Introducing Windows 2000 Security: Features and Management
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
NTFS • Windows Reinstallation – Bypass ACL • Administrators Privilege – Bypass Ownership
Windows Encrypting File System Motivation • Laptops are very integrated in enterprises… • Stolen/lost computers loaded with confidential/business data • Data Privacy Issues • Offline Access – Bypass NTFS • Windows reinstallation – Bypass ACL • Administrators privilege – Bypass Ownership www.winitor.com 01 March 2010 Windows Encrypting File System Mechanism • Principle • A random - unique - symmetric key encrypts the data • An asymmetric key encrypts the symmetric key used to encrypt the data • Combination of two algorithms • Use their strengths • Minimize their weaknesses • Results • Increased performance • Increased security Asymetric Symetric Data www.winitor.com 01 March 2010 Windows Encrypting File System Characteristics • Confortable • Applying encryption is just a matter of assigning a file attribute www.winitor.com 01 March 2010 Windows Encrypting File System Characteristics • Transparent • Integrated into the operating system • Transparent to (valid) users/applications Application Win32 Crypto Engine NTFS EFS &.[ßl}d.,*.c§4 $5%2=h#<.. www.winitor.com 01 March 2010 Windows Encrypting File System Characteristics • Flexible • Supported at different scopes • File, Directory, Drive (Vista?) • Files can be shared between any number of users • Files can be stored anywhere • local, remote, WebDav • Files can be offline • Secure • Encryption and Decryption occur in kernel mode • Keys are never paged • Usage of standardized cryptography services www.winitor.com 01 March 2010 Windows Encrypting File System Availibility • At the GUI, the availibility -

Active @ UNDELETE Users Guide | TOC | 2
Active @ UNDELETE Users Guide | TOC | 2 Contents Legal Statement..................................................................................................4 Active@ UNDELETE Overview............................................................................. 5 Getting Started with Active@ UNDELETE........................................................... 6 Active@ UNDELETE Views And Windows......................................................................................6 Recovery Explorer View.................................................................................................... 7 Logical Drive Scan Result View.......................................................................................... 7 Physical Device Scan View................................................................................................ 8 Search Results View........................................................................................................10 Application Log...............................................................................................................11 Welcome View................................................................................................................11 Using Active@ UNDELETE Overview................................................................. 13 Recover deleted Files and Folders.............................................................................................. 14 Scan a Volume (Logical Drive) for deleted files..................................................................15 -

Copyrighted Material
Index Note to the Reader: Throughout this index boldfaced page numbers indicate primary discussions of a topic. Italicized page numbers indicate illustrations. IUSR_computername account, 274–275 Numbers disabling, 61 mapping certificates to, 283–286 3DES, 125–126, 416, 494 user accounts, configuring for 802.1x standard (IEEE), 181–184, 494 delegation, 46 authentication for, 182 ACEs (Access Control Entries) combining VPNs with, 190 authentication for clients, 494 802.11a standard (IEEE), 494 in Discretionary Access Control List, 7 vs. 802.11b, 170 Active Directory (AD), 3, 494 802.11b standard (IEEE), 494 assigning GPO to container in, 28 for certificate store, 404 Configuration container for certificate templates, 360 A mapping certificates to accounts, 283–286 Access Control Entries (ACEs), 494 in mixed mode, 324 in Discretionary Access Control List, 7 publishing certificates through, 404–409 Access Control List (ACL), 494 in child domain, 406–409 Access Control Settings dialog box, 16 from standalone online CA, 404–406 Auditing tab, 16, 440 to view published certificates and CRLs, “Access Is Denied” error message, 420 358–359 access point, 494. See also wireless access Active Directory domain controller point (WAP) client security to traffic, 226–229 access token, 260, 494 testing, 227–229 account lockout policy, in security Active Directory domains templates, 9 Properties dialog box, General tab, 228 account logon events, tracking, 15, 445 trust relationships, 271–273, 272 account management events, tracking, 15, Active Directory object, auditing, 18 445–446 Active Directory Properties dialog box, 228 Account Policies Active Directory Sites and Services (ADSS), security template configuration, 12, 5, 494 12–14, 13 configuration, 407–408 in security templates, 9 Active Directory Users and Computers (ADUC), accountability trail, 14 COPYRIGHTED5, MATERIAL494 accounts Active Server Pages (ASP), SUS and, 111 Administrator account, renaming, 55, 56 AD. -
Jim Allchin on Longhorn, Winfs, 64-Bit and Beyond Page 34 Jim
0805red_cover.v5 7/19/05 2:57 PM Page 1 4 Scripting Solutions to Simplify Your Life Page 28 AUGUST 2005 WWW.REDMONDMAG.COM MrMr WindowsWindows Jim Allchin on Longhorn, WinFS, 64-Bit and Beyond Page 34 > $5.95 05 • AUGUST Make Room for Linux Apps Page 43 25274 867 27 Active Directory Design Disasters Page 49 71 Project1 6/16/05 12:36 PM Page 1 Exchange Server stores & PSTs driving you crazy? Only $399 for 50 mailboxes; $1499 for unlimited mailboxes! Archive all mail to SQL and save 80% storage space! Email archiving solution for internal and external email Download your FREE trial from www.gfi.com/rma Project1 6/16/05 12:37 PM Page 2 Get your FREE trial version of GFI MailArchiver for Exchange today! GFI MailArchiver for Exchange is an easy-to-use email archiving solution that enables you to archive all internal and external mail into a single SQL database. Now you can provide users with easy, centralized access to past email via a web-based search interface and easily fulfill regulatory requirements (such as the Sarbanes-Oxley Act). GFI MailArchiver leverages the journaling feature of Exchange Server 2000/2003, providing unparalleled scalability and reliability at a competitive cost. GFI MailArchiver for Exchange features Provide end-users with a single web-based location in which to search all their past email Increase Exchange performance and ease backup and restoration End PST hell by storing email in SQL format Significantly reduce storage requirements for email by up to 80% Comply with Sarbanes-Oxley, SEC and other regulations. -

Encrypting File System
SVEUČILIŠTE U ZAGREBU FAKULTET ELEKTROTEHNIKE I RAČUNARSTVA Seminarski rad iz kolegija „Računalna forenzika“ Encrypting File System Luka Škorić Zagreb, siječanj, 2018. Sadržaj 1. Uvod ................................................................................................................................................ 1 2. NTFS............................................................................................................................................... 2 3. Karakteristike Encrypting File System-a ................................................................................... 4 3.1. Enkripcijski algoritmi ............................................................................................................. 5 3.2. Način rada .............................................................................................................................. 6 3.3. Nedostatci EFS-a .................................................................................................................. 8 4. Zaključak ...................................................................................................................................... 10 5. Literatura ...................................................................................................................................... 11 1. Uvod Enkripcija tvrdog diska predstavlja proces zaštite podataka pretvaranjem podataka u nečitki kod, što kao cilj ima zaštitu istih podataka od nedozvoljenog pristupa. Filesystem - level encryption, često nazvan i file/folder -

Windows Poster 20-12-2013 V3
Microsoft® Discover the Open Specifications technical documents you need for your interoperability solutions. To obtain these technical documents, go to the Open Specifications Interactive Tiles: open specifications poster © 2012-2014 Microsoft Corporation. All rights reserved. http://msdn.microsoft.com/openspecifications/jj128107 Component Object Model (COM+) Technical Documentation Technical Documentation Presentation Layer Services Technical Documentation Component Object Model Plus (COM+) Event System Protocol Active Directory Protocols Overview Open Data Protocol (OData) Transport Layer Security (TLS) Profile Windows System Overview Component Object Model Plus (COM+) Protocol Active Directory Lightweight Directory Services Schema WCF-Based Encrypted Server Administration and Notification Protocol Session Layer Services Windows Protocols Overview Component Object Model Plus (COM+) Queued Components Protocol Active Directory Schema Attributes A-L Distributed Component Object Model (DCOM) Remote Protocol Windows Overview Application Component Object Model Plus (COM+) Remote Administration Protocol Directory Active Directory Schema Attributes M General HomeGroup Protocol Supplemental Shared Abstract Data Model Elements Component Object Model Plus (COM+) Tracker Service Protocol Active Directory Schema Attributes N-Z Peer Name Resolution Protocol (PNRP) Version 4.0 Windows Data Types Services General Application Services Services Active Directory Schema Classes Services Peer-to-Peer Graphing Protocol Documents Windows Error Codes ASP.NET -

Disk Management (4 Min) When We Want to Install a Hard Drive in Our System We're Going to Need to Make That Hard Drive Either a Basic Disk Or a Dynamic Disk
Video – Disk Management (4 min) When we want to install a hard drive in our system we're going to need to make that hard drive either a basic disk or a dynamic disk. A basic disk, which is the default, contains primary and extended partitions as well as logical drives. A basic disk is limited to four partitions. The Windows operating system needs to be installed onto a basic disk. After it's installed the basic disk can then be converted to a dynamic disk. Primary partition. The primary partition contains the operating system. There can be up to four primary partitions per hard drive and a primary partition cannot be subdivided into smaller sections. A primary partition can also be marked as the active partition. The operating system uses the active partition to boot the computer. Only one primary partition per disk can be marked as active. In most cases, the C: drive is the active partition and contains the boot and system files. Meaning the MBR or Master Boot Record Partition Table. Newer systems that use EFI instead of BIOS are using the GPT or GUID partition table. If you're using the GPT instead of the MBR partition table you can have more than four primary partitions on a disk. An extended partition. There can only be one extended partition per hard drive. Once again, primary partitions, active partitions and extended partitions are all part of a basic disk. An extended partition cannot hold the operating system, but it can be subdivided into smaller sections called logical drives. -
![[MS-EFSR]: Encrypting File System Remote (EFSRPC) Protocol](https://docslib.b-cdn.net/cover/9728/ms-efsr-encrypting-file-system-remote-efsrpc-protocol-979728.webp)
[MS-EFSR]: Encrypting File System Remote (EFSRPC) Protocol
[MS-EFSR]: Encrypting File System Remote (EFSRPC) Protocol Intellectual Property Rights Notice for Open Specifications Documentation . Technical Documentation. Microsoft publishes Open Specifications documentation for protocols, file formats, languages, standards as well as overviews of the interaction among each of these technologies. Copyrights. This documentation is covered by Microsoft copyrights. Regardless of any other terms that are contained in the terms of use for the Microsoft website that hosts this documentation, you may make copies of it in order to develop implementations of the technologies described in the Open Specifications and may distribute portions of it in your implementations using these technologies or your documentation as necessary to properly document the implementation. You may also distribute in your implementation, with or without modification, any schema, IDL's, or code samples that are included in the documentation. This permission also applies to any documents that are referenced in the Open Specifications. No Trade Secrets. Microsoft does not claim any trade secret rights in this documentation. Patents. Microsoft has patents that may cover your implementations of the technologies described in the Open Specifications. Neither this notice nor Microsoft's delivery of the documentation grants any licenses under those or any other Microsoft patents. However, a given Open Specification may be covered by Microsoft Open Specification Promise or the Community Promise. If you would prefer a written license, or if the technologies described in the Open Specifications are not covered by the Open Specifications Promise or Community Promise, as applicable, patent licenses are available by contacting [email protected]. Trademarks. The names of companies and products contained in this documentation may be covered by trademarks or similar intellectual property rights. -
Advantages and Disadvantages of EFS and Effective Recovery of Encrypted Data Whitepaper
advantages and disadvantages of efs and effective recovery of encrypted data whitepaper Copyright (c) 2007 ElcomSoft Co.Ltd. Contents What is eFs? 3 eFs advantages and disadvantages 4 Data can be lost for good 5 how can one lose access to eFS-encrypted data? what is the eFS recovery agent? What to do in case of system failure? 7 possible actions to take Data decryption scheme Advanced eFs Data Recovery 8 About elcomsoft 10 AdvAntAges And disAdvAntAges of efs whitepaper 2 WhAt is eFs? One of the innovations in the Microsoft Windows 2000 and the NTFS 5.0 file system was the Encrypting File System (EFS) technology, which is designed to quickly encrypt files on the com- puter hard drive. NTFS by itself has built-in protection. However, as is frequently the case, it very quickly required additional security. The reason was the wide-spread use of NTFSDos-type utilities, which made it easy to circumvent the NTFS security system, gaining access to it through DOS, thus ignoring the set access rights. The EFS system uses both public and private key encryption and CryptoAPI architecture. EFS can use any symmetrical file encryption algorithm from the following list: Microsoft Windows 2000 used DESX, Windows XP used 3DES, and Windows XP SP1, 2003 and the new Windows Vista use AES. File encryption does not require the user to execute any preliminary operations. During the first encryption of the file, an encryption certificate and a private key are automatically issued for the user. One of the distinguishing convenient features of EFS is that the files remain encrypted when they are transferred to a different folder or to a different NTFS drive. -
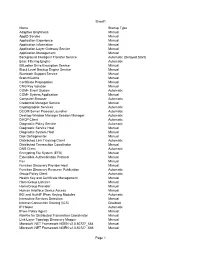
Tweakhound, Windows 7 Beta Default Services
Sheet1 Name Startup Type Adaptive Brightness Manual AppID Service Manual Application Experience Manual Application Information Manual Application Layer Gateway Service Manual Application Management Manual Background Intelligent Transfer Service Automatic (Delayed Start) Base Filtering Engine Automatic BitLocker Drive Encryption Service Manual Block Level Backup Engine Service Manual Bluetooth Support Service Manual BranchCache Manual Certificate Propagation Manual CNG Key Isolation Manual COM+ Event System Automatic COM+ System Application Manual Computer Browser Automatic Credential Manager Service Manual Cryptographic Services Automatic DCOM Server Process Launcher Automatic Desktop Window Manager Session Manager Automatic DHCP Client Automatic Diagnostic Policy Service Automatic Diagnostic Service Host Manual Diagnostic System Host Manual Disk Defragmenter Manual Distributed Link Tracking Client Automatic Distributed Transaction Coordinator Manual DNS Client Automatic Encrypting File System (EFS) Manual Extensible Authentication Protocol Manual Fax Manual Function Discovery Provider Host Manual Function Discovery Resource Publication Automatic Group Policy Client Automatic Health Key and Certificate Management Manual HomeGroup Listener Manual HomeGroup Provider Manual Human Interface Device Access Manual IKE and AuthIP IPsec Keying Modules Automatic Interactive Services Detection Manual Internet Connection Sharing (ICS) Disabled IP Helper Automatic IPsec Policy Agent Manual KtmRm for Distributed Transaction Coordinator Manual Link-Layer -
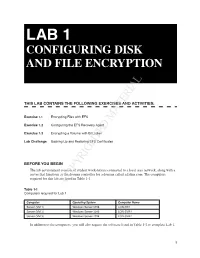
Configuring Disk and File Encryption
LAB 1 CONFIGURING DISK AND FILE ENCRYPTION THIS LAB CONTAINS THE FOLLOWING EXERCISES AND ACTIVITIES: Exercise 1.1 Encrypting Files with EFS Exercise 1.2 Configuring the EFS Recovery Agent Exercise 1.3 Encrypting a Volume with BitLocker Lab Challenge Backing Up and Restoring EFS Certificates BEFORE YOU BEGIN The lab environment consists of student workstations connected to a local area network, along with a server that functions as the domain controller for a domain called adatum.com. The computers required for this lab are listedCOPYRIGHTED in Table 1-1. MATERIAL Table 1-1 Computers required for Lab 1 Computer Operating System Computer Name Server (VM 1) Windows Server 2016 LON-DC1 Server (VM 2) Windows Server 2016 LON-SVR1 Server (VM 3) Windows Server 2016 LON-SVR2 In addition to the computers, you will also require the software listed in Table 1-2 to complete Lab 1. 1 744_Lab01_WS.indd 1 7/26/18 3:58 PM 2 70-744: Securing Windows Server 2016 Table 1-2 Software required for Lab 1 Software Location Lab 1 student worksheet Lab01_worksheet.docx (provided by instructor) Working with Lab Worksheets Each lab in this manual requires that you answer questions, shoot screen shots, and perform other activities that you will document in a worksheet named for the lab, such as Lab01_worksheet.docx. You will find these worksheets on the book companion site. It is recommended that you use a USB flash drive to store your worksheets, so you can submit them to your instructor for review. As you perform the exercises in each lab, open the appropriate worksheet file using Word, fill in the required information, and then save the file to your flash drive. -
Windows Powershell Best Practices Windows Powershell Best Practices
Windows PowerShell Best Practices Windows PowerShell Best Practices Expert recommendations, pragmatically applied Automate system administration using Windows PowerShell best practices—and optimize your operational efficiency. With this About the Author practical guide, Windows PowerShell expert and instructor Ed Ed Wilson, MCSE, CISSP, is a well-known Wilson delivers field-tested tips, real-world examples, and candid scripting expert and author of “Hey Windows Scripting Guy!”—one of the most popular advice culled from administrators across a range of business and blogs on Microsoft TechNet. He’s written technical scenarios. If you’re an IT professional with Windows several books on Windows scripting PowerShell experience, this book is ideal. for Microsoft Press, including Windows PowerShell 2.0 Best Practices and Windows PowerShell Scripting Guide. Discover how to: PowerShell • Use Windows PowerShell to automate Active Directory tasks • Explore available WMI classes and methods with CIM cmdlets • Identify and track scripting opportunities to avoid duplication • Use functions to encapsulate business logic and reuse code • Design your script’s best input method and output destination • Test scripts by checking their syntax and performance • Choose the most suitable method for running remote commands • Manage software services with Desired State Configuration Wilson BEST PRACTICES microsoft.com/mspress ISBN 978-0-7356-6649-8 U.S.A. $59.99 55999 Canada $68.99 [Recommended] 9 780735 666498 Operating Systems/Windows Server Celebrating 30 years! Ed Wilson 666498_Win_PowerShell_Best_Practices.indd 1 4/11/14 10:30 AM Windows PowerShell Best Practices Ed Wilson 666498_book.indb 1 12/20/13 10:50 AM Published with the authorization of Microsoft Corporation by: O’Reilly Media, Inc.