Q1 Home Anti-Malware Protection Jan-Mar 2020
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Ids/Ips
--,.---------------------------------- EO THONG TIN vA TRUYEN THONG CONG HOA xA HOI CHiT NGHIA VII::T NAM DQc qp -T\I' Do - Hl}.nh Phuc S6:'u5J1BTTTT-VNCERT Ha NQi, ngay • V/v Huang dful dam bao an toan thong : /\p C8AJj S:'~~G'lGrf~P CAOSJ Vi~TNAM tin cho cac C6ng/Trang thOng tin di~n t\r 'IAN PliCl,G Dill J,tN"A NO: ~. s6: .2.-.4.6 . T';ProAN CON~ ~PCSYN DEN Ngay:.OLLi.o.1.-1. .' eJ!. Aj0.,t N "'-I. "/I'<'~~""..•••••••••.•Cac Bi), COquan ngang Bi), COquan trvc thui)c C phu. nr~(c)N) iJE N~y:!l1..W~.ILUBND cac tinh, thanh ph5 trvc thui)c Trung uang, Chuy~n:....I(<r... ~~..r••••••••• .............. Th\Ic hi~n chi d:;to cua Thu tuOng Chinh pM v~ vi~c dam bao an toan 17~ong tin cho cac c6ng thong tin di~n tu, dang thai ~S th5ng nh~t v~ ni)i dung va ~ phuang phap quan Iy an t01m thong tin theo yeu cau cua Nghi diM cua Chinh phu s5 4312011/ND-CP ngay 13/612011, Bi) Thong tin va Truy~n thOng hUOng d~n cac co quan nha nuac triSn khai ap d\lng tM li~u "HuOng d~ mi)t s5 bi~n phap ky thu~t co ban dam bao an t01mcho c6ng/trang thong tin di~n ill". Hi li~u nay bao gam mi)t s5 bi~n phap ky thu~t thiSt ySu nh~t nh~m dam bao xay d\Iilg va v~ hanh an toan cac c6ng/trang thOng tin di~n ill va dugc trinh bay trong van ban gui kern theo cong van nay. -

Cost of a Cyber Incident)
CO ST OF A CYBER INCIDENT: S YSTEMATIC REVIEW AND C ROSS-VALIDATION OCTOBER 26, 2020 1 Acknowledgements We are grateful to Dr. Allan Friedman, Dr. Lawrence Gordon, Jay Jacobs, Dr. Sasha Romanosky, Matthew Shabat, Kelly Shortridge, Steven Surdu, David Tobar, Brett Tucker and Sounil Yu for the review comments and helpful feedback on the earlier draft of the report. The authors would like to thank CISA staff for support and advice on this project. 2 Table of Contents 1. Objectives .................................................................................................................................................................... 7 2. Results in Brief .......................................................................................................................................................... 8 3. Analysis ...................................................................................................................................................................... 16 3.1. Per-Incident Cost and Loss Estimates .............................................................................................. 18 3.1.1. Cross-Validation: Primary Loss Data for Large and Small Incidents .................................. 20 3.1.2. Reconciliation of Per-Incident Cost Studies .................................................................................. 26 3.1.3. Per-Record Estimates ............................................................................................................................. 29 3.2. Aggregate -
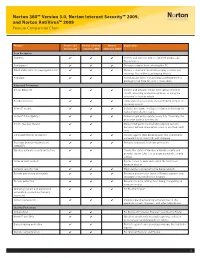
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton Antivirus™ 2009 Feature Comparison Chart
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton AntiVirus™ 2009 Feature Comparison Chart Feature Norton 360 Norton Internet Norton Explanation Version 3.0 Security 2009 AntiVirus 2009 Core Protection Antivirus ✔ ✔ ✔ Detects and removes viruses, Internet worms, and Trojan horses Antispyware ✔ ✔ ✔ Prevents spyware from infecting the PC Email and instant messaging protection ✔ ✔ ✔ Monitors email and instant messaging so users can exchange files without exchanging threats Antispam ✔ ✔ Automatically filters out annoying and fraudulent or phishing email from the user’s email inbox Advanced Protection Botnet detection ✔ ✔ ✔ Detects and prevents others from taking control of the PC, accessing private information, or using the computer to host an attack Rootkit detection ✔ ✔ ✔ Finds and removes threats that are hidden deep in the operating system Norton™ Insight ✔ ✔ ✔ Includes innovative, intelligence-driven technology for faster, fewer, shorter scans Norton™ Pulse Updates ✔ ✔ ✔ Delivers rapid pulse updates every 5 to 15 minutes for protection against new threats Smart, two-way firewall ✔ ✔ Makes intelligent incoming and outgoing security decisions without interrupting users to ask them each time Enhanced browser protection ✔ ✔ ✔ Secures against Web-based attacks that use browser vulnerabilities to infect PCs with malware Real-time behavioral protection ✔ ✔ ✔ Provides enhanced, real-time protection (SONAR™) Wireless network security protection ✔ ✔ Checks the status of wireless network security and provides expert advice on managing -

Anyconnect および Host Scan のアンチウイルス/アンチスパイウェア
AnyConnect および Host Scan のアンチウイルス/アンチスパイウェア/ファイアウォール サポート表 AnyConnect ポスチャ モジュールにより、AnyConnect Secure Mobility クライアントはホストにインス トールされているオペレーティング システム、およびアンチウイルス、アンチスパイウェア、ファイアウォールの 各ソフトウェアを識別できます。 Host Scan アプリケーションはポスチャ モジュールのコンポーネントに含まれ る、こうした情報を収集するアプリケーションです。 AnyConnect 3.0 より、Host Scan パッケージは AnyConnect Secure Mobility クライアントおよび Cisco Secure Desktop(CSD)の共有コンポーネントになっています。 それ以前は、Host Scan パッケージは CSD を インストールすることによってのみ利用可能になるコンポーネントの 1 つでした。 Host Scan パッケージを CSD から分離したのは、CSD の一部として提供されていたときよりも、ユー ザが頻繁に Host Scan サポート表を更新できるようにするためです。 このサポート表には、ユーザが動的なア クセス ポリシーで使用しているアンチウイルス/アンチスパイウェア/ファイアウォール アプリケーションの製品 名とバージョン情報が記載されています。 シスコでは、Host Scan パッケージに Host Scan アプリケーション、 Host Scan サポート表、および他のコンポーネントを含めて提供しています。 Host Scan サポート表のリスト アンチウイルス アプリケーション総合リスト アンチスパイウェア アプリケーション総合リスト ファイアウォール アプリケーション総合リスト Windows 用アンチウイルス Windows 用アンチスパイウェア Windows 用ファイアウォール Linux 用アンチウイルス Linux 用ファイアウォール Mac OS 用アンチウイルス Mac OS 用アンチスパイウェア Mac OS 用ファイアウォール A B C D E F G H I J K L M N O P Q R S T U V W X Y Z AA AB AC AD AE ファイル データ ファ バージョ データ ファイ データ ファイル データ ファイ エンジンのバー RTP の RTP の 前回のスキャン スキャン/クリー システムのフル アンイン GUI のアク トレイ アイコンの トレイ アイコン 有効期 脅威ログの取 スキャン プログラ フル スキャンの進捗 インストール ディ 一括スキャ メモリ スキャ アンチウイルス製品名 ライブ更新 サービス GUI の表示 のスキャ 有効日の取得 更新の進捗表示 プログラム言語の取得 イル dir の取 市場での別名 ン ルの時刻 のバージョン ルの署名 ジョン チェック 設定 時刻 ニング スキャン ストール ティブ化 表示 の非表示 限 得 ムの実行 表示 レクトリの取得 ン ン 1 ン 得 2 3 360Safe.com 4 360 Antivirus 1.x 9989999898888898 8888 8 9 8 9 9 9 88 5 360杀毒 1.x 9999988898888898 8889 8 8 8 9 9 9 88 6 AEC, spol. s r.o. 7 TrustPort Antivirus 2.x 8888998899888999 9888 8 9 8 9 8 988 8 Agnitum Ltd. -

Mind Your Own Business: a Longitudinal Study of Threats and Vulnerabilities in Enterprises
Mind your Own Business: A Longitudinal Study of Threats and Vulnerabilities in Enterprises Abstract—Enterprises own a significant fraction of the hosts to, financial assets, and security investment. Thus, it is very connected to the Internet and possess valuable assets, such as likely that the best practices mentioned above do not equally financial data and intellectual property, which may be targeted apply to all of them. by attackers. They suffer attacks that exploit unpatched hosts and install malware, resulting in breaches that may cost millions Currently, it is not clear how the security posture of in damages. Despite the scale of this phenomenon, the threat and enterprises differ according to different factors and whether vulnerability landscape of enterprises remains under-studied. The enterprises are indeed more secure than consumer hosts, i.e., security posture of enterprises remains unclear, and it’s unknown if their security investment is paying off. In this paper, we aim whether enterprises are indeed more secure than consumer hosts. to throw light into these questions by conducting a large-scale To address these questions, we perform the largest and longest longitudinal measurement study of enterprise security. We an- enterprise security study up to date. Our data covers nearly alyze the enterprise threat landscape including the prevalence 3 years and is collected from 28K enterprises, belonging to 67 industries, which own 82M hosts and 73M public-facing servers. of malware and PUP in enterprise hosts and how common security practices, such as vulnerability patching and operating Our measurements comprise of two parts: an analysis of system updates are handled. -

Amit a Windows 7
DVD DVD Többé nem fog akadozni az internet 11 Friss 9 GB 2009 A LEGÚJABB DRIVEREK, HASZNOS PROGRAMOK, Megmutatjuk, hogyan kell beállítani a rejtélyes Qos-t – lépésről lépésre R 90 A HÓNAP JÁTÉKAI, EXKLUZÍV CSOMAgok… 9 tipp: tökéletes TFT-képminőség Nem kell drága pénzen új monitor! Profin beállítjuk a mostanit R 98 GO DIGITAL! 2009/11_ CHIPONLINE.HU Ennyire (nem) biztonságos a vírusirtója – felfedjük! A DVD-N: Tesztünkből kiderül, hogy miért csődöl be sok víruskereső éles helyzetben R 40 es VÍRUSVADÁSZ teLJ CSOMAG Amit a Windows 7 jobban tud… 46 Gyors sikerek! Több gépre... Csak a CHIP-en! R TELJES VERZIÓ TELJES VERZIÓ TELJES VERZIÓ Egyedi, vicces, ...Szinkroni- Sytem Backup: …és, amin még javítani kell. Az összes új funkció szórakoztató zálás, mentés, vadonatúj, családi album megosztás 2010-es verzió és rejtett képesség tesztje + a Win 7 mint második rendszer Szimatolók a PC-jén? Segítünk! A legjobb eszközök az adatlopás ellen: 100% anonim szörf és levelezés R 26 Zseniális új funkciók eszközeihez T ESZ pt 20 tipp, melyekkel lenyűgöző tulajdonságokat LA TOVÁBBI DVD-TARTALOM 58 P R csalogathat elő átlagos hardvereiből 84 Radeon HD5870 Radeon teszt >> HD5870 10 tény a CPU-król >> Új technológiák: OpenID >> Mozizzunk óriástévén >> Gyorsteszt: P55-ös alaplapok >> Rés a víruspajzson >> Ennyire jó a 7 Windows >> CHIP mini PC >> 20 dolog, amit nem tudott… >> Soha többé net akadozó 1995 Ft, előfizetéssel 1395 Ft R XXI. évfolyam, 11. szám, 2009. november P55-ÖSz ALA asztali PC-k 36 Kiadja a Motor-Presse Budapest Lapkiadó Kft. A forradalma R CD CD Többé nem fog akadozni az internet 11 melléklettel 2009 EXKLUZÍV CSOMAGOK, FRISS Megmutatjuk, hogyan kell beállítani a rejtélyes Qos-t – lépésről lépésre R 90 PROGRAMOK, VÍRUSVÉDELEM.. -

Forescout Counteract® Endpoint Support Compatibility Matrix Updated: October 2018
ForeScout CounterACT® Endpoint Support Compatibility Matrix Updated: October 2018 ForeScout CounterACT Endpoint Support Compatibility Matrix 2 Table of Contents About Endpoint Support Compatibility ......................................................... 3 Operating Systems ....................................................................................... 3 Microsoft Windows (32 & 64 BIT Versions) ...................................................... 3 MAC OS X / MACOS ...................................................................................... 5 Linux .......................................................................................................... 6 Web Browsers .............................................................................................. 8 Microsoft Windows Applications ...................................................................... 9 Antivirus ................................................................................................. 9 Peer-to-Peer .......................................................................................... 25 Instant Messaging .................................................................................. 31 Anti-Spyware ......................................................................................... 34 Personal Firewall .................................................................................... 36 Hard Drive Encryption ............................................................................. 38 Cloud Sync ........................................................................................... -
Webroot Secureanywhere User Guide Complete Edition
User Guide for the Complete Edition Webroot Software, Inc. 385 Interlocken Crescent Suite 800 Broomfield, CO 80021 www.webroot.com Version 8.0.1 Webroot SecureAnywhere User Guide for the Complete Edition Version 8.0.1; May, 2012 © 2011- 2012 Webroot Software, Inc. All rights reserved. Webroot is a registered trademark and SecureAnywhere is a trademark of Webroot Software, Inc. All other product and company names mentioned may be trademarks or registered trademarks of their respective owners. Contents 1: Getting Started . .1 Installing the software. .2 Using the main interface. .5 Using the system tray menu. .6 Viewing the protection status . .7 Creating a Webroot account. .8 Adding PCs to your account . .9 Adding mobile devices to your account . .10 Viewing the PC security status online . .11 2: Scans . .15 About scans . .16 Running an immediate scan. .17 Running a custom scan . .19 Changing the scan schedule . .21 Changing scan settings . .23 3: Shields . .25 About shields . .26 Changing Realtime shield settings . .27 Changing Behavior shield settings . .29 Changing Core System shield settings . .31 Changing Web Threat shield settings . .33 4: Firewall. .35 About the firewall . .36 Changing firewall alert settings . .37 Managing network applications . .38 5: Quarantine . .41 About quarantine . .42 Managing quarantined items . .43 Managing file detection . .45 Using antimalware tools . .47 Saving a threat log . .49 6: Identity Protection. .51 About the Identity shield. .52 Changing Identity shield settings . .53 Managing protected applications . .55 Managing protected websites. .57 7: Password Management . .61 About Password Management . .62 Downloading the Passwords component . .63 Capturing login credentials in a website. -

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -
Kaspersky Managed Service Providers Program
Kaspersky for Business MOBILE CONTROLS CLOUD ENDPOINT NETWORK SECURITY REPORTING VIRTUALIZATION SIEM SUPPORT SERVERS SERVICES CLOUD APPS Kaspersky Managed Service Providers Program Technical Reference Guide www.kaspersky.com #truecybersecurity Table of contents Program benefits 1 MSP program requirements 1 Products 2 Training and certification 5 Professional services 5 Technical designs 6 Kaspersky Endpoint Security Cloud 6 Kaspersky Endpoint Security for Business Select 6 Kaspersky Endpoint Security for Business Advanced 6 Kaspersky Hybrid Cloud Security 7 Kaspersky Security for Microsoft Office 365 8 Kaspersky Security for Mail Server 8 Kaspersky Security for Internet Gateways 9 Customer onboarding checklist 10 Appendix A 11 Appendix B 12 Appendix C 13 Appendix D 17 Program benefits • Flexible licensing allow you to choose between a monthly subscription and an annual license. Because you own the product license, there’s no need to spend time administrating contract renewals with customers — extending licenses is easy; no special action is required. • Increase sales revenues with volume-based discounts — the more customers you have, the less you pay. Pricing depends on the total number of devices of all customers. Sell more and gain bigger discounts. • Be even more efficient and grow your client base without having to hire additional engineers. With built-in best practices that drive operational efficiency, you’ll improve your tech-to-device ratio and boost your bottom line. Increase your scalability and protect more endpoints with fewer headaches. • Improved usability. Kaspersky Lab understands the importance of ease of use when it comes to security, and our design and usability specialists are closely involved in product development. -
Printmgr File
ˆ200F$l2ZLVgqon1gÈŠ 200F$l2ZLVgqon1g¨ VDI-W7-PR3-1248 SYMANTEC CORPORATION Donnelley Financial12.6.30 EGV yanns0ap24-May-2018 22:26 EST 594139 TX 1 2* SYMANTEC CORP PAL HTM ESS 0C Page 1 of 1 UNITED STATES SECURITIES AND EXCHANGE COMMISSION Washington, D.C. 20549 FORM SD SPECIALIZED DISCLOSURE REPORT Symantec Corporation (Exact Name of Registrant as Specified in its Charter) Delaware 000-17781 77-0181864 (State or other jurisdiction of (Commission (IRS Employer incorporation or organization ) File Number) Identification No.) 350 Ellis Street, Mountain View, California 94043 (Address of Principal Executive Offices) (Zip Code) Nicholas R. Noviello, Executive Vice President and Chief Financial Officer (650) 527-8000 (Name and telephone number, including area code, of the person to contact in connection with this report.) Not Applicable (Former Name or Former Address, if Changed Since Last Report) Check the appropriate box below to indicate the rule pursuant to which this form is being filed, and provide the period to which the information in this form applies: Rule 13p-1 under the Securities Exchange Act (17 CFR 240.13p-1) for the reporting period January 1 to December 31, 2017 ˆ200F$l2ZLVhV$Vk6$Š 200F$l2ZLVhV$Vk6$ VDI-W7-PFL-0639 SYMANTEC CORPORATION Donnelley Financial12.6.29 EGV ahern0ap24-May-2018 23:14 EST 594139 TX 2 3* SYMANTEC CORP PAL HTM ESS 0C Page 1 of 1 Item 1.01. Conflict Minerals Disclosure and Report. Conflict Minerals Disclosure A copy of the Conflict Minerals Report of Symantec Corporation (“Symantec”) for the reporting period January 1 to December 31, 2017 is filed as Exhibit 1.01 to this specialized disclosure report on Form SD and is also available at Symantec’s website at https://www.symantec.com/about/corporate-responsibility/resources/corporate-responsibility-policies . -

Q3 Consumer Endpoint Protection Jul-Sep 2020
HOME ANTI- MALWARE PROTECTION JUL - SEP 2020 selabs.uk [email protected] @SELabsUK www.facebook.com/selabsuk blog.selabs.uk SE Labs tested a variety of anti-malware (aka ‘anti-virus’; aka ‘endpoint security’) products from a range of well-known vendors in an effort to judge which were the most effective. Each product was exposed to the same threats, which were a mixture of targeted attacks using well-established techniques and public email and web-based threats that were found to be live on the internet at the time of the test. The results indicate how effectively the products were at detecting and/or protecting against those threats in real time. 2 Home Anti-Malware Protection July - September 2020 MANAGEMENT Chief Executive Officer Simon Edwards CONTENTS Chief Operations Officer Marc Briggs Chief Human Resources Officer Magdalena Jurenko Chief Technical Officer Stefan Dumitrascu Introduction 04 TEstING TEAM Executive Summary 05 Nikki Albesa Zaynab Bawa 1. Total Accuracy Ratings 06 Thomas Bean Solandra Brewster Home Anti-Malware Protection Awards 07 Liam Fisher Gia Gorbold Joseph Pike 2. Threat Responses 08 Dave Togneri Jake Warren 3. Protection Ratings 10 Stephen Withey 4. Protection Scores 12 IT SUPPORT Danny King-Smith 5. Protection Details 13 Chris Short 6. Legitimate Software Ratings 14 PUBLICatION Sara Claridge 6.1 Interaction Ratings 15 Colin Mackleworth 6.2 Prevalence Ratings 16 Website selabs.uk Twitter @SELabsUK 6.3 Accuracy Ratings 16 Email [email protected] Facebook www.facebook.com/selabsuk 6.4 Distribution of Impact Categories 17 Blog blog.selabs.uk Phone +44 (0)203 875 5000 7.