Application Binary Interface 2015.04.02
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Doin' the Eagle Rock
VIRUS BULLETIN www.virusbtn.com MALWARE ANALYSIS 1 DOIN’ THE EAGLE ROCK this RNG in every virus for which he requires a source of random numbers. Peter Ferrie Microsoft, USA The virus then allocates two blocks of memory: one to hold the intermediate encoding of the virus body, and the other to hold the fully encoded virus body. The virus decompresses If a fi le contains no code, can it be executed? Can arithmetic a fi le header into the second block. The fi le header is operations be malicious? Here we have a fi le that contains compressed using a simple Run-Length Encoder algorithm. no code, and no data in any meaningful sense. All it The header is for a Windows Portable Executable fi le, and it contains is a block of relocation items, and all relocation seems as though the intention was to produce the smallest items do is cause a value to be added to locations in the possible header that can still be executed on Windows. There image. So, nothing but relocation items – and yet it also are overlapping sections, and ‘unnecessary’ fi elds have been contains W32/Lerock. removed. The virus then allocates a third block of memory, Lerock is written by the same virus author as W32/Fooper which will hold a copy of the unencoded virus body. (see VB, January 2010, p.4), and behaves in the same way at a The virus searches for zeroes within the unencoded memory high level, but at a lower level it differs in an interesting way. -

Strict Protection for Virtual Function Calls in COTS C++ Binaries
vfGuard: Strict Protection for Virtual Function Calls in COTS C++ Binaries Aravind Prakash Xunchao Hu Heng Yin Department of EECS Department of EECS Department of EECS Syracuse University Syracuse University Syracuse University [email protected] [email protected] [email protected] Abstract—Control-Flow Integrity (CFI) is an important se- these binary-only solutions are unfortunately coarse-grained curity property that needs to be enforced to prevent control- and permissive. flow hijacking attacks. Recent attacks have demonstrated that existing CFI protections for COTS binaries are too permissive, While coarse-grained CFI solutions have significantly re- and vulnerable to sophisticated code reusing attacks. Accounting duced the attack surface, recent efforts by Goktas¸¨ et al. [9] for control flow restrictions imposed at higher levels of semantics and Carlini [10] have demonstrated that coarse-grained CFI is key to increasing CFI precision. In this paper, we aim to provide solutions are too permissive, and can be bypassed by reusing more stringent protection for virtual function calls in COTS large gadgets whose starting addresses are allowed by these C++ binaries by recovering C++ level semantics. To achieve this solutions. The primary reason for such permissiveness is the goal, we recover C++ semantics, including VTables and virtual lack of higher level program semantics that introduce certain callsites. With the extracted C++ semantics, we construct a sound mandates on the control flow. For example, given a class CFI policy and further improve the policy precision by devising two filters, namely “Nested Call Filter” and “Calling Convention inheritance, target of a virtual function dispatch in C++ must Filter”. -

Common Object File Format (COFF)
Application Report SPRAAO8–April 2009 Common Object File Format ..................................................................................................................................................... ABSTRACT The assembler and link step create object files in common object file format (COFF). COFF is an implementation of an object file format of the same name that was developed by AT&T for use on UNIX-based systems. This format encourages modular programming and provides powerful and flexible methods for managing code segments and target system memory. This appendix contains technical details about the Texas Instruments COFF object file structure. Much of this information pertains to the symbolic debugging information that is produced by the C compiler. The purpose of this application note is to provide supplementary information on the internal format of COFF object files. Topic .................................................................................................. Page 1 COFF File Structure .................................................................... 2 2 File Header Structure .................................................................. 4 3 Optional File Header Format ........................................................ 5 4 Section Header Structure............................................................. 5 5 Structuring Relocation Information ............................................... 7 6 Symbol Table Structure and Content........................................... 11 SPRAAO8–April 2009 -
Tricore Architecture Manual for a Detailed Discussion of Instruction Set Encoding and Semantics
User’s Manual, v2.3, Feb. 2007 TriCore 32-bit Unified Processor Core Embedded Applications Binary Interface (EABI) Microcontrollers Edition 2007-02 Published by Infineon Technologies AG 81726 München, Germany © Infineon Technologies AG 2007. All Rights Reserved. Legal Disclaimer The information given in this document shall in no event be regarded as a guarantee of conditions or characteristics (“Beschaffenheitsgarantie”). With respect to any examples or hints given herein, any typical values stated herein and/or any information regarding the application of the device, Infineon Technologies hereby disclaims any and all warranties and liabilities of any kind, including without limitation warranties of non- infringement of intellectual property rights of any third party. Information For further information on technology, delivery terms and conditions and prices please contact your nearest Infineon Technologies Office (www.infineon.com). Warnings Due to technical requirements components may contain dangerous substances. For information on the types in question please contact your nearest Infineon Technologies Office. Infineon Technologies Components may only be used in life-support devices or systems with the express written approval of Infineon Technologies, if a failure of such components can reasonably be expected to cause the failure of that life-support device or system, or to affect the safety or effectiveness of that device or system. Life support devices or systems are intended to be implanted in the human body, or to support and/or maintain and sustain and/or protect human life. If they fail, it is reasonable to assume that the health of the user or other persons may be endangered. User’s Manual, v2.3, Feb. -
IAR C/C++ Compiler Reference Guide for V850
IAR Embedded Workbench® IAR C/C++ Compiler Reference Guide for the Renesas V850 Microcontroller Family CV850-9 COPYRIGHT NOTICE © 1998–2013 IAR Systems AB. No part of this document may be reproduced without the prior written consent of IAR Systems AB. The software described in this document is furnished under a license and may only be used or copied in accordance with the terms of such a license. DISCLAIMER The information in this document is subject to change without notice and does not represent a commitment on any part of IAR Systems. While the information contained herein is assumed to be accurate, IAR Systems assumes no responsibility for any errors or omissions. In no event shall IAR Systems, its employees, its contractors, or the authors of this document be liable for special, direct, indirect, or consequential damage, losses, costs, charges, claims, demands, claim for lost profits, fees, or expenses of any nature or kind. TRADEMARKS IAR Systems, IAR Embedded Workbench, C-SPY, visualSTATE, The Code to Success, IAR KickStart Kit, I-jet, I-scope, IAR and the logotype of IAR Systems are trademarks or registered trademarks owned by IAR Systems AB. Microsoft and Windows are registered trademarks of Microsoft Corporation. Renesas is a registered trademark of Renesas Electronics Corporation. V850 is a trademark of Renesas Electronics Corporation. Adobe and Acrobat Reader are registered trademarks of Adobe Systems Incorporated. All other product names are trademarks or registered trademarks of their respective owners. EDITION NOTICE Ninth edition: May 2013 Part number: CV850-9 This guide applies to version 4.x of IAR Embedded Workbench® for the Renesas V850 microcontroller family. -

The 7 Dwarves: Debugging Information Beyond Gdb
The 7 dwarves: debugging information beyond gdb Arnaldo Carvalho de Melo Red Hat, Inc. [email protected] [email protected] Abstract • To find out possibilities for reduction of such data structures; The DWARF debugging information format has been so • Use of information about function parameters and far used in debuggers such as gdb, and more recently in return types to generate Linux kernel modules for tools such as systemtap and frysk. obtaining data needed for generation of callgraphs In this paper the author will show additional scenarios and values set to fields at runtime; where such information can be useful, such as: • A tool that given two object files shows a binary diff to help understanding the effects of source • Showing the layout of data structures; code changes on size of functions and data struc- tures. • Reorganizing such data structures to remove align- ment holes; Some use cases will be presented, showing how the tools • Improving CPU cache utilization; can be used to solve real world problems. • Displaying statistics about inlining of functions; Ideas discussed with some fellow developers but not yet • Re-creating structs and functions from the debug- tried will also be presented, with the intent of hopefully ging information; having them finally tested in practice by interested read- ers. • Showing binary diffs to help understand the effects of any code change. 2 DWARF Debugging Format And much more. DWARF [3] is a debugging file format used by many compilers to store information about data structures, 1 Introduction variables, functions and other language aspects needed by high level debuggers. -

Linking Basics.Docx Page 1 of 35 Initial Creation: March, 24, 2015 Date Updated: October 4, 2015
An Overview of Object Files And Linking Harry H. Porter III Portland State University cs.pdx.edu/~harry April 9, 2015 Goals of this Paper Audience: CS-201 students Coverage: Compiling Linking Object files External Symbols Relocatable Code Segments (.text, .data., .bss) Filename: Linking Basics.docx Page 1 of 35 Initial Creation: March, 24, 2015 Date Updated: October 4, 2015 Overview In order to create an executable file, a program must be compiled and linked. In this paper, I’ll use the “C” programming language as an example, but this discussion applies to other compiled languages like C++. Languages that are interpreted (like Java or Python) do things differently and linking does not apply to them. We’ll also discuss the Linux/Unix system, but other OSes are similar. A program begins as a human readable source text file, such as “hello.c”. The program must first be compiled and this step produces a human readable text file in assembly code. Then the assembly code version is assembled and this produces an object file. Finally, the object file is linked and the executable file is produced. At some later time, the OS will load the executable file into memory run it. Many programs are large and these programs are broken into several “.c” files. We’ll look at an example involving two files, “hello.c” and “there.c”. Each of the .c files must be compiled and assembled, but these steps can be done independently. In other words, we can compile and assemble hello.c before we even create the there.c file. -

Lecture 21: Calling Conventions Menu Calling Convention Calling Convention X86 C Calling Convention
CS216: Program and Data Representation University of Virginia Computer Science Spring 2006 David Evans Menu Lecture 21: Calling Conventions • x86 C Calling Convention • Java Byte Code Wizards http://www.cs.virginia.edu/cs216 UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 2 Calling Convention Calling Convention • Rules for how the caller and the Caller Callee callee make subroutine calls • Where to put • Where to find • Caller needs to know: params params • What registers can I • What registers – How to pass parameters assume are same must I not bash – What registers might be bashed by • Where to find result • Where to put result called function • State of stack • State of stack – What is state of stack after return – Where to get result UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 3 UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 4 Calling Convention: x86 C Calling Convention Easiest for Caller Caller Callee Caller Callee • Where to put • Where to find • Params on stack in • Find params on stack params params reverse order in reverse order • What registers can I • What registers • Can assume EBX, • Must not bash EBX, assume are same must I not bash EDI and ESI are EDI or ESI – All of them – None of them same • Put result in EAX • Where to find result • Where to put result • Find result in EAX • Stack rules next • State of stack • State of stack • Stack rules next Need to save and Need to save and restore restore EBX, EDI (EAX), ECX, EDX and ESI UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 5 UVa CS216 -

Chapter 13 ARM Image Format
Chapter 13 ARM Image Format This chapter describes the ARM Image Format (AIF). It contains the following sections: • Overview of the ARM Image Format on page 13-2 • AIF variants on page 13-3 • The layout of AIF on page 13-4. ARM DUI 0041C Copyright © 1997 and 1998 ARM Limited. All rights reserved. 13-1 ARM Image Format 13.1 Overview of the ARM Image Format ARM Image Format (AIF) is a simple format for ARM executable images, consisting of: • a 128-byte header • the image code • the image initialized static data. An AIF image is capable of self-relocation if it is created with the appropriate linker options. The image can be loaded anywhere and it will execute where it is loaded. After an AIF image has been relocated, it can create its own zero-initialized area. Finally, the image is entered at the unique entry point. 13-2 Copyright © 1997 and 1998 ARM Limited. All rights reserved. ARM DUI 0041C ARM Image Format 13.2 AIF variants There are three variants of AIF: Executable AIF Executable AIF can be loaded at its load address and entered at the same point (at the first word of the AIF header). It prepares itself for execution by relocating itself if required and setting to zero its own zero-initialized data. The header is part of the image itself. Code in the header ensures that the image is properly prepared for execution before being entered at its entry address. The fourth word of an executable AIF header is: BL entrypoint The most significant byte of this word (in the target byte order) is 0xeb. -
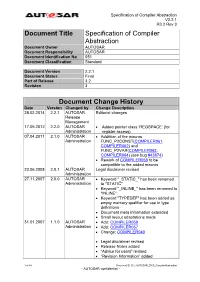
Specification of Compiler Abstraction
Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Document Title Specification of Compiler Abstraction Document Owner AUTOSAR Document Responsibility AUTOSAR Document Identification No 051 Document Classification Standard Document Version 2.2.1 Document Status Final Part of Release 3.2 Revision 3 Document Change History Date Version Changed by Change Description 28.02.2014 2.2.1 AUTOSAR Editorial changes Release Management 17.05.2012 2.2.0 AUTOSAR Added pointer class ‘REGSPACE’ (for Administration register access) 07.04.2011 2.1.0 AUTOSAR Addtition of the macros Administration FUNC_P2CONST(COMPILER061, COMPILER062) and FUNC_P2VAR(COMPILER063, COMPILER064) (see bug #43874) Rework of COMPILER058 to be compatible to the added macros 23.06.2008 2.0.1 AUTOSAR Legal disclaimer revised Administration 27.11.2007 2.0.0 AUTOSAR Keyword "_STATIC_" has been renamed Administration to "STATIC" Keyword "_INLINE_" has been renamed to "INLINE" Keyword "TYPEDEF" has been added as empty memory qualifier for use in type definitions Document meta information extended Small layout adaptations made 31.01.2007 1.1.0 AUTOSAR Add: COMPILER058 Administration Add: COMPILER057 Change: COMPILER040 Legal disclaimer revised Release Notes added “Advice for users” revised “Revision Information” added 1 of 44 Document ID 051: AUTOSAR_SWS_CompilerAbstraction - AUTOSAR confidential - Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Document Change History Date Version Changed by Change Description 27.04.2006 1.0.0 AUTOSAR Initial Release Administration 2 of 44 Document ID 051: AUTOSAR_SWS_CompilerAbstraction - AUTOSAR confidential - Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Disclaimer This specification and the material contained in it, as released by AUTOSAR is for the purpose of information only. -
EECS 373 Design of Microprocessor-Based Systems
Procedures Procedures are very important for writing reusable and maintainable code in assembly and high-level languages. How are they implemented? · Application Binary Interfaces · Calling Conventions · Recursive Calls · Examples Reference: PowerPC Embedded ABI General Concepts · Caller: The calling procedure Callee: The procedure called by the caller ¼ int mult(x, y) prod = mult (a, b) ¼ ¼ return (x * y) · Caller and callee must agree on: · How to pass parameters · How to return the return value(s), if any · How to maintain relevant information across calls · PowerPC architecture does not define ªagreementº. Instead, common policies are defined by convention. PowerPC Features The PowerPC ISA provides the following features to support procedure/function calls: · link register (p. 2-11) · bl: branch and link (p. 4-41) · blr: branch to link register (Table F-4) A Very Simple Calling Convention · Passing arguments · Use GPRs r3 to r10 in order · Use stack in main memory if more than 8 arguments · Passing return value · Leave result in r3 Example int func(int a, int b) { return (a + b); } main { ¼ func(5,6); ¼ } Another Example int func2(int a, int b) { return func(a , b); } main { ¼ func2(5,6); ¼ } The Stack · Information for each function invocation (e.g. link register) is saved on the call stack or simply stack. · Each function invocation has its own stack frame (a.k.a. activation record ). high address func2 stack frame func stack frame stack pointer low address Using the Stack main ¼ Describe the stack and LR contents ¼ · right before -

Symbol Table Relocation Table Object File Format Where Are We Now
inst.eecs.berkeley.edu/~cs61c UCB CS61C : Machine Structures Symbol Table Lecture 19 – Running a Program II . List of “items” in this file that may be used by other files. (Compiling, Assembling, Linking, Loading) Hello to . What are they? Lecturer SOE 2008-03-05 Neil Sharma Labels: function calling Dan Garcia from the 3rd row! Data: anything in the .data section; variables which may be accessed across files Researchers at Princeton have developed a flexible electricity-producing sheet of rubber that can use body movements into electricity. Breathing generates 1 W, walking around the room generates 70 W. Shoes may be the best place, to power/recharge cell phones & iPods. www.nytimes.com/2010/03/02/science/02obribbon.html CS61C L19 : Running a Progam II … Compiling, Assembling, Linking, and Loading (3) Garcia, Spring 2010 © UCB Relocation Table Object File Format . List of “items” this file needs the address later. object file header: size and position of the other . What are they? pieces of the object file Any label jumped to: j or jal . text segment: the machine code internal . data segment: binary representation of the data in external (including lib files) the source file Any piece of data connected with an address . relocation information: identifies lines of code that such as the la instruction need to be “handled” . symbol table: list of this file’s labels and data that can be referenced . debugging information . A standard format is ELF (except MS) http://www.skyfree.org/linux/references/ELF_Format.pdf CS61C L19 : Running a Progam II … Compiling, Assembling, Linking, and Loading (4) Garcia, Spring 2010 © UCB CS61C L19 : Running a Progam II … Compiling, Assembling, Linking, and Loading (5) Garcia, Spring 2010 © UCB Where Are We Now? Linker (1/3) .