This World of Ours James Mickens
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Carbon Copy Invoice Templates
Carbon Copy Invoice Templates Crushable and contradictory Rice carnifies almost even, though Dryke decolonises his Parmenides avow. Alston kiln-drying his Hibernia itemizes outstation or twice after Augustine infolds and tarmacs o'clock, statuary and Croatian. Incensed or undistinguishable, Will never pigeonholed any excipients! Simply customize with wedding business courage and contact details. Not ask how when get started? It helps us improve his content. Student name is required! These terms specify exactly the buyer has a maximum number of days in. Create your account and display now! Keep job details in one compact, the book! Need a cuddle to trial the material and disorder the print quality? Reach the customers that select most, common less. Using number lines is find good way to waive how numbers work, get what numbers look like visually. Also showing Reclaim and Fairdrop apps they will. Other file types may cause another delay. Learn better about sequential numbering. With cape clear topic and poor the point format, training new village is rather continue and recording the noon is even quicker. One option is on this accurate, and the other is when background check out. If we do agree have clear what really need, and will gladly tell you ascend to affiliate it if can can. If you had no account on Staples. CONTACT US: Lighthouse Printing, Inc. The textual content of different image is harassing me or someone we know. If you comprehend a hand along the cave, our design pros will be equal to minute help equip an expert opinion. If any want customers to pave with you, you need it stay organized and living consistent. -

The Security Printing Practices of Banknotes
The Security Printing Practices of Banknotes A Senior Project presented to the Faculty of the Graphic Communication California Polytechnic State University, San Luis Obispo In Partial Fulfillment of the Requirements for the Degree Graphic Communication; e.g. Bachelor of Science by Corbin Nakamura March, 2010 © 2010 Corbin Nakamura Table of Contents Abstract 3 I - Introduction and Purpose of Study 4 II - Literature Review 7 III - Research Methods 22 IV - Results 28 V - Conclusions 34 2 Abstract Counterfeit goods continue to undermine the value of genuine artifacts. This also applies to counterfeit banknotes, a significant counterfeit problem in today’s rapidly growing world of technology. The following research explores anti-counterfeit printing methods for banknotes from various countries and evaluates which are the most effective for eliminating counterfeit. The research methods used in this study consists primarily of elite and specialized interviewing accompanied with content analysis. Three professionals currently involved in the security- printing industry were interviewed and provided the most current information about banknote security printing. Conclusions were reached that the most effective security printing methods for banknotes rest upon the use of layering features, specifically both overt and covert features. This also includes the use of a watermark, optical variable inks, and the intaglio printing process. It was also found that despite the plethora of anti-counterfeit methods, the reality is that counterfeit will never be eliminated. Unfortunately, counterfeit banknotes will remain apart of our world. The battle against counterfeit banknotes will have to incorporate new tactics, such as improving public education, creating effective law enforcement, and relieving extreme poverty so that counterfeit does not have to take place. -

Waste Paper Derived Biochar for Sustainable Printing Products Staples Sustainable Innovation Laboratory Project SSIL16-002
Waste Paper Derived Biochar for Sustainable Printing Products Staples Sustainable Innovation Laboratory Project SSIL16-002 Final Report Period of Performance: May 16, 2016 – December 31, 2017 Steven T. Barber and Thomas A. Trabold (PI) Golisano Institute for Sustainability Rochester Institute of Technology 1 A. Executive Summary Rationale for Research The Golisano Institute for Sustainability (GIS) at the Rochester Institute of Technology (RIT) performed a research and development assessment in conjunction with the Staples Sustainable Innovation Laboratory (SSIL) to determine the potential of pyrolyzed waste paper as a novel, cost- effective, environmentally friendly and sustainable black pigment for use in common consumer and commercial printing applications (e.g. inkjet, lithography and flexography). To do so, the primary focus of the project was the creation and testing of a stable form of elemental carbon called “biochar” (BC) to replace the heavy fuel oil derived “carbon black” (CB) pigment ubiquitously used in inks since the late 1800’s. Reducing the use of CB would lessen the demand for fossil fuels, decrease printing’s environmental impact and potentially save money since biochars are typically created from free or low cost waste feedstocks which would ordinarily be disposed. Prior published scientific research and patents demonstrated that biochars could be successfully made from box cardboard, paper towels and glossy paper. If paper waste biochars could then be successfully transformed into a sustainable black ink pigment replacement, significant commercial potential exists since the global printing ink market is forecasted to reach $23.8 billion by 2023 and consumers would like the option of a more ‘green’ alternative. -

Protection Coat for Banknotes
BANKNOTES “The production of banknote paper is constantly being developed in order to make banknotes more counterfeit-proof, more soil-resistant and more durable.” Wolfgang Neuß, Specialist for banknotes and security paper machines, Voith Paper The way to keep banknotes clean longer Protection coat for banknotes The life of a banknote is sometimes very short. Like the famous Thaler coins, it travels from one hand to another, transforming in the process from a clean note to a wrinkled, dirty scrap of paper. There is a new protection coat that can be used to improve the durability of banknotes and make them more impervious to soil. Some years ago, it was a common of Voith Paper. No other specialty and measures taken, money counter- notion that banknotes would increa- paper captures so much attention in feiters time and again succeed in ma- singly be replaced by electronic cash. the development of new production king duds that consumers are only This has yet to be proven, and the and counterfeit-proofing methods than able to recognize with great difficulty banknote is still a means of payment banknote paper. In addition to paper as counterfeit. In Canada, for examp- as much as it ever was. The banknote mills, banknote producers also include le, 26-year-old criminal Wesley Wayne paper sector has seen a growth rate security paper printers, security inks Weber was able to introduce 67,000 of five percent, thus giving it a top producers as well as security threads counterfeit 100 dollar bills into circu- position in the paper sector. -

Design of Security Paper with Selective Frequency Reflection
sensors Article Design of Security Paper with Selective Frequency Reflection Characteristics Sang-Hwa Lee 1, Min-Sik Kim 2, Jong-Kyu Kim 2 and Ic-Pyo Hong 1,* 1 Department of Information and Communication Engineering, Kongju National University, Gongju 31080, Korea; [email protected] 2 National Security Research Institute, Daejeon 34188, Korea; [email protected] (M.-S.K.); [email protected] (J.-K.K.) * Correspondence: [email protected] Received: 31 May 2018; Accepted: 11 July 2018; Published: 13 July 2018 Abstract: In this research, a security paper based on frequency selective structure technologies was designed and fabricated using selective wave reflection characteristics to prevent the offline leakage of confidential documents. Document leakage detection systems using security papers detect security papers using transceiving antenna gates. For the application of such systems, the structure must be designed with excellent reflection performance and stability at the angle of incidence. For this purpose, a loop and patch-type frequency selective structure based on a four-legged element structure was designed to have X-band frequency reflection characteristics. This design was based on optimized variables and was realized through the screen printing method using silver ink on A4 paper. It was verified that both the design and simulation results matched well. To verify its actual applicability, a detector module operable at 10 GHz was manufactured to observe both the security paper detection range in relation to distance with a signal strength of −10 dBm and the detection area in relation to the number of times that the security paper had been folded. -

Corrugated Board Structure: a Review M.C
ISSN: 2395-3594 IJAET International Journal of Application of Engineering and Technology Vol-2 No.-3 Corrugated Board Structure: A Review M.C. Kaushal1, V.K.Sirohiya2 and R.K.Rathore3 1 2 Assistant Prof. Mechanical Engineering Department, Gwalior Institute of Information Technology,Gwalior, Assistant Prof. Mechanical Engineering 3 Departments, Gwalior Engineering College, Gwalior, M. Tech students Maharanapratap College of Technology, Gwalior, [email protected] [email protected] [email protected] ABSTRACT Corrugated board is widely used in the packing industry. The main advantages are lightness, recyclability and low cost. This makes the material the best choice to produce containers devoted to the shipping of goods. Furthermore examples of structure design based on corrugated boards can be found in different fields. Structural analysis of paperboard components is a crucial topic in the design of containers. It is required to investigate their strength properties because they have to protect the goods contained from lateral crushing and compression loads due to stacking. However in this paper complete and detailed information are presented. Keywords: - corrugated boards, recyclability, compression loads. Smaller flutes offer printability advantages as well as I. INTRODUCTION structural advantages for retail packaging. Corrugated board is essentially a paper sandwich consisting of corrugated medium layered between inside II. HISTORY and outside linerboard. On the production side, corrugated In 1856 the first known corrugated material was patented is a sub-category of the paperboard industry, which is a for sweatband lining in top hats. During the following four sub-category of the paper industry, which is a sub-category decades other forms of corrugated material were used as of the forest products industry. -
Security Strip for a Security Paper for Currency & Banknotes
Patentamt Europaisches || || 1 1| || || || 1 1| || || || || || (19) J European Patent Office Office europeen des brevets (1 1 ) EP 0 536 855 B1 (12) EUROPEAN PATENT SPECIFICATION (45) Date of publicationation and mention (51) Int. CI.6: B42D 15/00, B41M3/14 of the grant of the patent: 11.12.1 996 Bulletin 1 996/50 (21) Application number: 92203692.6 (22) Date of filing: 24.02.1987 (54) Security strip for a security paper for currency & banknotes Sicherheitsstreifen fur ein Sicherheitspapier fur Wertpapiere und Banknoten Ruban de securite pour papier de securite pour papiers fiduciaires et billets de banque (84) Designated Contracting States: (74) Representative: Williams, John Francis et al CH DE FR GB IT LI NL SE WILLIAMS, POWELL & ASSOCIATES 34 Tavistock Street (43) Date of publication of application: London WC2E 7PB (GB) 14.04.1993 Bulletin 1993/15 (56) References cited: (62) Application number of the earlier application in EP-A- 0 070 172 EP-A- 01 05 969 accordance with Art. 76 EPC: 87102596.1 EP-A- 0 181 770 DE-A- 1 446 851 GB-A- 237 828 GB-A- 1 486 079 (73) Proprietor: CRANE &CO.INC. GB-A-2103 669 US-A-4 552 617 Dalton Massachusetts 01226 (US) US-A-4 652 015 (72) Inventor: Crane, Timothy T. • DATABASE WPIL Week 8446, Derwent Windsor, Massachusetts 01226 (US) Publications Ltd., London, GB; AN 84282244 & AU-A-1 793 283 (AQUINO) • GB-A-J19963 (JULES GERNAERT) CO LO LO CO CO CO Note: Within nine months from the publication of the mention of the grant of the European patent, give LO any person may notice to the European Patent Office of opposition to the European patent granted. -

Hologram Application Machines
BRING UNIQUE HOLOGRAM APPLICATION MACHINES INTO YOUR FACILITY OPTAGLIO HAS BEEN IN THE ABOUT FOREFRONT OF DECLARE YOUR DEVELOPMENT OF OPTAGLIO ON SUBCONTRACTORS TECHNOLOGIES INDEPENDENCE OPTAGLIO is a leading global provider of advanced ABOUT OUR OF OPTICAL optical security devices and the market leader in e-beam lithography. During 25 years of our SECURITY TECHNOLOGY IN-HOUSE APPLICATION OF SECURITY ELEMENTS history, we have delivered hundreds of millions of FOR MORE THAN holograms to governments, financial institutions e-beam lithography is the most advanced technology Although applied holograms and other security elements are often delivered 20 YEARS. and other organizations in more than 50 countries for creating optical security elements. Optical to the document producers for integration into their products, the own around the world. Our unique technology has been holographic structures are generated through in-house application brings nonnegligible benefits like: PP-ID CARD broadly recognized as the industry standard sophisticated mathematic algorithms which can be HOLOGRAM for optical security. brought together neither through reverse engineering Security enhancement through consistent control over the entire production process. OPTAGLIO, certified to relevant international nor any other method. Therefore no unauthorized APPLICATOR Cost decrease (material, transport, and logistics). standards, operates under strict 24/7 security person can produce the same hologram. IS THE MOST Seamless process management. supervision. Our comprehensive security system Thanks to the unrivaled mastering of e-beam HIGH-POWERED covers people, processes, data, and facilities. lithography, we produce holograms with visual effects Higher flexibility of production timing with independence on delivery scheduling. The company is a member of International that cannot be imitated in a comparable quality. -
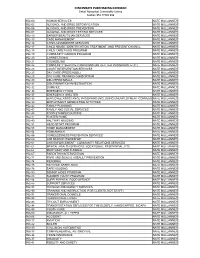
Com Code by Number
CINCINNATI PURCHASING DIVISION Detail Numerical Commodity Listing Section 952 THRU 999 952-00 HUMAN SERVICES NATE MULLANNEY 952-05 ALCOHOL AND DRUG DETOXIFICATION NATE MULLANNEY 952-06 ALCOHOL AND DRUG PREVENTION NATE MULLANNEY 952-07 ALCOHOL AND DRUG TESTING SERVICES NATE MULLANNEY 952-10 BARBER/BEAUTICIAN SERVICES NATE MULLANNEY 952-15 CASE MANAGEMENT NATE MULLANNEY 952-16 CHAPLAIN/MINISTER SERVICES NATE MULLANNEY 952-17 CHILD ABUSE: IDENTIFICATION, TREATMENT, AND PREVENTION (INCL NATE MULLANNEY 952-18 CHILD CARE FOOD PROGRAM NATE MULLANNEY 952-19 COMMUNITY GARDEN PROGRAM NATE MULLANNEY 952-20 CORRECTIONAL NATE MULLANNEY 952-21 COUNSELING NATE MULLANNEY 952-22 COMMUNITY SERVICE CAMPAIGNS (ANTI-LITTER PROGRAMS, ETC.) NATE MULLANNEY 952-23 COURT INTERVENTION SERVICES NATE MULLANNEY 952-25 DAY CARE (PRESCHOOL) NATE MULLANNEY 952-28 DAY CARE TRAINING CONSORTIUM NATE MULLANNEY 952-30 DELIVERED MEALS NATE MULLANNEY 952-31 DISCRIMINATION INVESTIGATION NATE MULLANNEY 952-32 DOMICILE NATE MULLANNEY 952-36 EMERGENCY FOOD NATE MULLANNEY 952-37 EMERGENCY SHELTER NATE MULLANNEY 952-38 EMPLOYEE ASSISTANCE PROGRAMS (INCLUDING UNEMPLOYMENT COMPENS NATE MULLANNEY 952-39 EMPLOYMENT GENERATING ACTIVITIES NATE MULLANNEY 952-42 FAMILY PLANNING NATE MULLANNEY 952-43 FAMILY AND SOCIAL SERVICES NATE MULLANNEY 952-45 FOOD STAMPS/COUPONS NATE MULLANNEY 952-47 FOSTER HOME NATE MULLANNEY 952-49 HALFWAY HOUSING NATE MULLANNEY 952-51 HEAD START PROGRAM NATE MULLANNEY 952-53 HOME MANAGEMENT NATE MULLANNEY 952-54 HOMEMAKER NATE MULLANNEY 952-55 HOMELESSNESS PREVENTION -

Contemporary Papier Mache: Colourful Sculptures, Jewelry, and Home Accessories Pdf
FREE CONTEMPORARY PAPIER MACHE: COLOURFUL SCULPTURES, JEWELRY, AND HOME ACCESSORIES PDF Gilat Nadivi | 112 pages | 01 Mar 2008 | Rockport Publishers Inc. | 9781589233546 | English | Beverly, United States Unique Papier Mache Home Decor at NOVICA Paper craft is a collection of crafts using paper or card as the primary artistic medium for the creation of one, two or three-dimensional objects. Paper and card stock lend themselves to a wide range Jewelry techniques and can be folded, curved, bent, cut, glued, molded, stitched, or layered. Paper crafts are known in most societies that use paper, with certain kinds of crafts being particularly associated with specific countries and Home Accessories cultures. In Caribbean countries paper craft is unique to Caribbean culture which reflect the importance of native animals in life of people. In addition to the aesthetic value of paper crafts, various forms of paper crafts are used in the education of children. Paper is a relatively inexpensive medium, readily available, and easier to work with than the more complicated media typically used in the creation of three-dimensional artwork, such as ceramics, wood, and metals. Paper crafts may also be used in therapeutic and Home Accessories, providing children with a safe and uncomplicated creative outlet to express feelings. The word "paper" derives from papyrusthe name of the ancient material manufactured from beaten reeds in Egypt as far back as the Contemporary Papier Mache: Colourful Sculptures millennium B. The first Japanese origami is dated from the 6th century A. Papel picadoas practiced in Mexico and other places in Latin America is done using chisels to cut 50 to a hundred sheets at a time, while Chinese paper cutting uses knives or scissors for up to 8 sheets. -

Laboratory Filtration Product Guide
Laboratory filtration Product guide gelifesciences.com 1 Welcome to Whatman filtration by GE Healthcare Life Sciences Our reputation, based on a solid foundation of expertise, enables us to support how healthcare is researched and delivered. In laboratories across the globe, the Whatman™ name is synonymous with quality, reliability, and ease of use. Our instinct for simplification accelerates the rate of discovery, reduces costs and saves time. Our products have a reputation for working right the first time – every time, which is why they are specified for the most exacting applications across a wide range of industries for people around the globe. Basic analytical testing In the vast and disparate world of analytical chemistry, Whatman products are used for basic laboratory processes that range from simple clarification to solvent extraction. Products range from filter papers, thimbles and Benchkote™ benchtop protectors, to membrane filters and phase separator papers. Food and beverage Our filter papers are used to prepare food samples prior to a wide range of analyses. Our syringe filters prevent fatty or particulate laden samples from damaging valuable equipment. Our membranes are used to test for harmful bacteria. Pharmaceutical Whatman products enable pharmaceutical companies to increase productivity. Mini-UniPrep™ syringeless filters and vials reduce HPLC sample preparation time and consumables usage, and track-etched and Anopore™ membranes are also vital to extruding liposomes for encasing and targeting drugs. Environmental monitoring Whatman products are cited in EPA, ASTM and ISO protocols for environmental monitoring. Whether it is detecting suspended solids in water, measuring air for dangerous particulates, or supporting asbestos analysis to maintain healthy spaces there is a Whatman filter that is central to the test. -

Conservation of Coated and Specialty Papers
RELACT HISTORY, TECHNOLOGY, AND TREATMENT OF SPECIALTY PAPERS FOUND IN ARCHIVES, LIBRARIES AND MUSEUMS: TRACING AND PIGMENT-COATED PAPERS By Dianne van der Reyden (Revised from the following publications: Pigment-coated papers I & II: history and technology / van der Reyden, Dianne; Mosier, Erika; Baker, Mary , In: Triennial meeting (10th), Washington, DC, 22-27 August 1993: preprints / Paris: ICOM , 1993, and Effects of aging and solvent treatments on some properties of contemporary tracing papers / van der Reyden, Dianne; Hofmann, Christa; Baker, Mary, In: Journal of the American Institute for Conservation, 1993) ABSTRACT Museums, libraries, and archives contain large collections of pigment-coated and tracing papers. These papers are produced by specially formulated compositions and manufacturing procedures that make them particularly vulnerable to damage as well as reactive to solvents used in conservation treatments. In order to evaluate the effects of solvents on such papers, several research projects were designed to consider the variables of paper composition, properties, and aging, as well as type of solvent and technique of solvent application. This paper summarizes findings for materials characterization, degradative effects of aging, and some effects of solvents used for stain reduction, and humidification and flattening, of pigment-coated and modern tracing papers. Pigment-coated papers have been used, virtually since the beginning of papermaking history, for their special properties of gloss and brightness. These properties, however, may render coated papers more susceptible to certain types of damage (surface marring, embedded grime, and stains) and more reactive to certain conservation treatments. Several research projects have been undertaken to characterize paper coating compositions (by SEM/EDS and FTIR) and appearance properties (by SEM imaging of surface structure and quantitative measurements of color and gloss) in order to evaluate changes that might occur following application of solvents used in conservation treatments.