IRIX® Admin: Networking and Mail
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Introduction to Command Line and Accessing Servers Remotely
Introduction to command line and accessing servers remotely Marco Büchler, Emily Franzini, Greta Franzini, Maria Moritz eTRAP Research Group Göttingen Centre for Digital Humanities Institute of Computer Science Georg August University Göttingen, Germany DH Estonia 2015 - Text Reuse Hackathon 20. Oktober 2015 Who am I? • 2001/2 Head of Quality Assurance department in a software company • 2006 Diploma in Computer Science on big • scale co-occurrence analysis • 2007- Consultant for several SMEs in IT sector • 2008 Technical project management of eAQUA project • 2011 PI and project manager of eTRACES project • 2013 PhD in „Digital Humanities“ on Text Reuse • 2014- Head of Early Career Research Group eTRAP at Göttingen Centre for Digital Humanities DH Estonia 2015 - Text Reuse Hackathon 20. Oktober 2015 Agenda 1) Connecting to the server 2) Some command line introduction DH Estonia 2015 - Text Reuse Hackathon 20. Oktober 2015 Connecting to the server 1) Windows: Start Putty 2) Mac + Linux: Open a terminal 3) Connecting to server via ssh -l <login> 192.168.11.4 4) Enter password DH Estonia 2015 - Text Reuse Hackathon 20. Oktober 2015 Which folder am I on the server? Command: pwd (parent working directory) Usage: pwd <ENTER> Example: pwd <ENTER> DH Estonia 2015 - Text Reuse Hackathon 20. Oktober 2015 Which files and directories are contained in my pwd? Command: ls (list) Usage: ls -l <FOLDER> <ENTER> // list all files and directory one on each line ls -la <FOLDER> <ENTER> // show also hidden files ls -lh <FOLDER> <ENTER> // show e.g. files sizes in human- friendly version Example: ls -l <ENTER> ls -lh /home/mbuechler <ENTER> DH Estonia 2015 - Text Reuse Hackathon 20. -
The Challenges of Dynamic Network Interfaces
The Challenges of Dynamic Network Interfaces by Brooks Davis brooks@{aero,FreeBSD}.org The Aerospace Corporation The FreeBSD Project EuroBSDCon 2004 October 29-31, 2004 Karlsruhe, Germany Introduction ● History of Dynamic Interfaces ● Problems ● Possible Solutions ● Advice to Implementors ● Future Work Early UNIX ● Totally static. ● All devices must be compiled in to kernel ● Fast and easy to program ● Difficult to maintain as the number of devices grows Autoconfiguration ● Introduced in 4.1BSD (June 1981) ● One kernel can serve multiple hardware configurations ● Probe – Test for existence of devices, either using stored addresses or matching devices on self-identifying buses ● Attach – Allocate a driver instance (as of 6.0, this must be fully dynamic) Kernel Modules ● Allows drivers to be added at run time ● LKM (Loadable Kernel Modules) – Introduced in 2.0 by Terry Lambert – Modeled after the facility in SunOS ● KLD (dynamic kernel linker) – Introduced along with newbus in 3.0 by Doug Rabson – Added a generic if_detach() function PC Card & CardBus ● Initial PC Card (PCMCIA) support via PAO in 2.0 ● Fairly good support in 3.0 ● Most PAO changes merged in 4.0 – PAO development ceased ● CardBus support in 5.0 Other Removable Devices ● USB Ethernet (4.0) ● Firewire (fwe(4) in 4.8, fwip(4) in 5.3) ● Bluetooth (5.2) ● Hot plug PCI ● Compact PCI ● PCI Express ● Express Card Netgraph ● Node implement network functions ● Arbitrary connection of nodes allowed ● ng_iface(4) node creates interfaces on demand Interface Cloning ● Handles most pseudo -

Download the Specification
Internationalizing and Localizing Applications in Oracle Solaris Part No: E61053 November 2020 Internationalizing and Localizing Applications in Oracle Solaris Part No: E61053 Copyright © 2014, 2020, Oracle and/or its affiliates. License Restrictions Warranty/Consequential Damages Disclaimer This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in your license agreement or allowed by law, you may not use, copy, reproduce, translate, broadcast, modify, license, transmit, distribute, exhibit, perform, publish, or display any part, in any form, or by any means. Reverse engineering, disassembly, or decompilation of this software, unless required by law for interoperability, is prohibited. Warranty Disclaimer The information contained herein is subject to change without notice and is not warranted to be error-free. If you find any errors, please report them to us in writing. Restricted Rights Notice If this is software or related documentation that is delivered to the U.S. Government or anyone licensing it on behalf of the U.S. Government, then the following notice is applicable: U.S. GOVERNMENT END USERS: Oracle programs (including any operating system, integrated software, any programs embedded, installed or activated on delivered hardware, and modifications of such programs) and Oracle computer documentation or other Oracle data delivered to or accessed by U.S. Government end users are "commercial -

CIS 90 - Lesson 2
CIS 90 - Lesson 2 Lesson Module Status • Slides - draft • Properties - done • Flash cards - NA • First minute quiz - done • Web calendar summary - done • Web book pages - gillay done • Commands - done • Lab tested – done • Print latest class roster - na • Opus accounts created for students submitting Lab 1 - • CCC Confer room whiteboard – done • Check that headset is charged - done • Backup headset charged - done • Backup slides, CCC info, handouts on flash drive - done 1 CIS 90 - Lesson 2 [ ] Has the phone bridge been added? [ ] Is recording on? [ ] Does the phone bridge have the mike? [ ] Share slides, putty, VB, eko and Chrome [ ] Disable spelling on PowerPoint 2 CIS 90 - Lesson 2 Instructor: Rich Simms Dial-in: 888-450-4821 Passcode: 761867 Emanuel Tanner Merrick Quinton Christopher Zachary Bobby Craig Jeff Yu-Chen Greg L Tommy Eric Dan M Geoffrey Marisol Jason P David Josh ? ? ? ? Leobardo Gabriel Jesse Tajvia Daniel W Jason W Terry? James? Glenn? Aroshani? ? ? ? ? ? ? = need to add (with add code) to enroll in Ken? Luis? Arturo? Greg M? Ian? this course Email me ([email protected]) a relatively current photo of your face for 3 points extra credit CIS 90 - Lesson 2 First Minute Quiz Please close your books, notes, lesson materials, forum and answer these questions in the order shown: 1. What command shows the other users logged in to the computer? 2. What is the lowest level, inner-most component of a UNIX/Linux Operating System called? 3. What part of UNIX/Linux is both a user interface and a programming language? email answers to: [email protected] 4 CIS 90 - Lesson 2 Commands Objectives Agenda • Understand how the UNIX login • Quiz operation works. -
Linux Software User's Manual
New Generation Systems (NGS) Linux Software User’s Manual Version 1.0, September 2019 www.moxa.com/product © 2019 Moxa Inc. All rights reserved. New Generation Systems (NGS) Linux Software User’s Manual The software described in this manual is furnished under a license agreement and may be used only in accordance with the terms of that agreement. Copyright Notice © 2019 Moxa Inc. All rights reserved. Trademarks The MOXA logo is a registered trademark of Moxa Inc. All other trademarks or registered marks in this manual belong to their respective manufacturers. Disclaimer Information in this document is subject to change without notice and does not represent a commitment on the part of Moxa. Moxa provides this document as is, without warranty of any kind, either expressed or implied, including, but not limited to, its particular purpose. Moxa reserves the right to make improvements and/or changes to this manual, or to the products and/or the programs described in this manual, at any time. Information provided in this manual is intended to be accurate and reliable. However, Moxa assumes no responsibility for its use, or for any infringements on the rights of third parties that may result from its use. This product might include unintentional technical or typographical errors. Changes are periodically made to the information herein to correct such errors, and these changes are incorporated into new editions of the publication. Technical Support Contact Information www.moxa.com/support Moxa Americas Moxa China (Shanghai office) Toll-free: 1-888-669-2872 Toll-free: 800-820-5036 Tel: +1-714-528-6777 Tel: +86-21-5258-9955 Fax: +1-714-528-6778 Fax: +86-21-5258-5505 Moxa Europe Moxa Asia-Pacific Tel: +49-89-3 70 03 99-0 Tel: +886-2-8919-1230 Fax: +49-89-3 70 03 99-99 Fax: +886-2-8919-1231 Moxa India Tel: +91-80-4172-9088 Fax: +91-80-4132-1045 Table of Contents 1. -

Introduzione Al Mondo Freebsd
Introduzione al mondo FreeBSD Corso avanzato Netstudent Netstudent http://netstudent.polito.it E.Richiardone [email protected] maggio 2009 CC-by http://creativecommons.org/licenses/by/2.5/it/ The FreeBSD project - 1 ·EÁ un progetto software open in parte finanziato ·Lo scopo eÁ mantenere e sviluppare il sistema operativo FreeBSD ·Nasce su CDROM come FreeBSD 1.0 nel 1993 ·Deriva da un patchkit per 386BSD, eredita codice da UNIX versione Berkeley 1977 ·Per problemi legali subisce un rallentamento, release 2.0 nel 1995 con codice royalty-free ·Dalla release 5.0 (2003) assume la struttura che ha oggi ·Disponibile per x86 32 e 64bit, ia64, MIPS, ppc, sparc... ·La mascotte (Beastie) nasce nel 1984 The FreeBSD project - 2 ·Erede di 4.4BSD (eÁ la stessa gente...) ·Sistema stabile; sviluppo uniforme; codice molto chiaro, ordinato e ben commentato ·Documentazione ufficiale ben curata ·Licenza molto permissiva, spesso attrae aziende per progetti commerciali: ·saltuariamente esterni collaborano con implementazioni ex-novo (i.e. Intel, GEOM, atheros, NDISwrapper, ZFS) ·a volte no (i.e. Windows NT) ·Semplificazione di molte caratteristiche tradizionali UNIX Di cosa si tratta Il progetto FreeBSD include: ·Un sistema base ·Bootloader, kernel, moduli, librerie di base, comandi e utility di base, servizi tradizionali ·Sorgenti completi in /usr/src (~500MB) ·EÁ giaÁ abbastanza completo (i.e. ipfw, ppp, bind, ...) ·Un sistema di gestione per software aggiuntivo ·Ports e packages ·Documentazione, canali di assistenza, strumenti di sviluppo ·i.e. Handbook, -

Programming IBM PASE for I 7.1
IBM IBM i Programming IBM PASE for i 7.1 IBM IBM i Programming IBM PASE for i 7.1 Note Before using this information and the product it supports, be sure to read the information in “Notices,” on page 71. This edition applies to IBM AIX 6 Technology Level 1 and to IBM i 7.1 (product number 5770-SS1) and to all subsequent releases and modifications until otherwise indicated in new editions. This version does not run on all reduced instruction set computer (RISC) models nor does it run on CISC models. © Copyright IBM Corporation 2000, 2010. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents IBM PASE for i ............ 1 Using IBM PASE for i native methods from What's new for IBM i 7.1 .......... 1 Java ............... 28 PDF file for IBM PASE for i ......... 2 Working with environment variables .... 28 IBM PASE for i overview .......... 3 Calling IBM i programs and procedures from IBM PASE for i concepts ......... 3 your IBM PASE for i programs ....... 29 IBM PASE for i as a useful option for application Calling ILE procedures ........ 29 development ............. 4 Examples: Calling ILE procedures .... 31 Installing IBM PASE for i .......... 5 Calling IBM i programs from IBM PASE for i 37 Planning for IBM PASE for i ......... 6 Example: Calling IBM i programs from Preparing programs to run in IBM PASE for i ... 7 IBM PASE for i .......... 37 Analyzing program compatibility with IBM PASE Running IBM i commands from IBM PASE for for i ............... -

The Challenges of Dynamic Network Interfaces
The Challenges of Dynamic Network Interfaces Brooks Davis The FreeBSD Project Seattle, WA brooks@{aero,FreeBSD}.org Abstract vices to the modern age of near complete dynamism. Following this history, the problems caused by this dynamism are discussed in detail. Then solutions to On early BSD systems, network interfaces were some of these problems are proposed and analyzed, static objects created at kernel compile time. To- and advice to implementers of userland applications day the situation has changed dramatically. PC is given. Finally, the issues are summarized and fu- Card, USB, and other removable buses allow hard- ture work is discussed. ware interfaces to arrive and depart at run time. Pseudo-device cloning also allows pseudo-devices to be created dynamically. Additionally, in FreeBSD and Dragonfly, interfaces can be renamed by the ad- 2 History ministrator. With these changes, interfaces are now dynamic objects which may appear, change, or dis- appear at any time. This dynamism invalidates a In early versions of UNIX, the exact set of devices number of assumptions that have been made in the on the system had to be compiled in to the kernel. If kernel, in external programs, and even in standards the administrator attempted to use a device which such as SNMP. This paper explores the history of was compiled in, but not installed, a panic or hang the transition of network interfaces from static to dy- was nearly certain. This system was easy to pro- namic. Issues raised by these changes are discussed gram and efficient to execute. Unfortunately, it was and possible solutions suggested. -
PC-BSD 9 Turns a New Page
CONTENTS Dear Readers, Here is the November issue. We are happy that we didn’t make you wait for it as long as for October one. Thanks to contributors and supporters we are back and ready to give you some usefull piece of knowledge. We hope you will Editor in Chief: Patrycja Przybyłowicz enjoy it as much as we did by creating the magazine. [email protected] The opening text will tell you What’s New in BSD world. It’s a review of PC-BSD 9 by Mark VonFange. Good reading, Contributing: especially for PC-BSD users. Next in section Get Started you Mark VonFange, Toby Richards, Kris Moore, Lars R. Noldan, will �nd a great piece for novice – A Beginner’s Guide To PF Rob Somerville, Erwin Kooi, Paul McMath, Bill Harris, Jeroen van Nieuwenhuizen by Toby Richards. In Developers Corner Kris Moore will teach you how to set up and maintain your own repository on a Proofreaders: FreeBSD system. It’s a must read for eager learners. Tristan Karstens, Barry Grumbine, Zander Hill, The How To section in this issue is for those who enjoy Christopher J. Umina experimenting. Speed Daemons by Lars R Noldan is a very good and practical text. By reading it you can learn Special Thanks: how to build a highly available web application server Denise Ebery with advanced networking mechanisms in FreeBSD. The Art Director: following article is the �nal one of our GIS series. The author Ireneusz Pogroszewski will explain how to successfully manage and commission a DTP: complex GIS project. -

Absolute BSD—The Ultimate Guide to Freebsd Table of Contents Absolute BSD—The Ultimate Guide to Freebsd
Absolute BSD—The Ultimate Guide to FreeBSD Table of Contents Absolute BSD—The Ultimate Guide to FreeBSD............................................................................1 Dedication..........................................................................................................................................3 Foreword............................................................................................................................................4 Introduction........................................................................................................................................5 What Is FreeBSD?...................................................................................................................5 How Did FreeBSD Get Here?..................................................................................................5 The BSD License: BSD Goes Public.......................................................................................6 The Birth of Modern FreeBSD.................................................................................................6 FreeBSD Development............................................................................................................7 Committers.........................................................................................................................7 Contributors........................................................................................................................8 Users..................................................................................................................................8 -
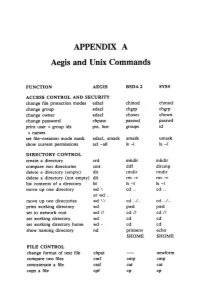
APPENDIX a Aegis and Unix Commands
APPENDIX A Aegis and Unix Commands FUNCTION AEGIS BSD4.2 SYSS ACCESS CONTROL AND SECURITY change file protection modes edacl chmod chmod change group edacl chgrp chgrp change owner edacl chown chown change password chpass passwd passwd print user + group ids pst, lusr groups id +names set file-creation mode mask edacl, umask umask umask show current permissions acl -all Is -I Is -I DIRECTORY CONTROL create a directory crd mkdir mkdir compare two directories cmt diff dircmp delete a directory (empty) dlt rmdir rmdir delete a directory (not empty) dlt rm -r rm -r list contents of a directory ld Is -I Is -I move up one directory wd \ cd .. cd .. or wd .. move up two directories wd \\ cd . ./ .. cd . ./ .. print working directory wd pwd pwd set to network root wd II cd II cd II set working directory wd cd cd set working directory home wd- cd cd show naming directory nd printenv echo $HOME $HOME FILE CONTROL change format of text file chpat newform compare two files emf cmp cmp concatenate a file catf cat cat copy a file cpf cp cp Using and Administering an Apollo Network 265 copy std input to std output tee tee tee + files create a (symbolic) link crl In -s In -s delete a file dlf rm rm maintain an archive a ref ar ar move a file mvf mv mv dump a file dmpf od od print checksum and block- salvol -a sum sum -count of file rename a file chn mv mv search a file for a pattern fpat grep grep search or reject lines cmsrf comm comm common to 2 sorted files translate characters tic tr tr SHELL SCRIPT TOOLS condition evaluation tools existf test test -

Converting a Hebrew Code Page CP1255 to the UTF-8 Format
LIBICONV – An Interface to Team Developer By Jean-Marc Gemperle Technical Support Engineer November, 2005 Abstract ..................................................................................... 3 Introduction............................................................................... 3 What Is LIBICONV?.................................................................... 4 Obtaining and Building LIBICONV for Win32.............................. 4 A DLL Interface to Team Developer............................................ 4 Team Developer ICONV Samples and Tests................................ 5 A Brief Description of the Application......................................... 6 Converting a Hebrew Code Page CP1255 to the UTF-8 Format................................................................................. 7 Converting the Generated UTF-8 Back to the CP1255 Hebrew Code Page .............................................................. 8 Chinese ISO-2022-CN-EXT to UTF-8 .................................... 9 ISO-8859-1 to DOS 437..................................................... 10 ISO-8859-1 to WINDOWS-1250 Cannot Convert ............... 11 ISO88591 to WINDOWS-1250 Using Translit .................... 11 Conclusions .............................................................................. 12 Abstract This technical white paper proposes an interface from GUPTA Team Developer to the GNU LIBICONV allowing a Team Developer programmer to convert their documents to a different form of encoding. See http://www.gnu.org/software/libiconv/