Webroot Secureanywhere User Guide Complete Edition
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -

Q3 Consumer Endpoint Protection Jul-Sep 2020
HOME ANTI- MALWARE PROTECTION JUL - SEP 2020 selabs.uk [email protected] @SELabsUK www.facebook.com/selabsuk blog.selabs.uk SE Labs tested a variety of anti-malware (aka ‘anti-virus’; aka ‘endpoint security’) products from a range of well-known vendors in an effort to judge which were the most effective. Each product was exposed to the same threats, which were a mixture of targeted attacks using well-established techniques and public email and web-based threats that were found to be live on the internet at the time of the test. The results indicate how effectively the products were at detecting and/or protecting against those threats in real time. 2 Home Anti-Malware Protection July - September 2020 MANAGEMENT Chief Executive Officer Simon Edwards CONTENTS Chief Operations Officer Marc Briggs Chief Human Resources Officer Magdalena Jurenko Chief Technical Officer Stefan Dumitrascu Introduction 04 TEstING TEAM Executive Summary 05 Nikki Albesa Zaynab Bawa 1. Total Accuracy Ratings 06 Thomas Bean Solandra Brewster Home Anti-Malware Protection Awards 07 Liam Fisher Gia Gorbold Joseph Pike 2. Threat Responses 08 Dave Togneri Jake Warren 3. Protection Ratings 10 Stephen Withey 4. Protection Scores 12 IT SUPPORT Danny King-Smith 5. Protection Details 13 Chris Short 6. Legitimate Software Ratings 14 PUBLICatION Sara Claridge 6.1 Interaction Ratings 15 Colin Mackleworth 6.2 Prevalence Ratings 16 Website selabs.uk Twitter @SELabsUK 6.3 Accuracy Ratings 16 Email [email protected] Facebook www.facebook.com/selabsuk 6.4 Distribution of Impact Categories 17 Blog blog.selabs.uk Phone +44 (0)203 875 5000 7. -

Endpoint Integrity Check\221\316\211\236\210\352\227\227.Xlsx
エンドポイントインテグリティチェック - アンチウイルス対応メーカ一覧 360safe.com AEC, spol. s r.o. ALWIL Software AT & T AVG Technologies Agnitum Ltd AhnLab, Inc. Aliant America Online, Inc. Antiy Labs Authentium, Inc. Avanquest Publishing USA, Inc. Avira GmbH Beijing Rising Technology Corp. Ltd. Bell Bell Aliant BellSouth Bitdefender BullGuard Ltd. CJSC Returnil Software CMC Information Security Cat Computer Services Pvt. Ltd. Central Command , Inc. Check Point, Inc Cisco Systems, Inc. ClamAV ClamWin Comodo Group Computer Associates International, Inc Coranti, Inc Crawler LLC Cyber Defender Corp. Defender Pro LLC ESTsoft Corp. EathLink, Inc Emsi Software GmbH Eset Software F-Secure Corp. FairPoint Faronics Corporation Fortinet, Inc Frisk Software International GData Software AG GFI Software Grisoft, Inc. H+BEDV Datentechnik GmbH HAURI, Inc IKARUS Software GmbH Internet Security Systems, Inc. Jiangmin, Inc K7 Computing Pvt. Ltd. kaspersky Labs Kingsoft Corp. LANDesk Software, Ltd. Lavasoft, Inc. Lumension Security McAfee, Inc. MicroWorld Microsoft Corp. N-able Technologies Inc Nano Security New Technology Wave Inc. Norman ASA ONO Omniquad PC Tools Software PCSecurityShield Panda Software Parallels, Inc. Preventon Technologies Ltd. Prevx Ltd. Quick Heal Technologies (P) Ltd. Radialpoint Inc. Rogers SOFTWIN SalD Ltd. Security Coverage Inc. Sereniti, Inc. Shavlik Technologies Sophos, Plc Sunbelt Software Symantec Corp. TELUS Thirtyseven4, LLC. Tobit.Software Trend Micro, Inc. Troppus Software Corporation TrustPort, a.s. VCOM VMware, Inc. Verizon Videotron Virgin Broadband Virgin Media Virus BlokAda Ltd. Virus Buster Ltd. Webroot Software, Inc Yahoo!, Inc Zone Labs LLC e frontier, Inc. eEye Digital Security iolo technologies, LLC. -
PC Pitstop Supershield 2.0
Anti -Virus Comparative PC Matic PC Pitstop SuperShield 2.0 Language: English February 2017 Last Revision: 30 th March 2017 www.av-comparatives.org Commissioned by PC Matic - 1 - PC Pitstop – February 2017 www.av-comparatives.org Introduction This report has been commissioned by PC Matic. We found PC Matic PC Pitstop very easy to install. The wizard allows the user to change the location of the installation folder and the placing of shortcuts, but the average user only needs to click Next a few times. The program can be started as soon the setup wizard completes. A Different Approach PC Matic approaches security differently than traditional security products. PC Matic relies mainly on a white list to defeat malware; this can lead to a higher number of false alarms if users have files which are not yet on PC Matic’s whitelist. Unknown files are uploaded to PC Matic servers, where they get compared against a black- and white list (signed and unsigned). By default, PC Matic SuperShield only blocks threats and unknown files on-execution, but does not remove/quarantine them. Additional features In addition to malware protection, PC Matic also provides system maintenance and optimization features. These include checking for driver updates, outdated programs with vulnerabilities, erroneous registry entries and disk fragmentation. A single scan can be run which checks not only for malware, but also for any available system optimization opportunities. Commissioned by PC Matic - 2 - PC Pitstop – February 2017 www.av-comparatives.org Tested products The tested products have been chosen by PC Matic. We used the latest available product versions and updates available at time of testing (February 2017). -

Webroot Secureanywhere® Business Endpoint Protection the Security Industry Had a BIG IDEA About How to Address Today’S Increasing Threats
Webroot SecureAnywhere® Business Endpoint Protection The security industry had a BIG IDEA about how to address today’s increasing threats. Push down gargantuan loads of signatures to ever fatter software clients. Face it, your current endpoint security software is slow, heavy, and you wonder if it causes more problems than it solves. Meanwhile you have to keep up with a number of new challenges – from a more mobile workforce to more dangerous malware. Has this broken model pushed you to the breaking point? Do long scan times, massive downloads, and slow performance make your users less productive ? Do constant updates, patches, and reimaging requests distract you and your staff from addressing true business needs ? Does mammoth security software consume too many resources on your users’ computers – and does managing it require a dedicated server ? Are you concerned that you don’t have enough control when endpoint devices leave the office ? “Over 450,000 new “67% of attacks carried “No organization is immune malicious software programs out are for criminal to the problem of security are registered each day.” purposes.” risks, regardless of size.“ AV-Test, The Independent IT – Security Institute Hackmageddon.com Canalys Research Fixing security requires a new, Smarter approach. It’s called forget the old approach. Seeing traditional security software become too big and too much “Downloaded, copied to target, set up, installed, of a burden on endpoint devices, networks, and IT staff, Webroot “running, baselined, and fully scanned in 5 minutes? I’d decided to start fresh. We built a new kind of security software that love to see anyone else come close.” Sean Kethcart, IT Systems Support Analyst, Haymarket Center completely does away with old-school approaches like signature downloads, the need for constant updates, and big-footprint client “This is by far the fastest, easiest malware solution I software. -
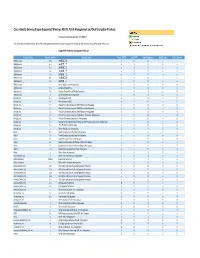
Cisco Identity Services Engine Supported Windows AV/AS/PM/DE
Cisco Identity Services Engine Supported Windows AS/AV, Patch Management and Disk Encryption Products Compliance Module Version 3.6.10363.2 This document provides Windows AS/AV, Patch Management and Disk Encryption support information on the the Cisco AnyConnect Agent Version 4.2. Supported Windows Antispyware Products Vendor_Name Product_Version Product_Name Check_FSRTP Set_FSRTP VirDef_Signature VirDef_Time VirDef_Version 360Safe.com 10.x 360安全卫士 vX X v v 360Safe.com 4.x 360安全卫士 vX X v v 360Safe.com 5.x 360安全卫士 vX X v v 360Safe.com 6.x 360安全卫士 vX X v v 360Safe.com 7.x 360安全卫士 vX X v v 360Safe.com 8.x 360安全卫士 vX X v v 360Safe.com 9.x 360安全卫士 vX X v v 360Safe.com x Other 360Safe.com Antispyware Z X X Z X Agnitum Ltd. 7.x Outpost Firewall Pro vX X X O Agnitum Ltd. 6.x Outpost Firewall Pro 2008 [AntiSpyware] v X X v O Agnitum Ltd. x Other Agnitum Ltd. Antispyware Z X X Z X AhnLab, Inc. 2.x AhnLab SpyZero 2.0 vv O v O AhnLab, Inc. 3.x AhnLab SpyZero 2007 X X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2007 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2008 Platinum AntiSpyware v X O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 2009 Platinum AntiSpyware v v O v O AhnLab, Inc. 7.x AhnLab V3 Internet Security 7.0 Platinum Enterprise AntiSpyware v X O v O AhnLab, Inc. 8.x AhnLab V3 Internet Security 8.0 AntiSpyware v v O v O AhnLab, Inc. -

Q1 Home Anti-Malware Protection Jan-Mar 2020
HOME ANTI- MALWARE PROTECTION JAN - MAR 2020 www.SELabs.uk [email protected] @SELabsUK www.facebook.com/selabsuk blog.selabs.uk SE Labs tested a variety of anti-malware (aka ‘anti-virus’; aka ‘endpoint security’) products from a range of well-known vendors in an effort to judge which were the most effective. Each product was exposed to the same threats, which were a mixture of targeted attacks using well-established techniques and public email and web-based threats that were found to be live on the internet at the time of the test. The results indicate how effectively the products were at detecting and/or protecting against those threats in real time. 2 Home Anti-Malware Protection January - March 2020 MANAGEMENT Chief Executive Officer Simon Edwards CONTENTS Chief Operations Officer Marc Briggs Chief Human Resources Officer Magdalena Jurenko Chief Technical Officer Stefan Dumitrascu Introduction 04 TESTING TEAM Executive Summary 05 Thomas Bean Solandra Brewster 1. Total Accuracy Ratings 06 Dimitar Dobrev Liam Fisher Home Anti-Malware Protection Awards 07 Gia Gorbold Dave Togneri 2. Threat Responses 08 Jake Warren Stephen Withey 3. Protection Ratings 10 IT SUPPORT 4. Protection Scores 12 Danny King-Smith Chris Short 5. Protection Details 13 PUBLICATION 6. Legitimate Software Ratings 14 Steve Haines Colin Mackleworth 6.1 Interaction Ratings 15 Website www.SELabs.uk 6.2 Prevalence Ratings 16 Twitter @SELabsUK Email [email protected] 6.3 Accuracy Ratings 16 Facebook www.facebook.com/selabsuk Blog blog.selabs.uk 6.4 Distribution of Impact Categories 17 Phone 0203 875 5000 Post SE Labs Ltd, 7. -
ESAP 2.8.4 Release Notes
ESAP 2.8.4 Release Notes Version Mac and Windows 3.6.10120.2 (V2 Unified + V3). Published July 2015 Note: The SDK embedded in this ESAP version has been tested and qualified to interoperate with a limited list of end endpoint security applications covering most of the widely used products listed in the supported products list, all new products added to the supported list and all products for which a bug fix was added in this release. Noteworthy changes: • This ESAP version contains additional files in preparation of new features that will be enabled in the next major release of SA and IC. ESAP 2.8.4 and Pulse Secure Access/Access Control Service Compatibility Chart: This ESAP package can be installed on the following Pulse Secure Access/Access Control Service software versions. • SA 8.0Rx • SA 7.4Rx • SA 7.3Rx • SA 7.2Rx • SA 7.1Rx • SA 7.0Rx • SA 6.5Rx • UAC 5.0Rx • UAC 4.4Rx • UAC 4.3Rx • UAC 4.2Rx • UAC 4.1Rx • UAC 4.0Rx • UAC 3.1Rx © 2015 by Pulse Secure, LLC. All rights reserved 2 Note: The ESAP package may install and function without any errors on older releases however as the install has not been tested, we recommend that it be used only on the above versions of software releases. Support has been added for the following products in ESAP2.8.4 Windows OS Antivirus Products [Bitdefender] Endpoint Client by Bitdefender (5.x) [Symantec Corp.] Norton Internet Security (22.x) [Webroot Software, Inc.] Webroot AntiVirus (9.x) Antispyware Products [Bitdefender] Endpoint Client by Bitdefender (5.x) [Symantec Corp.] Norton Internet Security (22.x) [Webroot Software, Inc.] Webroot AntiVirus (9.x) Firewall Products [Bitdefender] Endpoint Client by Bitdefender Firewall (5.x) [Microsoft Corp.] Microsoft Windows Firewall (10.x) [Symantec Corp.] Norton Internet Security (22.x) MAC OS Antivirus Products [Doctor Web] Dr.Web for Mac (10.x) [F-Secure Corp.] F-Secure Anti-Virus for Mac (1.x) [Kaspersky Labs] Kaspersky Anti-Virus (15.x) Antispyware Products [Doctor Web] Dr.Web for Mac (10.x) © 2015 by Pulse Secure, LLC. -

Partner Edge
PROGRAM BRIEF Partner Edge MSP Program The Webroot Partner Edge Program helps our MSP, Reseller, Distributor and Security vendor partners to grow their businesses with predictable and recurring revenue income from our cloud-based cybersecurity and threat intelligence solutions. Webroot provides the industry-specific tools; security and threat intelligence services; training; integrations; certifications and platforms partners need to ensure the reliability and trust so essential to your customers. Webroot’s goal is to empower all of our We are always business partners to become their most successful. looking for Why partner with Webroot? industry leading • Predictable, recurring revenue grows your business • Sales and marketing tools enable greater profitability technologies • Superior cybersecurity solutions that reduce your costs to bring to our • Technical and sales certifications to support your Service clients. Webroot’s MSPs who partner with Webroot enjoy: technology has • Single endpoint solution for antivirus/antimalware greatly reduced • Powerful integrated Endpoint and DNS protection, plus automated security awareness training to empower end users virus disruptions • Lower operational costs on our clients’ • Superior productivity, uptime, and customer satisfaction • Single-pane-of-glass online management console designed for multi-sites and systems. customers to reduce administrative effort • Zero on-site hardware infrastructure to maintain Erik Nachbahr • Rollback remediation and no reimaging President and Founder • RMM integrations -

Fileless Malware Protection Test
FILELESS MALWARE PROTECTION TEST OCTOBER 2017 Fileless Malware Protection Test. October 2017. 1 / 12 INTRODUCTION In times of digitalization of each aspect of public and private life new and interesting techniques of bypassing protections are abundant. Although for a few years the main threat among the malicious software has still been the techniques based on asymmetric cryptography, we cannot complain about the lack of methods of deceiving the protection products whose level of preparation and complicated escalation cycle exceed the viruses from the ransomware family. The threats examined in this report are so-called fileless malware. Although the infection vector usually starts traditionally, i.e. from the delivery of a malicious file to the victim’s computer – via scam or a drive-by download attack as a result of using an exploit – this is where the similarities to traditional attacks with files end. The fileless malicious software operates directly in the computer’s internal memory. In this scenario, the activated virus will not be transferred to quarantine by the protecting software as it is not a file, but a set of instructions to be executed, operating on system processes. The authors of malicious code, who often are experts in their field, can use this in order not to leave any traces on the hard drive and to make detection by the antivirus software difficult. The fileless threats have a few features in common with rootkits: they can store data in the register which is the base for the settings of internal memory and some applications, and even intercept and modify some low-level API functions. -

Faqs for Webroot Secureanywhere Identity Shield
FAQs for Webroot SecureAnywhere Identity Shield Table of Contents General Questions .....................................................................................................................................................2 Why is the bank offering Webroot SecureAnywhere Identity Shield? ............................................................................................. 2 What does it protect? ....................................................................................................................................................................... 2 Who is Webroot? .............................................................................................................................................................................. 2 Is the Webroot software different from the bank than I can get directly from Webroot? .............................................................. 2 Can I upgrade Webroot software? .................................................................................................................................................... 2 What is the difference between my antivirus and Webroot SecureAnywhere Identity Shield? ...................................................... 2 What happens if my Webroot SecureAnywhere Identity Shield detects a threat? .......................................................................... 3 Installing Webroot SecureAnywhere Identity Shield ....................................................................................................4 -
Security Survey 2021
Independent Tests of Anti-Virus Software IT Security Survey 2021 LANGUAGE : ENGLISH LAST REVISION : 8TH FEBRUARY 2021 WWW.AV-COMPARATIVES.ORG IT Security Survey 2021 www.av-comparatives.org Security Survey 2021 We have conducted our annual survey, which helps us to improve our service to the end-user community. Respondents were asked for their opinions on various topics related to anti-virus software testing and anti-virus software in general. We would like to thank everyone who took the time to complete the survey. Key data Survey Period: 11 th December 2020 – 30 th December 2020 Valid responses of real users: 2,111 The survey ran for about two weeks. It contained various control questions and checks, which helped us to identify and remove invalid responses. Whilst there was a raffle conducted this year, with a gift box as a prize, this only became clear once a participant had completed the survey. This was done to avoid people submitting meaningless answers simply to try to win a prize. The survey results are invaluable to us. This report contains the results of the survey questions. Overview In 2020, restrictions on personal movement to counteract the spread of COVID-19 led to unprecedented use of the Internet. Millions of people worked from home rather than in an office, and millions more arranged virtual social meetings using platforms like Skype and Zoom. Whilst tablets and smartphones remained as popular as before, ZDNet 1 reported a 28.3% rise in laptop sales relative to the previous year. This makes security software for desktop operating systems more important than ever, as cybercriminals attempt to exploit the new situation.