The Ultimate Cybersecurity Guide for the It Professional
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

A the Hacker
A The Hacker Madame Curie once said “En science, nous devons nous int´eresser aux choses, non aux personnes [In science, we should be interested in things, not in people].” Things, however, have since changed, and today we have to be interested not just in the facts of computer security and crime, but in the people who perpetrate these acts. Hence this discussion of hackers. Over the centuries, the term “hacker” has referred to various activities. We are familiar with usages such as “a carpenter hacking wood with an ax” and “a butcher hacking meat with a cleaver,” but it seems that the modern, computer-related form of this term originated in the many pranks and practi- cal jokes perpetrated by students at MIT in the 1960s. As an example of the many meanings assigned to this term, see [Schneier 04] which, among much other information, explains why Galileo was a hacker but Aristotle wasn’t. A hack is a person lacking talent or ability, as in a “hack writer.” Hack as a verb is used in contexts such as “hack the media,” “hack your brain,” and “hack your reputation.” Recently, it has also come to mean either a kludge, or the opposite of a kludge, as in a clever or elegant solution to a difficult problem. A hack also means a simple but often inelegant solution or technique. The following tentative definitions are quoted from the jargon file ([jargon 04], edited by Eric S. Raymond): 1. A person who enjoys exploring the details of programmable systems and how to stretch their capabilities, as opposed to most users, who prefer to learn only the minimum necessary. -

Post-Mortem of a Zombie: Conficker Cleanup After Six Years Hadi Asghari, Michael Ciere, and Michel J.G
Post-Mortem of a Zombie: Conficker Cleanup After Six Years Hadi Asghari, Michael Ciere, and Michel J.G. van Eeten, Delft University of Technology https://www.usenix.org/conference/usenixsecurity15/technical-sessions/presentation/asghari This paper is included in the Proceedings of the 24th USENIX Security Symposium August 12–14, 2015 • Washington, D.C. ISBN 978-1-939133-11-3 Open access to the Proceedings of the 24th USENIX Security Symposium is sponsored by USENIX Post-Mortem of a Zombie: Conficker Cleanup After Six Years Hadi Asghari, Michael Ciere and Michel J.G. van Eeten Delft University of Technology Abstract more sophisticated C&C mechanisms that are increas- ingly resilient against takeover attempts [30]. Research on botnet mitigation has focused predomi- In pale contrast to this wealth of work stands the lim- nantly on methods to technically disrupt the command- ited research into the other side of botnet mitigation: and-control infrastructure. Much less is known about the cleanup of the infected machines of end users. Af- effectiveness of large-scale efforts to clean up infected ter a botnet is successfully sinkholed, the bots or zom- machines. We analyze longitudinal data from the sink- bies basically remain waiting for the attackers to find hole of Conficker, one the largest botnets ever seen, to as- a way to reconnect to them, update their binaries and sess the impact of what has been emerging as a best prac- move the machines out of the sinkhole. This happens tice: national anti-botnet initiatives that support large- with some regularity. The recent sinkholing attempt of scale cleanup of end user machines. -

Jeffrey Heim, Marcel Hernandez, Maria Nunez,& Matthias Katerna Morris Worm on November 2, 1988, Robert Tappan Morris Releas
Jeffrey Heim, Marcel Hernandez, Maria Nunez,& Matthias Katerna Morris Worm On November 2, 1988, Robert Tappan Morris released a worm into the internet. The experimental worm was the first of its kind. It replicated itself and programmed itself, so it ended up spreading much faster than Morris expected. It self-programmed and self-replicated at an exponential rate in a manner that had never been seen before. Morris knew this worm was not necessarily ethical, for he released it out of MIT instead of his own Cornell University. In due course, many computers across the United States had crashed because of Morris. Once he discovered how much damage the worm had been causing, he reached out to a friend at Harvard looking for a solution to stop it. They attempted in sending an anonymous message to the network with directions that could kill the worm, but the message came through too late since they system was clogged. Many significant computers at colleges, businesses and the military became infected. The cost to fix each computer ranged from $200 to over $53,000. The worm exploited vulnerabilities in computer systems and in the UNIX email software. Within 24 hours of releasing the worm, thousands of people were aware something was unusual. Eventually, it would infect ten percent of all computers using the internet. The Morris Worm was the largest malware case ever to reach this percentage. However, the percentage was so high due to the fact that the number of computers was much less than today. The computers it impacted included significant systems, such as Stanford’s, Berkley’s and NASA’s. -

Computer Security CS 426 Lecture 15
Computer Security CS 426 Lecture 15 Malwares CS426 Fall 2010/Lecture 15 1 Trapdoor • SttitittSecret entry point into a system – Specific user identifier or password that circumvents normal security procedures. • Commonlyyy used by developers – Could be included in a compiler. CS426 Fall 2010/Lecture 15 2 Logic Bomb • Embedded in legitimate programs • Activated when specified conditions met – E.g., presence/absence of some file; Particular date/time or particular user • When triggered, typically damages system – Modify/delete files/disks CS426 Fall 2010/Lecture 15 3 Examppgle of Logic Bomb • In 1982 , the Trans-Siber ian Pipe line inc iden t occurred. A KGB operative was to steal the plans fhititdtltditfor a sophisticated control system and its software from a Canadian firm, for use on their Siberi an pi peli ne. The CIA was tippe d o ff by documents in the Farewell Dossier and had the company itlibbithinsert a logic bomb in the program for sabotage purposes. This eventually resulted in "the most monu mental non-nu clear ex plosion and fire ever seen from space“. CS426 Fall 2010/Lecture 15 4 Trojan Horse • Program with an overt Example: Attacker: (expected) and covert effect Place the following file cp /bin/sh /tmp/.xxsh – Appears normal/expected chmod u+s,o+x /tmp/.xxsh – Covert effect violates security policy rm ./ls • User tricked into executing ls $* Trojan horse as /homes/victim/ls – Expects (and sees) overt behavior – Covert effect performed with • Victim user’s authorization ls CS426 Fall 2010/Lecture 15 5 Virus • Self-replicating -

Using Malware's Self-Defence Mechanism to Harden
Using Malware’s Self-Defence Mechanism to Harden Defence and Remediation Tools Jonathan Pan Wee Kim Wee School of Communication and Information, Nanyang Technological University, Singapore [email protected] Abstract— Malware are becoming a major problem to every them to completely bypass the protection of Firewall and individual and organization in the cyber world. They are Anti-Virus. According to Filiol [30], Malware detection is a advancing in sophistication in many ways. Besides their NP-hard problem. Besides the fact that these defences are advanced abilities to penetrate and stay evasive against detection becoming ineffective against Malware, these defences are also and remediation, they have strong resilience mechanisms that becoming victims of attacks by Malware as part of the latter’s are defying all attempts to eradicate them. Malware are also attacking defence of the systems and making them defunct. self-preservation strategy [21], [27]. The starting point of this When defences are brought down, the organisation or individual cyber problem with Malware is their ability to infiltrate. This will lose control over the IT assets and defend against the is typically done through the weakest link in the defence Malware perpetuators. In order to gain the capability to defend, strategy due to humans are involved. One went as far as to it is necessary to keep the defences or remediation tools active comment that it is people’s stupidity that led to security lapses and not defunct. Given that Malware have proven to be resilient [7]. Malware will inevitably infiltrate past the defences and against deployed defences and remediation tools, the proposed when they do, it is essential to quickly contain these Malware research advocates to utilize the techniques used by Malware to before they induce greater damages to the organizations. -

Strategies of Computer Worms
304543_ch09.qxd 1/7/05 9:05 AM Page 313 CHAPTER 9 Strategies of Computer Worms “Worm: n., A self-replicating program able to propagate itself across network, typically having a detrimental effect.” —Concise Oxford English Dictionary, Revised Tenth Edition 313 304543_ch09.qxd 1/7/05 9:05 AM Page 314 Chapter 9—Strategies of Computer Worms 9.1 Introduction This chapter discusses the generic (or at least “typical”) structure of advanced computer worms and the common strategies that computer worms use to invade new target systems. Computer worms primarily replicate on networks, but they represent a subclass of computer viruses. Interestingly enough, even in security research communities, many people imply that computer worms are dramatically different from computer viruses. In fact, even within CARO (Computer Antivirus Researchers Organization), researchers do not share a common view about what exactly can be classified as a “worm.” We wish to share a common view, but well, at least a few of us agree that all computer worms are ultimately viruses1. Let me explain. The network-oriented infection strategy is indeed a primary difference between viruses and computer worms. Moreover, worms usually do not need to infect files but propagate as standalone programs. Additionally, several worms can take con- trol of remote systems without any help from the users, usually exploiting a vul- nerability or set of vulnerabilities. These usual characteristics of computer worms, however, do not always hold. Table 9.1 shows several well-known threats. Table -

Iptrust Botnet / Malware Dictionary This List Shows the Most Common Botnet and Malware Variants Tracked by Iptrust
ipTrust Botnet / Malware Dictionary This list shows the most common botnet and malware variants tracked by ipTrust. This is not intended to be an exhaustive list, since new threat intelligence is always being added into our global Reputation Engine. NAME DESCRIPTION Conficker A/B Conficker A/B is a downloader worm that is used to propagate additional malware. The original malware it was after was rogue AV - but the army's current focus is undefined. At this point it has no other purpose but to spread. Propagation methods include a Microsoft server service vulnerability (MS08-067) - weakly protected network shares - and removable devices like USB keys. Once on a machine, it will attach itself to current processes such as explorer.exe and search for other vulnerable machines across the network. Using a list of passwords and actively searching for legitimate usernames - the ... Mariposa Mariposa was first observed in May 2009 as an emerging botnet. Since then it has infected an ever- growing number of systems; currently, in the millions. Mariposa works by installing itself in a hidden location on the compromised system and injecting code into the critical process ͞ĞdžƉůŽƌĞƌ͘ĞdžĞ͘͟/ƚŝƐknown to affect all modern Windows versions, editing the registry to allow it to automatically start upon login. Additionally, there is a guard that prevents deletion while running, and it automatically restarts upon crash/restart of explorer.exe. In essence, Mariposa opens a backdoor on the compromised computer, which grants full shell access to ... Unknown A botnet is designated 'unknown' when it is first being tracked, or before it is given a publicly- known common name. -
Tangled Web : Tales of Digital Crime from the Shadows of Cyberspace
TANGLED WEB Tales of Digital Crime from the Shadows of Cyberspace RICHARD POWER A Division of Macmillan USA 201 West 103rd Street, Indianapolis, Indiana 46290 Tangled Web: Tales of Digital Crime Associate Publisher from the Shadows of Cyberspace Tracy Dunkelberger Copyright 2000 by Que Corporation Acquisitions Editor All rights reserved. No part of this book shall be reproduced, stored in a Kathryn Purdum retrieval system, or transmitted by any means, electronic, mechanical, pho- Development Editor tocopying, recording, or otherwise, without written permission from the Hugh Vandivier publisher. No patent liability is assumed with respect to the use of the infor- mation contained herein. Although every precaution has been taken in the Managing Editor preparation of this book, the publisher and author assume no responsibility Thomas Hayes for errors or omissions. Nor is any liability assumed for damages resulting from the use of the information contained herein. Project Editor International Standard Book Number: 0-7897-2443-x Tonya Simpson Library of Congress Catalog Card Number: 00-106209 Copy Editor Printed in the United States of America Michael Dietsch First Printing: September 2000 Indexer 02 01 00 4 3 2 Erika Millen Trademarks Proofreader Benjamin Berg All terms mentioned in this book that are known to be trademarks or ser- vice marks have been appropriately capitalized. Que Corporation cannot Team Coordinator attest to the accuracy of this information. Use of a term in this book should Vicki Harding not be regarded as affecting the validity of any trademark or service mark. Design Manager Warning and Disclaimer Sandra Schroeder Every effort has been made to make this book as complete and as accurate Cover Designer as possible, but no warranty or fitness is implied. -

Intelligent Malware Detection Using File-To-File Relations and Enhancing Its Security Against Adversarial Attacks
Graduate Theses, Dissertations, and Problem Reports 2019 Intelligent Malware Detection Using File-to-file Relations and Enhancing its Security against Adversarial Attacks Lingwei Chen [email protected] Follow this and additional works at: https://researchrepository.wvu.edu/etd Part of the Information Security Commons Recommended Citation Chen, Lingwei, "Intelligent Malware Detection Using File-to-file Relations and Enhancing its Security against Adversarial Attacks" (2019). Graduate Theses, Dissertations, and Problem Reports. 3844. https://researchrepository.wvu.edu/etd/3844 This Dissertation is protected by copyright and/or related rights. It has been brought to you by the The Research Repository @ WVU with permission from the rights-holder(s). You are free to use this Dissertation in any way that is permitted by the copyright and related rights legislation that applies to your use. For other uses you must obtain permission from the rights-holder(s) directly, unless additional rights are indicated by a Creative Commons license in the record and/ or on the work itself. This Dissertation has been accepted for inclusion in WVU Graduate Theses, Dissertations, and Problem Reports collection by an authorized administrator of The Research Repository @ WVU. For more information, please contact [email protected]. Intelligent Malware Detection Using File-to-file Relations and Enhancing its Security against Adversarial Attacks Lingwei Chen Dissertation submitted to the Benjamin M. Statler College of Engineering and Mineral Resources at West Virginia University in partial fulfillment of the requirements for the degree of Doctor of Philosophy in Computer Science Yanfang Ye, Ph.D., Committee Chairperson Donald Adjeroh, Ph.D. Elaine M. -
Chapter 3: Viruses, Worms, and Blended Threats
Chapter 3 Chapter 3: Viruses, Worms, and Blended Threats.........................................................................46 Evolution of Viruses and Countermeasures...................................................................................46 The Early Days of Viruses.................................................................................................47 Beyond Annoyance: The Proliferation of Destructive Viruses .........................................48 Wiping Out Hard Drives—CIH Virus ...................................................................48 Virus Programming for the Masses 1: Macro Viruses...........................................48 Virus Programming for the Masses 2: Virus Generators.......................................50 Evolving Threats, Evolving Countermeasures ..................................................................51 Detecting Viruses...................................................................................................51 Radical Evolution—Polymorphic and Metamorphic Viruses ...............................53 Detecting Complex Viruses ...................................................................................55 State of Virus Detection.........................................................................................55 Trends in Virus Evolution..................................................................................................56 Worms and Vulnerabilities ............................................................................................................57 -
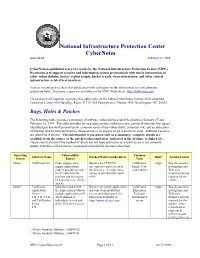
Cybernotes Issue #4-99 February 17, 1999
National Infrastructure Protection Center CyberNotes Issue #4-99 February 17, 1999 CyberNotes is published every two weeks by the National Infrastructure Protection Center (NIPC). Its mission is to support security and information system professionals with timely information on cyber vulnerabilities, hacker exploit scripts, hacker trends, virus information, and other critical infrastructure-related best practices. You are encouraged to share this publication with colleagues in the information and infrastructure protection field. Electronic copies are available on the NIPC Web site at http://www.nipc.gov. Please direct any inquiries regarding this publication to the Editor-CyberNotes, National Infrastructure Protection Center, FBI Building, Room 11719, 935 Pennsylvania Avenue, NW, Washington, DC, 20535. Bugs, Holes & Patches The following table provides a summary of software vulnerabilities identified between January 27 and February 12, 1999. The table provides the operating system, software name, potential vulnerability/impact, identified patches/workarounds/alerts, common name of the vulnerability, potential risk, and an indication of whether attacks have utilized this vulnerability or an exploit script is known to exist. Software versions are identified if known. This information is presented only as a summary; complete details are available from the source of the patch/workaround/alert, indicated in the footnote or linked site. Please note that even if the method of attack has not been utilized or an exploit script is not currently widely available on the Internet, a potential vulnerability has been identified. Operating Vulnerability/ Common Software Name Patches/Workarounds/Alerts Risk* Attacks/Scripts System Impact Name Allaire1 ColdFusion 4.0 Code snippets from Remove the CFDOCS ColdFusion High Bug discussed in sample applications directory or restrict access to Sample Code newsgroups and make it possible to make the directory. -
Lesson 6: Hacking Malware
LESSON 6 HACKING MALWARE Lesson 6: Malware WARNING The Hacker Highschool Project is a learning tool and as with any learning tool there are dangers. Some lessons if abused may result in physical injury. Some additional dangers may also exist where there is not enough research on possible effects of emanations from particular technologies. Students using these lessons should be supervised yet encouraged to learn, try, and do. However ISECOM cannot accept responsibility for how any information herein is abused. The following lessons and workbooks are open and publicly available under the following terms and conditions of ISECOM: All works in the Hacker Highschool Project are provided for non-commercial use with elementary school students, junior high school students, and high school students whether in a public institution, private institution, or a part of home-schooling. These materials may not be reproduced for sale in any form. The provision of any class, course, training, or camp with these materials for which a fee is charged is expressly forbidden without a license including college classes, university classes, trade-school classes, summer or computer camps, and similar. To purchase a license, visit the LICENSE section of the HHS web page at http://www.hackerhighschool.org/licensing.html. The HHS Project is an open community effort and if you find value in this project we ask that you support us through the purchase of a license, a donation, or sponsorship. 2 Lesson 6: Malware Table of Contents WARNING....................................................................................................................................................2