Information Leakage and Steganography: Detecting and Blocking Covert Channels
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Brave Lions Two Alternate Views Hickie & Horgan Fashion - Page 16 Exclusive Interview Rud’S World - Page 22 Sport - Page 26
ISSUE 2 / VOLUME 19 4.10.05 METROSEXUALS BRAVE LIONS TWO ALTERNATE VIEWS HICKIE & HORGAN FASHION - PAGE 16 EXCLUSIVE INTERVIEW RUD’S WORLD - PAGE 22 SPORT - PAGE 26 gone.” Irish Students Destroy J1 Flat JACK CANE The College Tribune has not received any infor- “A PLACE TO CRASH mation as to whether the sub-leasers of the other AND PARTY, THAT’S IT, Some of the destruction caused There are no criminal proceedings in motion on apartments will be paying for damages incurred. WHO CARES ABOUT IT?” by former UCD students either side of the Atlantic. When a number of them were contacted, the stu- Maher’s hope that “the students involved will have dents alleged to have been involved declined to com- “This happens all the time.” These are Irish students are being held responsible some moral feelings to pay up what they owe” ment. the words of UCD Student Advisor Ronan Murphy, a former employee of UC Santa for approximately US$15,000 worth of appears to have had some success. However, the destruction of the Isla Vista apart- Barbara. damages to three apartments in Santa In an email sent to the College Tribune, Maher ments has already had a negative effect on the rep- Barbara, California. Former UCD students reported that the tenants of apartment #8 have paid According to Murphy, the latest reports were involved in the devastation of the utation of Irish students in Santa Barbara. of destruction of three apartments by Irish US$1,800 towards the damages in that residence. Katie Maher confirmed “if BDC do take Irish stu- three apartments. -

Music Education for Children Across Ireland
music generation is ireland’s national music education program that helps children and young people access a range of high quality vocal and instrumental tuition in their local area. to date, the program has reached over 20,000 children and young people across 12 areas of the country. job opportunities have been created for 250 musicians. over 60 diverse and exciting music programs are being delivered in 300 different tuition centres around the country. initiated by music network, music generation has been seed funded by a €7m philanthropic donation by u2 (€5m) and the ireland funds (€2m) from 2010-2015. building upon the principles of philanthropy which seek to achieve long term sustainable outcomes, music generation has worked closely with local music education partnerships and government since its initiation. in july 2014, the department of education and skills joined with the local music education partners to co-fund the program. music generation is an extraordinary example of a partnership between the private sector, the irish government and local funding partners, which is bringing about momentous change in music education in ireland. music education for children across ireland connect 2015 | 32 2014 has been an amazing year for music generation Music Generation recently hosted over 200 delegates in Dublin Composed by Brian Irvine and five young Sligo composers, the for a special Music Education Conference and a packed Gala concerts featured over 200 young musicians and singers in a Concert, with over 400 young people performing in the presence wonderful ensemble performance. of President Michael D. Higgins at the National Concert Hall. -

2013/B/39 Tuairisceáin Bhliantiúla Faighte Idir 02-Dei-2013 Agus 08-Dei-2013 Inneács De Na Cineál Áiteamh
AITHEANTAS EAGRÁIN: 2013/B/39 TUAIRISCEÁIN BHLIANTIÚLA FAIGHTE IDIR 02-DEI-2013 AGUS 08-DEI-2013 INNEÁCS DE NA CINEÁL ÁITEAMH B1AU - TUAIRISCEAN BLIANTUIL LE TUAIRISCEAN INIUCHORA B1 - TUAIRISCEAN BLIANTUIL - GAN CUNTAIS B1C - TUAIRISCEAN BLIANTUIL -GINEARALTA B1B - TUAIRISCEAN BLIANTUIL IONADUIL CRO GAZETTE, CÉADAOIN, 9ú DEIREADH FÓMHAIR 2013 3 TUAIRISCEÁIN BHLIANTIÚLA FAIGHTE IDIR 02-DEI-2013 AGUS 08-DEI-2013 Uimhir na Ainm na Cáipéis Dáta Uimhir na Ainm na Cáipéis Dáta CuideachtaCuideacht Faighte CuideachtaCuideacht Faighte 3033 SICK AND INDIGENT ROOMKEEPERS' B1C 01/10/2013 21745 AHERN'S GARAGE LIMITED B1C 25/09/2013 SOCIETY (INCORPORATED) 21855 THURLES WHOLESALE CASH AND B1C 20/09/2013 3518 GRAND HOTEL,MALAHIDE,LIMITED B1C 04/10/2013 CARRY, LIMITED 7129 W. & R. JACOB B1 03/10/2013 21901 L. LYNCH AND CO LIMITED B1C 27/09/2013 7229 FIAT GROUP AUTOMOBILES IRELAND B1C 03/10/2013 22058 BERKEL (IRELAND) LIMITED B1C 02/10/2013 LIMITED 22133 I.I.E. LIMITED B1 02/10/2013 7433 CLARMORE LIMITED B1C 25/09/2013 22734 TRUSTEES OF MUCKROSS HOUSE B1C 16/09/2013 7640 ADELPHI-CARLTON LIMITED B1C 02/10/2013 (KILLARNEY), LIMITED 7749 JOHN KELLY, (WATERFORD) LIMITED B1C 02/10/2013 22874 PWS CELBRIDGE LIMITED B1C 11/09/2013 8050 DUNDEALGAN GREYHOUND RACING B1C 30/09/2013 23423 TUCKS O'BRIEN LIMITED B1C 30/09/2013 COMPANY LIMITED 23605 ARKLOW SHIPPING B1AU 01/10/2013 8142 CLASSIC FUEL & OIL LIMITED B1C 02/10/2013 23653 ROADMASTER CARAVANS LIMITED B1C 03/10/2013 8485 STEPHEN FALLER LIMITED B1C 25/09/2013 23771 IRISH BISCUITS B1 03/10/2013 8585 J. -

Linn Dara Carers Warned By
E RE F E H LT OCAL WEST EDITION 20th July 2018 Phone: 087 252 4064 • Email: [email protected] • www.localnews.ie Delivering to: Ballyfermot Lucann Leixlip eCelbriwdge Clondaslkin Palmerstown Kilcock Maynooth l l l l l l l Linn Dara carers NO MORE TV BILLS EVER SPECIAL OFFER warned by HSE €250 IRISH COMPANY fully install ed EXCELLENT SPECIAL TO AFTERCARE SERVICE LOCAL NEWS by Paul Kelly Tel: 083 3133133 STAFF AT Cherry Orchard’s shuttered Linn Dara were berated, cross-examined and sworn to silence by their managers as news of the shock closure of the mental health centre leaked out. Linn Dara was closed late in the week of Monday, July 2. And Local News has learned that, astoundingly, staff were forced to make fu - ture appointments for clients to come to Linn Dara — knowing that the centre would be closed when they got there. Meanwhile, qualified nurse and mental health champion Senator Máire Devine, talking exclusively Pictured enjoying the Longitude Festival recently, which was blessed with some of the best weather of to Local News , expressed this balmy summer. pic by ©INPHO/Ryan Byrne/Red Bull Content fury at the decision. House Painting “The HSE won’t get away internal & USELESS pletely useless.” “If you have money, you with this,” she vowed. Bríd Smith, TD (PBP, can get private care. If you external “They talk about the cen - don't, you wait or die.” And she also attacked Dublin South Central) has tre being ‘suspended’ until Meanwhile, Linn Dara Junior Health Minister Jim raised Linn Dara in the special rates for September, then October. -

IMRO Annual Report 2007
IMRO ANNUAL REPORT & ACCOUNTS 2007 Cover IMRO.indd 1 07/08/2008 10:50:57 IMRO ANNUAL REPORT & ACCOUNTS 2007 Title Page IMRO 1 30/07/2008 1 3:11:55 Blank Page IMRO 1 30/07/2008 1 3:07:51 IMRO BOARD OF DIRECTORS: Keith Donald (Cathaoirleach), Paul Brady, Philip Flynn, Eddie Joyce, Johnny Lappin, Steve Lindsey (UK), Donagh Long, Eleanor McEvoy, Charlie McGettigan, Christy Moore, James Morris, CREDITS Michael O’Riordan, Niall Toner. PRODUCTION MANAGER: Mairin Sheehy CONTRIBUTORS: Jackie Hayden, Greg McAteer, Colm O’Hare, Peter Murphy DESIGN & PRODUCTION: Hot Press, 13 Trinity Street, Dublin 2. ART DIRECTOR: David Keane ADDITIONAL DESIGN: Graham Keogh PRODUCTION CO-ORDINATOR: Anne Marie Conlon 3 Credits IMRO 1 30/07/2008 1 3:13:14 Blank Page IMRO 1 30/07/2008 1 3:08:22 6 TAKING IMRO TO HEART KEITH DONALD tells us about his plans for his term as IMRO Chairman. 9 FINANCIAL HIGHLIGHTS IN 2007 10 IMRO WELCOMES NEW CEO VICTOR FINN We talk to newly-appointed CEO, VICTOR FINN about the future of the CONTENTS organisation. 12 NEWS REVIEW A look at the music news that made headlines over the last year. 15 IMRO MOVING AHEAD Publishers MICHAEL O’RIORDAN, PETER BARDON and STEVE LINDSEY share their views on the challenges and opportunities facing Irish music. 18 THE SONGWRITERS’ PERSPECTIVE PAUL BRADY and ELEANOR MCEVOY on the trials and tribulations of being a modern-day songwriter. 20 ONCE UPON A TIME GLEN HANSARD and MARKETA IRGLOVA talk about the life-changing experience of winning an Oscar in March 2008. -

The Cocktail Issue Welcome to the April Issue of Our Magazine
The Cocktail Issue Welcome to the April issue of our magazine. Having spent December pub-crawling, Janu- index ary and February bringing you the low-down on the best overall venues in the city, and March comparing Asian and Mediterranean cuisine, 2night’s been pretty active in the last few months. So what better way to unwind 04 than with a creative concoction of well-mixed Special Feature - Mixing it up A roundup of the city’s top spirits? Mixing business with pleasure, we’ve places for cocktails. put together a list of 30 great cocktail bars to relax in. In addition to that, we’re previewing the major films coming out this month – there are some real winners, and some serious post-Oscar stinkers – and have an interview 11 with Niall Holohan of Readers Wives, a Dublin Competitions Win concert tickets indie band generating serious buzz. And if and meals out with 2night! you fancy free stuff, we’ve got that too: turn to page 11 for a chance to go to the Tripod after-show party of the Black Eyed Peas, Shakespears Sister’s long-awaited comeback at The Button Factory, the magnificently 12 misanthropic Mark E. Smith and The Fall, and Music - The Naturals Oxford indie sensations Stornoway. 2night chats to Niall Holohan, Between those attractions, our regular round- lead singer of Readers Wives up of the best events in Dublin this April, and the hundreds of venues we’ve scouted out in the ‘Best of Dublin’ section at the back, we hope you’ll find this issue as tasty as we do. -

Programme of Events October
Programme of Events October - December 2015 What is the European Capital of Culture? Each year since 1985, the European Union designates one or more cities as a European Capital of Culture. Chosen cities and their regions are expected to present an innovative year-long cultural programme that highlights the richness and diversity of cultures in Europe. In the year 2020, Ireland and Croatia have been designated as host countries for this prestigious title. Why Compete? The benets of being awarded the European Capital of Culture are economic and social as well as cultural. Galway's bid is being jointly led by Galway City Council and Galway County Council. Galway We’re Backing the Bid is competing against Dublin, Limerick and a coalition of Kilkenny, Waterford and Wexford to become the European Capital of Culture in the year 2020. The Galway bid is both a city and county bid. Let’s Make Galway the What is the status of Galway’s bid? Galway has until 17th October 2015, to submit an 80-page bid document to the European Union. This European Capital of Culture 2020 bid document will outline Galway’s proposed artistic vision and proposed year-long programme of cultural events. On November 12th 2015, a team of 10 people from Galway will present the bid proposal to a panel of 12 European judges. By early December, Galway will nd out if it has been shortlisted to the nal two regions competing for the designation. @galway2020 #IBackGalway 4 5 TOWN HALL THEATRE · BLACK BOX THEATRE · TOWN HALL STUDIO OCTOBER - DECEMBER 2015 PROGRAMME AT A GLANCE MONTH -
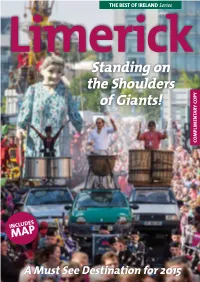
Limerick Guide
THE BEST OF IRELAND Series LimerickStanding on the Shoulders of Giants! COMPLIMENTARY COPY COMPLIMENTARY INCLUDES MAP A Must See Destination for 2015 Limerick Guide Lotta stories in this town. This town. This old, bold, cold town. This big town. This pig town. “Every house a story…This gets up under your skin town…Fill you with wonder town…This quare, rare, my ho-o-ome is there town. Full of life town. Extract from Pigtown by local playwright, Mike Finn. Editor: Rachael Finucane Contributing writers: Rachael Finucane, Bríana Walsh and Cian Meade. Photography: Lorcan O’Connell, Dave Gaynor, Limerick City of Culture, Limerick Marketing Company, Munster Images, Tarmo Tulit, Rachael Finucane and others (see individual photos for details). 2 | The Best Of Ireland Series Limerick Guide Contents THE BEST OF IRELAND Series Contents 4. Introducing Limerick 29. Festivals & Events 93. Further Afield 6. Farewell National 33. Get Active in Limerick 96. Accommodation City of Culture 2014 46. Family Fun 98. Useful Information/ 8. History & Heritage Services 57. Shopping Heaven 17. Arts & Culture 100. Maps 67. Food & Drink A Tourism and Marketing Initiative from Southern Marketing Design Media € For enquiries about inclusion in updated editions of this guide, please contact 061 310286 / [email protected] RRP: 3.00 No part of this publication may be reproduced without the written permission of the publishers. © Southern Marketing Design Media 2015. Every effort has been made in the production of this magazine to ensure accuracy at the time of publication. The editors cannot be held responsible for any errors or omissions, or for any alterations made after publication. -

National Geographic Traveller Article
THE NEW The cultural heritage of the Emerald Isle stretches back millennia, but what about modern Ireland? We explore the source and raise a glass to Irish culture, whether it’s tasting its culinary revolution, exploring the thriving arts movement, tapping our feet to the best new music or diving into the surf scene for a weekend away. The island of Ireland — North and Republic — is alive with stories and experiences IRELAND WORDS PÓL Ó CONGHAILE IMAGE: DAVID SCIORA 74 nationalgeographic.co.uk/travel April 2020 75 IRELAND IRELAND CULINARY REVOLUTION LIMERICK GO TO MARKET Limerick’s storied food scene is informed by its setting, sandwiched between the River Shannon and pastureland — and now its historic market is the focus of a new food tour At Limerick’s Milk Market, I’ve eaten a sausage are changing. There are festivals like roll, and muesli sourdough bread slathered in Pigtown Culture & Food Series, an autumn homemade marmalade, followed by paprika- programme of food-related events. There are battered monkfish fritters, and then somehow also casual stops, such as La Cucina Centro made room for some ‘spiralaytos’ — crisps (Italian) and Canteen (Asian) serving up whizzed from potatoes with a hand drill zingy eats, while a tasting platter I order at device. I’m glad I skipped breakfast. No. 1 Pery Square, a chic Georgian townhouse “Growing up, this was somewhere we hotel, is a hymn to local ingredients like always came on a Saturday morning,” says Ispíní charcuterie and Castleconnell honey. my guide, Siobhán O’Neill. “For the bit of By King John’s Castle, a bold new mural of shopping, or the turkeys for Christmas; local hero Dolores O’Riordan, the late lead there was a little more blood and guts in the singer of The Cranberries, feels like a splash market back then. -

UNIVERSIDAD CARLOS III DE MADRID Doctorado En Ciencia Y Tecnología Informática Phd Thesis Information Leakage and Steganograph
UNIVERSIDAD CARLOS III DE MADRID Doctorado en Ciencia y Tecnología Informática PhD Thesis Information Leakage and Steganography: Detecting and Blocking Covert Channels Author: Jorge Blasco Alís Supervisors: Dr. Julio César Hernández Castro Dr. Pedro Peris López Computer Science Department May 21, 2012 I was just guessing At numbers and figures Pulling the puzzles apart Questions of science Science and progress Do not speak as loud as my heart Coldplay - The Scientist To my parents Agradecimientos Escribir estas líneas es a la vez lo más fácil y lo más difícil de todo este camino. En estos últimos años han sucedido muchas cosas. He reído y he llorado. He sentido la soledad, pero también el más cálido de los abrazos y la mejor de las compañías. Durante este camino, cada una de las personas con las que he compartido un instante de mi vida me ha aportado un granito de arena para convertirme en la persona que soy ahora. Pero no sólo eso. Sé con certeza que si no fuese por cada uno de vosotros, nunca habría llegado al final del camino. En primer lugar tengo que dar gracias a mis tutores Julio y Pedro. Julio, me acuerdo perfectamente cuando decidí empezar esta aventura. Te preguntaba en una de nuestras reuniones si existía la posibilidad de hacer un doctorado, qué era estar en la universidad y si merecía la pena. Acertaste de pleno y sinceramente, te doy las gracias por haberme hecho elegir este camino. Gracias por tu guía y por apoyarme tanto en los ratos buenos, como en los ratos malos, que realmente es cuando más lo he necesitado. -

2007 SXSW Festival
2/22/2018 SXSW 2007 Band Lineup Released About Us Live Sessions Interviews Best Albums of 2012 Subscribe Tickets HearYa - Indie Music Blog Indie Music Blog, Live Sessions, and Daily MP3 Downloads. SXSW 2007 Band Lineup Released by oz on February 12, 2007 http://www.facebook.com/plugins/like.php?href=http%3A%2F%2Fwww.hearya.co Finally…we can start planning SXSW. The list of bands was released a week ago, but I was in Tahoe and couldn’t post it. Thanks to DoneWaiting.com for reformatting the list (it’s a lot of bands) and for the party updates. Our SXSW strategy planning will be much easier thanks to their coverage. Aa (Brooklyn NY); AA Sound System (Edmonton AB); A Band of Bees (Ventnor UK); Aberdeen City (Boston MA); The A-Bones (Brooklyn NY); About (Amsterdam THE NETHERLANDS); A Cursive Memory (Los Angeles CA); Peter Adams And The Nocturnal Collective (Cincinnati OH); Pierre Aderne (Rio de Janeiro BRAZIL); Aesop Rock (Brooklyn NY); A Fine Frenzy (Los Angeles CA); After Forever (Reuver THE NETHERLANDS); Afterhours (Milano ITALY); Against Me! (Gainesville FL); Airbourne (Melbourne AUSTRALIA); Air Traffic (Bournemouth UK); Akimbo (Seattle WA); Tetuzi Akiyama (Tokyo JAPAN); Alabama Thunderpussy (Richmond VA); Alamo Race Track (Amsterdam THE NETHERLANDS); The Alarm Clocks (Cleveland OH); Allison (Mexico D.F. MEXICO); All the Saints (Atlanta GA); All Time Low (Baltimore MD); ALOKE (New York NY); Alternative Champs (Charlotte NC); AM (New Orleans LA); Amber Pacific (Seattle WA); Scott Amendola (Berkeley CA); American Flamewhip (Winnipeg MB); American -

Press Book from 01.03.2013 to 31.03.2013
Press Book from 01.03.2013 to 31.03.2013 Copyright Material. This may only be copied under the terms of a Newspaper Licensing Ireland agreement (www.newspaperlicensing.ie) or wirtten publisher permission. -2- Table of Contents 27/02/2013 Kerryman North: A celebration of ceol, craic, ceilis and Irish culture....................................................................... 3 07/03/2013 Cork Independent: Bell X1, Little Mix, Ke$ha for Marquee.......................................................................................... 7 12/03/2013 Inish Times: Culdaff rocks!................................................................................................................................8 08/03/2013 Irish Independent Tabloid: Delorentos dedicate award to drummer's late mother................................................................ 11 12/03/2013 Fingal Independent: Delorentos scoop Album of the Year award.................................................................................12 08/03/2013 Irish Times: Delorentos sparkle to win top prize............................................................................................ 13 07/03/2013 Sligo Weekender: Dingle band in Furey's Bar.......................................................................................................... 15 28/02/2013 Northern Standard: Eurovision winner to deliver Song Writing Workshop as part of PEACE III Project ThHdTthPjill.... 16 26/03/2013 Western People-Western Sport supplement: Filmmakers and composers collaborate in