sample & Technical Tools & Support & Folder Buy Documents Software Community LM1881 SNLS384G –FEBRUARY 1995–REVISED JUNE 2015 LM1881 Video Sync Separator 1 Features 3 Description The LM1881 Video sync separator extracts timing 1• AC Coupled Composite Input Signal information including composite and vertical sync, • >10-kΩ Input Resistance burst or back porch timing, and odd and even field • <10-mA Power Supply Drain Current information from standard negative going sync NTSC, • Composite Sync and Vertical Outputs PAL (1) and SECAM video signals with amplitude from • Odd and Even Field Output 0.5-V to 2-V p-p. The integrated circuit is also capable of providing sync separation for non- • Burst Gate or Back Porch Output standard, faster horizontal rate video signals. The • Horizontal Scan Rates to 150 kHz vertical output is produced on the rising edge of the • Edge Triggered Vertical Output first serration in the vertical sync period. A default vertical output is produced after a time delay if the • Default Triggered Vertical Output for Non- rising edge mentioned above does not occur within Standard Video Signal (Video Games-Home the externally set delay period, such as might be the Computers) case for a non-standard video signal. 2 Applications Device Information(1) • Video Cameras and Recorders PART NUMBER PACKAGE BODY SIZE (NOM) SOIC (8) 4.90 mm × 3.91 mm • Broadcasting Systems LM1881 • Set-Top Boxes PDIP (8) 9.81 mm × 6.35 mm • Home Entertainment (1) For all available packages, see the orderable addendum at the end of the data sheet. • Computing and Gaming Applications (1) PAL in this datasheet refers to European broadcast TV standard “Phase Alternating Line”, and not to Programmable Array Logic. -
Lecture 7 Network Management and Debugging
SYSTEM ADMINISTRATION MTAT.08.021 LECTURE 7 NETWORK MANAGEMENT AND DEBUGGING Prepared By: Amnir Hadachi and Artjom Lind University of Tartu, Institute of Computer Science [email protected] / [email protected] 1 LECTURE 7: NETWORK MGT AND DEBUGGING OUTLINE 1.Intro 2.Network Troubleshooting 3.Ping 4.SmokePing 5.Trace route 6.Network statistics 7.Inspection of live interface activity 8.Packet sniffers 9.Network management protocols 10.Network mapper 2 1. INTRO 3 LECTURE 7: NETWORK MGT AND DEBUGGING INTRO QUOTE: Networks has tendency to increase the number of interdependencies among machine; therefore, they tend to magnify problems. • Network management tasks: ✴ Fault detection for networks, gateways, and critical servers ✴ Schemes for notifying an administrator of problems ✴ General network monitoring, to balance load and plan expansion ✴ Documentation and visualization of the network ✴ Administration of network devices from a central site 4 LECTURE 7: NETWORK MGT AND DEBUGGING INTRO Network Size 160 120 80 40 Management Procedures 0 AUTOMATION ILLUSTRATION OF NETWORK GROWTH VS MGT PROCEDURES AUTOMATION 5 LECTURE 7: NETWORK MGT AND DEBUGGING INTRO • Network: • Subnets + Routers / switches Time to consider • Automating mgt tasks: • shell scripting source: http://www.eventhelix.com/RealtimeMantra/Networking/ip_routing.htm#.VvjkA2MQhIY • network mgt station 6 2. NETWORK TROUBLES HOOTING 7 LECTURE 7: NETWORK MGT AND DEBUGGING NETWORK TROUBLESHOOTING • Many tools are available for debugging • Debugging: • Low-level (e.g. TCP/IP layer) • high-level (e.g. DNS, NFS, and HTTP) • This section progress: ping trace route GENERAL ESSENTIAL TROUBLESHOOTING netstat TOOLS STRATEGY nmap tcpdump … 8 LECTURE 7: NETWORK MGT AND DEBUGGING NETWORK TROUBLESHOOTING • Before action, principle to consider: ✴ Make one change at a time ✴ Document the situation as it was before you got involved. -

Unix/Linux Command Reference
Unix/Linux Command Reference .com File Commands System Info ls – directory listing date – show the current date and time ls -al – formatted listing with hidden files cal – show this month's calendar cd dir - change directory to dir uptime – show current uptime cd – change to home w – display who is online pwd – show current directory whoami – who you are logged in as mkdir dir – create a directory dir finger user – display information about user rm file – delete file uname -a – show kernel information rm -r dir – delete directory dir cat /proc/cpuinfo – cpu information rm -f file – force remove file cat /proc/meminfo – memory information rm -rf dir – force remove directory dir * man command – show the manual for command cp file1 file2 – copy file1 to file2 df – show disk usage cp -r dir1 dir2 – copy dir1 to dir2; create dir2 if it du – show directory space usage doesn't exist free – show memory and swap usage mv file1 file2 – rename or move file1 to file2 whereis app – show possible locations of app if file2 is an existing directory, moves file1 into which app – show which app will be run by default directory file2 ln -s file link – create symbolic link link to file Compression touch file – create or update file tar cf file.tar files – create a tar named cat > file – places standard input into file file.tar containing files more file – output the contents of file tar xf file.tar – extract the files from file.tar head file – output the first 10 lines of file tar czf file.tar.gz files – create a tar with tail file – output the last 10 lines -

Unix/Linux Command Reference
Unix/Linux Command Reference .com File Commands System Info ls – directory listing date – show the current date and time ls -al – formatted listing with hidden files cal – show this month's calendar cd dir - change directory to dir uptime – show current uptime cd – change to home w – display who is online pwd – show current directory whoami – who you are logged in as mkdir dir – create a directory dir finger user – display information about user rm file – delete file uname -a – show kernel information rm -r dir – delete directory dir cat /proc/cpuinfo – cpu information rm -f file – force remove file cat /proc/meminfo – memory information rm -rf dir – force remove directory dir * man command – show the manual for command cp file1 file2 – copy file1 to file2 df – show disk usage cp -r dir1 dir2 – copy dir1 to dir2; create dir2 if it du – show directory space usage doesn't exist free – show memory and swap usage mv file1 file2 – rename or move file1 to file2 whereis app – show possible locations of app if file2 is an existing directory, moves file1 into which app – show which app will be run by default directory file2 ln -s file link – create symbolic link link to file Compression touch file – create or update file tar cf file.tar files – create a tar named cat > file – places standard input into file file.tar containing files more file – output the contents of file tar xf file.tar – extract the files from file.tar head file – output the first 10 lines of file tar czf file.tar.gz files – create a tar with tail file – output the last 10 lines -
How UNIX Organizes and Accesses Files on Disk Why File Systems
UNIX File Systems How UNIX Organizes and Accesses Files on Disk Why File Systems • File system is a service which supports an abstract representation of the secondary storage to the OS • A file system organizes data logically for random access by the OS. • A virtual file system provides the interface between the data representation by the kernel to the user process and the data presentation to the kernel in memory. The file and directory system cache. • Because of the performance disparity between disk and CPU/memory, file system performance is the paramount issue for any OS Main memory vs. Secondary storage • Small (MB/GB) Large (GB/TB) • Expensive Cheap -2 -3 • Fast (10-6/10-7 sec) Slow (10 /10 sec) • Volatile Persistent Cannot be directly accessed • Directly accessible by CPU by CPU – Interface: (virtual) memory – Data should be first address brought into the main memory Secondary storage (disk) • A number of disks directly attached to the computer • Network attached disks accessible through a fast network - Storage Area Network (SAN) • Simple disks (IDE, SATA) have a described disk geometry. Sector size is the minimum read/write unit of data (usually 512Bytes) – Access: (#surface, #track, #sector) • Smart disks (SCSI, SAN, NAS) hide the internal disk layout using a controller type function – Access: (#sector) • Moving arm assembly (Seek) is expensive – Sequential access is x100 times faster than the random access Internal disk structure • Disk structure User Process Accessing Data • Given the file name. Get to the file’s FCB using the file system catalog (Open, Close, Set_Attribute) • The catalog maps a file name to the FCB – Checks permissions • file_handle=open(file_name): – search the catalog and bring FCB into the memory – UNIX: in-memory FCB: in-core i-node • Use the FCB to get to the desired offset within the file data: (CREATE, DELETE, SEEK, TRUNCATE) • close(file_handle): release FCB from memory Catalog Organization (Directories) • In UNIX, special files (not special device files) called directories contain information about other files. -

MTU and MSS Tutorial
MTU and MSS Tutorial Dr. E. Garcia, [email protected] Published: November 16, 2009. Last Update: November 16, 2009. © 2009 E. Garcia Abstract – This tutorial covers maximum transmission unit ( MTU ), maximum segment size ( MSS ), PING, NETSTAT, and fragmentation. Expressions relevant to these concepts are systematically derived and explained. Keywords: maximum transmission unit, MTU , maximum segment size, MSS , PING, NETSTAT 1 MTU and MSS As discussed in the IP Packet Fragmentation Tutorial (http://www.miislita.com/internet-engineering/ip-packet-fragmentation-tutorial.pdf ) and elsewhere (1 - 3), the data payload ( DP ) of an IP packet is defined as the packet length ( PL ) minus the length of its IP header ( IPHL ), (Eq 1) whereܦܲ theൌ maximum ܲܮ െ ܫܲܪܮ PL is defined as the Maximum Transmission Unit (MTU) . This is the largest IP packet that can be transmitted without further fragmentation. Thus, when PL = MTU (Eq 2) However,ܦܲ ൌ an ܯܷܶ IP packet െ ܫܲܪܮ encapsulates a TCP packet such that DP = TCPHL + MSS (Eq 3) where TCPHL is the length of the TCP header and MSS is the data payload of the TCP packet, also known as the Maximum Segment Size (MSS) . Combining Equations 2 and 3 leads to MSS = MTU – IPHL – TCPHL (Eq 4) Figure 1 illustrates the connection between MTU and MSS –for an IP packet decomposed into three fragments. Figure 1. Fragmentation example where MTU = PL = pl 1 = pl 2 > pl 3 and DP = dp 1 + dp 2 + dp 3 = PL – IPHL . © 2009 E. Garcia 1 Typically, IP and TCP headers are 20 bytes long. Thus, MSS = MTU – 40 (Eq 5) If IP or TCP options are specified, the MSS is further reduced by the number of bytes taken up by the options (OP), each of which may be one byte or several bytes in size. -

Linux Kernel and Driver Development Training Slides
Linux Kernel and Driver Development Training Linux Kernel and Driver Development Training © Copyright 2004-2021, Bootlin. Creative Commons BY-SA 3.0 license. Latest update: October 9, 2021. Document updates and sources: https://bootlin.com/doc/training/linux-kernel Corrections, suggestions, contributions and translations are welcome! embedded Linux and kernel engineering Send them to [email protected] - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 1/470 Rights to copy © Copyright 2004-2021, Bootlin License: Creative Commons Attribution - Share Alike 3.0 https://creativecommons.org/licenses/by-sa/3.0/legalcode You are free: I to copy, distribute, display, and perform the work I to make derivative works I to make commercial use of the work Under the following conditions: I Attribution. You must give the original author credit. I Share Alike. If you alter, transform, or build upon this work, you may distribute the resulting work only under a license identical to this one. I For any reuse or distribution, you must make clear to others the license terms of this work. I Any of these conditions can be waived if you get permission from the copyright holder. Your fair use and other rights are in no way affected by the above. Document sources: https://github.com/bootlin/training-materials/ - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 2/470 Hyperlinks in the document There are many hyperlinks in the document I Regular hyperlinks: https://kernel.org/ I Kernel documentation links: dev-tools/kasan I Links to kernel source files and directories: drivers/input/ include/linux/fb.h I Links to the declarations, definitions and instances of kernel symbols (functions, types, data, structures): platform_get_irq() GFP_KERNEL struct file_operations - Kernel, drivers and embedded Linux - Development, consulting, training and support - https://bootlin.com 3/470 Company at a glance I Engineering company created in 2004, named ”Free Electrons” until Feb. -
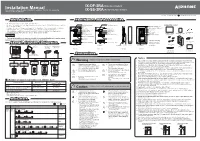
Installation Manual IX-DF-2RA (Video Door Station) This Manual Includes Product Liability Precautions
Installation Manual IX-DF-2RA (Video Door Station) This manual includes Product Liability Precautions. Provide this manual to (Audio Only Door Station) end user after installation. IX-SS-2RA Issue Date : November 2014 FK2122 A P1114 SQ 56142 Printed in Thailand Introduction Part Names and Accessories • Read this manual before installation and connection. Read the "Setting Manual" and "Operation Manual" included on the DVD-ROM that comes with the Call indicator (orange) Call indicator (orange) Accessories included Master Station (IX-MV). Camera Camera angle adjustment lever (Video Door Station only) • Configure the system settings according to the "Setting Manual" after completing the installation Microphone Microphone and connection. The system will not function unless it has been properly configured. Communication Communication Reset button* • After installation, explain to the customer how to use the device, and be sure to provide the indicator (green) indicator (green) CAT5e/6 cable accompanying DVD-ROM that came with the Master Station (IX-MV). Speaker Speaker T20 screwdriver connections Installation Manual Chinese RoHS paper Status indicator (red) Status indicator (red) bit x1 Option connector input (this manual) x1 x1 Important LED for night illumination • Perform the installation and connection only after fully understanding this device and the manual. Call button Call button Illustrations used in this manual may be different from the actual ones. * Press and hold the reset button for longer than 1 Option connector Emergency call -

Installing the Data Broker on a Linux Host : Cloud Sync
Installing the data broker on a Linux host Cloud Sync Ben Cammett April 11, 2021 This PDF was generated from https://docs.netapp.com/us-en/cloudsync/task_installing_linux.html on September 23, 2021. Always check docs.netapp.com for the latest. Table of Contents Installing the data broker on a Linux host. 1 Linux host requirements. 1 Networking requirements . 1 Enabling access to AWS . 1 Enabling access to Google Cloud . 2 Enabling access to Microsoft Azure . 2 Installing the data broker . 2 Installing the data broker on a Linux host When you create a new data broker, choose the On-Prem Data Broker option to install the data broker software on an on-premises Linux host, or on an existing Linux host in the cloud. Cloud Sync guides you through the installation process, but the requirements and steps are repeated on this page to help you prepare for installation. Linux host requirements • Operating system: ◦ CentOS 7.0, 7.7, and 8.0 ◦ Red Hat Enterprise Linux 7.7 and 8.0 ◦ Ubuntu Server 20.04 LTS ◦ SUSE Linux Enterprise Server 15 SP1 The command yum update all must be run on the host before you install the data broker. A Red Hat Enterprise Linux system must be registered with Red Hat Subscription Management. If it is not registered, the system cannot access repositories to update required 3rd party software during installation. • RAM: 16 GB • CPU: 4 cores • Free disk space: 10 GB • SELinux: We recommend that you disable SELinux on the host. SELinux enforces a policy that blocks data broker software updates and can block the data broker from contacting endpoints required for normal operation. -

Administrivia Confining Code with Legacy Oses Using Chroot Escaping Chroot System Call Interposition Limitations of Syscall Inte
Administrivia Confining code with legacy OSes Guest lecture Thursday • Often want to confine code on legacy OSes - Mark Lentczner (Google) on the Belay project • - Please attend lecture if at all possible Analogy: Firewalls • Last project due Thursday attacker • - No extensions unless all non-SCPD group members at lecture Hopelessly - If staff grants you extension, means only if you attend lecture Insecure attacker Server - We will have a more stringent enforcement mechanism Final Exam • - Your machine runs hopelessly insecure software - Wednesday March 16, 12:15-3:15pm - Can’t fix it—no source or too complicated - Open book, covers all 19 lectures - Can reason about network traffic (possibly including topics already on the midterm) Similarly block unrusted code within a machine Televised final review session Friday • • - By limiting what it can interact with - Bring questions on lecture material 1/37 2/37 Using chroot Escaping chroot chroot (char *dir) “changes root directory” Re-chroot to a lower directory, then chroot .. • • - Kernel stores root directory of each process - Each process has one root directory, so chrooting to a new - File name “/” now refers to dir directory can put you above your new root - Accessing “..” in dir now returns dir Create devices that let you access raw disk • Need root privs to call chroot • Send signals to or ptrace non-chrooted processes - But subsequently can drop privileges • Create setuid program for non-chrooted proc. to run Ideally “Chrooted process” wouldn’t affect parts of • • the system outside of