Oracle Solaris 11.4 Security Target, V1.3
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Porting Darwin to the MV88F6281 Arming the Snowleopard
Porting Darwin to the MV88F6281 ARMing the SnowLeopard. Tristan Schaap 1269011 Apple Inc. Platform Technologies Group Delft University of Technology Dept. of Computer Science Committee: Ir. B.R. Sodoyer Dr. K. van der Meer Preface! 3 Introduction! 4 Summary! 5 Building a new platform! 6 Booting iBoot! 7 Building the kernelcache! 8 Booting the kernel! 10 THUMBs down! 16 Conclusion! 18 Future Work! 19 Glossary! 20 References! 21 Appendix A! 22 Appendix B! 23 Skills! 23 Process! 26 Reflection! 27 Appendix C! 28 Plan of Approach! 28 2 Preface Due to innovative nature of this project, I have had to limit myself in the detail in which I describe my work. This means that this report will be lacking in such things as product specific- and classified information. I would like to thank a few people who made it possible for me to successfully complete my internship at the Platform Technologies Group at Apple. First off, the people who made this internship possible, John Kelley, Ben Byer and my manager John Wright. Mike Smith, Tom Duffy and Anthony Yvanovich for helping me through the rough patches of this project. And the entirety of Core OS for making my stay an unforgettable experience. 3 Introduction About the Platform Technologies Group As it was described by a manager: “We do the plumbing, if we do our jobs right, you never see it.”. The Platform Technologies Group, a subdivision of the Core OS department, works on the embedded platforms that Apple maintains. Here, platforms are brought up and the embedded kernel and lower level support for the platforms is maintained. -

Linux on the Road
Linux on the Road Linux with Laptops, Notebooks, PDAs, Mobile Phones and Other Portable Devices Werner Heuser <wehe[AT]tuxmobil.org> Linux Mobile Edition Edition Version 3.22 TuxMobil Berlin Copyright © 2000-2011 Werner Heuser 2011-12-12 Revision History Revision 3.22 2011-12-12 Revised by: wh The address of the opensuse-mobile mailing list has been added, a section power management for graphics cards has been added, a short description of Intel's LinuxPowerTop project has been added, all references to Suspend2 have been changed to TuxOnIce, links to OpenSync and Funambol syncronization packages have been added, some notes about SSDs have been added, many URLs have been checked and some minor improvements have been made. Revision 3.21 2005-11-14 Revised by: wh Some more typos have been fixed. Revision 3.20 2005-11-14 Revised by: wh Some typos have been fixed. Revision 3.19 2005-11-14 Revised by: wh A link to keytouch has been added, minor changes have been made. Revision 3.18 2005-10-10 Revised by: wh Some URLs have been updated, spelling has been corrected, minor changes have been made. Revision 3.17.1 2005-09-28 Revised by: sh A technical and a language review have been performed by Sebastian Henschel. Numerous bugs have been fixed and many URLs have been updated. Revision 3.17 2005-08-28 Revised by: wh Some more tools added to external monitor/projector section, link to Zaurus Development with Damn Small Linux added to cross-compile section, some additions about acoustic management for hard disks added, references to X.org added to X11 sections, link to laptop-mode-tools added, some URLs updated, spelling cleaned, minor changes. -
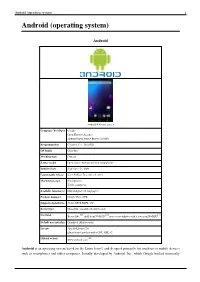
Android (Operating System) 1 Android (Operating System)
Android (operating system) 1 Android (operating system) Android Android 4.4 home screen Company / developer Google Open Handset Alliance Android Open Source Project (AOSP) Programmed in C (core), C++, Java (UI) OS family Unix-like Working state Current Source model Open source with proprietary components Initial release September 23, 2008 Latest stable release 4.4.2 KitKat / December 9, 2013 Marketing target Smartphones Tablet computers Available language(s) Multi-lingual (46 languages) Package manager Google Play, APK Supported platforms 32-bit ARM, MIPS, x86 Kernel type Monolithic (modified Linux kernel) [1] [2] [3] Userland Bionic libc, shell from NetBSD, native core utilities with a few from NetBSD Default user interface Graphical (Multi-touch) License Apache License 2.0 Linux kernel patches under GNU GPL v2 [4] Official website www.android.com Android is an operating system based on the Linux kernel, and designed primarily for touchscreen mobile devices such as smartphones and tablet computers. Initially developed by Android, Inc., which Google backed financially Android (operating system) 2 and later bought in 2005, Android was unveiled in 2007 along with the founding of the Open Handset Alliance: a consortium of hardware, software, and telecommunication companies devoted to advancing open standards for mobile devices. The first publicly available smartphone running Android, the HTC Dream, was released on October 22, 2008. The user interface of Android is based on direct manipulation, using touch inputs that loosely correspond to real-world actions, like swiping, tapping, pinching and reverse pinching to manipulate on-screen objects. Internal hardware such as accelerometers, gyroscopes and proximity sensors are used by some applications to respond to additional user actions, for example adjusting the screen from portrait to landscape depending on how the device is oriented. -

The Dragonflybsd Operating System
1 The DragonFlyBSD Operating System Jeffrey M. Hsu, Member, FreeBSD and DragonFlyBSD directories with slightly over 8 million lines of code, 2 million Abstract— The DragonFlyBSD operating system is a fork of of which are in the kernel. the highly successful FreeBSD operating system. Its goals are to The project has a number of resources available to the maintain the high quality and performance of the FreeBSD 4 public, including an on-line CVS repository with mirror sites, branch, while exploiting new concepts to further improve accessible through the web as well as the cvsup service, performance and stability. In this paper, we discuss the motivation for a new BSD operating system, new concepts being mailing list forums, and a bug submission system. explored in the BSD context, the software infrastructure put in place to explore these concepts, and their application to the III. MOTIVATION network subsystem in particular. A. Technical Goals Index Terms— Message passing, Multiprocessing, Network The DragonFlyBSD operating system has several long- operating systems, Protocols, System software. range technical goals that it hopes to accomplish within the next few years. The first goal is to add lightweight threads to the BSD kernel. These threads are lightweight in the sense I. INTRODUCTION that, while user processes have an associated thread and a HE DragonFlyBSD operating system is a fork of the process context, kernel processes are pure threads with no T highly successful FreeBSD operating system. Its goals are process context. The threading model makes several to maintain the high quality and performance of the FreeBSD guarantees with respect to scheduling to ensure high 4 branch, while exploring new concepts to further improve performance and simplify reasoning about concurrency. -

Cryptanalysis of the Random Number Generator of the Windows Operating System
Cryptanalysis of the Random Number Generator of the Windows Operating System Leo Dorrendorf School of Engineering and Computer Science The Hebrew University of Jerusalem 91904 Jerusalem, Israel [email protected] Zvi Gutterman Benny Pinkas¤ School of Engineering and Computer Science Department of Computer Science The Hebrew University of Jerusalem University of Haifa 91904 Jerusalem, Israel 31905 Haifa, Israel [email protected] [email protected] November 4, 2007 Abstract The pseudo-random number generator (PRNG) used by the Windows operating system is the most commonly used PRNG. The pseudo-randomness of the output of this generator is crucial for the security of almost any application running in Windows. Nevertheless, its exact algorithm was never published. We examined the binary code of a distribution of Windows 2000, which is still the second most popular operating system after Windows XP. (This investigation was done without any help from Microsoft.) We reconstructed, for the ¯rst time, the algorithm used by the pseudo- random number generator (namely, the function CryptGenRandom). We analyzed the security of the algorithm and found a non-trivial attack: given the internal state of the generator, the previous state can be computed in O(223) work (this is an attack on the forward-security of the generator, an O(1) attack on backward security is trivial). The attack on forward-security demonstrates that the design of the generator is flawed, since it is well known how to prevent such attacks. We also analyzed the way in which the generator is run by the operating system, and found that it ampli¯es the e®ect of the attacks: The generator is run in user mode rather than in kernel mode, and therefore it is easy to access its state even without administrator privileges. -

Vulnerabilities of the Linux Random Number Generator
Black Hat 2006 Open to Attack Vulnerabilities of the Linux Random Number Generator Zvi Gutterman Chief Technology Officer with Benny Pinkas Tzachy Reinman Zvi Gutterman CTO, Safend Previously a chief architect in the IP infrastructure group for ECTEL (NASDAQ:ECTX) and an officer in the Israeli Defense Forces (IDF) Elite Intelligence unit. Master's and Bachelor's degrees in Computer Science from the Israeli Institute of Technology. Ph.D. candidate at the Hebrew University of Jerusalem, focusing on security, network protocols, and software engineering. - Proprietary & Confidential - Safend Safend is a leading provider of innovative endpoint security solutions that protect against corporate data leakage and penetration via physical and wireless ports. Safend Auditor and Safend Protector deliver complete visibility and granular control over all enterprise endpoints. Safend's robust, ultra- secure solutions are intuitive to manage, almost impossible to circumvent, and guarantee connectivity and productivity, without sacrificing security. For more information, visit www.safend.com. - Proprietary & Confidential - Pseudo-Random-Number-Generator (PRNG) Elementary and critical component in many cryptographic protocols Usually: “… Alice picks key K at random …” In practice looks like random.nextBytes(bytes); session_id = digest.digest(bytes); • Which is equal to session_id = md5(get next 16 random bytes) - Proprietary & Confidential - If the PRNG is predictable the cryptosystem is not secure Demonstrated in - Netscape SSL [GoldbergWagner 96] http://www.cs.berkeley.edu/~daw/papers/ddj-netscape.html Apache session-id’s [GuttermanMalkhi 05] http://www.gutterman.net/publications/2005/02/hold_your_sessions_an_attack_o.html - Proprietary & Confidential - General PRNG Scheme 0 0 01 Stateseed 110 100010 Properties: 1. Pseudo-randomness Output bits are indistinguishable from uniform random stream 2. -

Analysis of Entropy Usage in Random Number Generators
DEGREE PROJECT IN THE FIELD OF TECHNOLOGY ENGINEERING PHYSICS AND THE MAIN FIELD OF STUDY COMPUTER SCIENCE AND ENGINEERING, SECOND CYCLE, 30 CREDITS STOCKHOLM, SWEDEN 2017 Analysis of Entropy Usage in Random Number Generators KTH ROYAL INSTITUTE OF TECHNOLOGY SCHOOL OF COMPUTER SCIENCE AND COMMUNICATION Analysis of Entropy Usage in Random Number Generators JOEL GÄRTNER Master in Computer Science Date: September 16, 2017 Supervisor: Douglas Wikström Examiner: Johan Håstad Principal: Omegapoint Swedish title: Analys av entropianvändning i slumptalsgeneratorer School of Computer Science and Communication i Abstract Cryptographically secure random number generators usually require an outside seed to be initialized. Other solutions instead use a continuous entropy stream to ensure that the internal state of the generator always remains unpredictable. This thesis analyses four such generators with entropy inputs. Furthermore, different ways to estimate entropy is presented and a new method useful for the generator analy- sis is developed. The developed entropy estimator performs well in tests and is used to analyse en- tropy gathered from the different generators. Furthermore, all the analysed generators exhibit some seemingly unintentional behaviour, but most should still be safe for use. ii Sammanfattning Kryptografiskt säkra slumptalsgeneratorer behöver ofta initialiseras med ett oförutsägbart frö. En annan lösning är att istället konstant ge slumptalsgeneratorer entropi. Detta gör det möjligt att garantera att det interna tillståndet i generatorn hålls oförutsägbart. I den här rapporten analyseras fyra sådana generatorer som matas med entropi. Dess- utom presenteras olika sätt att skatta entropi och en ny skattningsmetod utvecklas för att användas till analysen av generatorerna. Den framtagna metoden för entropiskattning lyckas bra i tester och används för att analysera entropin i de olika generatorerna. -

Trusted Platform Module ST33TPHF20SPI FIPS 140-2 Security Policy Level 2
STMICROELECTRONICS Trusted Platform Module ST33TPHF20SPI ST33HTPH2E28AAF0 / ST33HTPH2E32AAF0 / ST33HTPH2E28AAF1 / ST33HTPH2E32AAF1 ST33HTPH2028AAF3 / ST33HTPH2032AAF3 FIPS 140-2 Security Policy Level 2 Firmware revision: 49.00 / 4A.00 HW version: ST33HTPH revision A Date: 2017/07/19 Document Version: 01-11 NON-PROPRIETARY DOCUMENT FIPS 140-2 SECURITY POLICY NON-PROPRIETARY DOCUMENT Page 1 of 43 Table of Contents 1 MODULE DESCRIPTION .................................................................................................................... 3 1.1 DEFINITION ..................................................................................................................................... 3 1.2 MODULE IDENTIFICATION ................................................................................................................. 3 1.2.1 AAF0 / AAF1 ......................................................................................................................... 3 1.2.2 AAF3 ..................................................................................................................................... 4 1.3 PINOUT DESCRIPTION ...................................................................................................................... 6 1.4 BLOCK DIAGRAMS ........................................................................................................................... 8 1.4.1 HW block diagram ............................................................................................................... -

Dev/Random and FIPS
/dev/random and Your FIPS 140-2 Validation Can Be Friends Yes, Really Valerie Fenwick Manager, Solaris Cryptographic Technologies team Oracle May 19, 2016 Photo by CGP Grey, http://www.cgpgrey.com/ Creative Commons Copyright © 2016, Oracle and/or its affiliates. All rights reserved. Not All /dev/random Implementations Are Alike • Your mileage may vary – Even across OS versions – Solaris 7‘s /dev/random is nothing like Solaris 11’s – Which look nothing like /dev/random in Linux, OpenBSD, MacOS, etc – Windows gets you a whole ‘nother ball of wax… • No common ancestry – Other than concept Copyright © 2016, Oracle and/or its affiliates. All rights reserved 3 /dev/random vs /dev/urandom • On most OSes, /dev/urandom is a PRNG (Pseudo-Random Number Generator) – In some, so is their /dev/random • Traditionally, /dev/urandom will never block – /dev/random will block • For fun, on some OSes /dev/urandom is a link to /dev/random Copyright © 2016, Oracle and/or its affiliates. All rights reserved 4 FreeBSD: /dev/random • /dev/urandom is a link to /dev/random • Only blocks until seeded • Based on Fortuna Copyright © 2016, Oracle and/or its affiliates. All rights reserved 5 OpenBSD: /dev/random • Called /dev/arandom • Does not block • Formerly based on ARCFOUR – Now based on ChaCha20 – C API still named arc4random() Copyright © 2016, Oracle and/or its affiliates. All rights reserved 6 MacOS: /dev/random • /dev/urandom is a link to /dev/random • 160-bit Yarrow PRNG, uses SHA1 and 3DES Copyright © 2016, Oracle and/or its affiliates. All rights reserved 7 Linux: /dev/random • Blocks when entropy is depleted • Has a separate non-blocking /dev/urandom Copyright © 2016, Oracle and/or its affiliates. -

Linux Random Number Generator
Not-So-Random Numbers in Virtualized Linux and the Whirlwind RNG Adam Everspaugh, Yan Zhai, Robert Jellinek, Thomas Ristenpart, Michael Swift Department of Computer Sciences University of Wisconsin-Madison {ace, yanzhai, jellinek, rist, swift}@cs.wisc.edu Abstract—Virtualized environments are widely thought to user-level cryptographic processes such as Apache TLS can cause problems for software-based random number generators suffer a catastrophic loss of security when run in a VM that (RNGs), due to use of virtual machine (VM) snapshots as is resumed multiple times from the same snapshot. Left as an well as fewer and believed-to-be lower quality entropy sources. Despite this, we are unaware of any published analysis of the open question in that work is whether reset vulnerabilities security of critical RNGs when running in VMs. We fill this also affect system RNGs. Finally, common folklore states gap, using measurements of Linux’s RNG systems (without the that software entropy sources are inherently worse on virtu- aid of hardware RNGs, the most common use case today) on alized platforms due to frequent lack of keyboard and mouse, Xen, VMware, and Amazon EC2. Despite CPU cycle counters interrupt coalescing by VM managers, and more. Despite providing a significant source of entropy, various deficiencies in the design of the Linux RNG makes its first output vulnerable all this, to date there have been no published measurement during VM boots and, more critically, makes it suffer from studies evaluating the security of Linux (or another common catastrophic reset vulnerabilities. We show cases in which the system RNG) in modern virtualized environments. -

Getting Started with Openbsd Device Driver Development
Getting started with OpenBSD device driver development Stefan Sperling <[email protected]> EuroBSDcon 2017 Clarifications (1/2) Courtesy of Jonathan Gray (jsg@): We don't want source code to firmware We want to be able to redistribute firmware freely Vendor drivers are often poorly written, we need to be able to write our own We want documentation on the hardware interfaces Source code is not documentation OpenBSD Device Drivers 2/46 Clarifications (2/2) I would like to add: Device driver code runs in our kernel Firmware code runs on a peripheral device, not in our kernel When we say \Binary Blobs" we are talking about closed-source device drivers, not firmware Firmware often runs with high privileges; use at your own risk If you do not want closed-source firmware, then don't buy and use hardware which needs it We are software developers, we do not build hardware We will not sign NDAs Please talk to hardware vendors and advocate for change; the current situation is very bad for free software OpenBSD Device Drivers 3/46 This talk is for ... somewhat competent C programmers who use OpenBSD and would like to use a device which lacks support so have an itch to scratch (enhance or write a driver) but are not sure where to start perhaps are not sure how the development process works and will research all further details themselves The idea for this talk came about during conversations I had at EuroBSDcon 2016. Common question: "How do I add support for my laptop's wifi device?" OpenBSD Device Drivers 4/46 Itches I have scratched.. -
Iocell Documentation Release 1.7.3
iocell Documentation Release 1.7.3 iocell Nov 23, 2018 Contents 1 Documentation: 3 1.1 Basic usage................................................3 1.2 Networking................................................6 1.3 Jail types.................................................8 1.4 Best practices............................................... 10 1.5 Advanced usage............................................. 11 1.6 How to create and use templates..................................... 15 1.7 Create a jail package!.......................................... 15 1.8 Create a Debian Squeeze jail (GNU/kFreeBSD)............................. 16 1.9 Known Issues............................................... 17 1.10 FAQ.................................................... 18 1.11 Indices and tables............................................ 19 i ii iocell Documentation, Release 1.7.3 iocell is a zero dependency drop in jail/container manager amalgamating some of the best features and technologies FreeBSD operating system has to offer. It is geared for ease of use with a simple and easy to understand command syntax. FEATURES: • Templates, clones, basejails, fully independent jails • Ease of use • Zero configuration files • Rapid thin provisioning within seconds • Automatic package installation • Virtual networking stacks (vnet) • Shared IP based jails (non vnet) • Resource limits (CPU, MEMORY, etc.) • Filesystem quotas and reservations • Dedicated ZFS datasets inside jails • Transparent ZFS snapshot management • Binary updates • Differential jail packaging • Export and import • And many more! Contents 1 iocell Documentation, Release 1.7.3 2 Contents CHAPTER 1 Documentation: 1.1 Basic usage This section is about basic use and is a suitable quick howto for newcomers. 1.1.1 Fetch a release The very first step with iocell is to fetch a RELEASE. By default iocell will attempt to fetch the host’s current RE- LEASE from the freebsd.org servers. Once the RELEASE bits are downloaded, the most recent patches are applied too.