RISC-V Instructions and How to Implement Functions
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Strict Protection for Virtual Function Calls in COTS C++ Binaries
vfGuard: Strict Protection for Virtual Function Calls in COTS C++ Binaries Aravind Prakash Xunchao Hu Heng Yin Department of EECS Department of EECS Department of EECS Syracuse University Syracuse University Syracuse University [email protected] [email protected] [email protected] Abstract—Control-Flow Integrity (CFI) is an important se- these binary-only solutions are unfortunately coarse-grained curity property that needs to be enforced to prevent control- and permissive. flow hijacking attacks. Recent attacks have demonstrated that existing CFI protections for COTS binaries are too permissive, While coarse-grained CFI solutions have significantly re- and vulnerable to sophisticated code reusing attacks. Accounting duced the attack surface, recent efforts by Goktas¸¨ et al. [9] for control flow restrictions imposed at higher levels of semantics and Carlini [10] have demonstrated that coarse-grained CFI is key to increasing CFI precision. In this paper, we aim to provide solutions are too permissive, and can be bypassed by reusing more stringent protection for virtual function calls in COTS large gadgets whose starting addresses are allowed by these C++ binaries by recovering C++ level semantics. To achieve this solutions. The primary reason for such permissiveness is the goal, we recover C++ semantics, including VTables and virtual lack of higher level program semantics that introduce certain callsites. With the extracted C++ semantics, we construct a sound mandates on the control flow. For example, given a class CFI policy and further improve the policy precision by devising two filters, namely “Nested Call Filter” and “Calling Convention inheritance, target of a virtual function dispatch in C++ must Filter”. -
Tricore Architecture Manual for a Detailed Discussion of Instruction Set Encoding and Semantics
User’s Manual, v2.3, Feb. 2007 TriCore 32-bit Unified Processor Core Embedded Applications Binary Interface (EABI) Microcontrollers Edition 2007-02 Published by Infineon Technologies AG 81726 München, Germany © Infineon Technologies AG 2007. All Rights Reserved. Legal Disclaimer The information given in this document shall in no event be regarded as a guarantee of conditions or characteristics (“Beschaffenheitsgarantie”). With respect to any examples or hints given herein, any typical values stated herein and/or any information regarding the application of the device, Infineon Technologies hereby disclaims any and all warranties and liabilities of any kind, including without limitation warranties of non- infringement of intellectual property rights of any third party. Information For further information on technology, delivery terms and conditions and prices please contact your nearest Infineon Technologies Office (www.infineon.com). Warnings Due to technical requirements components may contain dangerous substances. For information on the types in question please contact your nearest Infineon Technologies Office. Infineon Technologies Components may only be used in life-support devices or systems with the express written approval of Infineon Technologies, if a failure of such components can reasonably be expected to cause the failure of that life-support device or system, or to affect the safety or effectiveness of that device or system. Life support devices or systems are intended to be implanted in the human body, or to support and/or maintain and sustain and/or protect human life. If they fail, it is reasonable to assume that the health of the user or other persons may be endangered. User’s Manual, v2.3, Feb. -
IAR C/C++ Compiler Reference Guide for V850
IAR Embedded Workbench® IAR C/C++ Compiler Reference Guide for the Renesas V850 Microcontroller Family CV850-9 COPYRIGHT NOTICE © 1998–2013 IAR Systems AB. No part of this document may be reproduced without the prior written consent of IAR Systems AB. The software described in this document is furnished under a license and may only be used or copied in accordance with the terms of such a license. DISCLAIMER The information in this document is subject to change without notice and does not represent a commitment on any part of IAR Systems. While the information contained herein is assumed to be accurate, IAR Systems assumes no responsibility for any errors or omissions. In no event shall IAR Systems, its employees, its contractors, or the authors of this document be liable for special, direct, indirect, or consequential damage, losses, costs, charges, claims, demands, claim for lost profits, fees, or expenses of any nature or kind. TRADEMARKS IAR Systems, IAR Embedded Workbench, C-SPY, visualSTATE, The Code to Success, IAR KickStart Kit, I-jet, I-scope, IAR and the logotype of IAR Systems are trademarks or registered trademarks owned by IAR Systems AB. Microsoft and Windows are registered trademarks of Microsoft Corporation. Renesas is a registered trademark of Renesas Electronics Corporation. V850 is a trademark of Renesas Electronics Corporation. Adobe and Acrobat Reader are registered trademarks of Adobe Systems Incorporated. All other product names are trademarks or registered trademarks of their respective owners. EDITION NOTICE Ninth edition: May 2013 Part number: CV850-9 This guide applies to version 4.x of IAR Embedded Workbench® for the Renesas V850 microcontroller family. -

Lecture 21: Calling Conventions Menu Calling Convention Calling Convention X86 C Calling Convention
CS216: Program and Data Representation University of Virginia Computer Science Spring 2006 David Evans Menu Lecture 21: Calling Conventions • x86 C Calling Convention • Java Byte Code Wizards http://www.cs.virginia.edu/cs216 UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 2 Calling Convention Calling Convention • Rules for how the caller and the Caller Callee callee make subroutine calls • Where to put • Where to find • Caller needs to know: params params • What registers can I • What registers – How to pass parameters assume are same must I not bash – What registers might be bashed by • Where to find result • Where to put result called function • State of stack • State of stack – What is state of stack after return – Where to get result UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 3 UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 4 Calling Convention: x86 C Calling Convention Easiest for Caller Caller Callee Caller Callee • Where to put • Where to find • Params on stack in • Find params on stack params params reverse order in reverse order • What registers can I • What registers • Can assume EBX, • Must not bash EBX, assume are same must I not bash EDI and ESI are EDI or ESI – All of them – None of them same • Put result in EAX • Where to find result • Where to put result • Find result in EAX • Stack rules next • State of stack • State of stack • Stack rules next Need to save and Need to save and restore restore EBX, EDI (EAX), ECX, EDX and ESI UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 5 UVa CS216 -
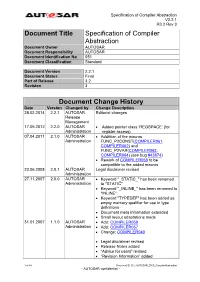
Specification of Compiler Abstraction
Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Document Title Specification of Compiler Abstraction Document Owner AUTOSAR Document Responsibility AUTOSAR Document Identification No 051 Document Classification Standard Document Version 2.2.1 Document Status Final Part of Release 3.2 Revision 3 Document Change History Date Version Changed by Change Description 28.02.2014 2.2.1 AUTOSAR Editorial changes Release Management 17.05.2012 2.2.0 AUTOSAR Added pointer class ‘REGSPACE’ (for Administration register access) 07.04.2011 2.1.0 AUTOSAR Addtition of the macros Administration FUNC_P2CONST(COMPILER061, COMPILER062) and FUNC_P2VAR(COMPILER063, COMPILER064) (see bug #43874) Rework of COMPILER058 to be compatible to the added macros 23.06.2008 2.0.1 AUTOSAR Legal disclaimer revised Administration 27.11.2007 2.0.0 AUTOSAR Keyword "_STATIC_" has been renamed Administration to "STATIC" Keyword "_INLINE_" has been renamed to "INLINE" Keyword "TYPEDEF" has been added as empty memory qualifier for use in type definitions Document meta information extended Small layout adaptations made 31.01.2007 1.1.0 AUTOSAR Add: COMPILER058 Administration Add: COMPILER057 Change: COMPILER040 Legal disclaimer revised Release Notes added “Advice for users” revised “Revision Information” added 1 of 44 Document ID 051: AUTOSAR_SWS_CompilerAbstraction - AUTOSAR confidential - Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Document Change History Date Version Changed by Change Description 27.04.2006 1.0.0 AUTOSAR Initial Release Administration 2 of 44 Document ID 051: AUTOSAR_SWS_CompilerAbstraction - AUTOSAR confidential - Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Disclaimer This specification and the material contained in it, as released by AUTOSAR is for the purpose of information only. -
EECS 373 Design of Microprocessor-Based Systems
Procedures Procedures are very important for writing reusable and maintainable code in assembly and high-level languages. How are they implemented? · Application Binary Interfaces · Calling Conventions · Recursive Calls · Examples Reference: PowerPC Embedded ABI General Concepts · Caller: The calling procedure Callee: The procedure called by the caller ¼ int mult(x, y) prod = mult (a, b) ¼ ¼ return (x * y) · Caller and callee must agree on: · How to pass parameters · How to return the return value(s), if any · How to maintain relevant information across calls · PowerPC architecture does not define ªagreementº. Instead, common policies are defined by convention. PowerPC Features The PowerPC ISA provides the following features to support procedure/function calls: · link register (p. 2-11) · bl: branch and link (p. 4-41) · blr: branch to link register (Table F-4) A Very Simple Calling Convention · Passing arguments · Use GPRs r3 to r10 in order · Use stack in main memory if more than 8 arguments · Passing return value · Leave result in r3 Example int func(int a, int b) { return (a + b); } main { ¼ func(5,6); ¼ } Another Example int func2(int a, int b) { return func(a , b); } main { ¼ func2(5,6); ¼ } The Stack · Information for each function invocation (e.g. link register) is saved on the call stack or simply stack. · Each function invocation has its own stack frame (a.k.a. activation record ). high address func2 stack frame func stack frame stack pointer low address Using the Stack main ¼ Describe the stack and LR contents ¼ · right before -

“Option Summary” in Using the GNU Compiler Collection (GCC)
Using the GNU Compiler Collection For gcc version 4.3.6 (GCC) Richard M. Stallman and the GCC Developer Community Published by: GNU Press Website: www.gnupress.org a division of the General: [email protected] Free Software Foundation Orders: [email protected] 51 Franklin Street, Fifth Floor Tel 617-542-5942 Boston, MA 02110-1301 USA Fax 617-542-2652 Last printed October 2003 for GCC 3.3.1. Printed copies are available for $45 each. Copyright c 1988, 1989, 1992, 1993, 1994, 1995, 1996, 1997, 1998, 1999, 2000, 2001, 2002, 2003, 2004, 2005, 2006, 2007 2008 Free Software Foundation, Inc. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with the Invariant Sections being “GNU General Public License” and “Funding Free Software”, the Front-Cover texts being (a) (see below), and with the Back-Cover Texts being (b) (see below). A copy of the license is included in the section entitled “GNU Free Documentation License”. (a) The FSF’s Front-Cover Text is: A GNU Manual (b) The FSF’s Back-Cover Text is: You have freedom to copy and modify this GNU Manual, like GNU software. Copies published by the Free Software Foundation raise funds for GNU development. i Short Contents Introduction ............................................. 1 1 Programming Languages Supported by GCC ............... 3 2 Language Standards Supported by GCC .................. 5 3 GCC Command Options ............................... 9 4 C Implementation-defined behavior ..................... 237 5 Extensions to the C Language Family .................. -
System Calls
System Calls 1 Learning Outcomes • A high-level understanding of System Calls – Mostly from the user’s perspective • From textbook (section 1.6) • Exposure architectural details of the MIPS R3000 – Detailed understanding of the of exception handling mechanism • From “Hardware Guide” on class web site • Understanding of the existence of compiler function calling conventions – Including details of the MIPS ‘C’ compiler calling convention • Understanding of how the application kernel boundary is crossed with system calls in general • Including an appreciation of the relationship between a case study (OS/161 system call handling) and the general case. 2 Operating System System Calls Kernel Level Operating System Requests Applications (System Calls) User Level Applications Applications 3 System Calls • Can be viewed as special function calls – Provides for a controlled entry into the kernel – While in kernel, they perform a privileged operation – Returns to original caller with the result • The system call interface represents the abstract machine provided by the operating system. 4 A Brief Overview of Classes System Calls • From the user’s perspective – Process Management – File I/O – Directories management – Some other selected Calls – There are many more • On Linux, see man syscalls for a list 5 Some System Calls For Process Management 6 Some System Calls For File Management 7 Some System Calls For Directory Management 8 Some System Calls For Miscellaneous Tasks 9 System Calls • A stripped down shell: while (TRUE) { /* repeat forever */ -

System V Application Binary Interface AMD64 Architecture Processor Supplement Draft Version 0.99.4
System V Application Binary Interface AMD64 Architecture Processor Supplement Draft Version 0.99.4 Edited by Michael Matz1, Jan Hubickaˇ 2, Andreas Jaeger3, Mark Mitchell4 January 13, 2010 [email protected] [email protected] [email protected] [email protected] AMD64 ABI Draft 0.99.4 – January 13, 2010 – 15:33 Contents 1 Introduction 8 2 Software Installation 9 3 Low Level System Information 10 3.1 Machine Interface . 10 3.1.1 Processor Architecture . 10 3.1.2 Data Representation . 10 3.2 Function Calling Sequence . 14 3.2.1 Registers and the Stack Frame . 14 3.2.2 The Stack Frame . 15 3.2.3 Parameter Passing . 16 3.3 Operating System Interface . 23 3.3.1 Exception Interface . 23 3.3.2 Virtual Address Space . 23 3.3.3 Page Size . 23 3.3.4 Virtual Address Assignments . 23 3.4 Process Initialization . 26 3.4.1 Initial Stack and Register State . 26 3.4.2 Thread State . 29 3.4.3 Auxiliary Vector . 29 3.5 Coding Examples . 31 3.5.1 Architectural Constraints . 32 3.5.2 Conventions . 34 3.5.3 Position-Independent Function Prologue . 35 3.5.4 Data Objects . 36 3.5.5 Function Calls . 44 3.5.6 Branching . 46 1 AMD64 ABI Draft 0.99.4 – January 13, 2010 – 15:33 3.5.7 Variable Argument Lists . 49 3.6 DWARF Definition . 54 3.6.1 DWARF Release Number . 55 3.6.2 DWARF Register Number Mapping . 55 3.7 Stack Unwind Algorithm . 55 4 Object Files 59 4.1 ELF Header . -

Introduction to Intel X86-64 Assembly, Architecture, Applications, & Alliteration
Introduction to Intel x86-64 Assembly, Architecture, Applications, & Alliteration Xeno Kovah – 2014-2015 [email protected] All materials is licensed under a Creative Commons “Share Alike” license. • http://creativecommons.org/licenses/by-sa/3.0/ Attribution condition: You must indicate that derivative work "Is derived from Xeno Kovah's 'Intro x86-64’ class, available at http://OpenSecurityTraining.info/IntroX86-64.html” Attribution condition: You must indicate that derivative work "Is derived from Xeno Kovah's ‘Intro x86-64’ class, available at http://OpenSecurityTraining.info/IntroX86-64.html" The Stack • The stack is a conceptual area of main memory (RAM) which is designated by the OS when a program is started. – Different OS start it at different addresses by their own convention • A stack is a Last-In-First-Out (LIFO/FILO) data structure where data is "pushed" on to the top of the stack and "popped" off the top. • By convention the stack grows toward lower memory addresses. Adding something to the stack means the top of the stack is now at a lower memory address. Book page107 The Stack 2 • As already mentioned, RSP points to the top of the stack, the lowest address which is being used – While data will exist at addresses beyond the top of the stack, it is considered undefined • The stack keeps track of which functions were called before the current one, it holds local variables and is often used to pass arguments to the next function to be called. • A firm understanding of what is happening on the stack is *essential* to understanding a program’s operation. -

Calling Conventions for Different C++ Compilers and Operating Systems
5. Calling conventions for different C++ compilers and operating systems By Agner Fog. Copenhagen University College of Engineering. Copyright © 2004 - 2012. Last updated 2012-02-29. Contents 1 Introduction ....................................................................................................................... 3 2 The need for standardization............................................................................................. 5 3 Data representation...........................................................................................................6 4 Data alignment .................................................................................................................. 8 5 Stack alignment................................................................................................................. 9 6 Register usage ................................................................................................................10 6.1 Can floating point registers be used in 64-bit Windows? ........................................... 13 6.2 YMM vector registers................................................................................................ 14 6.3 Register usage in kernel code................................................................................... 14 7 Function calling conventions ........................................................................................... 16 7.1 Passing and returning objects.................................................................................. -
Calling Conventions and the Stack CS2253 Owen Kaser, UNBSJ
Calling Conventions and the Stack CS2253 Owen Kaser, UNBSJ Overview ● Stacks and the Load/Store Multiple Instructions ● Subroutines ● ARM Application Procedure Call Standard – Code Linkage Mechanism – Parameter Passing – Caller- and Callee-Save Registers ● See Chapter 13 of textbook Stack in Memory ● Recall from CS1083 (or CS2383) that one can use an array to store a stack's data. Also need an integer array index, called TOP. ● Push(value) → Data[++TOP] = value; ● Pop → return Data[TOP--]; ● TOP was initialized to -1 and always points to the value to be popped. Stack grows up. ● ARM folk call this a “full ascending” stack Full-Descending Stack ● In low-level programming, a Full-Descending stack is more common. ARM ABI requires it. ● TOS is initialized to max_valid_index +1 ● Push(value) → Data[ --TOP] = value ● Pop → return Data[ TOP++] ● We decrement before on push and increment after on pop. ● DB and IA. Empty Stacks ● To ARM, an empty stack is where the top-of- stack pointer indicates where the next push will go. ● Push(value) → Data[TOP--] ● Pop → return Data[++TOP] ● Decrement After (DA) and Increment Before(IB) for an “empty descending” stack. ● Empty ascending stacks are also possible. ARM Assembly Push ● Use a form of the store multiple (STM) instruction for push, and a form of load multiple (LDM) for pop. ● Top-of-Stack is usually the R13 register (alias SP) ● Push(value in R5) → STMDB SP!, {R5} ● Pop (from stack to R5) → LDMIA SP!, {R5} ● This is for a Full-Descending stack, so you can use STMFD and LDMFD if desired (maybe). ● Crossware does not support PUSH and POP (textbook 13.2.2) An Un-RISCy Quirk ● We'll soon see that programmers often want to push (or pop) a bunch of registers to the stack.