On the Scalability and Security of Distributed Multiplayer Online Games
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -

Casual Gaming
Casual gaming KW Cheng [email protected] VU Amsterdam January 28, 2011 Abstract Common elements in the design of casual games include [TRE10]: Casual games have started to get a large player - Rules and goals must be clear. base in the last decade. In this paper we are - Players need to be able to quickly reach profi- going to have a basic look at the technology in- ciency. volved in creating casual games, common game - Casual gameplay adapts to a players life and mechanics, and the influence of social media on schedule. casual games. - Game concepts borrow familiar content and themes from life. 1 Introduction 1.2 History In this paper we are going to look at how ca- sual games are being created. This will include The start of casual gaming began in 1990 when useful tools, and commonly used programming Microsoft started bundling Windows Solitaire with languages. The main part of this paper will look Windows. Many people were still getting used at some game mechanics which are at the core to the idea of using a mouse to navigate through of casual games. We will pick out some popular a graphical user interface. Microsoft used Win- games and look at which mechanics are crucial to dows Solitaire to train people to use the mouse a successful gameplay. We will also look at the and to soothe people intimidated by the operat- influence of how social media introduced more ing system. [LEV08] The reason why Windows people to casual games. Solitaire is successful is because it is accessible, you do not have to install anything, because it 1.1 What are casual games comes with your operating system. -
Security in Online Gaming Bachelor Thesis Information Science
RADBOUD UNIVERSITY NIJMEGEN Security in online gaming Bachelor Thesis Information Science Rens van Summeren January 26, 2011 Online gaming has gone through an explosive growth in popularity during the last decade, and continues to grow at a great speed. With this growth in popularity and thus in the amount of players, the need for security also becomes increasingly clear. This thesis aims to provide a definition of security in online gaming, as well as security analysis for the various threats with examples and countermeasures. The goal is to help players and game developers assess online gaming security, and inform security experts about existing issues. CONTENTS 1 Introduction ................................................................................................................................... 1 Definition ............................................................................................................................... 1 Preface .................................................................................................................................. 1 2 Online Gaming ............................................................................................................................... 2 2.1 Why Look at the Security of Online Games? ................................................................... 2 2.2 Types of Online Games and Business Models ................................................................. 2 2.3 Massive Multiplayer Online Games ................................................................................ -

Comparative Study of Anti-Cheat Methods in Video Games
Comparative Study of Anti-cheat Methods in Video Games Samuli Lehtonen Master’s thesis UNIVERSITY OF HELSINKI Department of Computer Science Helsinki, March 7, 2020 HELSINGIN YLIOPISTO — HELSINGFORS UNIVERSITET — UNIVERSITY OF HELSINKI Tiedekunta — Fakultet — Faculty Laitos — Institution — Department Faculty of Science Department of Computer Science Tekijä — Författare — Author Samuli Lehtonen Työn nimi — Arbetets titel — Title Comparative Study of Anti-cheat Methods in Video Games Oppiaine — Läroämne — Subject Computer Science Työn laji — Arbetets art — Level Aika — Datum — Month and year Sivumäärä — Sidoantal — Number of pages Master’s thesis March 7, 2020 71 + 48 as appendices Tiivistelmä — Referat — Abstract Online gaming is more popular than ever and many video game companies are reliant on the cash flow generated by online games. If a video game company wants its game to be successful, the game has to be resilient against cheating, the presence of which can ruin an otherwise successful game. Cheating in a video game can bankrupt an entire company as the non-cheating players leave the game because of unscrupulous individuals using cheats to gain an unfair advantage. Cheating can also involve criminal activity where maliciously acquired in-game items are traded against real money online. Commercial cheat programs are sold on online black markets and are available even to players who have no deep technical knowledge. The widespread availability and easy accessibility of cheats compounds the issue. This thesis will categorize different anti-cheat techniques and give a brief history of anti-cheat starting from the early 1980s. The history section describes how the fight against online cheating began and how it has evolved over the years. -

KARELIA University of Applied Sciences Degree Programme in Business Information Technology
KARELIA University of Applied Sciences Degree Programme In Business Information Technology Elmeri Telimaa Hacking Detection in Unreal Engine 4 Thesis May 2021 THESIS February 2021 Business Information Technology Tikkarinne 9 80200 JOENSUU FINLAND + 358 13 260 600 (switchboard) Author (s) Elmeri Telimaa Title Hacking Detection in Unreal Engine 4 Commissioned by - Abstract The goal of the thesis is to find an integrated tool within Unreal Engine 4 for detecting and combating cheating, that is quick to implement in a project. To achieve this goal, a prototype game was created and speedhacked. A counter for this hack was then implemented. Cheating in online games results in worse experience for the other players playing against the cheater, who then take their business elsewhere. This has a negative impact on both the game developer’s reputation and revenue. The speedhack used manipulates time on a client, making the user move more than intended. The detection method included within Unreal Engine 4 compares the time sent by the client to the time of the server to determine if there is discrepancy in the values. Using these values, we can determine if the client is speedhacking. The used detection method detected the hack and kicked the offending client out of the server. The method is easy to implement in a new project. Language Pages 32 English Appendices 1 Pages of Appendices 1 Keywords Unreal Engine, cheating, online games, speedhack, anti-cheat OPINNÄYTETYÖ Helmikuu 2021 Tietojenkäsittelyn koulutusohjelma Tikkarinne 9 80200 JOENSUU +358 13 260 600 (vaihde) Tekijä(t) Elmeri Telimaa Nimeke Hacking Detection in Unreal Engine 4 Toimeksiantaja - Tiivistelmä Tämän opinnäytetön tavoitteena on löytää Unreal Engine 4-pelimoottoriin integroitu työkalu, jonka avulla voidaan havaita ja estää huijaamista. -

Cheating by Video Game Participants
Cheating by Video Game Participants J.R. Parker University of Calgary [email protected] Abstract In this paper, I explore the concept of cheating in the medium of the video game. Why do people do it? How does online cheating differ from offline? The existence of cheat codes seems to imply that cheating is rampant and even encouraged - or perhaps it’s just that the codes are poorly named. I also look at criminal activity in games, and at some ways to reduce cheating activities in online games. Introduction The word ‘cheat’ carries with it ancient societal passions. There is deception associated with the word, a lie, but more than that. There is a deliberation about cheating that makes it a worse lie than most, and there is an implication of doing someone harm in order to benefit oneself. Biblical cheats have died for their sin, and card cheats in the old West suffered a similar fate. Technology has changed the manner in which people can cheat, and has created many new ways to do it. So-called computer crime, identity theft, phishing, and other modern ways of cheating are enabled by the prevalent use of digital technology in many areas of society. Of course, the activities listed above are actually crimes; yet non-criminal cheating takes place too. Plagiarism is now very easy because of search engines and the Internet (easier to detect, too!). People misrepresent their identity on the Web with greater frequency, sometimes in self-defense. Cheating at games has traditionally been held in low regard because people that you play with are often friends. -

Security Design in Online Games
Security Design in Online Games Jeff Yan Department of Computer Science and Engineering The Chinese University of Hong Kong Shatin, N.T., Hong Kong Email: [email protected] Abstract and they charge a user when he logs in to play on their servers. Thus, the traditional headache of copy protection The emergence of online games has fundamentally changed can now be forgotten. Other problems have replaced it, such security requirements for computer games, which previ- as password security, payment security and the availability ously were largely concerned with copy protection. In this of systems that host online games. But these are relatively paper, we examine how new security requirements impact well understood as they are shared by other networked e- the design of online games by using online Bridge, a sim- commerce applications. ple client-server game, as our case study. We argue that se- A new security concern in games is online cheating [17, curity is emerging as an inherent design issue for online 22]. Cheating was very popular in single player console or games, after graphics and artificial intelligence, which have PC games. For example, it has been common for a player become important issues of the design of most games for to make game missions easier by using cheating tools. For decades. The most important new security concern in on- single-player games, cheaters were cheating the computer line game design is fairness enforcement, and most secu- and nobody else would care. For online games, however, rity mechanisms all contribute to a single objective, namely, cheaters are now cheating human players sitting elsewhere making the play fair for each user. -

Joël A. Lamotte Born: 1983 – French Tel: 0(+33)6.52.26.61.58 Email: [email protected]
Joël A. Lamotte Born: 1983 – French Tel: 0(+33)6.52.26.61.58 email: [email protected] PROFESSIONAL EXPERIENCE Independent - Lille (France) (Since July 2012) Projects: Working on NetRush (RTS game) and Art Of Sequence (OSS digital story-telling tools) Developed a client-server multi-process concurrent-tasks game-specific engine for the needs of NetRush (RTS game). Learned a lot about concurrency (using C++) while doing so, using the practical case of this game. Designed NetRush and several other smaller game prototypes. Developed and published an interpreter for AOSL in JavaScript as a partial Proof of Concept of Art of Sequence projects. Development on Art Of Sequence tools are still going on. Kayac - Kamakura (Japan) Creator (2012, 4 months) Projects: Make Games (Farmer Carrots Zombies , unreleased rogue-like prototype) Provided international game development expertise and point of view to the company that wished to sell games worldwide. Challenged to develop an iOS game in no time. It took us 2 weeks to produce FCZ, I made all the code and sound design and half of the game design. However, pressed by the time we were not able to do better. Releasing it publicly what not my decision but I did my best to make it enjoyable. Learned iOS (ObjectiveC/C++) development, Japanese keyboard, MacOSX use and Cocos2D-X (which I patched and provided back to the devs) in a very short time. Proposed 7 game concepts to work on next (after FCZ) which have all been approved, the game development team being confident in my skills, they suggested that I should chose the project myself. -

Lumin Software End User License Agreement Version 0.96
LUMIN SOFTWARE END USER LICENSE AGREEMENT VERSION 0.96 IMPORTANT: PLEASE READ THIS LUMIN SOFTWARE END USER LICENSE AGREEMENT (THIS “LICENSE”) CAREFULLY BEFORE USING YOUR MAGIC LEAP ONE (“DEVICE”). THE TERMS OF THIS LICENSE ARE ALSO AVAILABLE ON MAGIC LEAP’S WEBSITE LOCATED AT WWW.MAGICLEAP.COM/LEGAL. THIS LICENSE DESCRIBES THE LIMITED RIGHTS YOU HAVE TO USE THE LUMIN SOFTWARE ON YOUR DEVICE AND IS A BINDING CONTRACT BETWEEN YOU AND MAGIC LEAP, INC. ("MAGIC LEAP"). BY CLICKING “ACCEPT”, OR BY INSTALLING OR USING THE LUMIN SOFTWARE, YOU REPRESENT YOU HAVE READ, UNDERSTAND, AND AGREE TO BE BOUND BY THE TERMS AND CONDITIONS OF THIS LICENSE. IF YOU DO NOT AGREE TO THIS LICENSE, INCLUDING THE MANDATORY ARBITRATION AND CLASS ACTION WAIVER REFERENCED IN SECTION 10, THEN YOU MAY NOT CONTINUE WITH THE INSTALLATION OR USE OF THE LUMIN SOFTWARE. IN SUCH EVENT, YOU MAY RETURN THE DEVICE WITHIN THE RETURN PERIOD IN ACCORDANCE WITH MAGIC LEAP’S RETURN POLICY LOCATED AT WWW.MAGICLEAP.COM/WARRANTY. NOTICES REGARDING OSS (AS DEFINED BELOW) AND OTHER ITEMS ARE ADDRESSED AT THE END OF THIS LICENSE. 1. LICENSE TO LUMIN SOFTWARE AND UPDATES 1.1 This License covers your use of all Lumin Software, unless any particular Lumin Software component or application is accompanied by separate terms. In that case, the separate terms will solely govern the applicable Lumin Software component or application. If the separate terms do not accompany the Lumin Software component or application, they may be found in the Lumin Software’s NOTICES file. “Lumin Software” means individually or collectively: (a) the Lumin OS software on your Device; (b) all applications that are pre-installed on your Device; (c) certain OSS (defined in Section 4 below); and (d) all related documentation. -

Multiplayer Game Programming: Architecting Networked Games
ptg16606381 Multiplayer Game Programming ptg16606381 The Addison-Wesley Game Design and Development Series Visit informit.com/series/gamedesign for a complete list of available publications. ptg16606381 Essential References for Game Designers and Developers hese practical guides, written by distinguished professors and industry gurus, Tcover basic tenets of game design and development using a straightforward, common-sense approach. The books encourage readers to try things on their own and think for themselves, making it easier for anyone to learn how to design and develop digital games for both computers and mobile devices. Make sure to connect with us! informit.com/socialconnect Multiplayer Game Programming Architecting Networked Games ptg16606381 Joshua Glazer Sanjay Madhav New York • Boston • Indianapolis • San Francisco Toronto • Montreal • London • Munich • Paris • Madrid Cape Town • Sydney • Tokyo • Singapore • Mexico City Many of the designations used by manufacturers and sellers to distinguish their products Editor-in-Chief are claimed as trademarks. Where those designations appear in this book, and the Mark Taub publisher was aware of a trademark claim, the designations have been printed with initial capital letters or in all capitals Acquisitions Editor Laura Lewin The authors and publisher have taken care in the preparation of this book, but make no expressed or implied warranty of any kind and assume no responsibility for errors or Development Editor omissions. No liability is assumed for incidental or consequential damages in connection Michael Thurston with or arising out of the use of the information or programs contained herein. Managing Editor For information about buying this title in bulk quantities, or for special sales opportunities Kristy Hart (which may include electronic versions; custom cover designs; and content particular to your business, training goals, marketing focus, or branding interests), please contact our Project Editor corporate sales department at [email protected] or (800) 382-3419. -
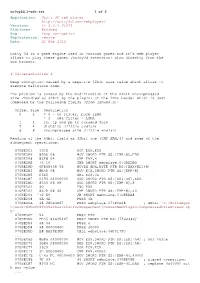
Application: Unity 3D Web Player
unity3d_1-adv.txt 1 of 2 Application: Unity 3D web player http://unity3d.com/webplayer/ Versions: <= 3.2.0.61061 Platforms: Windows Bug: heap corruption Exploitation: remote Date: 21 Feb 2012 Unity 3d is a game engine used in various games and it’s web player allows to play these games (unity3d extension) also directly from the web browser. # Vulnerabilities # Heap corruption caused by a negative 32bit size value which allows to execute malicious code. The problem is caused by the modification of the 64bit uncompressed size (handled as 32bit by the plugin) of the lzma header which is just composed by the following fields (from lzma86.h): Offset Size Description 0 1 = 0 - no filter, pure LZMA = 1 - x86 filter + LZMA 1 1 lc, lp and pb in encoded form 2 4 dictSize (little endian) 6 8 uncompressed size (little endian) Reading of the 64bit field as 32bit one (CMP EAX,4) and some of the subsequent operations: 070BEDA3 33C0 XOR EAX,EAX 070BEDA5 895D 08 MOV DWORD PTR SS:[EBP+8],EBX 070BEDA8 83F8 04 CMP EAX,4 070BEDAB 73 10 JNB SHORT webplaye.070BEDBD 070BEDAD 0FB65438 05 MOVZX EDX,BYTE PTR DS:[EAX+EDI+5] 070BEDB2 8B4D 08 MOV ECX,DWORD PTR SS:[EBP+8] 070BEDB5 D3E2 SHL EDX,CL 070BEDB7 0196 A4000000 ADD DWORD PTR DS:[ESI+A4],EDX 070BEDBD 8345 08 08 ADD DWORD PTR SS:[EBP+8],8 070BEDC1 40 INC EAX 070BEDC2 837D 08 40 CMP DWORD PTR SS:[EBP+8],40 070BEDC6 ^72 E0 JB SHORT webplaye.070BEDA8 070BEDC8 6A 4A PUSH 4A 070BEDCA 68 280A4B07 PUSH webplaye.074B0A28 ; ASCII "C:/BuildAgen t/work/b0bcff80449a48aa/PlatformDependent/CommonWebPlugin/CompressedFileStream.cp p" 070BEDCF 53 PUSH EBX 070BEDD0 FF35 84635407 PUSH DWORD PTR DS:[7546384] 070BEDD6 6A 04 PUSH 4 070BEDD8 68 00000400 PUSH 40000 070BEDDD E8 BA29E4FF CALL webplaye.06F0179C .. -

434556 Master Thesis Final
Levelling Up Leadership An Analysis on the Development of Leadership Skills through Competitive Gaming Name Alan Byssing Lafi _______________ Student ID 8452 Name Anders Rud Liltorp _______________ Student ID 85717 Master’s Thesis (LA) Supervisor: Helle Zinner Henriksen Copenhagen Business School MSc in Business Administration & Information Systems Submission Deadline: May 15th, 2018 at 16:00 pm Number of Characters: 264.607 Number of Pages: 118 Abstract As gaming is rapidly becoming increasingly popular, the need for research on the effects and use of gaming as a tool for learning and personal development is increasing. Additionally, the need for leaders who feel at home in the digital world is rising, as technology is becoming an increasingly important factor in almost any business. Therefore, the purpose of this thesis is to investigate if participating in the in-game management of a competitive gaming team, can improve an individual’s leadership skills. The thesis adopts and interpretivist philosophy in order to understand the differences between humans as social actors. The research approach is deductive as the existing knowledge on leadership is integrated and summarized through a literature review, which is then used to create a framework of leadership skills. The framework is then tested by interviewing competitive video game players and analyzing the data they provided. The respondents were found by using a variety of websites that rank teams and players, in order to guarantee that the respondents were playing on a sufficient level. Based on the collected data, models were created to visualize and compare the differences in leadership skills across individuals, game genres and in relation to career length.