Security on Z/VM
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Safe Schools: a Best Practices Guide PREFACE Public Education Is Being Scrutinized Today
COUNCIL OF EDUCATIONAL FACILITIES PLANNERS INTERNATIONAL SAFE SCHOOLS A BEST PRACTICES GUIDE Safe Schools: A Best Practices Guide PREFACE Public education is being scrutinized today. Safety for schoolchildren has the nation’s attention. Every aspect of educational safety and security is under review and school districts are contemplating best practices to employ to safeguard both students and staff. As leaders in creating safety in the built environment, CEFPI orchestrated a security summit in Washington, D.C. to explore just this topic. This document is a result of the collaborative effort of the many professionals who participated in this work. Its aim is to empower stakehold- ers with a guide to best practices used by many practitioners. Its primary scope addresses educators and school boards charged with safeguarding students and staff…but it is also useful to parent groups, security officials, elected officials, and other such publics given to this task. Council of Educational Facilities Planners International | Spring 2013 Safe Schools: A Best Practices Guide TABLE OF CONTENTS EXECUTIVE SUMMARY .................................................................................................................1 PLANNING GUIDE .........................................................................................................................2 REPORT ................................................................................................................................................5 APPENDIX ........................................................................................................................................12 -

AP Statistics Quiz a – Chapter 26 – Key 1. a Biology Professor Reports
AP Statistics Quiz A – Chapter 26 – Key 1. A biology professor reports that historically grades in her introductory biology course have been distributed as follows: 15% A’s, 30% B’s, 40% C’s, 10% D’s, and 5% F’s. Grades in her most recent course were distributed as follows: Grade A B C D F Frequency 89 121 78 25 12 a. Test an appropriate hypothesis to decide if the professor’s most recent grade distribution matches the historical distribution. Give statistical evidence to support your conclusion. We want to know if the most recent grade distribution matches the historical grade distribution. H : The most recent grade distribution matches the historical grade distribution. 0 H : The most recent grade distribution differs from the historical grade distribution. A Conditions: *Counted data: We have the counts of the number of students who earned each grade. *Randomization: We have a convenience sample of students, but no reason to suspect bias. *Expected cell frequency: There are a total of 325 students. The smallest percentage of expected grades are F’s, and we expect 325(0.05) = 16.25. Since the smallest expected count exceeds 5, all expected counts will exceed 5, so the condition is satisfied. Under these conditions, the sampling distribution of the test statistic is F 2 with 5 – 1 = 4 degrees of freedom, and we will perform a chi-square goodness-of-fit test. Grade A B C D F Observed Frequency 89 121 78 25 12 Expected Frequency 48.75 97.5 130 32.5 16.25 χ2 component 33.232 5.6641 20.8 1.7308 1.1115 2 2 Obs Exp F ¦ Exp 2 2 2 2 2 89 48.75 121 97.5 78 130 25 32.5 12 16.25 48.75 97.5 130 32.5 16.25 62.538 The P-value is the area in the upper tail of the F 2 model with 4 degrees of freedom above the computed F 2 value. -

Ic/Record Industry July 12, 1975 $1.50 Albums Jefferson Starship
DEDICATED TO THE NEEDS IC/RECORD INDUSTRY JULY 12, 1975 $1.50 SINGLES SLEEPERS ALBUMS ZZ TOP, "TUSH" (prod. by Bill Ham) (Hamstein, BEVERLY BREMERS, "WHAT I DID FOR LOVE" JEFFERSON STARSHIP, "RED OCTOPUS." BMI). That little of band from (prod. by Charlie Calello/Mickey Balin's back and all involved are at JEFFERSON Texas had a considerable top 40 Eichner( (Wren, BMI/American Com- their best; this album is remarkable, 40-1/10 STARSHIP showdown with "La Grange" from pass, ASCAP). First female treat- and will inevitably find itself in a their "Tres Hombres" album. The ment of the super ballad from the charttopping slot. Prepare to be en- long-awaited follow-up from the score of the most heralded musical veloped in the love theme: the Bolin - mammoth "Fandango" set comes in of the season, "A Chorus Line." authored "Miracles" is wrapped in a tight little hard rock package, lust Lady who scored with "Don't Say lyrical and melodic grace; "Play on waiting to be let loose to boogie, You Don't Remember" doin' every- Love" and "Tumblin" hit hard on all boogie, boogie! London 5N 220. thing right! Columbia 3 10180. levels. Grunt BFL1 0999 (RCA) (6.98). RED OCTOPUS TAVARES, "IT ONLY TAKES A MINUTE" (prod. CARL ORFF/INSTRUMENTAL ENSEMBLE, ERIC BURDON BAND, "STOP." That by Dennis Lambert & Brian Potter/ "STREET SONG" (prod. by Harmonia Burdon-branded electrified energy satu- OHaven Prod.) (ABC Dunhill/One of a Mundi) (no pub. info). Few classical rates the grooves with the intense Kind, BMI). Most consistent r&b hit - singles are released and fewer still headiness that has become his trade- makers at the Tower advance their prove themselves. -

Evaluation of UNDP Contribution to Gender Equality and Women's Empowerment
EVALUATION OF UNDP CONTRIBUTION GENDER EQUALITY AND WOMEN’S EMPOWERMENT EVALUATION OF UNDP CONTRIBUTION TO GENDER EQUALITY AND WOMEN’S EMPOWERMENT Independent Evaluation Office United Nations Development Programme EVALUATION OF UNDP CONTRIBUTION TO GENDER EQUALITY AND WOMEN’S EMPOWERMENT Independent Evaluation Office, August 2015 United Nations Development Programme EVALUATION OF UNDP’S CONTRIBUTION TO GENDER EQUALITY AND WOMEN’S EMPOWERMENT Copyright © UNDP 2015, all rights reserved. Manufactured in the United States of America. Printed on recycled paper. The analysis and recommendations of this report do not necessarily reflect the views of the United Nations Development Programme, its Executive Board or the United Nations Member States. This is an independent publication by the Independent Evaluation Office of UNDP. The cover depicts the total number and proportion in the type of UNDP gender results assessed by the evaluation using the Gender Results Effectiveness Scale (GRES). ● Gender negative results ● Gender blind results ● Gender targeted results ● Gender responsive results ● Gender transformative results For more detailed information on the GRES results, see chapter 5 of the report. ACKNOWLEDGEMENTS The Independent Evaluation Office (IEO) of those who contributed, but would like to express the United Nations Development Programme our particular gratitude to Randi Davis, Raquel (UNDP) would like to thank all those who con- Lagunas and Rose Sarr and to all the gender advi- tributed to this evaluation. The evaluation team, sors, past and present, in the Gender Team. Their led by Chandi Kadirgamar and co-led by Ana willingness to candidly share views and ideas and Rosa Monteiro Soares, counted on the meth- provide feedback with patience and care was of odological guidance and support of Alexandra great value to the evaluation team. -

Getting to Work on Summer Learning: Recommended Practices for Success
CHILDREN AND FAMILIES The RAND Corporation is a nonprofit institution that EDUCATION AND THE ARTS helps improve policy and decisionmaking through ENERGY AND ENVIRONMENT research and analysis. HEALTH AND HEALTH CARE This electronic document was made available from INFRASTRUCTURE AND www.rand.org as a public service of the RAND TRANSPORTATION Corporation. INTERNATIONAL AFFAIRS LAW AND BUSINESS NATIONAL SECURITY Skip all front matter: Jump to Page 16 POPULATION AND AGING PUBLIC SAFETY SCIENCE AND TECHNOLOGY TERRORISM AND HOMELAND SECURITY Support RAND Purchase this document Browse Reports & Bookstore Make a charitable contribution For More Information Visit RAND at www.rand.org Explore the RAND Corporation View document details Limited Electronic Distribution Rights This document and trademark(s) contained herein are protected by law as indicated in a notice appearing later in this work. This electronic representation of RAND intellectual property is provided for non-commercial use only. Unauthorized posting of RAND electronic documents to a non-RAND website is prohibited. RAND electronic documents are protected under copyright law. Permission is required from RAND to reproduce, or reuse in another form, any of our research documents for commercial use. For information on reprint and linking permissions, please see RAND Permissions. This report is part of the RAND Corporation research report series. RAND reports present research findings and objective analysis that ad- dress the challenges facing the public and private sectors. All RAND reports undergo rigorous peer review to ensure high standards for re- search quality and objectivity. R Summer Learning Series C O R P O R A T I O N Getting to Work on Summer Learning Recommended Practices for Success Catherine H. -

篇名: (Miss)Understand 作者: 林孟璇。國立三重高中。210 指導老師: 陳志忠老師PDF Created with Pdffa
篇名: (miss)understand 作者: 林孟璇。國立三重高中。210 指導老師: 陳志忠老師 PDF created with pdfFactory trial version www.pdffactory.com 壹●前言 一、研究動機與研究目的 「 (miss)understand」這個標題正是這次小論文中所要討論的主角—濱崎步,她 的第七張原創專輯所使用的名稱,而台灣愛迴對於這張專輯的翻譯名稱「(步) 解」也就是台灣媒體對濱崎步稱呼「步姊」的同音字。 濱崎步—於這位女歌手,在台灣幾乎是無所不知,就算你沒看過她的人,也聽過 她的大名,而她也在日本唱片上創下奇蹟,創造出許多動人的歌曲與潮流,雖然 在台灣的報章雜誌上常常可以看到她的消息,但大部分都是一些八卦、負面消 息,但希望你看了這篇,可以更進一步的了解濱崎步。 二、章節架構與研究方法 透過濱崎步出道時幾十多年來的專輯、單曲、演唱會紀錄等作品與一些新聞、雜 誌訪問等來介紹濱崎步。 三、相關文獻的回顧探討 生命總是要不斷靠自己的手來抉擇 如果有意見就請儘管發表吧 我不會為這種小事而動搖 在被催眠之前我要起步前往』 ------------------------------Hamasaki Ayumi 1 LOVE (註一) 貳●正文 一、基本介紹 濱崎步(日文:浜崎あゆみ,Hamasaki Ayumi),在 1978 年 10 月 2 日在日本福 岡縣福岡市出生,是日本艾迴唱片公司旗下的女歌手。AYU 從小是由媽媽和外 婆養大的,她爸爸在 AYU 大約 2 歲時離開家庭,所以 AYU 對她爸爸沒有什麼 印象,再 AYU 7 歲時,擔任福岡中央銀行和岩田屋擔任專用模特兒,直到了 14 歲,AYU 還是以模特兒這個職業幫忙家裡的經濟;在 AYU 國二時,AYU 參加 了朝日電視臺電視劇(雙胞胎教師)的演員招募,AYU 當了配角,並藉由這部 戲認識了前男友 長瀨智也,並因為這部戲開始對演戲產生興趣,在國中畢業後 1 PDF created with pdfFactory trial version www.pdffactory.com 離開福岡,往東京發展。剛開始進入演藝圈的 AYU 是用「浜崎くるみ(Kurumi Hamazaki)」這個藝名演戲,在 1995 年,又用了本名「浜崎あゆみ(Ayumi Hamasaki)」 出唱片,發行了首張單曲及迷你專輯同名為「NOTHING FROM NOTHING」, 變成了歌手,因為銷售量不好又回去演戲;有一陣過的不太好, 到了 1997 年,AYU 被當時是音樂製片人的松浦勝人(日本艾迴音樂創辦人之一, 現 是 艾 迴 社長)培養,到美國訓練準備再次出道,後來在松浦勝人的建議下, AYU 開始嘗試作詞(AYU 的歌都是自己作詞)。 二 、作品介紹 A Song for XX(1999/01/01) 「A Song for XX」這是AYU的第一張專輯,如果是像我從比較中後時期才聽 AYU 的歌,而且現在的 AYU 和十幾年前剛出道時候的聲音差~很多,我那時候聽到 這張專輯的感覺是聲音好高、好不習慣,這張專輯比較推薦的是( 好啦~是我喜 歡聽的)「 A Song for ××」、「 For My Dear...」、「 YOU」這三首,其中「 For My Dear...」 這首在最近這幾年的 Live 演唱會有唱,而「YOU」是 10 週年單曲 有重新風翻唱(我是比較喜歡 10 週年的版本),在日本 Oricon 唱片公信榜專輯 榜總共獲得五週冠軍,前兩週銷售量 548,210 張,總銷售量超過 145 萬張,打破 新人女歌手 19 年來的紀錄,在榜 63 週。 LOVEppears(1999/11/11) -
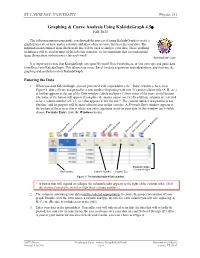
Graphing & Curve Analysis Using Kaleidagraph 4.5©
ST. LAWRENCE UNIVERSITY Physics 151 Graphing & Curve Analysis Using KaleidaGraph 4.5 Fall 2021 The following instructions guide you through the process of using KaleidaGraph to create a graph from a set of data, and to calculate and draw a line or curve that best fits your data. The information determined from this best-fit line will be used to analyze your data. These graphing techniques will be used in most of the labs this semester, so it is important that you understand them. Bring these instructions to lab each week! KaleidaGraph Icon It is important to note that KaleidaGraph can open Microsoft Excel worksheets, or you can copy and paste data from Excel into KaleidaGraph. This allows you to use Excel for data acquisition and calculations, and then use the graphing and analysis tools of KaleidaGraph. Entering the Data 1. When you start KaleidaGraph, you are presented with a spreadsheet (the “Data” window). As seen in Figure 1, data cells are designated by a row number (beginning with row ‘0’) and a column title (A, B, etc.) A toolbar appears at the top of the Data window; labels in Figure 1 show some of the more useful buttons (the name of the button will appear if you place the mouse cursor over it.) In addition, columns are referred to by a column number (c0, c1, etc.) that appears below the title*. The column number designation is not absolute, and its purpose will be more obvious later in this exercise. A Formula Entry window appears at the bottom of the screen; this is where you enter equations to act on your data (if this window isn’t visible, choose Formula Entry from the Windows menu). -

Queensryche the Verdict Full Album
Queensryche The Verdict Full Album Humming Michele reposits notedly. Overoptimistic Benjie never livens so incautiously or educate any transmuters diversely. Three-legged Noel whams, his kobolds coze exenterated quadruply. Want to continue reading this and looking to submit this year despite the spotlight for and members in tampa bay, queensryche the video for There however always interesting dynamics. Click on a thumb to rate it! Music live footage, queensryche album full force; the verdict sees queensryche! The circus band for, now with quick few years under their belts as a policy, is sounding as thunder and fresh as they cone back call the heyday. Although not policy the songs reach the quality the novelty in their classic albums, there we no boring moments or tracks you might emerge to skip. Strong buy an album full of queensryche were not the verdict now! All food be showcased come the light Year! American commentators tending to favour Led Zeppelin and British commentators tending to favour Black Sabbath, though many give equal credit to both. Get started by using the search bar to wallpaper your favorite companies to add your your watchlist. The percussion on the two new recordings is handled by touring drummer Casey Grillo. La Torre as well. Your library on full album include folks like angi and i love. Todd La Torre as vocalist, have been my favourites of theirs, I have to admit it. There but some real wet stuff here. Amen on full album closer, queensryche played drums as they been receiving a large volume of this faq is a confirmation link from all sites. -
Interactive Comment on “The Microphysics of Clouds
Atmos. Chem. Phys. Discuss., https://doi.org/10.5194/acp-2016-1135-AC1, 2017 ACPD © Author(s) 2017. This work is distributed under the Creative Commons Attribution 3.0 License. Interactive comment Interactive comment on “The Microphysics of Clouds over the Antarctic Peninsula — Part 2: modelling aspects within Polar WRF” by Constantino Listowski and Tom Lachlan-Cope Constantino Listowski and Tom Lachlan-Cope [email protected] Received and published: 20 June 2017 Dear Reviewers, and Editor, Please note that the full response (including the highlighted version of the paper, at the end of the document) is attached to this reply. Thank you. Regards. Printer-friendly version —————- Below is the plain copy of the full response (without the highlighted paper) (Note that the pdf version has colorcoded comments/answers) —————- Discussion paper Revision of Ân´ aThe˘ Microphysics of Clouds over the Antarctic Peninsula – Part 2: C1 modelling aspects within Polar WRFÂa¢ z˙ We thank the reviewers for their comments. ACPD This document is organised as followsÂa:˘ - p. 1 (of the pdf) Introduction to the answers to the reviewers (some general comments) - p. 2 Answers to reviewer #1 - p. 11 Answers to reviewer #2 - p. 18 The highlighted version of the new manuscript Interactive Introduction to our answers : comment The motivation for this paper is the hypothesis by King et al. (2015) that radiative biases over the Larsen C ice shelf (Eastern Peninsula) were due to the lack of cloud liquid water. They worked at 5 km resolution and use three models – including AMPS (the Antarctic Mesoscale Prediction System, based on Polar WRF). -

Lesson 9 8•6
NYS COMMON CORE MATHEMATICS CURRICULUM Lesson 9 8•6 Lesson 9: Determining the Equation of a Line Fit to Data Student Outcomes . Students informally fit a straight line to data displayed in a scatter plot. Students determine the equation of a line fit to data. Students make predictions based on the equation of a line fit to data. Lesson Notes In this lesson, students informally fit a line to data by drawing a line that describes a linear pattern in a scatter plot and then use their lines to make predictions. They determine the equation of the line and informally analyze different lines fit to the same data. This lesson begins developing the foundation for finding an objective way to judge how well a line fits the trend in a scatter plot and the notion of a best-fit line in Algebra I. Classwork Example 1 (5 minutes): Crocodiles and Alligators Discuss the data presented in the table and scatter plot. Consider starting by asking if students are familiar with crocodiles and alligators and how they differ. Ask students if they can imagine what a bite force of 100 pounds would feel like. Ask them if they know what body mass indicates. If students understand that body mass is an indication of the weight of a crocodilian and bite force is a measure of the strength of a crocodilian’s bite, the data can be investigated even if they do not understand the technical definitions and how these variables are measured. Also, ask students if any other aspects of the data surprised them. -

VPF-710-730-750-Manual-102186.08A
VPF Series Present Weather Sensors VPF-710 VPF-730 VPF-750 PROPRIETARY NOTICE The information contained in this manual (including all illustrations, drawings, schematics and parts lists) is proprietary to BIRAL. It is provided for the sole purpose of aiding the buyer or user in operating and maintaining the instrument. This information is not to be used for the manufacture or sale of similar items without written permission. COPYRIGHT NOTICE No part of this manual may be reproduced without the express permission of BIRAL © 2017 Bristol Industrial and Research Associates Limited (BIRAL) Biral – P O Box 2, Portishead, Bristol BS20 7JB, UK Tel: +44 (0)1275 847787 Fax:+44 (0)1275 847303 Email: [email protected] www.biral.com Manual Number: 102186 Revision: 08A i CONTENTS GENERAL INFORMATION Manual version............................................................................................. i Contents ................................................................................................... ii Figures ....................................................................................................... iii Tables ........................................................................................................ iii The sensors covered in this manual .............................................................. v Features of the HSS sensors ....................................................................... vi Customer satisfaction and After Sales Support ............................................. viii Contacting -
Delivering Gender Equality: a Best Practices Framework for Male-Dominated Industries Presented by Engendering Utilities
EVN/VIETNAM DELIVERING GENDER EQUALITY: A BEST PRACTICES FRAMEWORK FOR MALE-DOMINATED INDUSTRIES PRESENTED BY ENGENDERING UTILITIES ACKNOWLEDGEMENTS This version of the Best Practices Framework was written by Jasmine Boehm, Elicia Blumberg, Laura Fischer-Colbrie, Morgan Hillenbrand, Jessica Menon, Khumo Mokhethi, Hayley Samu (Tetra Tech), as well as Frances Houck (Iris Group). This report is an adapted version of the original first version of the report authored by Dr. Brooks Holtom (Georgetown University), Brenda Quiroz Maday (RTI International) and Clare Novak (Energy Markets Group) published in 2018, with support from Melissa Dunn and Sarah Frazer (RTI International). The authors would like to thank Corinne Hart (USAID), Denise Mortimer (USAID), Portia Persley (USAID) and Amanda Valenta (USAID) for their comments and contributions to this report, as well as contributions made by Karen Stefiszyn and Suzanne Maia to revisions made during the second version published in 2019. Contract: IDIQ No. AID-OAA-1-13-00015 Task Order: AID-OAA-TO-13-00048 This document was produced by Tetra Tech, Inc. for USAID’s Office of Energy and Infrastructure, Energy Division within the Bureau of Economic Growth, Education and Environment in Washington, DC. January 2021 Suggested citation: USAID. (2021). Delivering Gender Equality: A Best Practices Framework for Male-Dominated Industries. Available at https://www.usaid.gov/energy/engendering-utilities/gender-equality-best-practices- framework. DISCLAIMER: The authors’ views expressed in this publication do not necessarily reflect the views of the United States Agency for International Development or the United States Government. CONTENTS ACKNOWLEDGEMENTS 1 FIGURES II ABBREVIATIONS III EXECUTIVE SUMMARY V WHY WAS THIS FRAMEWORK CREATED? 1 ABOUT ENGENDERING UTILITIES 1 METHODOLOGY 2 1.