Introducing Ex
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Text Editing in UNIX: an Introduction to Vi and Editing
Text Editing in UNIX A short introduction to vi, pico, and gedit Copyright 20062009 Stewart Weiss About UNIX editors There are two types of text editors in UNIX: those that run in terminal windows, called text mode editors, and those that are graphical, with menus and mouse pointers. The latter require a windowing system, usually X Windows, to run. If you are remotely logged into UNIX, say through SSH, then you should use a text mode editor. It is possible to use a graphical editor, but it will be much slower to use. I will explain more about that later. 2 CSci 132 Practical UNIX with Perl Text mode editors The three text mode editors of choice in UNIX are vi, emacs, and pico (really nano, to be explained later.) vi is the original editor; it is very fast, easy to use, and available on virtually every UNIX system. The vi commands are the same as those of the sed filter as well as several other common UNIX tools. emacs is a very powerful editor, but it takes more effort to learn how to use it. pico is the easiest editor to learn, and the least powerful. pico was part of the Pine email client; nano is a clone of pico. 3 CSci 132 Practical UNIX with Perl What these slides contain These slides concentrate on vi because it is very fast and always available. Although the set of commands is very cryptic, by learning a small subset of the commands, you can edit text very quickly. What follows is an outline of the basic concepts that define vi. -

User Manual for Ox: an Attribute-Grammar Compiling System Based on Yacc, Lex, and C Kurt M
Computer Science Technical Reports Computer Science 12-1992 User Manual for Ox: An Attribute-Grammar Compiling System based on Yacc, Lex, and C Kurt M. Bischoff Iowa State University Follow this and additional works at: http://lib.dr.iastate.edu/cs_techreports Part of the Programming Languages and Compilers Commons Recommended Citation Bischoff, Kurt M., "User Manual for Ox: An Attribute-Grammar Compiling System based on Yacc, Lex, and C" (1992). Computer Science Technical Reports. 21. http://lib.dr.iastate.edu/cs_techreports/21 This Article is brought to you for free and open access by the Computer Science at Iowa State University Digital Repository. It has been accepted for inclusion in Computer Science Technical Reports by an authorized administrator of Iowa State University Digital Repository. For more information, please contact [email protected]. User Manual for Ox: An Attribute-Grammar Compiling System based on Yacc, Lex, and C Abstract Ox generalizes the function of Yacc in the way that attribute grammars generalize context-free grammars. Ordinary Yacc and Lex specifications may be augmented with definitions of synthesized and inherited attributes written in C syntax. From these specifications, Ox generates a program that builds and decorates attributed parse trees. Ox accepts a most general class of attribute grammars. The user may specify postdecoration traversals for easy ordering of side effects such as code generation. Ox handles the tedious and error-prone details of writing code for parse-tree management, so its use eases problems of security and maintainability associated with that aspect of translator development. The translators generated by Ox use internal memory management that is often much faster than the common technique of calling malloc once for each parse-tree node. -
A Brief Introduction to Unix-2019-AMS
A Brief Introduction to Linux/Unix – AMS 2019 Pete Pokrandt UW-Madison AOS Systems Administrator [email protected] Twitter @PTH1 Brief Intro to Linux/Unix o Brief History of Unix o Basics of a Unix session o The Unix File System o Working with Files and Directories o Your Environment o Common Commands Brief Intro to Unix (contd) o Compilers, Email, Text processing o Image Processing o The vi editor History of Unix o Created in 1969 by Kenneth Thompson and Dennis Ritchie at AT&T o Revised in-house until first public release 1977 o 1977 – UC-Berkeley – Berkeley Software Distribution (BSD) o 1983 – Sun Workstations produced a Unix Workstation o AT&T unix -> System V History of Unix o Today – two main variants, but blended o System V (Sun Solaris, SGI, Dec OSF1, AIX, linux) o BSD (Old SunOS, linux, Mac OSX/MacOS) History of Unix o It’s been around for a long time o It was written by computer programmers for computer programmers o Case sensitive, mostly lowercase abbreviations Basics of a Unix Login Session o The Shell – the command line interface, where you enter commands, etc n Some common shells Bourne Shell (sh) C Shell (csh) TC Shell (tcsh) Korn Shell (ksh) Bourne Again Shell (bash) [OSX terminal] Basics of a Unix Login Session o Features provided by the shell n Create an environment that meets your needs n Write shell scripts (batch files) n Define command aliases n Manipulate command history n Automatically complete the command line (tab) n Edit the command line (arrow keys in tcsh) Basics of a Unix Login Session o Logging in to a unix -

UNIX (Solaris/Linux) Quick Reference Card Logging in Directory Commands at the Login: Prompt, Enter Your Username
UNIX (Solaris/Linux) QUICK REFERENCE CARD Logging In Directory Commands At the Login: prompt, enter your username. At the Password: prompt, enter ls Lists files in current directory your system password. Linux is case-sensitive, so enter upper and lower case ls -l Long listing of files letters as required for your username, password and commands. ls -a List all files, including hidden files ls -lat Long listing of all files sorted by last Exiting or Logging Out modification time. ls wcp List all files matching the wildcard Enter logout and press <Enter> or type <Ctrl>-D. pattern Changing your Password ls dn List files in the directory dn tree List files in tree format Type passwd at the command prompt. Type in your old password, then your new cd dn Change current directory to dn password, then re-enter your new password for verification. If the new password cd pub Changes to subdirectory “pub” is verified, your password will be changed. Many systems age passwords; this cd .. Changes to next higher level directory forces users to change their passwords at predetermined intervals. (previous directory) cd / Changes to the root directory Changing your MS Network Password cd Changes to the users home directory cd /usr/xx Changes to the subdirectory “xx” in the Some servers maintain a second password exclusively for use with Microsoft windows directory “usr” networking, allowing you to mount your home directory as a Network Drive. mkdir dn Makes a new directory named dn Type smbpasswd at the command prompt. Type in your old SMB passwword, rmdir dn Removes the directory dn (the then your new password, then re-enter your new password for verification. -

Lex and Yacc
Lex and Yacc A Quick Tour HW8–Use Lex/Yacc to Turn this: Into this: <P> Here's a list: Here's a list: * This is item one of a list <UL> * This is item two. Lists should be <LI> This is item one of a list indented four spaces, with each item <LI>This is item two. Lists should be marked by a "*" two spaces left of indented four spaces, with each item four-space margin. Lists may contain marked by a "*" two spaces left of four- nested lists, like this: space margin. Lists may contain * Hi, I'm item one of an inner list. nested lists, like this:<UL><LI> Hi, I'm * Me two. item one of an inner list. <LI>Me two. * Item 3, inner. <LI> Item 3, inner. </UL><LI> Item 3, * Item 3, outer list. outer list.</UL> This is outside both lists; should be back This is outside both lists; should be to no indent. back to no indent. <P><P> Final suggestions: Final suggestions 2 if myVar == 6.02e23**2 then f( .. ! char stream LEX token stream if myVar == 6.02e23**2 then f( ! tokenstream YACC parse tree if-stmt == fun call var ** Arg 1 Arg 2 float-lit int-lit . ! 3 Lex / Yacc History Origin – early 1970’s at Bell Labs Many versions & many similar tools Lex, flex, jflex, posix, … Yacc, bison, byacc, CUP, posix, … Targets C, C++, C#, Python, Ruby, ML, … We’ll use jflex & byacc/j, targeting java (but for simplicity, I usually just say lex/yacc) 4 Uses “Front end” of many real compilers E.g., gcc “Little languages”: Many special purpose utilities evolve some clumsy, ad hoc, syntax Often easier, simpler, cleaner and more flexible to use lex/yacc or similar tools from the start 5 Lex: A Lexical Analyzer Generator Input: Regular exprs defining "tokens" my.flex Fragments of declarations & code Output: jflex A java program “yylex.java” Use: yylex.java Compile & link with your main() Calls to yylex() read chars & return successive tokens. -

Differentiating Logarithm and Exponential Functions
Differentiating logarithm and exponential functions mc-TY-logexp-2009-1 This unit gives details of how logarithmic functions and exponential functions are differentiated from first principles. In order to master the techniques explained here it is vital that you undertake plenty of practice exercises so that they become second nature. After reading this text, and/or viewing the video tutorial on this topic, you should be able to: • differentiate ln x from first principles • differentiate ex Contents 1. Introduction 2 2. Differentiation of a function f(x) 2 3. Differentiation of f(x)=ln x 3 4. Differentiation of f(x) = ex 4 www.mathcentre.ac.uk 1 c mathcentre 2009 1. Introduction In this unit we explain how to differentiate the functions ln x and ex from first principles. To understand what follows we need to use the result that the exponential constant e is defined 1 1 as the limit as t tends to zero of (1 + t) /t i.e. lim (1 + t) /t. t→0 1 To get a feel for why this is so, we have evaluated the expression (1 + t) /t for a number of decreasing values of t as shown in Table 1. Note that as t gets closer to zero, the value of the expression gets closer to the value of the exponential constant e≈ 2.718.... You should verify some of the values in the Table, and explore what happens as t reduces further. 1 t (1 + t) /t 1 (1+1)1/1 = 2 0.1 (1+0.1)1/0.1 = 2.594 0.01 (1+0.01)1/0.01 = 2.705 0.001 (1.001)1/0.001 = 2.717 0.0001 (1.0001)1/0.0001 = 2.718 We will also make frequent use of the laws of indices and the laws of logarithms, which should be revised if necessary. -

Unix Commands (09/04/2014)
Unix Commands (09/04/2014) • Access control – login <login_name> – exit – passwd <login_name> – yppassswd <loginname> – su – • Login as Super user – su <login> • Login as user <login> • Root Prompt – [root@localhost ~] # • User Prompt – [bms@raxama ~] $ On Line Documentation – man <command/topic> – info <command/topic> • Working with directories – mkdir –p <subdir> ... {-p create all directories in path if not present} mkdir –p /2015/Jan/21/14 will create /2015, Jan, 21 & 14 in case any of these is absent – cd <dir> – rm -r <subdir> ... Man Pages • 1 Executable programs or shell commands • 2 System calls (functions provided by the kernel) • 3 Library calls (functions within program libraries) • 4 Special files (usually found in /dev) • 5 File formats and conventions eg /etc/passwd • 6 Games • 7 Miscellaneous (including macro packages and conventions), e.g. man(7), groff(7) • 8 System administration commands (usually only for root) • 9 Kernel routines [Non standard] – man grep, {awk,sed,find,cut,sort} – man –k mysql, man –k dhcp – man crontab ,man 5 crontab – man printf, man 3 printf – man read, man 2 read – man info Runlevels used by Fedora/RHS Refer /etc/inittab • 0 - halt (Do NOT set initdefault to this) • 1 - Single user mode • 2 - Multiuser, – without NFS (The same as 3, if you do not have networking) • 3 - Full multi user mode w/o X • 4 - unused • 5 - X11 • 6 - reboot (Do NOT set init default to this) – init 6 {Reboot System} – init 0 {Halt the System} – reboot {Requires Super User} – <ctrl> <alt> <del> • in tty[2-7] mode – tty switching • <ctrl> <alt> <F1-7> • In Fedora 10 tty1 is X. -

Processes in Linux/Unix
Processes in Linux/Unix A program/command when executed, a special instance is provided by the system to the process. This instance consists of all the services/resources that may be utilized by the process under execution. • Whenever a command is issued in unix/linux, it creates/starts a new process. For example, pwd when issued which is used to list the current directory location the user is in, a process starts. • Through a 5 digit ID number unix/linux keeps account of the processes, this number is call process id or pid. Each process in the system has a unique pid. • Used up pid’s can be used in again for a newer process since all the possible combinations are used. • At any point of time, no two processes with the same pid exist in the system because it is the pid that Unix uses to track each process. Initializing a process A process can be run in two ways: 1. Foreground Process : Every process when started runs in foreground by default, receives input from the keyboard and sends output to the screen. When issuing pwd command $ ls pwd Output: $ /home/geeksforgeeks/root When a command/process is running in the foreground and is taking a lot of time, no other processes can be run or started because the prompt would not be available until the program finishes processing and comes out. 2. Backround Process : It runs in the background without keyboard input and waits till keyboard input is required. Thus, other processes can be done in parallel with the process running in background since they do not have to wait for the previous process to be completed. -

Action Language BC: Preliminary Report
Proceedings of the Twenty-Third International Joint Conference on Artificial Intelligence Action Language BC: Preliminary Report Joohyung Lee1, Vladimir Lifschitz2 and Fangkai Yang2 1School of Computing, Informatics and Decision Systems Engineering, Arizona State University [email protected] 2 Department of Computer Science, Univeristy of Texas at Austin fvl,[email protected] Abstract solves the frame problem by incorporating the commonsense law of inertia in its semantics, which makes it difficult to talk The action description languages B and C have sig- about fluents whose behavior is described by defaults other nificant common core. Nevertheless, some expres- than inertia. The position of a moving pendulum, for in- sive possibilities of B are difficult or impossible to stance, is a non-inertial fluent: it changes by itself, and an simulate in C, and the other way around. The main action is required to prevent the pendulum from moving. The advantage of B is that it allows the user to give amount of liquid in a leaking container changes by itself, and Prolog-style recursive definitions, which is impor- an action is required to prevent it from decreasing. A spring- tant in applications. On the other hand, B solves loaded door closes by itself, and an action is required to keep the frame problem by incorporating the common- it open. Work on the action language C and its extension C+ sense law of inertia in its semantics, which makes was partly motivated by examples of this kind. In these lan- it difficult to talk about fluents whose behavior is guages, the inertia assumption is expressed by axioms that the described by defaults other than inertia. -
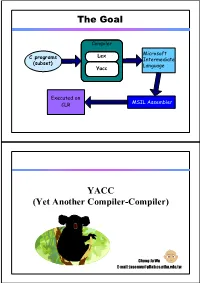
The Goal YACC
The Goal Compiler Lex Microsoft C programs Intermediate (subset) Language Yacc Executed on MSIL Assembler CLR YACC (Yet Another Compiler-Compiler) Chung-Ju Wu E-mail: [email protected] Why use Lex & Yacc ? • Writing a compiler is difficult requiring lots of time and effort. • Construction of the scanner and parser is routine enough that the process may be automated. Lexical Rules Scanner --------- Compiler Parser Grammar Compiler --------- Code Semantics generator Introduction • What is YACC ? – Tool which will produce a parser for a given grammar. – YACC (Yet Another Compiler Compiler) is a program designed to compile a LALR(1) grammar and to produce the source code of the syntactic analyzer of the language produced by this grammar. History • Original written by Stephen C. Johnson, 1975. •Variants: – lex, yacc (AT&T) – bison: a yacc replacement (GNU) – flex: fast lexical analyzer (GNU) – BSD yacc – PCLEX, PCYACC (Abraxas Software) How YACC Works File containing desired gram.y grammar in yacc format yacc yacc program y.tab.c C source program created by yacc cc C compiler or gcc Executable program that will parse a.out grammar given in gram.y How YACC Works y.tab.h YACC source (*.y) yacc y.tab.c y.output (1) Parser generation time y.tab.c C compiler/linker a.out (2) Compile time Abstract Token stream a.out Syntax Tree (3) Run time An YACC File Example %{ #include <stdio.h> %} %token NAME NUMBER %% statement: NAME '=' expression | expression { printf("= %d\n", $1); } ; expression: expression '+' NUMBER { $$ = $1 + $3; } | expression '-' NUMBER { $$ = $1 - $3; } | NUMBER { $$ = $1; } ; %% int yyerror(char *s) { fprintf(stderr, "%s\n", s); return 0; } int main(void) { yyparse(); return 0; } Works with Lex How to work ? Works with Lex call yylex() [0-9]+ next token is NUM NUM ‘+’ NUM YACC File Format %{ C declarations %} yacc declarations %% Grammar rules %% Additional C code – Comments enclosed in /* .. -

How Do You Use the Vi Text Editor?
How do you use the vi text editor? 1.What is the Visual Text Editor (vi)?...................................................................2 2.Configuring your vi session..............................................................................2 2.1.Some of the options available in vi are:................................................3 2.2.Sample of the .exrc file........................................................................3 3.vi Quick Reference Guide.................................................................................4 3.1.Cursor Movement Commands.............................................................4 3.2.Inserting and Deleting Text.................................................................5 3.3.Change Commands.............................................................................6 3.4.File Manipulation...............................................................................7 Institute of Microelectronics, Singapore FAQ for vi text editor E1 1. What is the Visual Text Editor (vi)? The Visual Test Editor, more commonly known as the vi text editor, is a standard “visual” (full screen) editor available for test editing in UNIX. It is a combination of the capabilities of the UNIX ed and ex text editors. It has specific modes for text insertion and deletion as well as command entering. Type view on the command line of the UNIX shell terminal to enter the read- only mode of vi. To switch between the line editor, ex, mode and the full screen wrapmargin vi mode: • To enter the ex mode from the vi mode, type Q • To enter the vi mode from the ex mode, type vi When vi is entered on the command line, you enter vi’s command (entering) mode. Positioning and editing commands can be entered to perform functions in this mode whilst advanced editing commands can be entered following a colon (:) that places you at the bottom of the file. To enter text insertion mode, a vi text insertion command i, o, or a is typed so that text will no longer be interpreted as positioning or editing commands in this mode. -

Functionality and Expression in Computer Programs: Refining the Tests for Software Copyright Infringement
SAMUELSON_F&E ARTICLE (DO NOT DELETE) 1/31/2017 12:08 PM FUNCTIONALITY AND EXPRESSION IN COMPUTER PROGRAMS: REFINING THE TESTS FOR SOFTWARE COPYRIGHT INFRINGEMENT Pamela Samuelson* Abstract Courts have struggled for decades to develop a test for judging infringement claims in software copyright cases that distinguishes between program expression that copyright law protects and program functionality for which copyright protection is unavailable. The case law thus far has adopted four main approaches to judging copyright infringement claims in software cases. One, now mostly discredited, test would treat all structure, sequence, and organization (SSO) of programs as protectable expression unless there is only one way to perform a program function. A second, now widely applied, three-step test calls for creation of a hierarchy of abstractions for an allegedly infringed program, filtration of unprotectable elements, and comparison of the protectable expression of the allegedly infringed program with the expression in the second program that is the basis of the infringement claim. A third approach has focused on whether the allegedly infringing elements are program processes or methods of operation that lie outside the scope of protection available from copyright law. A fourth approach has concentrated on whether the allegedly infringing elements of a program are instances in which ideas or functions have merged with program expression. This Article offers both praise and criticism of the approaches taken thus far to judging software copyright infringement, and it proposes an alternative unified test for infringement that is consistent with traditional principles of copyright law and that will promote healthy competition and ongoing innovation in the software industry.