Strict Protection for Virtual Function Calls in COTS C++ Binaries
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Architecture of Decentvm
The Architecture of the DecentVM Towards a Decentralized Virtual Machine for Many-Core Computing Annette Bieniusa Johannes Eickhold Thomas Fuhrmann University of Freiburg, Germany Technische Universitat¨ Munchen,¨ Germany [email protected] fjeick,[email protected] Abstract We have accomplished these goals by combining an off-line Fully decentralized systems avoid bottlenecks and single points transcoder with a virtual machine that executes modified bytecode. of failure. Thus, they can provide excellent scalability and very The transcoder performs the verification and statically links the robust operation. The DecentVM is a fully decentralized, distributed required classes of an application or library. Thereby, the resulting virtual machine. Its simplified instruction set allows for a small binary – a so-called blob – is significantly smaller than the original VM code footprint. Its partitioned global address space (PGAS) class files, and its execution requires a significantly less complex memory model helps to easily create a single system image (SSI) virtual machine. Both these effects result in the low memory across many processors and processor cores. Originally, the VM was footprint of DecentVM. designed for networks of embedded 8-bit processors. Meanwhile, All libraries that are required by an application are identified via it also aims at clusters of many core processors. This paper gives a cryptographic hashes. Thus, an application’s code can be deployed brief overview of the DecentVM architecture. as if it was a statically linked executable. The software vendor can thus test the executable as it runs on the customer site without Categories and Subject Descriptors C.1.4 [Processor Architec- interference from different library versions. -

Dynamically Loaded Classes As Shared Libraries: an Approach to Improving Virtual Machine Scalability
Dynamically Loaded Classes as Shared Libraries: an Approach to Improving Virtual Machine Scalability Bernard Wong Grzegorz Czajkowski Laurent Daynès University of Waterloo Sun Microsystems Laboratories 200 University Avenue W. 2600 Casey Avenue Waterloo, Ontario N2L 3G1, Canada Mountain View, CA 94043, USA [email protected] {grzegorz.czajkowski, laurent.daynes}@sun.com Abstract machines sold today have sufficient amount of memory to hold a few instances of the Java virtual machine (JVMTM) Sharing selected data structures among virtual [2]. However, on servers hosting many applications, it is machines of a safe language can improve resource common to have many instances of the JVM running utilization of each participating run-time system. The simultaneously, often for lengthy periods of time. challenge is to determine what to share and how to share Aggregate memory requirement can therefore be large, it in order to decrease start-up time and lower memory and meeting it by adding more memory is not always an footprint without compromising the robustness of the option. In these settings, overall memory footprint must be system. Furthermore, the engineering effort required to kept to a minimum. For personal computer users, the main implement the system must not be prohibitive. This paper irritation is due to long start-up time, as they expect good demonstrates an approach that addresses these concerns TM responsiveness from interactive applications, which in in the context of the Java virtual machine. Our system contrast is of little importance in enterprise computing. transforms packages into shared libraries containing C/C++ programs typically do not suffer from excessive classes in a format matching the internal representation memory footprint or lengthy start-up time. -

Proceedings of the Third Virtual Machine Research and Technology Symposium
USENIX Association Proceedings of the Third Virtual Machine Research and Technology Symposium San Jose, CA, USA May 6–7, 2004 © 2004 by The USENIX Association All Rights Reserved For more information about the USENIX Association: Phone: 1 510 528 8649 FAX: 1 510 548 5738 Email: [email protected] WWW: http://www.usenix.org Rights to individual papers remain with the author or the author's employer. Permission is granted for noncommercial reproduction of the work for educational or research purposes. This copyright notice must be included in the reproduced paper. USENIX acknowledges all trademarks herein. MCI-Java: A Modified Java Virtual Machine Approach to Multiple Code Inheritance Maria Cutumisu, Calvin Chan, Paul Lu and Duane Szafron Department of Computing Science, University of Alberta {meric, calvinc, paullu, duane}@cs.ualberta.ca Abstract Java has multiple inheritance of interfaces, but only single inheritance of code via classes. This situation results in duplicated code in Java library classes and application code. We describe a generalization to the Java language syntax and the Java Virtual Machine (JVM) to support multiple inheritance of code, called MCI-Java. Our approach places multiply-inherited code in a new language construct called an implementation, which lies between an interface and a class in the inheritance hierarchy. MCI-Java does not support multiply-inherited data, which can cause modeling and performance problems. The MCI-Java extension is implemented by making minimal changes to the Java syntax, small changes to a compiler (IBM Jikes), and modest localized changes to a JVM (SUN JDK 1.2.2). The JVM changes result in no measurable performance overhead in real applications. -

Design and Implementation of a Scala Compiler Backend Targeting the Low Level Virtual Machine Geoffrey Reedy
University of New Mexico UNM Digital Repository Computer Science ETDs Engineering ETDs 5-1-2014 Design and Implementation of a Scala Compiler Backend Targeting the Low Level Virtual Machine Geoffrey Reedy Follow this and additional works at: https://digitalrepository.unm.edu/cs_etds Recommended Citation Reedy, Geoffrey. "Design and Implementation of a Scala Compiler Backend Targeting the Low Level Virtual Machine." (2014). https://digitalrepository.unm.edu/cs_etds/67 This Thesis is brought to you for free and open access by the Engineering ETDs at UNM Digital Repository. It has been accepted for inclusion in Computer Science ETDs by an authorized administrator of UNM Digital Repository. For more information, please contact [email protected]. Geoffrey Reedy Candidate Computer Science Department This thesis is approved, and it is acceptable in quality and form for publication: Approved by the Thesis Committee: Darko Stefanovic , Chairperson Jed Crandall Matthew Lakin Design and Implementation of a Scala Compiler Backend Targeting the Low Level Virtual Machine by Geoffrey Reedy B.S., Computer Science, University of Missouri — Rolla, 2004 THESIS Submitted in Partial Fulfillment of the Requirements for the Degree of Master of Science Computer Science The University of New Mexico Albuquerque, New Mexico May, 2014 ©2014, Geoffrey Reedy iii Design and Implementation of a Scala Compiler Backend Targeting the Low Level Virtual Machine by Geoffrey Reedy B.S., Computer Science, University of Missouri — Rolla, 2004 M.S., Computer Science, University of New Mexico, 2014 Abstract The Scala programming language successfully blends object-oriented and functional programming. The current implementation of Scala is tied to the Java Virtual Machine (JVM) which constrains the implementation and deployment targets. -

Java and C CSE351, Summer 2018
L23: Java and C CSE351, Summer 2018 Java and C CSE 351 Summer 2018 Instructor: Justin Hsia Teaching Assistants: Josie Lee Natalie Andreeva Teagan Horkan https://xkcd.com/801/ L23: Java and C CSE351, Summer 2018 Administrivia Lab 5 due Friday (8/17) at 11:59 pm . Hard deadline Course evaluations now open . See Piazza post @120 for links Final Exam: Friday in lecture . Review Session: Wed, 8/15, 5‐6:30 pm in EEB 045 . You get ONE double‐sided handwritten 8.5 11” cheat sheet 2 L23: Java and C CSE351, Summer 2018 Roadmap C: Java: Memory & data car *c = malloc(sizeof(car)); Car c = new Car(); Integers & floats c->miles = 100; c.setMiles(100); x86 assembly c->gals = 17; c.setGals(17); Procedures & stacks float mpg = get_mpg(c); float mpg = Executables free(c); c.getMPG(); Arrays & structs Memory & caches Assembly get_mpg: Processes language: pushq %rbp movq %rsp, %rbp Virtual memory ... Memory allocation popq %rbp Java vs. C ret OS: Machine 0111010000011000 100011010000010000000010 code: 1000100111000010 110000011111101000011111 Computer system: 3 L23: Java and C CSE351, Summer 2018 Java vs. C Reconnecting to Java (hello CSE143!) . But now you know a lot more about what really happens when we execute programs We’ve learned about the following items in C; now we’ll see what they look like for Java: . Representation of data . Pointers / references . Casting . Function / method calls including dynamic dispatch 4 L23: Java and C CSE351, Summer 2018 Worlds Colliding CSE351 has given you a “really different feeling” about what computers do and how programs execute We have occasionally contrasted to Java, but CSE143 may still feel like “a different world” . -

G22.2110-003 Programming Languages - Fall 2012 Lecture 12
G22.2110-003 Programming Languages - Fall 2012 Lecture 12 Thomas Wies New York University Review Last lecture I Modules Outline I Classes I Encapsulation and Inheritance I Initialization and Finalization I Dynamic Method Binding I Abstract Classes I Simulating First-Class Functions Sources: I PLP, ch. 9 I PLP, ch. 3.6.3 What is OOP? (part I) The object idea: I bundling of data (data members) and operations (methods) on that data I restricting access to the data An object contains: I data members: arranged as a set of named fields I methods: routines which take the object they are associated with as an argument (known as member functions in C++) A class is a construct which defines the data and methods associated with all of its instances (objects). What is OOP? (part II) The inheritance and dynamic binding ideas: I inheritance: classes can be extended: I by adding new fields I by adding new methods I by overriding existing methods (changing behavior) If class B extends class A, we say that B is a subclass (or a derived or child class) of A, and A is a superclass (or a base or a parent class) of B. I dynamic binding: wherever an instance of a class is required, we can also use an instance of any of its subclasses; when we call one of its methods, the overridden versions are used. Information Hiding in Classes Like modules, classes can restrict access to their data and methods. Unlike modules, classes must take inheritance into account in their access control. -
Tricore Architecture Manual for a Detailed Discussion of Instruction Set Encoding and Semantics
User’s Manual, v2.3, Feb. 2007 TriCore 32-bit Unified Processor Core Embedded Applications Binary Interface (EABI) Microcontrollers Edition 2007-02 Published by Infineon Technologies AG 81726 München, Germany © Infineon Technologies AG 2007. All Rights Reserved. Legal Disclaimer The information given in this document shall in no event be regarded as a guarantee of conditions or characteristics (“Beschaffenheitsgarantie”). With respect to any examples or hints given herein, any typical values stated herein and/or any information regarding the application of the device, Infineon Technologies hereby disclaims any and all warranties and liabilities of any kind, including without limitation warranties of non- infringement of intellectual property rights of any third party. Information For further information on technology, delivery terms and conditions and prices please contact your nearest Infineon Technologies Office (www.infineon.com). Warnings Due to technical requirements components may contain dangerous substances. For information on the types in question please contact your nearest Infineon Technologies Office. Infineon Technologies Components may only be used in life-support devices or systems with the express written approval of Infineon Technologies, if a failure of such components can reasonably be expected to cause the failure of that life-support device or system, or to affect the safety or effectiveness of that device or system. Life support devices or systems are intended to be implanted in the human body, or to support and/or maintain and sustain and/or protect human life. If they fail, it is reasonable to assume that the health of the user or other persons may be endangered. User’s Manual, v2.3, Feb. -
IAR C/C++ Compiler Reference Guide for V850
IAR Embedded Workbench® IAR C/C++ Compiler Reference Guide for the Renesas V850 Microcontroller Family CV850-9 COPYRIGHT NOTICE © 1998–2013 IAR Systems AB. No part of this document may be reproduced without the prior written consent of IAR Systems AB. The software described in this document is furnished under a license and may only be used or copied in accordance with the terms of such a license. DISCLAIMER The information in this document is subject to change without notice and does not represent a commitment on any part of IAR Systems. While the information contained herein is assumed to be accurate, IAR Systems assumes no responsibility for any errors or omissions. In no event shall IAR Systems, its employees, its contractors, or the authors of this document be liable for special, direct, indirect, or consequential damage, losses, costs, charges, claims, demands, claim for lost profits, fees, or expenses of any nature or kind. TRADEMARKS IAR Systems, IAR Embedded Workbench, C-SPY, visualSTATE, The Code to Success, IAR KickStart Kit, I-jet, I-scope, IAR and the logotype of IAR Systems are trademarks or registered trademarks owned by IAR Systems AB. Microsoft and Windows are registered trademarks of Microsoft Corporation. Renesas is a registered trademark of Renesas Electronics Corporation. V850 is a trademark of Renesas Electronics Corporation. Adobe and Acrobat Reader are registered trademarks of Adobe Systems Incorporated. All other product names are trademarks or registered trademarks of their respective owners. EDITION NOTICE Ninth edition: May 2013 Part number: CV850-9 This guide applies to version 4.x of IAR Embedded Workbench® for the Renesas V850 microcontroller family. -

Lecture 21: Calling Conventions Menu Calling Convention Calling Convention X86 C Calling Convention
CS216: Program and Data Representation University of Virginia Computer Science Spring 2006 David Evans Menu Lecture 21: Calling Conventions • x86 C Calling Convention • Java Byte Code Wizards http://www.cs.virginia.edu/cs216 UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 2 Calling Convention Calling Convention • Rules for how the caller and the Caller Callee callee make subroutine calls • Where to put • Where to find • Caller needs to know: params params • What registers can I • What registers – How to pass parameters assume are same must I not bash – What registers might be bashed by • Where to find result • Where to put result called function • State of stack • State of stack – What is state of stack after return – Where to get result UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 3 UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 4 Calling Convention: x86 C Calling Convention Easiest for Caller Caller Callee Caller Callee • Where to put • Where to find • Params on stack in • Find params on stack params params reverse order in reverse order • What registers can I • What registers • Can assume EBX, • Must not bash EBX, assume are same must I not bash EDI and ESI are EDI or ESI – All of them – None of them same • Put result in EAX • Where to find result • Where to put result • Find result in EAX • Stack rules next • State of stack • State of stack • Stack rules next Need to save and Need to save and restore restore EBX, EDI (EAX), ECX, EDX and ESI UVa CS216 Spring 2006 - Lecture 21: Calling Conventions 5 UVa CS216 -
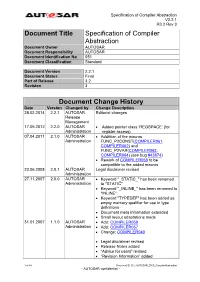
Specification of Compiler Abstraction
Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Document Title Specification of Compiler Abstraction Document Owner AUTOSAR Document Responsibility AUTOSAR Document Identification No 051 Document Classification Standard Document Version 2.2.1 Document Status Final Part of Release 3.2 Revision 3 Document Change History Date Version Changed by Change Description 28.02.2014 2.2.1 AUTOSAR Editorial changes Release Management 17.05.2012 2.2.0 AUTOSAR Added pointer class ‘REGSPACE’ (for Administration register access) 07.04.2011 2.1.0 AUTOSAR Addtition of the macros Administration FUNC_P2CONST(COMPILER061, COMPILER062) and FUNC_P2VAR(COMPILER063, COMPILER064) (see bug #43874) Rework of COMPILER058 to be compatible to the added macros 23.06.2008 2.0.1 AUTOSAR Legal disclaimer revised Administration 27.11.2007 2.0.0 AUTOSAR Keyword "_STATIC_" has been renamed Administration to "STATIC" Keyword "_INLINE_" has been renamed to "INLINE" Keyword "TYPEDEF" has been added as empty memory qualifier for use in type definitions Document meta information extended Small layout adaptations made 31.01.2007 1.1.0 AUTOSAR Add: COMPILER058 Administration Add: COMPILER057 Change: COMPILER040 Legal disclaimer revised Release Notes added “Advice for users” revised “Revision Information” added 1 of 44 Document ID 051: AUTOSAR_SWS_CompilerAbstraction - AUTOSAR confidential - Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Document Change History Date Version Changed by Change Description 27.04.2006 1.0.0 AUTOSAR Initial Release Administration 2 of 44 Document ID 051: AUTOSAR_SWS_CompilerAbstraction - AUTOSAR confidential - Specification of Compiler Abstraction V2.2.1 R3.2 Rev 3 Disclaimer This specification and the material contained in it, as released by AUTOSAR is for the purpose of information only. -
EECS 373 Design of Microprocessor-Based Systems
Procedures Procedures are very important for writing reusable and maintainable code in assembly and high-level languages. How are they implemented? · Application Binary Interfaces · Calling Conventions · Recursive Calls · Examples Reference: PowerPC Embedded ABI General Concepts · Caller: The calling procedure Callee: The procedure called by the caller ¼ int mult(x, y) prod = mult (a, b) ¼ ¼ return (x * y) · Caller and callee must agree on: · How to pass parameters · How to return the return value(s), if any · How to maintain relevant information across calls · PowerPC architecture does not define ªagreementº. Instead, common policies are defined by convention. PowerPC Features The PowerPC ISA provides the following features to support procedure/function calls: · link register (p. 2-11) · bl: branch and link (p. 4-41) · blr: branch to link register (Table F-4) A Very Simple Calling Convention · Passing arguments · Use GPRs r3 to r10 in order · Use stack in main memory if more than 8 arguments · Passing return value · Leave result in r3 Example int func(int a, int b) { return (a + b); } main { ¼ func(5,6); ¼ } Another Example int func2(int a, int b) { return func(a , b); } main { ¼ func2(5,6); ¼ } The Stack · Information for each function invocation (e.g. link register) is saved on the call stack or simply stack. · Each function invocation has its own stack frame (a.k.a. activation record ). high address func2 stack frame func stack frame stack pointer low address Using the Stack main ¼ Describe the stack and LR contents ¼ · right before -

Comparative Studies of 10 Programming Languages Within 10 Diverse Criteria Revision 1.0
Comparative Studies of 10 Programming Languages within 10 Diverse Criteria Revision 1.0 Rana Naim∗ Mohammad Fahim Nizam† Concordia University Montreal, Concordia University Montreal, Quebec, Canada Quebec, Canada [email protected] [email protected] Sheetal Hanamasagar‡ Jalal Noureddine§ Concordia University Montreal, Concordia University Montreal, Quebec, Canada Quebec, Canada [email protected] [email protected] Marinela Miladinova¶ Concordia University Montreal, Quebec, Canada [email protected] Abstract This is a survey on the programming languages: C++, JavaScript, AspectJ, C#, Haskell, Java, PHP, Scala, Scheme, and BPEL. Our survey work involves a comparative study of these ten programming languages with respect to the following criteria: secure programming practices, web application development, web service composition, OOP-based abstractions, reflection, aspect orientation, functional programming, declarative programming, batch scripting, and UI prototyping. We study these languages in the context of the above mentioned criteria and the level of support they provide for each one of them. Keywords: programming languages, programming paradigms, language features, language design and implementation 1 Introduction Choosing the best language that would satisfy all requirements for the given problem domain can be a difficult task. Some languages are better suited for specific applications than others. In order to select the proper one for the specific problem domain, one has to know what features it provides to support the requirements. Different languages support different paradigms, provide different abstractions, and have different levels of expressive power. Some are better suited to express algorithms and others are targeting the non-technical users. The question is then what is the best tool for a particular problem.