Generalized Sphere-Packing and Sphere-Covering Bounds on the Size
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Selective Maximum Coverage and Set Packing
Selective Maximum Coverage and Set Packing Felix J. L. Willamowski1∗ and Bj¨ornF. Tauer2y 1 Lehrstuhl f¨urOperations Research RWTH Aachen University [email protected] 2 Lehrstuhl f¨urManagement Science RWTH Aachen University [email protected] Abstract. In this paper we introduce the selective maximum coverage and the selective maximum set packing problem and variants of them. Both problems are strongly related to well studied problems such as maximum coverage, set packing, and (bipartite) hypergraph matching. The two problems are given by a collection of subsets of a ground set and index subsets of the indices of these subsets. Additionally, there are weights either for each element of the ground set or each subset for each index subset. The goal is to find at most one index per index subset such that the total weight of covered elements or of disjoint subsets is maximum. Applications arise in transportation, e.g., dispatching for ride- sharing services. We prove strong intractability results for the problems and provide almost best possible approximation guarantees. 1 Introduction and Preliminaries We introduce the selective maximum coverage problem (smc) generalizing the weighted maximum k coverage problem (wmkc) which is given by a finite ground set X with weights w : X ! Q≥0, a finite collection S of subsets of X, and an 0 integer k 2 Z≥0. The goal is to find a subcollection S ⊆ S containing at most k P subsets and maximizing the total weight of covered elements x2X0 w(x) with 0 X = [S2S0 S. For unit weights, w ≡ 1, the problem is called maximum k coverage problem (mkc). -

Exact Algorithms and APX-Hardness Results for Geometric Packing and Covering Problems∗
Exact Algorithms and APX-Hardness Results for Geometric Packing and Covering Problems∗ Timothy M. Chan† Elyot Grant‡ March 29, 2012 Abstract We study several geometric set cover and set packing problems involv- ing configurations of points and geometric objects in Euclidean space. We show that it is APX-hard to compute a minimum cover of a set of points in the plane by a family of axis-aligned fat rectangles, even when each rectangle is an ǫ-perturbed copy of a single unit square. We extend this result to several other classes of objects including almost-circular ellipses, axis-aligned slabs, downward shadows of line segments, downward shad- ows of graphs of cubic functions, fat semi-infinite wedges, 3-dimensional unit balls, and axis-aligned cubes, as well as some related hitting set prob- lems. We also prove the APX-hardness of a related family of discrete set packing problems. Our hardness results are all proven by encoding a highly structured minimum vertex cover problem which we believe may be of independent interest. In contrast, we give a polynomial-time dynamic programming algo- rithm for geometric set cover where the objects are pseudodisks containing the origin or are downward shadows of pairwise 2-intersecting x-monotone curves. Our algorithm extends to the weighted case where a minimum-cost cover is required. We give similar algorithms for several related hitting set and discrete packing problems. 1 Introduction In a geometric set cover problem, we are given a range space (X, )—a universe X of points in Euclidean space and a pre-specified configurationS of regions or geometric objects such as rectangles or half-planes. -
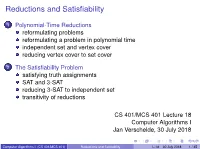
Reductions and Satisfiability
Reductions and Satisfiability 1 Polynomial-Time Reductions reformulating problems reformulating a problem in polynomial time independent set and vertex cover reducing vertex cover to set cover 2 The Satisfiability Problem satisfying truth assignments SAT and 3-SAT reducing 3-SAT to independent set transitivity of reductions CS 401/MCS 401 Lecture 18 Computer Algorithms I Jan Verschelde, 30 July 2018 Computer Algorithms I (CS 401/MCS 401) Reductions and Satifiability L-18 30 July 2018 1 / 45 Reductions and Satifiability 1 Polynomial-Time Reductions reformulating problems reformulating a problem in polynomial time independent set and vertex cover reducing vertex cover to set cover 2 The Satisfiability Problem satisfying truth assignments SAT and 3-SAT reducing 3-SAT to independent set transitivity of reductions Computer Algorithms I (CS 401/MCS 401) Reductions and Satifiability L-18 30 July 2018 2 / 45 reformulating problems The Ford-Fulkerson algorithm computes maximum flow. By reduction to a flow problem, we could solve the following problems: bipartite matching, circulation with demands, survey design, and airline scheduling. Because the Ford-Fulkerson is an efficient algorithm, all those problems can be solved efficiently as well. Our plan for the remainder of the course is to explore computationally hard problems. Computer Algorithms I (CS 401/MCS 401) Reductions and Satifiability L-18 30 July 2018 3 / 45 imagine a meeting with your boss ... From Computers and intractability. A Guide to the Theory of NP-Completeness by Michael R. Garey and David S. Johnson, Bell Laboratories, 1979. Computer Algorithms I (CS 401/MCS 401) Reductions and Satifiability L-18 30 July 2018 4 / 45 what you want to say is From Computers and intractability. -
8. NP and Computational Intractability
Chapter 8 NP and Computational Intractability CS 350 Winter 2018 1 Algorithm Design Patterns and Anti-Patterns Algorithm design patterns. Ex. Greedy. O(n log n) interval scheduling. Divide-and-conquer. O(n log n) FFT. Dynamic programming. O(n2) edit distance. Duality. O(n3) bipartite matching. Reductions. Local search. Randomization. Algorithm design anti-patterns. NP-completeness. O(nk) algorithm unlikely. PSPACE-completeness. O(nk) certification algorithm unlikely. Undecidability. No algorithm possible. 2 8.1 Polynomial-Time Reductions Classify Problems According to Computational Requirements Q. Which problems will we be able to solve in practice? A working definition. [von Neumann 1953, Godel 1956, Cobham 1964, Edmonds 1965, Rabin 1966] Those with polynomial-time algorithms. Yes Probably no Shortest path Longest path Matching 3D-matching Min cut Max cut 2-SAT 3-SAT Planar 4-color Planar 3-color Bipartite vertex cover Vertex cover Primality testing Factoring 4 Classify Problems Desiderata. Classify problems according to those that can be solved in polynomial-time and those that cannot. Provably requires exponential-time. Given a Turing machine, does it halt in at most k steps? (the Halting Problem) Given a board position in an n-by-n generalization of chess, can black guarantee a win? Frustrating news. Huge number of fundamental problems have defied classification for decades. This chapter. Show that these fundamental problems are "computationally equivalent" and appear to be different manifestations of one really hard problem. 5 Polynomial-Time Reduction Desiderata'. Suppose we could solve X in polynomial-time. What else could we solve in polynomial time? don't confuse with reduces from Reduction. -

Scribe Notes
6.440 Essential Coding Theory Feb 19, 2008 Lecture 4 Lecturer: Madhu Sudan Scribe: Ning Xie Today we are going to discuss limitations of codes. More specifically, we will see rate upper bounds of codes, including Singleton bound, Hamming bound, Plotkin bound, Elias bound and Johnson bound. 1 Review of last lecture n k Let C Σ be an error correcting code. We say C is an (n, k, d)q code if Σ = q, C q and ∆(C) d, ⊆ | | | | ≥ ≥ where ∆(C) denotes the minimum distance of C. We write C as [n, k, d]q code if furthermore the code is a F k linear subspace over q (i.e., C is a linear code). Define the rate of code C as R := n and relative distance d as δ := n . Usually we fix q and study the asymptotic behaviors of R and δ as n . Recall last time we gave an existence result, namely the Gilbert-Varshamov(GV)→ ∞ bound constructed by greedy codes (Varshamov bound corresponds to greedy linear codes). For q = 2, GV bound gives codes with k n log2 Vol(n, d 2). Asymptotically this shows the existence of codes with R 1 H(δ), which is similar≥ to− Shannon’s result.− Today we are going to see some upper bound results, that≥ is,− code beyond certain bounds does not exist. 2 Singleton bound Theorem 1 (Singleton bound) For any code with any alphabet size q, R + δ 1. ≤ Proof Let C Σn be a code with C Σ k. The main idea is to project the code C on to the first k 1 ⊆ | | ≥ | | n k−1 − coordinates. -

An Introduction to Coding Theory
An introduction to coding theory Adrish Banerjee Department of Electrical Engineering Indian Institute of Technology Kanpur Kanpur, Uttar Pradesh India Feb. 6, 2017 Lecture #7A: Bounds on the size of a code Adrish Banerjee Department of Electrical Engineering Indian Institute of Technology Kanpur Kanpur, Uttar Pradesh India An introduction to coding theory Outline of the lecture Hamming bound Adrish Banerjee Department of Electrical Engineering Indian Institute of Technology Kanpur Kanpur, Uttar Pradesh India An introduction to coding theory Outline of the lecture Hamming bound Perfect codes Adrish Banerjee Department of Electrical Engineering Indian Institute of Technology Kanpur Kanpur, Uttar Pradesh India An introduction to coding theory Outline of the lecture Hamming bound Perfect codes Singleton bound Adrish Banerjee Department of Electrical Engineering Indian Institute of Technology Kanpur Kanpur, Uttar Pradesh India An introduction to coding theory Outline of the lecture Hamming bound Perfect codes Singleton bound Maximum distance separable codes Adrish Banerjee Department of Electrical Engineering Indian Institute of Technology Kanpur Kanpur, Uttar Pradesh India An introduction to coding theory Outline of the lecture Hamming bound Perfect codes Singleton bound Maximum distance separable codes Plotkin Bound Adrish Banerjee Department of Electrical Engineering Indian Institute of Technology Kanpur Kanpur, Uttar Pradesh India An introduction to coding theory Outline of the lecture Hamming bound Perfect codes Singleton bound Maximum distance separable codes Plotkin Bound Gilbert-Varshamov bound Adrish Banerjee Department of Electrical Engineering Indian Institute of Technology Kanpur Kanpur, Uttar Pradesh India An introduction to coding theory Bounds on the size of a code The basic problem is to find the largest code of a given length, n and minimum distance, d. -
Algebraic Geometric Codes: Basic Notions Mathematical Surveys and Monographs
http://dx.doi.org/10.1090/surv/139 Algebraic Geometric Codes: Basic Notions Mathematical Surveys and Monographs Volume 139 Algebraic Geometric Codes: Basic Notions Michael Tsfasman Serge Vladut Dmitry Nogin American Mathematical Society EDITORIAL COMMITTEE Jerry L. Bona Peter S. Landweber Michael G. Eastwood Michael P. Loss J. T. Stafford, Chair Our research while working on this book was supported by the French National Scien tific Research Center (CNRS), in particular by the Inst it ut de Mathematiques de Luminy and the French-Russian Poncelet Laboratory, by the Institute for Information Transmis sion Problems, and by the Independent University of Moscow. It was also supported in part by the Russian Foundation for Basic Research, projects 99-01-01204, 02-01-01041, and 02-01-22005, and by the program Jumelage en Mathematiques. 2000 Mathematics Subject Classification. Primary 14Hxx, 94Bxx, 14G15, 11R58; Secondary 11T23, 11T71. For additional information and updates on this book, visit www.ams.org/bookpages/surv-139 Library of Congress Cataloging-in-Publication Data Tsfasman, M. A. (Michael A.), 1954- Algebraic geometry codes : basic notions / Michael Tsfasman, Serge Vladut, Dmitry Nogin. p. cm. — (Mathematical surveys and monographs, ISSN 0076-5376 ; v. 139) Includes bibliographical references and index. ISBN 978-0-8218-4306-2 (alk. paper) 1. Coding theory. 2. Number theory. 3. Geometry, Algebraic. I. Vladut, S. G. (Serge G.), 1954- II. Nogin, Dmitry, 1966- III. Title. QA268 .T754 2007 003'.54—dc22 2007061731 Copying and reprinting. Individual readers of this publication, and nonprofit libraries acting for them, are permitted to make fair use of the material, such as to copy a chapter for use in teaching or research. -
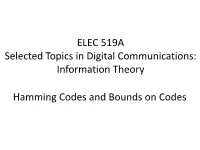
ELEC 619A Selected Topics in Digital Communications: Information Theory
ELEC 519A Selected Topics in Digital Communications: Information Theory Hamming Codes and Bounds on Codes Single Error Correcting Codes 2 Hamming Codes • (7,4,3) Hamming code 1 0 0 0 0 1 1 0 1 0 0 1 0 1 GIP | 0 0 1 0 1 1 0 0 0 0 1 1 1 1 • (7,3,4) dual code 0 1 1 1 1 0 0 T HPI -| 1011010 1 1 0 1 0 0 1 3 • The minimum distance of a code C is equal to the minimum number of columns of H which sum to zero • For any codeword c h0 h T 1 cH [c,c,...,c01 n1 ] ch 0011 ch ...c n1n1 h 0 hn1 where ho, h1, …, hn-1 are the column vectors of H T • cH is a linear combination of the columns of H 4 Significance of H • For a codeword of weight w (w ones), cHT is a linear combination of w columns of H. • Thus there is a one-to-one mapping between weight w codewords and linear combinations of w columns of H that sum to 0. • The minimum value of w which results in cHT=0, i.e., codeword c with weight w, determines that dmin = w 5 Distance 1 and 2 Codes • (5,2,1) code 10100 10110 HG= 10010 = 01000 00001 • (5,2,2) codes 11100 10110 HG= 11010 = 01110 00001 6 (7,4,3) Code • A codeword with weight dmin = 3 is given by the first row of G: c = 1000011 • The linear combination of the first and last 2 columns in H gives T T T T (011) +(010) +(001) = (000) • Thus a minimum of 3 columns (= dmin) are required to get a zero value for cHT 7 Binary Hamming Codes Let m be an integer and H be an m (2m - 1) matrix with columns which are the non-zero distinct elements from Vm. -

Classification of Perfect Codes and Minimal Distances in the Lee Metric
Master Thesis Classification of perfect codes and minimal distances in the Lee metric Naveed Ahmed 1982-06-20 Waqas Ahmed 1982-09-13 Subject: Mathematics Level: Advance Course code: 5MA12E Abstract Perfect codes and minimal distance of a code have great importance in the study of theory of codes. The perfect codes are classified generally and in particular for the Lee met- ric. However, there are very few perfect codes in the Lee metric. The Lee metric has nice properties because of its definition over the ring of integers residue modulo q.Itis conjectured that there are no perfect codes in this metric for q > 3, where q is a prime number. The minimal distance comes into play when it comes to detection and correction of error patterns in a code. A few bounds on the number of codewords and minimal distance of a code are discussed. Some examples for the codes are constructed and their minimal distance is calculated. The bounds are illustrated with the help of the results obtained. Key-words: Hamming metric; Lee metric; Perfect codes; Minimal distance iii Acknowledgments This thesis is written as a part of the Degree of Master of Science in Mathematics at Linnaeus University, Sweden. It is written at the School of Computer Science, Physics and Mathematics. We would like to thank our supervisor Per-Anders Svensson who has been very sup- porting throughout the whole period. We are also obliged to him for giving us chance to work under his supervision. We would also like to thank our Program Manager Marcus Nilsson who has been very helpful and very cooperative within all matters, and also all the respectable faculty members of the department. -

MAS309 Coding Theory
MAS309 Coding theory Matthew Fayers January–March 2008 This is a set of notes which is supposed to augment your own notes for the Coding Theory course. They were written by Matthew Fayers, and very lightly edited my me, Mark Jerrum, for 2008. I am very grateful to Matthew Fayers for permission to use this excellent material. If you find any mistakes, please e-mail me: [email protected]. Thanks to the following people who have already sent corrections: Nilmini Herath, Julian Wiseman, Dilara Azizova. Contents 1 Introduction and definitions 2 1.1 Alphabets and codes . 2 1.2 Error detection and correction . 2 1.3 Equivalent codes . 4 2 Good codes 6 2.1 The main coding theory problem . 6 2.2 Spheres and the Hamming bound . 8 2.3 The Singleton bound . 9 2.4 Another bound . 10 2.5 The Plotkin bound . 11 3 Error probabilities and nearest-neighbour decoding 13 3.1 Noisy channels and decoding processes . 13 3.2 Rates of transmission and Shannon’s Theorem . 15 4 Linear codes 15 4.1 Revision of linear algebra . 16 4.2 Finite fields and linear codes . 18 4.3 The minimum distance of a linear code . 19 4.4 Bases and generator matrices . 20 4.5 Equivalence of linear codes . 21 4.6 Decoding with a linear code . 27 5 Dual codes and parity-check matrices 30 5.1 The dual code . 30 5.2 Syndrome decoding . 34 1 2 Coding Theory 6 Some examples of linear codes 36 6.1 Hamming codes . 37 6.2 Existence of codes and linear independence . -

Math 550 Coding and Cryptography Workbook J. Swarts 0121709 Ii Contents
Math 550 Coding and Cryptography Workbook J. Swarts 0121709 ii Contents 1 Introduction and Basic Ideas 3 1.1 Introduction . 3 1.2 Terminology . 4 1.3 Basic Assumptions About the Channel . 5 2 Detecting and Correcting Errors 7 3 Linear Codes 13 3.1 Introduction . 13 3.2 The Generator and Parity Check Matrices . 16 3.3 Cosets . 20 3.3.1 Maximum Likelihood Decoding (MLD) of Linear Codes . 21 4 Bounds for Codes 25 5 Hamming Codes 31 5.1 Introduction . 31 5.2 Extended Codes . 33 6 Golay Codes 37 6.1 The Extended Golay Code : C24. ....................... 37 6.2 The Golay Code : C23.............................. 40 7 Reed-Muller Codes 43 7.1 The Reed-Muller Codes RM(1, m) ...................... 46 8 Decimal Codes 49 8.1 The ISBN Code . 49 8.2 A Single Error Correcting Decimal Code . 51 8.3 A Double Error Correcting Decimal Code . 53 iii iv CONTENTS 8.4 The Universal Product Code (UPC) . 56 8.5 US Money Order . 57 8.6 US Postal Code . 58 9 Hadamard Codes 61 9.1 Background . 61 9.2 Definition of the Codes . 66 9.3 How good are the Hadamard Codes ? . 67 10 Introduction to Cryptography 71 10.1 Basic Definitions . 71 10.2 Affine Cipher . 73 10.2.1 Cryptanalysis of the Affine Cipher . 74 10.3 Some Other Ciphers . 76 10.3.1 The Vigen`ereCipher . 76 10.3.2 Cryptanalysis of the Vigen`ereCipher : The Kasiski Examination . 77 10.3.3 The Vernam Cipher . 79 11 Public Key Cryptography 81 11.1 The Rivest-Shamir-Adleman (RSA) Cryptosystem . -

Packing Triangles in Low Degree Graphs and Indifference Graphsଁ Gordana Mani´C∗, Yoshiko Wakabayashi
Discrete Mathematics 308 (2008) 1455–1471 www.elsevier.com/locate/disc Packing triangles in low degree graphs and indifference graphsଁ Gordana Mani´c∗, Yoshiko Wakabayashi Departamento de Ciência da Computação, Universidade de São Paulo, Rua do Matão, 1010—CEP 05508-090–São Paulo, Brazil Received 5 November 2005; received in revised form 28 August 2006; accepted 11 July 2007 Available online 6 September 2007 Abstract We consider the problems of finding the maximum number of vertex-disjoint triangles (VTP) and edge-disjoint triangles (ETP) in a simple graph. Both problems are NP-hard. The algorithm with the best approximation ratio known so far for these problems has ratio 3/2 + ε, a result that follows from a more general algorithm for set packing obtained by Hurkens and Schrijver [On the size of systems of sets every t of which have an SDR, with an application to the worst-case ratio of heuristics for packing problems, SIAM J. Discrete Math. 2(1) (1989) 68–72]. We present improvements on the approximation ratio for restricted cases of VTP and ETP that are known to be APX-hard: we give an approximation algorithm for VTP on graphs with maximum degree 4 with ratio slightly less than 1.2, and for ETP on graphs with maximum degree 5 with ratio 4/3. We also present an exact linear-time algorithm for VTP on the class of indifference graphs. © 2007 Elsevier B.V. All rights reserved. Keywords: Packing triangles; Approximation algorithm; Polynomial algorithm; Low degree graph; Indifference graph 1. Introduction For a given family F of sets, a collection of pairwise disjoint sets of F is called a packing of F.