Configuring the Information Environment of Microcomputers with the Microsoft Windows 10 Operating System
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

P Palmtop Aper
u.s. $7.95 Publisher's Message ................................ , Letters to the Editor .................................. ~ - E New Third Party Ln Products and Services ............................ .E ..... =Q) HP Palmtop Users Groups ...................... J E :::J User to User ............................................ 1( :z Hal reports on the excitement at the HP Handheld - P Palmtop User's Conference, a new book by David Packard "<t" describing the history of HP, our new 200LXI1000CX Q) loaner p'rogram for developers, the 1995/1996 E Subscnbers PowerDisk and some good software :::J that didn't make it into thePowerDisk, but is on this o issue's ON DISK and CompuServe. > aper PalmtoD Wisdom .................................... 2< Know ~here you stand with your finances; Keep impqrtant information with you, and keep it secure; The best quotes may not tie in the quotes books. Built·in Apps on Vacation: To Africa and Back with the HP Palmtop ....................................... 1E acafTen/ The HP 200LX lielps a couple from Maryland prepare for their dream vacation to Africa. Built·in Apps on Vacation: Editor on Vacation .................................. 2( Even on vacation, Rich Hall, managing editor for The HP Palmtop Paper, finds the Palmtop to be an indispensable companion. AP~ointment Book: ~n ~~l~epP~~'~~~~~~.~~.~~...................... 2~ Appointment Book provides basic prol'ect management already built into the HP Pa mtop. DataBase: Print Your Database in the Format You Want .......................... 3( Create a custom database and print Hout in the for mat you want using the built-in DataBase program and Smart Clip. Lotus 1·2·3 Column: Basic Training for 1-2-3 Users ............... 3~ Attention first-time Lotus users, or those needing a bH of a refresher - get out your HP Palmtop and fonow along with this review of the basics. -
Linux Hardware Compatibility HOWTO
Linux Hardware Compatibility HOWTO Steven Pritchard Southern Illinois Linux Users Group [email protected] 3.1.5 Copyright © 2001−2002 by Steven Pritchard Copyright © 1997−1999 by Patrick Reijnen 2002−03−28 This document attempts to list most of the hardware known to be either supported or unsupported under Linux. Linux Hardware Compatibility HOWTO Table of Contents 1. Introduction.....................................................................................................................................................1 1.1. Notes on binary−only drivers...........................................................................................................1 1.2. Notes on commercial drivers............................................................................................................1 1.3. System architectures.........................................................................................................................1 1.4. Related sources of information.........................................................................................................2 1.5. Known problems with this document...............................................................................................2 1.6. New versions of this document.........................................................................................................2 1.7. Feedback and corrections..................................................................................................................3 1.8. Acknowledgments.............................................................................................................................3 -

Wearable Technology for Enhanced Security
Communications on Applied Electronics (CAE) – ISSN : 2394-4714 Foundation of Computer Science FCS, New York, USA Volume 5 – No.10, September 2016 – www.caeaccess.org Wearable Technology for Enhanced Security Agbaje M. Olugbenga, PhD Babcock University Department of Computer Science Ogun State, Nigeria ABSTRACT Sproutling. Watches like the Apple Watch, and jewelry such Wearable's comprise of sensors and have computational as Cuff and Ringly. ability. Gadgets such as wristwatches, pens, and glasses with Taking a look at the history of computer generations up to the installed cameras are now available at cheap prices for user to present, we could divide it into three main types: mainframe purchase to monitor or securing themselves. Nigerian faced computing, personal computing, and ubiquitous or pervasive with several kidnapping in schools, homes and abduction for computing[4]. The various divisions is based on the number ransomed collection and other unlawful acts necessitate these of computers per users. The mainframe computing describes reviews. The success of the wearable technology in medical one large computer connected to many users and the second, uses prompted the research into application into security uses. personal computing, as one computer per person while the The method of research is the use of case studies and literature term ubiquitous computing however, was used in 1991 by search. This paper takes a look at the possible applications of Paul Weiser. Weiser depicted a world full of embedded the wearable technology to combat the cases of abduction and sensing technologies to streamline and improve life [5]. kidnapping in Nigeria. Nigeria faced with several kidnapping in schools and homes General Terms are in dire need for solution. -
Scheme of Work 2021-22 Computer Class
Scheme of Work 2021-22 Rev. No: 01 Computer Class: III Date: 9 February 2021 Book: Computer 3 Term: I Periods of week: 2 Total teaching minutes per week: 80 minutes Duration of 1 period: 40 minutes Total Weeks: 17 weeks Week Content Week Content 1st Types of computers 9th Inside the system unit nd th 2 Types of computers 10 Inside the system unit rd th 3 Types of computers 11 Inside the system unit th th 4 Types of computers 12 Inside the system unit 5th Revision 13th Practical: Inside the system unit th th 6 Revision 14 Revision th th 7 Revision 15 Revision 16th 8th Quarterly Test First Term Exam 17th Page 1 of 5 This is a CONTROLLED & CONFIDENTIAL document of “Dr. A. Q. Khan School System”. Its unauthorized disclosure or reproduction shall be liable for prosecution under the copyright act and any other law Daily Lesson Plan (DLP) Session 2021-22 Subject: Computer Term – I Topic: Types of computer Class: III Week: 01 Learning Plan (Methodology) Time Resources Assessment Objectives By the end of this Introduction: Teacher should ask some question related to 40 Book Teacher should Lesson Students computer. min Board assess students by should be able to: Development: computer asking of: After reading the lesson teacher should tell them about four different Tell or explain main types of computer. questions about 1. Micro computer: These are most smallest and common computer computers. It is also called personal computer. These are types used in homes, school and colleges etc. these computers are divided into three types. -
Apollo Twin USB Hardware Manual
Apollo Twin USB Hardware Manual Manual Version 210429 www.uaudio.com A Letter from Bill Putnam Jr. Thank you for deciding to make the Apollo Twin High-Resolution Interface part of your music making experience. We know that any new piece of gear requires an investment of time and money — and our goal is to make your investment pay off. The fact that we get to play a part in your creative process is what makes our efforts meaningful, and we thank you for this. In many ways, the Apollo family of audio interface products represent the best examples of what Universal Audio has stood for over its long history; from UA’s original founding in the 1950s by my father, through our current vision of delivering the best of both analog and digital audio technologies. Starting with its high-quality analog I/O, Apollo Twin’s superior sonic performance serves as its foundation. This is just the beginning however, as Apollo Twin is the only desktop audio interface that allows you to run UAD plug-ins in real time. Want to monitor yourself through a Neve® console channel strip while tracking bass through a classic Fairchild or LA-2A compressor? Or how about tracking vocals through a Studer® tape machine with some added Lexicon® reverb?* With our growing library of more than 90 UAD plug-ins, the choices are limitless. At UA, we are dedicated to the idea that this powerful technology should ultimately serve the creative process — not be a barrier. These are the very ideals my father embodied as he invented audio equipment to solve problems in the studio. -

Understanding Alphabet and Google, 2017
This research note is restricted to the personal use of [email protected]. Understanding Alphabet and Google, 2017 Published: 24 February 2017 ID: G00297707 Analyst(s): Tom Austin, David Mitchell Smith, Yefim V. Natis, Isabelle Durand, Ray Valdes, Bettina Tratz-Ryan, Roberta Cozza, Daniel O'Connell, Lydia Leong, Jeffrey Mann, Andrew Frank, Brian Blau, Chris Silva, Mark Hung, Adam Woodyer, Matthew W. Cain, Steve Riley, Martin Reynolds, Whit Andrews, Alexander Linden, David Yockelson, Joe Mariano Google's size, market differentiation, rapid pace of innovation and ambitions can complicate fully understanding the vendor and its fit to current digital business needs. CIOs and IT leaders can use this report to explore in detail selected topics from the Gartner Vendor Rating. Key Findings ■ Two outcomes are apparent more than a year after the creation of the Alphabet-Google structure: Google is beginning to show increased momentum and has made significant investments in its enterprise offerings (most of its 2016 acquisitions were focused on this); and it is applying more discipline in Alphabet's "Other Bets." ■ Google is flourishing despite challenging external market factors: adverse publicity, competitors, government regulators and law enforcement. ■ Google values data, encourages bold investments in long-term horizons, pivots plans based on results in near real time, and reveres user-oriented engineering excellence. ■ Google is fully committed to 100% cloud-based and web-scale infrastructure, massive scaling, the maximum rate of change, and stream-lined business processes for itself and its customers. Recommendations CIOs and IT leaders managing vendor risk and performance should: ■ Plan for a long-term strategic relationship with Google based on an assumption that "what you see is what you get." Major vendor changes to core culture and fundamental operating principles in response to customer requests usually come slowly, if at all. -
TECHNICAL MANUAL of Intel H110 Express Chipset Based Mini-ITX
TECHNICAL MANUAL Of Intel H110 Express Chipset Based Mini-ITX M/B NO. G03-NF693-F Revision: 3.0 Release date: July 19, 2017 Trademark: * Specifications and Information contained in this documentation are furnished for information use only, and are subject to change at any time without notice, and should not be construed as a commitment by manufacturer. Environmental Protection Announcement Do not dispose this electronic device into the trash while discarding. To minimize pollution and ensure environment protection of mother earth, please recycle. i TABLE OF CONTENT ENVIRONMENTAL SAFETY INSTRUCTION ...................................................................... iii USER’S NOTICE .................................................................................................................. iv MANUAL REVISION INFORMATION .................................................................................. iv ITEM CHECKLIST ................................................................................................................ iv CHAPTER 1 INTRODUCTION OF THE MOTHERBOARD 1-1 FEATURE OF MOTHERBOARD ................................................................................ 1 1-2 SPECIFICATION ......................................................................................................... 2 1-3 LAYOUT DIAGRAM .................................................................................................... 3 CHAPTER 2 HARDWARE INSTALLATION 2-1 JUMPER SETTING .................................................................................................... -

Classification of Computer
Department Of Business Administration Dr. Rakesh Ranjan BBA Sem -2 Classification of Computer Generally, computers can be divided into 3 types. 1. Analog Computers 2. Digital Computers 3. Hybrid Computers ANALOG COMPUTERS : In this type of computers, numerical magnitudes are represented by physical quantities such as electric current, voltage, or resistance, mechanical movements, etc. These are machines which are designed to perform arithmetical functions upon numbers where the numbers are represented by physical quantity. Analog computers are widely used in manufacturing units where temperatures, pressure or flow of liquids are to be monitored continuously. It is also used at petrol pump where petrol pump contains an analog processor that connects fuel flow measurements into quantity and price values. Among the various drawbacks of using Analog computers are: They do not have the ability to store data in large quantities; They do not have the logical facilities; They can perform only arithmetical functions but are more costlier. DIGITAL COMPUTERS : A digital computer operates on data in the form of digits, rather than the physical quantities used in analog computers. That is, its input must be discrete rather than continuous and may consist of combinations of numbers, characters and special symbols, written in appropriate programming language. Digital computers can be classified into two parts: General Purpose Digital Computers They are also known as all purpose digital computers. Theoretically they can be used for any type of applications, e.g., computers that are used for payroll, graphs, analysis, etc. Special Purpose Digital Computers A digital computer is 'designed to solve problems of a restricted type. -
Embedded Android
www.it-ebooks.info www.it-ebooks.info Praise for Embedded Android “This is the definitive book for anyone wanting to create a system based on Android. If you don’t work for Google and you are working with the low-level Android interfaces, you need this book.” —Greg Kroah-Hartman, Core Linux Kernel Developer “If you or your team works on creating custom Android images, devices, or ROM mods, you want this book! Other than the source code itself, this is the only place where you’ll find an explanation of how Android works, how the Android build system works, and an overall view of how Android is put together. I especially like the chapters on the build system and frameworks (4, 6, and 7), where there are many nuggets of information from the AOSP source that are hard to reverse-engineer. This book will save you and your team a lot of time. I wish we had it back when our teams were starting on the Frozen Yogurt version of Android two years ago. This book is likely to become required reading for new team members working on Intel Android stacks for the Intel reference phones.” —Mark Gross, Android/Linux Kernel Architect, Platform System Integration/Mobile Communications Group/Intel Corporation “Karim methodically knocks out the many mysteries Android poses to embedded system developers. This book is a practical treatment of working with the open source software project on all classes of devices, beyond just consumer phones and tablets. I’m personally pleased to see so many examples provided on affordable hardware, namely BeagleBone, not just on emulators.” —Jason Kridner, Sitara Software Architecture Manager at Texas Instruments and cofounder of BeagleBoard.org “This book contains information that previously took hundreds of hours for my engineers to discover. -

A History of the Personal Computer Index/11
A History of the Personal Computer 6100 CPU. See Intersil Index 6501 and 6502 microprocessor. See MOS Legend: Chap.#/Page# of Chap. 6502 BASIC. See Microsoft/Prog. Languages -- Numerals -- 7000 copier. See Xerox/Misc. 3 E-Z Pieces software, 13/20 8000 microprocessors. See 3-Plus-1 software. See Intel/Microprocessors Commodore 8010 “Star” Information 3Com Corporation, 12/15, System. See Xerox/Comp. 12/27, 16/17, 17/18, 17/20 8080 and 8086 BASIC. See 3M company, 17/5, 17/22 Microsoft/Prog. Languages 3P+S board. See Processor 8514/A standard, 20/6 Technology 9700 laser printing system. 4K BASIC. See Microsoft/Prog. See Xerox/Misc. Languages 16032 and 32032 micro/p. See 4th Dimension. See ACI National Semiconductor 8/16 magazine, 18/5 65802 and 65816 micro/p. See 8/16-Central, 18/5 Western Design Center 8K BASIC. See Microsoft/Prog. 68000 series of micro/p. See Languages Motorola 20SC hard drive. See Apple 80000 series of micro/p. See Computer/Accessories Intel/Microprocessors 64 computer. See Commodore 88000 micro/p. See Motorola 80 Microcomputing magazine, 18/4 --A-- 80-103A modem. See Hayes A Programming lang. See APL 86-DOS. See Seattle Computer A+ magazine, 18/5 128EX/2 computer. See Video A.P.P.L.E. (Apple Pugetsound Technology Program Library Exchange) 386i personal computer. See user group, 18/4, 19/17 Sun Microsystems Call-A.P.P.L.E. magazine, 432 microprocessor. See 18/4 Intel/Microprocessors A2-Central newsletter, 18/5 603/4 Electronic Multiplier. Abacus magazine, 18/8 See IBM/Computer (mainframe) ABC (Atanasoff-Berry 660 computer. -
Pdas in Medicine.Pdf
Review Personal digital assistants in health care: experienced clinicians in the palm of your hand? Daniel C Baumgart Lancet 2005; 366: 1210–22 Physicians and other health-care professionals are rapidly adopting personal digital assistants (PDA). Palm pilots Department of Medicine, and other hand-held computers are also increasingly popular among medical students. PDAs can be used for Charité Medical School, medical student education and physician training, daily clinical practice, and research. PDAs and their increasing Virchow Hospital, Humboldt- integration with information technology in hospitals could change the way health care is delivered in the future. But University of Berlin, D-13344 Berlin, Germany despite the increasing use of PDAs, evidence from well-designed research studies is still needed to show how much (D C Baumgart MD) these devices can improve the quality of care, save patients’ lives, and ultimately reduce health-care expenses. In this Correspondence to: Review of PDA use in health care, the operating systems, basic functionality, security and safety, limitations, and Dr Daniel C Baumgart future implications of PDAs are examined. A personal perspective and an introduction to medical PDA applications, [email protected] software, guidelines, and programmes for health-care professionals is also provided. Health care in the developed world is characterised by a Clinicians are rapidly adopting PDAs into their daily rapidly increasing use of information technology in practice.1 In one study, more than half of -
NSA ANT Catalog PDF from EFF.Org
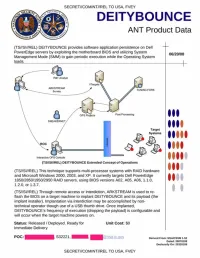
SECRET//COMINT//REL TO USA. FVEY DEITYBOUNCE ANT Product Data (TS//SI//REL) DEITYBOUNCE provides software application persistence on Dell PowerEdge servers by exploiting the motherboard BIOS and utilizing System Management Mode (SMM) to gain periodic execution while the Operating System loads. _________________ _________________________________________ TUMI KG FORK Post Proc*t*ftg Target Systems (TS//SM/REL) DEITYBOUNCE Extended Concept ot Operations (TS//SI//REL) This technique supports multi-processor systems with RAID hardware and Microsoft Windows 2000. 2003. and XP. It currently targets Dell PowerEdge A A 1850/2850/1950/2950 RAID servers, using BIOS versions A02. A05. A 0 6 .1.1.0. " " 1.2.0. or 1.3.7. (TS//SI//REL) Through remote access or interdiction. ARKSTREAM is used to re flash the BIOS on a target machine to implant DEITYBOUNCE and its payload (the implant installer). Implantation via interdiction may be accomplished by non technical operator though use of a USB thumb drive. Once implanted. DEITYBOUNCE's frequency of execution (dropping the payload) is configurable and will occur when the target machine powers on. Status: Released / Deployed. Ready for Unit Cost: $0 Immediate Delivery POC: S32221. | Oenverl From: NSAfCSSM 1-52 Dated: 20070108 Oeclaisify On: 20320108 SECRET//COMINT//REL TO USA. FVEY TOP SECRET//COMINT//REL TO USA. FVEY IRONCHEF ANT Product Data (TS//SI//REL) IRONCHEF provides access persistence to target systems by exploiting the motherboard BIOS and utilizing System Management Mode (SMM) to 07/14/08 communicate with a hardware implant that provides two-way RF communication. CRUMPET COVERT CLOSED NETWORK NETW ORK (CCN ) (Tefgef So*col CCN STRAITBIZAKRE N ode Compute* Node r -\— 0 - - j CCN S e rv e r STRAITBIZARRE Node CCN Computer UNITCORAKt Computer Node I Futoie Nodoe UNITE ORA KE Server Node I (TS//SI//REL) IRONCHEF Extended Concept of Operations (TS//SI/REL) This technique supports the HP Proliant 380DL G5 server, onto which a hardware implant has been installed that communicates over the l?C Interface (WAGONBED).