Jim Allchin on Longhorn, Winfs, 64-Bit and Beyond Page 34 Jim
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The NT Insider May-June 2016
; The commandments of x64 assembly: ; ; 1. Thou Shalt Not Write Inline Assembly ; 2. Thou Shalt Generate Unwind Data ; 3. Thou Shalt Comment Each Line of Assembly ; include macamd64.inc ; ; External C function to read an article ; ; NTSTATUS ; TheNTInsiderReadSingleArticle( ; PCHAR ArticleDescription, ; ULONG_PTR PageNumber, ; ); ; EXTERN TheNTInsiderReadSingleArticle:PROC .DATA PeterPontificates BYTE "COMPUTER SCIENCE EDUCATION? (YUP, STILL SUCKS)", 0 NewWaysToConnect BYTE "INTRODUCTION TO SIMPLE PERIPHERAL BUS DEVICES AND DRIVERS", 0 TipsForUsingIoTargets BYTE "A FEW RULES TO MAKE YOUR USE OF I/O TARGETS SIMPLE", 0 TodayInDriverSigning BYTE "COLOR ME CONFUSED (STILL. AGAIN.)", 0 AnalystsPerspective BYTE "MY DRIVER PASSES DRIVER VERIFIER! (OR DOES IT…)", 0 ByeByeCoInstallers BYTE "SURPRISE? NEW VERSIONS OF WDF NO LONGER SUPPORTED DOWNLEVEL", 0 .CODE NESTED_ENTRY TheNTInsiderReadEntireIssue, _TEXT save_reg rcx, 8h ; Home RCX save_reg rdx, 10h ; Home RDX save_reg r8, 18h ; Home R8 save_reg r9, 20h ; Home R9 alloc_stack 20h ; Make home space for TheNTInsiderReadSingleArticle END_PROLOGUE ; We are done manipulating the stack, so emit the ; appropriate unwind stuff lea rcx, [PeterPontificates] ; We're about to read the first article mov rdx, 4 ; Put page number in RDX. I realize this comment ; isn't useful, but I'm supposed to comment every ; line... call TheNTInsiderReadSingleArticle ; Read the article! test eax, eax ; Returns an NTSTATUS, so check SF js Exit ; If it's set there's an error and we need to leave lea rcx, [NewWaysToConnect] ; Time for the second article! mov rdx, 6 ; Do what I did last time call TheNTInsiderReadSingleArticle ; Read the next article! test eax, eax ; Testin'... js Exit ; And jumpin'... A publication of OSR Open Systems Resources, Inc. Resources, Systems Open OSR of A publication lea rcx, [TipsForUsingIoTargts] ; Let's read another article! mov rdx, 8 ; TODO: Learn to write a MASM loop.. -
NTFS • Windows Reinstallation – Bypass ACL • Administrators Privilege – Bypass Ownership
Windows Encrypting File System Motivation • Laptops are very integrated in enterprises… • Stolen/lost computers loaded with confidential/business data • Data Privacy Issues • Offline Access – Bypass NTFS • Windows reinstallation – Bypass ACL • Administrators privilege – Bypass Ownership www.winitor.com 01 March 2010 Windows Encrypting File System Mechanism • Principle • A random - unique - symmetric key encrypts the data • An asymmetric key encrypts the symmetric key used to encrypt the data • Combination of two algorithms • Use their strengths • Minimize their weaknesses • Results • Increased performance • Increased security Asymetric Symetric Data www.winitor.com 01 March 2010 Windows Encrypting File System Characteristics • Confortable • Applying encryption is just a matter of assigning a file attribute www.winitor.com 01 March 2010 Windows Encrypting File System Characteristics • Transparent • Integrated into the operating system • Transparent to (valid) users/applications Application Win32 Crypto Engine NTFS EFS &.[ßl}d.,*.c§4 $5%2=h#<.. www.winitor.com 01 March 2010 Windows Encrypting File System Characteristics • Flexible • Supported at different scopes • File, Directory, Drive (Vista?) • Files can be shared between any number of users • Files can be stored anywhere • local, remote, WebDav • Files can be offline • Secure • Encryption and Decryption occur in kernel mode • Keys are never paged • Usage of standardized cryptography services www.winitor.com 01 March 2010 Windows Encrypting File System Availibility • At the GUI, the availibility -

Active@ UNDELETE Documentation
Active @ UNDELETE Users Guide | Contents | 2 Contents Legal Statement.........................................................................................................5 Active@ UNDELETE Overview............................................................................. 6 Getting Started with Active@ UNDELETE.......................................................... 7 Active@ UNDELETE Views And Windows...................................................................................................... 7 Recovery Explorer View.......................................................................................................................... 8 Logical Drive Scan Result View..............................................................................................................9 Physical Device Scan View......................................................................................................................9 Search Results View...............................................................................................................................11 File Organizer view................................................................................................................................ 12 Application Log...................................................................................................................................... 13 Welcome View........................................................................................................................................14 Using -

RAID, LVM, WSS, Verschlüsselung)
Hochschule Wismar University of Applied Sciences Technology, Business and Design Fakultät für Ingenieurwissenschaften, Bereich EuI Projektarbeit Aufbereitung besonderer Speicherkonfigurationen als analysefähiges Material (RAID, LVM, WSS, Verschlüsselung) Eingereicht am: 6. Juli 2019 von: Melanie Wetzig Sven Lötgering Tom Gertenbach Stefan Depping Inhaltsverzeichnis Inhaltsverzeichnis 1 Vorüberlegungen4 1.1 Motivation und Zielstellung.......................4 1.2 Anforderung an den Ermittlungsprozess.................4 1.3 Einordnung in Ermittlungsprozess....................6 1.4 Write-Blocker...............................6 1.5 Software..................................7 1.5.1 Rohdatenformat (RAW).....................7 1.5.2 Expert Witness Format (EWF).................8 1.5.3 Advanced Forensic Format (AFF)................8 1.5.4 Xmount..............................8 2 Rechtliche Betrachtung9 2.1 Einleitung.................................9 2.2 Private Ermittlungen........................... 10 2.3 Behördliche Ermittlungen........................ 11 2.4 Zusammenfassung............................. 11 3 Speichermedien 13 3.1 Einleitung................................. 13 3.2 Magnetspeicher.............................. 13 3.2.1 Speicherung auf einer HDD................... 14 3.2.2 Löschen von Daten auf einer HDD............... 15 3.2.3 Forensische Relevanz....................... 15 3.3 Flash-Speicher............................... 15 3.3.1 Speicherung auf einer Solid-State-Drive (SSD)......... 16 3.3.2 Löschen von Daten auf einer SSD............... -

I Hate Comic Sans!
I HATE COMIC SANS! It’s Overused It’s Badly used It’s not serious typography Used Incorrectly by Hospitals, Businesses, and Banks, etc. ? “A Computer on Every Desk, In every Home, Running Microsoft Software” the Microsoft Mission statement c. 1980 Computers were expensive Marketed mostly to businesses Expensive Dial up internet Off peak use only on AOL (after 6pm-6am) Screen savers were products Microsoft Scenes After Dark (flying toasters) CD-ROM ‘multimedia’ software MS Beethoven, Schubert, Stravinsky, Strauss MS Ultimate Frank Lloyd Wright MS Wine Guide, MS Dogs, MS Complete Gardening Microsoft Home (1993 Consumer Division) •Goal: To create software for Mums, Dads, and kids Product titles: •Microsoft Flight Simulator* •Microsoft Encarta* •Microsoft Scenes* •Microsoft Creative Writer Wall Street Journal: Aug 24, 1995 • Home computers in US home electronic stores for about $1000 •First affordable computers available • with Windows 95 installed • MSN Online network released to compete with America Online (AOL), Compuserve, Genie etc. • First Generation Internet Explorer released in the Plus Pack for Windows 95 ‘Utopia’ Project Lead: Melinda French (future Mrs. BillG) UI used a simple method of Launching Applications Similar to Hypercard stacks of the late 1980s For children and novice users Release: to coincide with Win95 and 1995 Christmas Season Rover talks in Times New Roman 1994 Microsoft Bob DC Comics: DC Comics The Dark Knight Returns Watchmen DC COMICS: WATCHMEN 1986-87 ILLUSTRATOR/LETTERER : DAVE GIBBONS • -
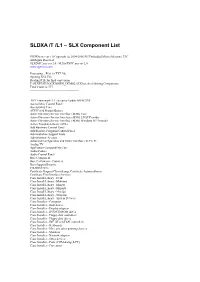
SLDXA /T /L1 – SLX Component List
SLDXA /T /L1 – SLX Component List SLDXA.exe ver 1.0 Copyright (c) 2004-2006 SJJ Embedded Micro Solutions, LLC All Rights Reserved SLXDiffC.exe ver 2.0 / SLXtoTXTC.exe ver 2.0 www.sjjmicro.com Processing... File1 to TXT file. Opening XSL File Reading RTF for final conversion F:\SLXTEST\LOCKDOWN_DEMO2.SLX has the following Components Total Count is: 577 -------------------------------------------------- .NET Framework 1.1 - Security Update KB887998 Accessibility Control Panel Accessibility Core ACPI Fixed Feature Button Active Directory Service Interface (ADSI) Core Active Directory Service Interface (ADSI) LDAP Provider Active Directory Service Interface (ADSI) Windows NT Provider Active Template Library (ATL) Add Hardware Control Panel Add/Remove Programs Control Panel Administration Support Tools Administrator Account Advanced Configuration and Power Interface (ACPI) PC Analog TV Application Compatibility Core Audio Codecs Audio Control Panel Base Component Base Performance Counters Base Support Binaries CD-ROM Drive Certificate Request Client & Certificate Autoenrollment Certificate User Interface Services Class Install Library - Desk Class Install Library - Mdminst Class Install Library - Mmsys Class Install Library - Msports Class Install Library - Netcfgx Class Install Library - Storprop Class Install Library - System Devices Class Installer - Computer Class Installer - Disk drives Class Installer - Display adapters Class Installer - DVD/CD-ROM drives Class Installer - Floppy disk controllers Class Installer - Floppy disk drives -

Active @ UNDELETE Users Guide | TOC | 2
Active @ UNDELETE Users Guide | TOC | 2 Contents Legal Statement..................................................................................................4 Active@ UNDELETE Overview............................................................................. 5 Getting Started with Active@ UNDELETE........................................................... 6 Active@ UNDELETE Views And Windows......................................................................................6 Recovery Explorer View.................................................................................................... 7 Logical Drive Scan Result View.......................................................................................... 7 Physical Device Scan View................................................................................................ 8 Search Results View........................................................................................................10 Application Log...............................................................................................................11 Welcome View................................................................................................................11 Using Active@ UNDELETE Overview................................................................. 13 Recover deleted Files and Folders.............................................................................................. 14 Scan a Volume (Logical Drive) for deleted files..................................................................15 -

Billg the Manager
BillG the Manager “Intelli…what?”–Bill Gates The breadth of the Microsoft product line and the rapid turnover of core technologies all but precluded BillG from micro-managing the company in spite of the perceptions and lore around that topic. In less than 10 years the technology base of the business changed from the 8-bit BASIC era to the 16-bit MS-DOS era and to now the tail end of the 16-bit Windows era, on the verge of the Win32 decade. How did Bill manage this — where and how did he engage? This post introduces the topic and along with the next several posts we will explore some specific projects. At 38, having grown Microsoft as CEO from the start, Bill was leading Microsoft at a global scale that in 1993 was comparable to an industrial-era CEO. Even the legendary Thomas Watson Jr., son of the IBM founder, did not lead IBM until his 40s. Microsoft could never have scaled the way it did had BillG managed via a centralized hub-and-spoke system, with everything bottlenecked through him. In many ways, this was BillG’s product leadership gift to Microsoft—a deeply empowered organization that also had deep product conversations at the top and across the whole organization. This video from the early 1980’s is a great introduction to the breadth of Microsoft’s product offerings, even at a very early stage of the company. It also features some vintage BillG voiceover and early sales executive Vern Raburn. (Source: Microsoft videotape) Bill honed a set of undocumented principles that defined interactions with product groups. -

Partitioner Och Filsystem 2
Partitioner och filsystem 2 File systems FAT Unix-like NTFS Vad är ett filsystem? • Datorer behöver en metod för att lagra och hämta data… • Referensmodell för filsystem (Carrier) – Filsystem kategori • Layout och storleksinformation – Innehålls kategori • Kluster och block – data enheter – Metadata kategori • Tidsinformation, storlek, access kontroll • Adresser till allokerade data enheter – Filnamn kategori • Oftast ihop-kopplad med metadata – Applikations kategori • Quota • Journaler • De modernaste påminner mycket om relations databaser Windows • NTFS (New Technology File System) – 6 versioner finns, de nyaste är v3.0 (Windows 2000) och v3.1 (XP, 2003, Vista, 2008, 7), kallas även 5.0, 5.1, 5.2, 6.0 och 6.1 (efter OS version) – Stöd för unicode, säkerhet, mm. - är mycket mer komplext än FAT! – http://en.wikipedia.org/wiki/Ntfs • FAT 12/16/32, VFAT (långa filnamn i Win95) – Används fortfarande men är inte effektivt för större lagringskapaciteter (klusterstorleken) – Långsammare access än NTFS • Windows Future Storage (WinFS) inställt projekt, enligt rykten var det en SQL-databas som ligger ovanpå ett NTFS filsystem – Läs mer på: http://www.ntfs.com/ – Och: http://en.wikipedia.org/wiki/WinFS FAT12, 16 och 32 • FAT12, finns på floppy diskar – Begränsad lagringskapacitet – Designat för MS-DOS 1.0 • FAT16, var designat för större diskar – Äldre OS använde detta • MS-DOS 3.0, Win95 OSR1, NT 3.5 och NT 4.0 – Max diskstorlek 2 GB • FAT32 kom när diskar större än 2GB kom – Vissa äldre och alla nya OS kan använda FAT32 • Windows 98/Me/2000/XP/2003/Vista/7 och 2008 • Begränsningar med FAT32 – Största formaterabara volymen är 32GB (större volymer kan dock användas, < 16 TiB) – Begränsade features vad gäller komprimering, kryptering, säkerhet och hastighet jämfört mot NTFS • http://en.wikipedia.org/wiki/FAT_file_system exFAT • exFAT (Extended File Allocation Table, a.k.a. -

Microsoft Word 1 Microsoft Word
Microsoft Word 1 Microsoft Word Microsoft Office Word 2007 in Windows Vista Developer(s) Microsoft Stable release 12.0.6425.1000 (2007 SP2) / April 28, 2009 Operating system Microsoft Windows Type Word processor License Proprietary EULA [1] Website Microsoft Word Windows Microsoft Word 2008 in Mac OS X 10.5. Developer(s) Microsoft Stable release 12.2.1 Build 090605 (2008) / August 6, 2009 Operating system Mac OS X Type Word processor License Proprietary EULA [2] Website Microsoft Word Mac Microsoft Word is Microsoft's word processing software. It was first released in 1983 under the name Multi-Tool Word for Xenix systems.[3] [4] [5] Versions were later written for several other platforms including IBM PCs running DOS (1983), the Apple Macintosh (1984), SCO UNIX, OS/2 and Microsoft Windows (1989). It is a component of the Microsoft Office system; however, it is also sold as a standalone product and included in Microsoft Microsoft Word 2 Works Suite. Beginning with the 2003 version, the branding was revised to emphasize Word's identity as a component within the Office suite; Microsoft began calling it Microsoft Office Word instead of merely Microsoft Word. The latest releases are Word 2007 for Windows and Word 2008 for Mac OS X, while Word 2007 can also be run emulated on Linux[6] . There are commercially available add-ins that expand the functionality of Microsoft Word. History Word 1981 to 1989 Concepts and ideas of Word were brought from Bravo, the original GUI writing word processor developed at Xerox PARC.[7] [8] On February 1, 1983, development on what was originally named Multi-Tool Word began. -

Inside Windows 10 - an Early Look at Microsoft’S Newest Operating System Volume 1 - by Onuora Amobi
0 www.windows10update.com – Comprehensive Windows 10 News Copyright Notice INSIDE WINDOWS 10 - AN EARLY LOOK AT MICROSOFT’S NEWEST OPERATING SYSTEM VOLUME 1 - BY ONUORA AMOBI ©2015 Nnigma Inc. All rights reserved. Any unauthorized use, sharing, reproduction or distribution of these materials by any means, electronic, mechanical, or otherwise is strictly prohibited. No portion of these materials may be reproduced in any manner whatsoever, without the express written consent of the Publisher or Author. Published under the Copyright Laws of The United States of America by: Nnigma Inc. 3579 East Foothill Blvd, Suite #254 Pasadena, CA 91107 www.Nnigma.com i www.windows10update.com – Comprehensive Windows 10 News Legal Notice While all attempts have been made to verify information provided in this publication, neither the author nor the publisher assumes any responsibility for errors, omissions or contradictory interpretation of the subject matter herein. This publication is not intended to be used as a source of binding technical, technological, legal or accounting advice. Please remember that the information contained may be subject to varying state and/or local laws or regulations that may apply to the user’s particular practice. The purchaser or reader of this publication assumes responsibility for the use of these materials and information. Adherence to all applicable laws and regulations, both federal, state, and local, governing professional licensing, business practices, advertising and any other aspects of doing business in the US or any other jurisdiction is the sole responsibility of the purchaser or reader. Nnigma Inc. assumes no responsibility or liability whatsoever on behalf of any purchaser or reader of these materials. -

Copyrighted Material
Index Note to the Reader: Throughout this index boldfaced page numbers indicate primary discussions of a topic. Italicized page numbers indicate illustrations. IUSR_computername account, 274–275 Numbers disabling, 61 mapping certificates to, 283–286 3DES, 125–126, 416, 494 user accounts, configuring for 802.1x standard (IEEE), 181–184, 494 delegation, 46 authentication for, 182 ACEs (Access Control Entries) combining VPNs with, 190 authentication for clients, 494 802.11a standard (IEEE), 494 in Discretionary Access Control List, 7 vs. 802.11b, 170 Active Directory (AD), 3, 494 802.11b standard (IEEE), 494 assigning GPO to container in, 28 for certificate store, 404 Configuration container for certificate templates, 360 A mapping certificates to accounts, 283–286 Access Control Entries (ACEs), 494 in mixed mode, 324 in Discretionary Access Control List, 7 publishing certificates through, 404–409 Access Control List (ACL), 494 in child domain, 406–409 Access Control Settings dialog box, 16 from standalone online CA, 404–406 Auditing tab, 16, 440 to view published certificates and CRLs, “Access Is Denied” error message, 420 358–359 access point, 494. See also wireless access Active Directory domain controller point (WAP) client security to traffic, 226–229 access token, 260, 494 testing, 227–229 account lockout policy, in security Active Directory domains templates, 9 Properties dialog box, General tab, 228 account logon events, tracking, 15, 445 trust relationships, 271–273, 272 account management events, tracking, 15, Active Directory object, auditing, 18 445–446 Active Directory Properties dialog box, 228 Account Policies Active Directory Sites and Services (ADSS), security template configuration, 12, 5, 494 12–14, 13 configuration, 407–408 in security templates, 9 Active Directory Users and Computers (ADUC), accountability trail, 14 COPYRIGHTED5, MATERIAL494 accounts Active Server Pages (ASP), SUS and, 111 Administrator account, renaming, 55, 56 AD.