Security System for Mobile Messaging Applications Pejman Dashtinejad
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -
AVG Android App Performance and Trend Report H1 2016
AndroidTM App Performance & Trend Report H1 2016 By AVG® Technologies Table of Contents Executive Summary .....................................................................................2-3 A Insights and Analysis ..................................................................................4-8 B Key Findings .....................................................................................................9 Top 50 Installed Apps .................................................................................... 9-10 World’s Greediest Mobile Apps .......................................................................11-12 Top Ten Battery Drainers ...............................................................................13-14 Top Ten Storage Hogs ..................................................................................15-16 Click Top Ten Data Trafc Hogs ..............................................................................17-18 here Mobile Gaming - What Gamers Should Know ........................................................ 19 C Addressing the Issues ...................................................................................20 Contact Information ...............................................................................21 D Appendices: App Resource Consumption Analysis ...................................22 United States ....................................................................................23-25 United Kingdom .................................................................................26-28 -

Cisco SCA BB Protocol Reference Guide
Cisco Service Control Application for Broadband Protocol Reference Guide Protocol Pack #60 August 02, 2018 Cisco Systems, Inc. www.cisco.com Cisco has more than 200 offices worldwide. Addresses, phone numbers, and fax numbers are listed on the Cisco website at www.cisco.com/go/offices. THE SPECIFICATIONS AND INFORMATION REGARDING THE PRODUCTS IN THIS MANUAL ARE SUBJECT TO CHANGE WITHOUT NOTICE. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL RESPONSIBILITY FOR THEIR APPLICATION OF ANY PRODUCTS. THE SOFTWARE LICENSE AND LIMITED WARRANTY FOR THE ACCOMPANYING PRODUCT ARE SET FORTH IN THE INFORMATION PACKET THAT SHIPPED WITH THE PRODUCT AND ARE INCORPORATED HEREIN BY THIS REFERENCE. IF YOU ARE UNABLE TO LOCATE THE SOFTWARE LICENSE OR LIMITED WARRANTY, CONTACT YOUR CISCO REPRESENTATIVE FOR A COPY. The Cisco implementation of TCP header compression is an adaptation of a program developed by the University of California, Berkeley (UCB) as part of UCB’s public domain version of the UNIX operating system. All rights reserved. Copyright © 1981, Regents of the University of California. NOTWITHSTANDING ANY OTHER WARRANTY HEREIN, ALL DOCUMENT FILES AND SOFTWARE OF THESE SUPPLIERS ARE PROVIDED “AS IS” WITH ALL FAULTS. CISCO AND THE ABOVE-NAMED SUPPLIERS DISCLAIM ALL WARRANTIES, EXPRESSED OR IMPLIED, INCLUDING, WITHOUT LIMITATION, THOSE OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT OR ARISING FROM A COURSE OF DEALING, USAGE, OR TRADE PRACTICE. IN NO EVENT SHALL CISCO OR ITS SUPPLIERS BE LIABLE FOR ANY INDIRECT, SPECIAL, CONSEQUENTIAL, OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. -

Enterprise Edition
Secure Communication. Simplified. SAFECHATS Problem Most companies use popular insecure email and ⛔ messaging services to communicate confidential information P The information flow within the Company is ⛔ disorganized Metadata is exposed and available to third-party ⛔ services SAFECHATS Introducing SAFECHATS Ultra-secure communication solution P Designed with security in mind SAFECHATS Why SAFECHATS? ✔ Information is always end-to-end encrypted by default P ✔ All-in-one communication suite: • Text messaging (one-on-one and group chats) • Voice calls • File transfers (no size and file type limits) SAFECHATS How does SAFECHATS solve the problem? ✔ Customizable white label solution ✔ Integrates with existing softwareP infrastructure ✔ Enterprise-wide account and contact list management, supervised audited chats for compliance SAFECHATS What makes SAFECHATS different? ✔ Your own isolated cloud environment or on-premise deployment P ✔ Customizable solution allows to be compliant with internal corporate security policies ✔ No access to your phone number and contact list SAFECHATS Screenshot Protection ✔ Notifications on iOS P ✔ DRM protection on Android SAFECHATS Identity Verification ✔ Protection from man-in-the-middle attacksP ✔ SMP Protocol SAFECHATS Privacy Features ✔ Show / hide messages and files P ✔ Recall messages and files ✔ Self-destructing messages and files SAFECHATS Additional Protection ✔ History retention control P ✔ Application lock: • PIN-code • Pattern-lock on Android devices • Touch ID on iOS devices SAFECHATS How does SAFECHATS -
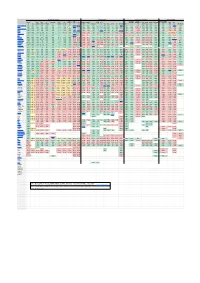
Digital Communications Protocols
Security & Privacy Compatibility Features & Usability Sustainability E2E E2E Offline Local Decentralized Active Open Open On Anonymous E2E E2E Default Audit FIDO1 Desktop Mobile Apple AOSP Messages messaging File Audio Video Phoneless or Federated Open IETF [1] TLS Client Server Premise [2] Private Group [3] [4] / U2F Web Web Android iOS [5] Win macOS Linux *BSD Terminal MDM [6] [7] [8] Share Call Call [9] [10] Spec [11] Introduced Element/Matrix TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE PARTIAL TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE 2014 XMPP TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE PARTIAL [12]TRUE FALSE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE [13] TRUE TRUE TRUE TRUE TRUE TRUE TRUE 1999 NextCloud Talk TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE TRUE TRUE FALSE TRUE TRUE TRUE TRUE TRUE FALSE FALSE 2018 Wire TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE TRUE FALSE TRUE TRUE FALSE TRUE TRUE TRUE TRUE PARTIAL TRUE TRUE FALSE TRUE TRUE TRUE TRUE FALSE FALSE FALSE 2014 Jami TRUE TRUE TRUE N/A [14] N/A TRUE TRUE FALSE [15] TRUE FALSE N/A [16] FALSE FALSE TRUE TRUE TRUE TRUE TRUE TRUE TRUE FALSE TRUE FALSE FALSE TRUE TRUE TRUE TRUE TRUE PARTIAL PARTIAL[17] [18] 2016 Briar [19] TRUE TRUE TRUE N/A [20] N/A TRUE TRUE TRUE TRUE TRUE N/A [21] FALSE FALSE TRUE FALSE TRUE FALSE FALSE FALSE FALSE FALSE FALSE TRUE TRUE FALSE FALSE FALSE FALSE TRUE FALSE FALSE 2016 Tox TRUE TRUE TRUE -
Protec3ng Messaging Other Than Email, Plus Network Link Protec3on
Protec'ng Messaging Other Than Email, plus Network Link Protec'on Joe St Sauver, Ph.D. [email protected] or [email protected] M3AAWG Senior Technical Advisor Scien@st, Farsight Security, Inc. Gold Ballroom, 1st Floor M3AAWG 36, San Francisco, California Wednesday Feb 17th, 2016, 15:30-16:30 hPps://www.stsauver.com/joe/crypto-other-than-email/ 1 Introduc'on • Today's session has two parts: – The first part will consider cryptographic privacy protecon for messaging other than email. – The second part will focus on cryptographic protecon of high speed internal links. • The common link between the two topics is that in each case, your op@ons are constrained by what the market offers. Today's goal is to help you understand why you want protec@on for these points of exposure, and how to select a solu@on. • Both of these topics are the subject of pending dra documents in the Pervasive Monitoring SIG. 2 I. Messaging Other Than Email 3 Messaging Other Than Email • M3AAWG has been working hard on protec@ng email against pervasive monitoring. • That's very important work, and protec@ng email privacy is a totally appropriate goal for M3AAWG. • Although M3AAWG has always had a strong focus on email, our charter, as the an@-Pervasive Monitoring SIG of the Messaging, Malware, and Mobile An-Abuse Working Group, includes, or should include, protec@ng mobile voice telephony and mobile applicaons (such as tex@ng/chat), too. • Arguably, for many users, secure mobile voice and secure text/ chat is as important, or even more important than email. -

National Security Agency | Cybersecurity Information Selecting
National Security Agency | Cybersecurity Information Selecting and Safely Using Collaboration Services for Telework - UPDATE Summary During a global pandemic or other crisis contingency scenarios, many United States Government (USG) personnel must operate from home while continuing to perform critical national functions and support continuity of government services. With limited access to government furnished equipment (GFE) such as laptops and secure smartphones, the use of (not typically approved) commercial collaboration services on personal devices for limited government official use becomes necessary and unavoidable. We define collaboration services as those capabilities that allow the workforce to communicate via internet-enabled text, voice, and video, and can include the sharing of files and other mission content. Collaboration can occur between two people or widened to include a large group to support mission needs. This document provides a snapshot of best practices and criteria based on capabilities available at the time of publication and was coordinated with the Department of Homeland Security (DHS), which has released similar guidance: “Cybersecurity Recommendations for Federal Agencies Using Video Conferencing” [1] and “Guidance for Securing Video Conferencing” [2]. This NSA publication is designed to provide simple and actionable considerations for individual government users. The intent of this document is not meant to be exhaustive or based on formal testing, but rather be responsive to a growing demand amongst the federal government to allow its workforce to operate remotely using personal devices when deemed to be in the best interests of the health and welfare of its workforce and the nation. Recommendations in this document are likely to change as collaboration services evolve and also address known vulnerabilities and threats. -

United States District Court for the Eastern District of Texas Marshall Division
Case 2:13-cv-00948-JRG-RSP Document 18 Filed 07/21/14 Page 1 of 14 PageID #: 158 UNITED STATES DISTRICT COURT FOR THE EASTERN DISTRICT OF TEXAS MARSHALL DIVISION MOBILE TELECOMMUNICATIONS § TECHNOLOGIES, LLC, § Plaintiff, § Civil Action No. 2:13-cv-948-JRG-RSP v. § § JURY TRIAL REQUESTED HTC AMERICA, INC., § Defendant. § PLAINTIFF MOBILE TELECOMMUNICATIONS TECHNOLOGIES, LLC’S AMENDED COMPLAINT Plaintiff Mobile Telecommunications Technologies, LLC (“MTel” or “Plaintiff”) by and through its undersigned attorneys, hereby pleads the following claims for patent infringement against Defendant HTC America, Inc. (“HTC” or “Defendant”) and alleges as follows. THE PARTIES 1. Plaintiff MTel is a Delaware limited liability company having a principal place of business at 1720 Lakepointe Drive, Suite 100 Lewisville, TX 75057. MTel is a wholly owned subsidiary of United Wireless Holdings, Inc. (“United Wireless”). In 2008, United Wireless, through another of its wholly owned subsidiaries, Velocita Wireless, LLC, purchased the SkyTel wireless network from Bell Industries, including assets related to SkyTel’s more than twenty year history as a wireless data company. Velocita Wireless, LLC, continued to operate the SkyTel wireless data network after the acquisition. As a result of that transaction, United Wireless gained ownership and control over the portfolio of intellectual property, including patents, developed over the years by several SkyTel-related entities, including Mobile Telecommunication Technologies Corp. (“MTEL Corp.”), Destineer Corporation, and SkyTel Communications. United Wireless subsequently assigned certain of the patent assets, including PLAINTIFF MOBILE TELECOMMUNICATIONS TECHNOLOGIES, LLC’S AMENDED COMPLAINT 740352V.1 Case 2:13-cv-00948-JRG-RSP Document 18 Filed 07/21/14 Page 2 of 14 PageID #: 159 the patents-in-suit, together with all rights of recovery related to those patent assets to its wholly owned subsidiary, MTel, which is the plaintiff here. -

It's 2 A.M. Do You Know What Your Data Is Doing?
It’s 2 a.m. Do You Know What Your Data is Doing? The files of a real estate brokerage are a treasure trove of data, packed full of information about people and homes. When you take a look into the files that you may carry with you daily or store under lock and key in your office, the data they contain while helpful to you and necessary to the transaction could be very harmful in the hands of another. The Federal Trade Commission recommends building a sound data security plan on the following 5 Key Principles 1. Take Stock 2. Scale Down 3. Lock It 4. Pitch It 5. Plan Ahead This course looks at those 5 Key Principles and how they relate to the day-to-day operations of a busy real estate brokerage. Take Stock “You don’t know what you’ve got until it’s gone…” Real Estate agents and Brokerages need to know what information they have, where it comes from and how they store it. For Brokers this begins with taking a look at the brokerage as an employer: 1. What information do you collect about employees and independent contractors of the brokerage? Social Security Numbers? Health Insurance forms or related information? Driver’s License numbers or photocopies of drivers licenses? Birthdate? Physical address? E-mail address? Telephone number? Vehicle information? 2. In what manner does the brokerage receive this information? o A form filled out and provided to the broker? o A digital form filled out and provided to the broker through the office intranet? o A digital form filled out and provided to the broker through e-mail? 3. -

The Leading Secure Communication & Collaboration Platform
pro The Leading Secure Communication & Collaboration Platform Security Wickr Pro is a user-friendly collaboration platform built with security first. Whether you are messaging, on a call, holding video conferences, file sharing, or using any of our other features, your communications are completely protected by our uncompromised, advanced security protocols. Compliance Wickr Pro allows you to secure all of your communications while still remaining compliant with industry regulations. You are in charge of what information is kept and what is automatically deleted with our expiration and burn-on-read timers. As you collaborate within Wickr, your communications and your customers’ data can remain secure. Control Wickr Pro gives you full administrative control over your network. Our security measures are customizable to your needs, so you can decide who has access to what data, set up security protocols, and be alerted if someone is out of network. "Given the multitude of attacks and access to communications solutions, enterprises need to deploy, manage and have flexible administrative controls to not only secure sensitive communications, but follow best practices for retaining information as required. Wickr is the only product that offers this through strong encryption, deployment options and selective controls." Joe Sullivan Former CSO of Facebook, Uber, and Cloudfare pro Features & Capabilities 1:1 and Group Audio and Video Screen Sharing and File Sharing and Messaging Calling Broadcasting Saving Create secure rooms with Conference with up -

Untraceable Links: Technology Tricks Used by Crooks to Cover Their Tracks
UNTRACEABLE LINKS: TECHNOLOGY TRICKS USED BY CROOKS TO COVER THEIR TRACKS New mobile apps, underground networks, and crypto-phones are appearing daily. More sophisticated technologies such as mesh networks allow mobile devices to use public Wi-Fi to communicate from one device to another without ever using the cellular network or the Internet. Anonymous and encrypted email services are under development to evade government surveillance. Learn how these new technology capabilities are making anonymous communication easier for fraudsters and helping them cover their tracks. You will learn how to: Define mesh networks. Explain the way underground networks can provide untraceable email. Identify encrypted email services and how they work. WALT MANNING, CFE President Investigations MD Green Cove Springs, FL Walt Manning is the president of Investigations MD, a consulting firm that conducts research related to future crimes while also helping investigators market and develop their businesses. He has 35 years of experience in the fields of criminal justice, investigations, digital forensics, and e-discovery. He retired with the rank of lieutenant after a 20-year career with the Dallas Police Department. Manning is a contributing author to the Fraud Examiners Manual, which is the official training manual of the ACFE, and has articles published in Fraud Magazine, Police Computer Review, The Police Chief, and Information Systems Security, which is a prestigious journal in the computer security field. “Association of Certified Fraud Examiners,” “Certified Fraud Examiner,” “CFE,” “ACFE,” and the ACFE Logo are trademarks owned by the Association of Certified Fraud Examiners, Inc. The contents of this paper may not be transmitted, re-published, modified, reproduced, distributed, copied, or sold without the prior consent of the author. -

Exinda Applications List
Application List Exinda ExOS Version 6.4 © 2014 Exinda Networks, Inc. 2 Copyright © 2014 Exinda Networks, Inc. All rights reserved. No parts of this work may be reproduced in any form or by any means - graphic, electronic, or mechanical, including photocopying, recording, taping, or information storage and retrieval systems - without the written permission of the publisher. Products that are referred to in this document may be either trademarks and/or registered trademarks of the respective owners. The publisher and the author make no claim to these trademarks. While every precaution has been taken in the preparation of this document, the publisher and the author assume no responsibility for errors or omissions, or for damages resulting from the use of information contained in this document or from the use of programs and source code that may accompany it. In no event shall the publisher and the author be liable for any loss of profit or any other commercial damage caused or alleged to have been caused directly or indirectly by this document. Document Built on Tuesday, October 14, 2014 at 5:10 PM Documentation conventions n bold - Interface element such as buttons or menus. For example: Select the Enable checkbox. n italics - Reference to other documents. For example: Refer to the Exinda Application List. n > - Separates navigation elements. For example: Select File > Save. n monospace text - Command line text. n <variable> - Command line arguments. n [x] - An optional CLI keyword or argument. n {x} - A required CLI element. n | - Separates choices within an optional or required element. © 2014 Exinda Networks, Inc.