Impostor Scams
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
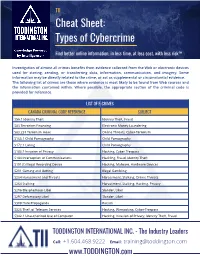
TII Cybercrime Cheat Sheet
TII Cheat Sheet: Types of Cybercrime Find better online information, in less time, at less cost, with less risk™ Investigation of almost all crimes benefits from evidence collected from the Web or electronic devices used for storing, sending, or transferring data, information, communication, and imagery. Some information may be directly related to the crime, or act as supplemental or circumstantial evidence. The following list of crimes are those where evidence is most likely to be found from Web sources and the information contained within. Where possible, the appropriate section of the criminal code is provided for reference. LIST OF E-CRIMES CANADA CRIMINAL CODE REFERENCE SUBJECT S56.1 Identity Theft Identity Theft, Fraud S83 Terrorism Financing Electronic Money Laundering S83.231 Terrorism Hoax Online Threats, Cyber-Terrorism S163.1 Child Pornography Child Pornography S172.1 Luring Child Pornography S183.1 Invasion of Privacy Hacking, Cyber-Trespass S184 Interception of Communications Hackling, Fraud, Identity Theft S191(1) Illegal Recording Device Hacking, Malware, Hardware Devices S201 Gaming and Betting Illegal Gambling S264 Harassment and Threats Harassment, Stalking, Online Threats S264 Stalking Harassment, Stalking, Hacking, Privacy S296 Blasphemous Libel Slander, Libel S297 Defamatory Libel Slander, Libel S308 Hate Propaganda Racism S326 Theft of Telecom Services Hacking, Wirejacking, Cyber-Trespass S342.1 Unauthorized Use of Computer Hacking, Invasion of Privacy, Identity Theft, Fraud TODDINGTON INTERNATIONAL INC. - The Industry -

Zerohack Zer0pwn Youranonnews Yevgeniy Anikin Yes Men
Zerohack Zer0Pwn YourAnonNews Yevgeniy Anikin Yes Men YamaTough Xtreme x-Leader xenu xen0nymous www.oem.com.mx www.nytimes.com/pages/world/asia/index.html www.informador.com.mx www.futuregov.asia www.cronica.com.mx www.asiapacificsecuritymagazine.com Worm Wolfy Withdrawal* WillyFoReal Wikileaks IRC 88.80.16.13/9999 IRC Channel WikiLeaks WiiSpellWhy whitekidney Wells Fargo weed WallRoad w0rmware Vulnerability Vladislav Khorokhorin Visa Inc. Virus Virgin Islands "Viewpointe Archive Services, LLC" Versability Verizon Venezuela Vegas Vatican City USB US Trust US Bankcorp Uruguay Uran0n unusedcrayon United Kingdom UnicormCr3w unfittoprint unelected.org UndisclosedAnon Ukraine UGNazi ua_musti_1905 U.S. Bankcorp TYLER Turkey trosec113 Trojan Horse Trojan Trivette TriCk Tribalzer0 Transnistria transaction Traitor traffic court Tradecraft Trade Secrets "Total System Services, Inc." Topiary Top Secret Tom Stracener TibitXimer Thumb Drive Thomson Reuters TheWikiBoat thepeoplescause the_infecti0n The Unknowns The UnderTaker The Syrian electronic army The Jokerhack Thailand ThaCosmo th3j35t3r testeux1 TEST Telecomix TehWongZ Teddy Bigglesworth TeaMp0isoN TeamHav0k Team Ghost Shell Team Digi7al tdl4 taxes TARP tango down Tampa Tammy Shapiro Taiwan Tabu T0x1c t0wN T.A.R.P. Syrian Electronic Army syndiv Symantec Corporation Switzerland Swingers Club SWIFT Sweden Swan SwaggSec Swagg Security "SunGard Data Systems, Inc." Stuxnet Stringer Streamroller Stole* Sterlok SteelAnne st0rm SQLi Spyware Spying Spydevilz Spy Camera Sposed Spook Spoofing Splendide -

FINANCIAL CRIME DIGEST July 2020
FINANCIAL CRIME DIGEST July 2020 Diligent analysis. Powering business.™ aperio-intelligence.com FINANCIAL CRIME DIGEST | JULY 2020 ISSN: 2632-8364 About Us Founded in 2014, Aperio Intelligence is a specialist, independent corporate intelligence frm, headquartered in London. Collectively our team has decades of experience in undertaking complex investigations and intelligence analysis. We speak over twenty languages in- house, including all major European languages, as well as Russian, Arabic, Farsi, Mandarin and Cantonese. We have completed more than 3,000 assignments over the last three years, involving some 150 territories. Our client base includes a broad range of leading international fnancial institutions, law frms and multinationals. Our role is to help identify and understand fnancial crime, contacts, cultivated over decades, who support us regularly integrity and reputational risks, which can arise from a lack in undertaking local enquiries on a confdential and discreet of knowledge of counterparties or local jurisdictions, basis. As a specialist provider of corporate intelligence, we enabling our clients to make better informed decisions. source information and undertake research to the highest legal and ethical standards. Our independence means we Our due diligence practice helps clients comply with anti- avoid potential conficts of interest that can affect larger bribery and corruption, anti-money laundering and other organisations. relevant fnancial crime legislation, such as sanctions compliance, or the evaluation of tax evasion or sanctions We work on a “Client First” basis, founded on a strong risks. Our services support the on-boarding, periodic or commitment to quality control, confdentiality and respect retrospective review of clients or third parties. for time constraints. -

Cybercrime Presentation
Cybercrime ‐ Marshall Area Chamber of October 10, 2017 Commerce CYBERCRIME Marshall Area Chamber of Commerce October 10, 2017 ©2017 RSM US LLP. All Rights Reserved. About the Presenter Jeffrey Kline − 27 years of information technology and information security experience − Master of Science in Information Systems from Dakota State University − Technology and Management Consulting with RSM − Located in Sioux Falls, South Dakota • Rapid Assessment® • Data Storage SME • Virtual Desktop Infrastructure • Microsoft Windows Networking • Virtualization Platforms ©2017 RSM US LLP. All Rights Reserved. RSM US LLP 1 Cybercrime ‐ Marshall Area Chamber of October 10, 2017 Commerce Content - Outline • History and introduction to cybercrimes • Common types and examples of cybercrime • Social Engineering • Anatomy of the attack • What can you do to protect yourself • Closing thoughts ©2017 RSM US LLP. All Rights Reserved. INTRODUCTION TO CYBERCRIME ©2017 RSM US LLP. All Rights Reserved. RSM US LLP 2 Cybercrime ‐ Marshall Area Chamber of October 10, 2017 Commerce Cybercrime Cybercrime is any type of criminal activity that involves the use of a computer or other cyber device. − Computers used as the tool − Computers used as the target ©2017 RSM US LLP. All Rights Reserved. Long History of Cybercrime John Draper uses toy whistle from Cap’n Crunch cereal 1971 box to make free phone calls Teller at New York Dime Savings Bank uses computer to 1973 funnel $1.5 million into his personal bank account First convicted felon of a cybercrime – “Captain Zap” 1981 who broke into AT&T computers UCLA student used a PC to break into the Defense 1983 Department’s international communication system Counterfeit Access Device and Computer Fraud and 1984 Abuse Act was passed ©2017 RSM US LLP. -

Catfishing”: a Comparative Analysis of U.S
“CATFISHING”: A COMPARATIVE ANALYSIS OF U.S. V. CANADIAN CATFISHING LAWS & THEIR LIMITATIONS Antonella Santi* I. INTRODUCTION ................................................................................... 75 II. BACKGROUND .................................................................................... 78 A. Catfishing– what is it? ...................................................................... 78 B. Harms of Catfishing .......................................................................... 78 C. Why do Perpetrators Catfish? ........................................................... 81 1. Loneliness ................................................................................ 81 2. Dissatisfaction with Physical Appearance ............................... 81 3. Sexuality and Gender Identity .................................................. 82 D. The Victim: Who Succumbs to Catfishing Schemes? ...................... 82 E. Society’s Contribution to Catfishing ................................................. 83 III. U.S. ANTI-CATFISHING LAWS ........................................................ 85 A. Federal Law ...................................................................................... 85 1. The Federal Identity Theft and Assumption Deterrence Act of 1998 ............................................................................................... 85 2. The Interstate Communications Act ......................................... 85 3. The Federal Interstate Stalking Punishment and Prevention Act ...................................................................................................... -
The SEON Online Fraud Dictionary - 2021 Edition
EBOOK The SEON Online Fraud Dictionary - 2021 Edition SEON Technologies Ltd. [email protected] seon.io +44 20 8089 2900 1 The SEON Online Fraud Dictionary - 2021 Edition The SEON Online Fraud Dictionary - 2021 Edition All the analysts agree: online fraud is going to increase in the upcoming years. And at SEON, our job is both to fight it, and to help companies prepare against attacks. This is why we wanted to compile a list of all the useful terms you might need to understand, prevent, and combat fraud. The vocabulary of online security and cybercrime evolves fast, and it’s important to keep up with the latest terms. But it’s also important to know the basics if this is your first entry into the world of cybercrime. We’ve compiled a list of both in this dictionary. 2 The SEON Online Fraud Dictionary - 2021 Edition 2FA Stands for 2-factor authentication. When a user wants to access a website or app, they need to provide a single piece of authentication (SFA) in the form of a password. Adding another method is called 2-factor authentication, and it improves security. You will also hear the name multi-factor authentication. Authentication factors can include facial scans, ID cards, SMS confirmations, security tokens, or biometric fingerprints, amongst others. According to Google, 2FA helps reduce 66% of targeted attacks, and 99% of bulk phishing attacks. 3D Secure A security protocol designed for online credit and debit card transactions. It is designed as an additional password validated by the issuer, which helps transfer liability to the customer in case of fraud. -

Copyrighted Material
1 The Many Faces of Evil Online Human wickedness is sometimes the product of a sort of conscious leeringly evil intent… But more usually it is the product of a semi‐deliberate inattention, in a swooning relationship to time. Iris Murdoch1 1.1 Introduction In May 2008, hackers bombarded the website of the Epilepsy Foundation of America with hundreds of pictures and links. The site provides advice, news on scientific research and contacts for people who suffer from epilepsy. People who suffer from epileptic seizures have to manage their condition carefully and need regular checkups and medical advice. Epilepsy patients often take precautionary mea- sures to deal with situations where they may be incapacitated and unable to act. Some patients suffer from what is called “photosensitive epilepsy,” which means that flickering and flashing images may trigger epileptic seizures. The hackers who attacked the Landover site exploited a security flaw and inserted links to pages with rapidly flashing images. These images were perceived inadvertently by epilepsy patients who were looking for medical information on the website and triggered severe migraines and near‐seizure reactions in some site visitors. “They were out to create seizures,” said Ken Lowenberg, senior director of web and print publishing for the COPYRIGHTED MATERIAL 1 Iris Murdoch, The Black Prince, Harmondsworth: Penguin, 1973, p. 189. Evil Online, First Edition. Dean Cocking and Jeroen van den Hoven. © 2018 John Wiley & Sons Ltd. Published 2018 by John Wiley & Sons Ltd. 0003386160.indd 1 3/6/2018 6:46:20 AM 2 The Many Faces of Evil Online foundation.2 The hackers did not seem to be interested in money or in control over the victim’s computer; they just wanted to create this impact on vulnerable people. -
2015 Buyer's Guide
Janmagazine_Layout 1 12/29/14 11:56 AM Page 1 Communications & new media Jan. 2015 II Vol. 29 No. 1 2015 BUYER’S GUIDE PRODUCTS & SERVICES IN MORE THAN 50 CATEGORIES FOR THE PR INDUSTRY BROADCAST MONITORING, SPEECH TRAINING, VIDEO, PRESS RELEASE DISTRIBUTION, CLIPPING SERVICES, COPYWRITING, PRINT SERVICES, TV PRODUCTION, RADIO, MEDIA MONITORING, MEDIA TOURS, NEWSWIRES, WEBCASTS, SOCIAL MEDIA, SATELLITE SERVICES, PSA’S & MORE! SPECIAL FEATURE: CRISIS COMMUNICATIONS Why no company is immune to a data breach Shareholder activism goes mainstream Top crisis blunders of 2014 Crisis training for campus sexual assault Crisis preparation in the digital age January 2015 | www.odwyerpr.com Nuance matters over formula in a crisis Profiles of crisis communications PR firms Janmagazine_Layout 1 12/29/14 11:56 AM Page 2 Janmagazine_Layout 1 12/29/14 11:56 AM Page 3 Janmagazine_Layout 1 12/29/14 11:56 AM Page 4 Vol. 29, No. 1 January 2015 EDITORIAL CRISIS PREPARATION IN PR, journalism jobs are stressful. THE DIGITAL AGE Favorable outcomes in today’s TRUSTEE OBJECTS TO SALE OF 6 28 crises come to those who prepare. BULLDOG ASSETS A bankruptcy trustee has objected to CIA PUBLIC AFFAIRS LEAKED Bulldog Reporter’s plans to sell assets.8 FALSE INFORMATION A Senate Intelligence Committee PR “FAILS” OF 2014 30 report reveals shocking details. Bill Cosby, the NFL, and GM top O’Dwyer’s PR “fails” of the year. THE LOST ART OF PAUSING 10 10 IN TIMES OF CRISIS Silence, reflection accompanies 2014, THE YEAR IN REVIEW 32 preparation in times of crisis. Jack O’Dwyer recounts the top PR stories of the year. -

ATA July BI-2-REV2.Qxd 6/29/07 9:55 PM Page 30
ATA July BI-2-REV2.qxd 6/29/07 9:55 PM Page 30 Nigerian 419 E-Mail Scams By Keiran Dunne Continuing the series on cyber security that began in the April 2007 issue of The ATA Chronicle, this Taking full advantage of modern communications article will focus on e-mail messages that attempt to defraud innocent vic- technology, perpetrators indiscriminately send large tims using variants of the so-called “Nigerian 419 scam,” a form of fraud volumes of e-mail “invitations” to anonymous named after the section of the Nigerian penal code that it violates. potential “investors.” The 419 Scam: Advance Fee Fraud by Another Name Advance fee fraud is a variation of your account?’ The sums involved costs, or a requirement that the a centuries-old confidence trick are usually in the millions of dol- “investor” must have a certain amount whereby victims are persuaded to pro- lars, and the investor is promised a of money on deposit in an interna- vide money with the promise of real- large share, often 40%. The pro- tional bank in order to process the izing substantially larger returns.1 posed deal is often presented as a transaction, and so forth. Whatever Taking full advantage of modern com- ‘harmless’ white-collar crime, in the reason, once the money is munications technology, perpetrators order to dissuade participants from advanced to the 419 scammer(s), it is indiscriminately send large volumes later contacting the authorities. never seen again and the transaction is of e-mail “invitations” to anonymous Similarly, the money is often said to never concluded. -

Other People's Money
Other people’s money Marcus Killick – CEO Gibrlatar FSC Gibraltar magazine February 2008 Some claim that all of literature can be distilled into seven basic plots. These are: overcoming the monster; rags to riches; the quest; voyage and return; comedy; tragedy; rebirth. The financial services frauds that the average person may fall victim to similarly fall into a few basic categories. The details may vary but these techniques have held true throughout the years. Whilst the newspapers focus on large scale frauds, many fraudsters deliberately go for small amounts from large numbers. They do this both to reduce the risk of detection and rely on the victim being too embarrassed at their own perceived stupidity to report the matter. As can be seen from some of the tricks below they may also allude to the enterprise being in some way illegal (for example a tax or exchange control evasion vehicle) so also deterring the victim from reporting the matter to the authorities for fear of getting themselves into trouble. Now to the scams 1) The pyramid scheme There are a number of types of pyramid scheme. The traditional versions all share one overriding characteristic. They promise consumers or investors large profits based primarily on recruiting others to join their program rather than being based on profits from any real investment or real sale of goods to the public. According to the US federal Trades Commission (FTC), there are two tell-tale signs that a product is simply being used to disguise a pyramid scheme: inventory loading and a lack of retail sales. -

Identity Theft 7
1 2 DOWNEASTER COMMON SENSE GUIDE GONE PHISING JANET T. MILLS ANNE L. HEAD GOVERNOR COMMISSIONER WILLIAM N. LUND SUPERINTENDENT 3 Maine Bureau of Consumer Credit Protection Toll-free Maine Consumer Assistance Maine Foreclosure Prevention Hotline 1-800-332-8529 (1-800-DEBT-LAW) 1-888-NO-4-CLŌZ TTY users call Maine relay 711 (1-888-664-2569) www.Credit.Maine.gov The Maine Bureau of Consumer Credit Protection was established in 1975 to enforce a wide variety of consumer financial protection laws, including: -Consumer Credit Code -Truth-in-Lending Act -Fair Credit Billing Act -Truth-in-Leasing Act -Fair Credit Reporting Act -Fair Debt Collection Practices Act -“Plain Language” Contract Law The Bureau conducts periodic examinations of creditors to determine compliance with these laws, responds to consumer complaints and inquiries, and operates the state’s foreclosure prevention hotline and housing counselor referral program. The Bureau also conducts educational seminars and provides speakers to advise consumers and creditors of their legal rights and responsibilities. William N. Lund Superintendent July 2014 DOWNEASTER COMMON SENSE GUIDE: GONE PHISHING IDENTIFYING AND AVOIDING CONSUMER SCAMS By David Leach, MPA and Steven Lemieux, MBA Cover Design: Edward Myslik Copyright © 2014 Bureau of Consumer Credit Protection, State of Maine The contents of this book may be reprinted, with attribution. Maine residents can obtain additional free copies of this booklet by contacting the Bureau of Consumer Credit Protection at 207-624-8527 or toll-free at 1-800-332-8529. Non-Maine residents may purchase the publication for $6 per copy, or at a volume discount of $4 per copy on orders of 50 or more. -
Brought to You by CFCU Community Credit Union TWISTS of FAKE New and Time-Tested Threats to Your Identity
Brought to you by CFCU Community Credit Union TWISTS OF FAKE New and time-tested threats to your identity Welcome to the scammer’s worst nightmare: this eBook! Within these pages, you’ll find tips on identity theft prevention, information on the most popular and prevalent scams, methods for safeguarding your personal information and much more. Read it now, and save it for further reference. Here at your credit union, we want to help you maintain your peace of mind and financial security! TABLE OF CONTENTS An Ounce of Prevention E-Statements: Safer than Paper Statements? 1 Keep Your Social Security Cards Secure 2 Identity Theft Prevention: Shredding 3 Secure Your Social Security Number 4 Going Away for the Holidays? Don’t Announce It Online … Until You’re Back 5 Shoulder Surfing 6 Handle It At Once 7 Safely Shopping Online 8 Financial Self-Defense: Diversify! 9 A Growing Threat To Small Businesses 11 Vacation Rental Scam 13 House Stealing 14 Fax Machines 15 Fake Job Listings 16 Online Safety 17 Check Fraud 18 Medical Identity Theft 19 Identity Theft Insurance 20 High Tech – Low Morals Beta Bots, Malware and Scams 21 Beyond The Password – Why We Need Better Computer Security 22 Pinterest Scams: Protect Yourself 24 Identity Theft And Technology – Including Social Media 26 Are You Inviting Thieves At Social Networking Sites? 28 Online Scams 29 Online Banking: Is it Safe? 30 Identity Theft: Storing Passwords 31 Identity Theft: Creating Passwords 32 The Importance Of Antivirus Software 33 How ‘Spoofing’ Can Happen From Legitimate Websites 34 Peer-To-Peer