Cyber Threats to Mobile Phones Paul Ruggiero and Jon Foote
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
2020 Identity Theft Statistics | Consumeraffairs
2020 Identity Theft Statistics | ConsumerAffairs Trending Home / Finance / Identity Theft Protection / Identity theft statistics Buyers Guides Last Updated 01/16/2020 News Write a review 2020Write a review Identity theft statistics Trends and statistics about identity theft Learn about identity theft protection by Rob Douglas Identity Theft Protection Contributing Editor In 2018, the Federal Trade Commission processed 1.4 million fraud reports totaling $1.48 billion in losses. According to the FTC’s “Consumer Sentinel Network Data Book,” the most common categories for fraud complaints were imposter scams, debt collection and identity theft. Credit card fraud was most prevalent in identity theft cases — more than 167,000 people reported a fraudulent credit card account was opened with their information. Identity theft trends in 2019 In the next year, the Identity Theft Resource Center (ITRC) predicts identity theft protection services will primarily focus on data breaches, data abuse and data privacy. ITRC also predicts that https://www.consumeraffairs.com/finance/identity-theft-statistics.html 2020 Identity Theft Statistics | ConsumerAffairs consumers will become more knowledgeable about how data breaches work and expect companies to provide more information about the specific types of data breached and demand more transparency in general in data breach reports. Cyber attacks are more ambitious According to a 2019 Internet Security Threat Report by Symantec, cybercriminals are diversifying their targets and using stealthier methods to commit identity theft and fraud. Cybercrime groups like Mealybug, Gallmaker and Necurs are opting for off-the-shelf tools and operating system features such as PowerShell to attack targets. Supply chain attacks are up 78% Malicious PowerShell scripts have increased by 1,000% Microsoft Office files make up 48% of malicious email attachments Internet of Things threats on the rise Cybercriminals attack IoT devices an average of 5,233 times per month. -

We Are All Rwandans”
UNIVERSITY OF CALIFORNIA Los Angeles “We are all Rwandans”: Imagining the Post-Genocidal Nation Across Media A dissertation submitted in partial satisfaction of the requirements for the degree Doctor of Philosophy in Film and Television by Andrew Phillip Young 2016 ABSTRACT OF DISSERTATION “We are all Rwandans”: Imagining the Post-Genocidal Nation Across Media by Andrew Phillip Young Doctor of Philosophy in Film and Television University of California, Los Angeles, 2016 Professor Chon A. Noriega, Chair There is little doubt of the fundamental impact of the 1994 Rwanda genocide on the country's social structure and cultural production, but the form that these changes have taken remains ignored by contemporary media scholars. Since this time, the need to identify the the particular industrial structure, political economy, and discursive slant of Rwandan “post- genocidal” media has become vital. The Rwandan government has gone to great lengths to construct and promote reconciliatory discourse to maintain order over a country divided along ethnic lines. Such a task, though, relies on far more than the simple state control of media message systems (particularly in the current period of media deregulation). Instead, it requires a more complex engagement with issues of self-censorship, speech law, public/private industrial regulation, national/transnational production/consumption paradigms, and post-traumatic media theory. This project examines the interrelationships between radio, television, newspapers, the ii Internet, and film in the contemporary Rwandan mediascape (which all merge through their relationships with governmental, regulatory, and funding agencies, such as the Rwanda Media High Council - RMHC) to investigate how they endorse national reconciliatory discourse. -

Address Munging: the Practice of Disguising, Or Munging, an E-Mail Address to Prevent It Being Automatically Collected and Used
Address Munging: the practice of disguising, or munging, an e-mail address to prevent it being automatically collected and used as a target for people and organizations that send unsolicited bulk e-mail address. Adware: or advertising-supported software is any software package which automatically plays, displays, or downloads advertising material to a computer after the software is installed on it or while the application is being used. Some types of adware are also spyware and can be classified as privacy-invasive software. Adware is software designed to force pre-chosen ads to display on your system. Some adware is designed to be malicious and will pop up ads with such speed and frequency that they seem to be taking over everything, slowing down your system and tying up all of your system resources. When adware is coupled with spyware, it can be a frustrating ride, to say the least. Backdoor: in a computer system (or cryptosystem or algorithm) is a method of bypassing normal authentication, securing remote access to a computer, obtaining access to plaintext, and so on, while attempting to remain undetected. The backdoor may take the form of an installed program (e.g., Back Orifice), or could be a modification to an existing program or hardware device. A back door is a point of entry that circumvents normal security and can be used by a cracker to access a network or computer system. Usually back doors are created by system developers as shortcuts to speed access through security during the development stage and then are overlooked and never properly removed during final implementation. -

Image Steganography Applications for Secure Communication
IMAGE STEGANOGRAPHY APPLICATIONS FOR SECURE COMMUNICATION by Tayana Morkel Submitted in partial fulfillment of the requirements for the degree Master of Science (Computer Science) in the Faculty of Engineering, Built Environment and Information Technology University of Pretoria, Pretoria May 2012 © University of Pretoria Image Steganography Applications for Secure Communication by Tayana Morkel E-mail: [email protected] Abstract To securely communicate information between parties or locations is not an easy task considering the possible attacks or unintentional changes that can occur during communication. Encryption is often used to protect secret information from unauthorised access. Encryption, however, is not inconspicuous and the observable exchange of encrypted information between two parties can provide a potential attacker with information on the sender and receiver(s). The presence of encrypted information can also entice a potential attacker to launch an attack on the secure communication. This dissertation investigates and discusses the use of image steganography, a technology for hiding information in other information, to facilitate secure communication. Secure communication is divided into three categories: self-communication, one-to-one communication and one-to-many communication, depending on the number of receivers. In this dissertation, applications that make use of image steganography are implemented for each of the secure communication categories. For self-communication, image steganography is used to hide one-time passwords (OTPs) in images that are stored on a mobile device. For one-to-one communication, a decryptor program that forms part of an encryption protocol is embedded in an image using image steganography and for one-to-many communication, a secret message is divided into pieces and different pieces are embedded in different images. -

Espionage Against the United States by American Citizens 1947-2001
Technical Report 02-5 July 2002 Espionage Against the United States by American Citizens 1947-2001 Katherine L. Herbig Martin F. Wiskoff TRW Systems Released by James A. Riedel Director Defense Personnel Security Research Center 99 Pacific Street, Building 455-E Monterey, CA 93940-2497 REPORT DOCUMENTATION PAGE Form Approved OMB No. 0704-0188 The public reporting burden for this collection of information is estimated to average 1 hour per response, including the time for reviewing instructions, searching existing data sources, gathering and maintaining the data needed, and completing and reviewing the collection of information. Send comments regarding this burden estimate or any other aspect of this collection of information, including suggestions for reducing the burden, to Department of Defense, Washington Headquarters Services, Directorate for Information Operations and Reports (0704- 0188), 1215 Jefferson Davis Highway, Suite 1204, Arlington, VA 22202-4302. Respondents should be aware that notwithstanding any other provision of law, no person shall be subject to any penalty for failing to comply with a collection of information if it does not display a currently valid OMB control number. PLEASE DO NOT RETURN YOUR FORM TO THE ABOVE ADDRESS. 1. REPORT DATE (DDMMYYYY) 2. REPORT TYPE 3. DATES COVERED (From – To) July 2002 Technical 1947 - 2001 4. TITLE AND SUBTITLE 5a. CONTRACT NUMBER 5b. GRANT NUMBER Espionage Against the United States by American Citizens 1947-2001 5c. PROGRAM ELEMENT NUMBER 6. AUTHOR(S) 5d. PROJECT NUMBER Katherine L. Herbig, Ph.D. Martin F. Wiskoff, Ph.D. 5e. TASK NUMBER 5f. WORK UNIT NUMBER 7. PERFORMING ORGANIZATION NAME(S) AND ADDRESS(ES) 8. -

Social Engineering Exposures
Aon Risk Solutions Financial Services Group Client Alert: Social Engineering Exposures While social engineering can refer to many things outside of a risk management context, within the insurance world, social engineering has assumed a specific, and notable, meaning. In brief, social engineering refers to the use of identity deception to gain the confidence of an employee to induce him or her to part with an organization’s money or securities. We will explore some of the most common forms of social engineering, relevant coverage interpretations, and available coverage solutions. Where Does The Threat Arise From? While a “theft” has undoubtedly occurred in a We’re here to Social engineering attacks can come in many social engineering loss, the commercial crime empower results forms, including: policy likely has not been triggered because the If you have questions employee did not “steal” the money/securities about your specific § Phishing scams are attempts by fraudsters to coverage or want more directly, and the employee certainly did not induce individuals into providing personal information, please benefit from it. Historically, crime policies did not information such as bank account numbers, contact your Aon broker. explicitly address social engineering, thus resulting passwords, and credit card numbers aon.com in varying outcomes. § Spear phishing is an electronic communications scam targeted towards a specific individual, Relevant Cases organization, or business Although a few courts have found coverage for § Vishing, or voice phishing is the criminal social engineering losses under crime policies, practice of using social engineering over the most courts have found that social engineering telephone to gain access to private personal and losses are not covered under the policy’s financial information Computer Fraud, Funds Transfer Fraud, or Forgery § SMiShing (short for “SMS phishing”) is a coverage agreements. -

Image Steganography: Protection of Digital Properties Against Eavesdropping
Image Steganography: Protection of Digital Properties against Eavesdropping Ajay Kumar Shrestha Ramita Maharjan Rejina Basnet Computer and Electronics Engineering Computer and Electronics Engineering Computer and Electronics Engineering Kantipur Engineering College, TU Kantipur Engineering College, TU Kantipur Engineering College, TU Lalitpur, Nepal Lalitpur, Nepal Lalitpur, Nepal [email protected] [email protected] [email protected] Abstract—Steganography is the art of hiding the fact that Data encryption is basically a strategy to make the data communication is taking place, by hiding information in other unreadable, invisible or incomprehensible during transmission information. Different types of carrier file formats can be used, by scrambling the content of data. Steganography is the art but digital images are the most popular ones because of their and science of hiding information by embedding messages frequency on the internet. For hiding secret information in within seemingly harmless messages. It also refers to the images, there exists a large variety of steganography techniques. “Invisible” communication. The power of Steganography is in Some are more complex than others and all of them have hiding the secret message by obscurity, hiding its existence in respective strong and weak points. Many applications may a non-secret file. Steganography works by replacing bits of require absolute invisibility of the secret information. This paper useless or unused data in regular computer files. This hidden intends to give an overview of image steganography, it’s uses and information can be plaintext or ciphertext and even images. techniques, basically, to store the confidential information within images such as details of working strategy, secret missions, According to Bhattacharyya et al., “Steganography’s niche in criminal and confidential information in various organizations security is to supplement cryptography, not replace it. -

The Fourth Amendment's National Security Exception: Its History and Limits L
Vanderbilt Law Review Volume 66 | Issue 5 Article 1 10-2013 The ourF th Amendment's National Security Exception: Its History and Limits L. Rush Atkinson Follow this and additional works at: https://scholarship.law.vanderbilt.edu/vlr Part of the Fourth Amendment Commons Recommended Citation L. Rush Atkinson, The ourF th Amendment's National Security Exception: Its History and Limits, 66 Vanderbilt Law Review xi (2019) Available at: https://scholarship.law.vanderbilt.edu/vlr/vol66/iss5/1 This Article is brought to you for free and open access by Scholarship@Vanderbilt Law. It has been accepted for inclusion in Vanderbilt Law Review by an authorized editor of Scholarship@Vanderbilt Law. For more information, please contact [email protected]. The Fourth Amendment's National Security Exception: Its History and Limits L. Rush Atkinson 66 Vand. L. Rev. 1343 (2013) Each year, federal agents conduct thousands of "national security investigations" into suspected spies, terrorists, and other foreign threats. The constitutional limits imposed by the Fourth Amendment, however, remain murky, and the extent to which national security justifies deviations from the Amendment's traditional rules is unclear. With little judicial precedent on point, the gloss of past executive practice has become an important means for gauging the boundaries of today's national security practices. Accounts of past executive practice, however, have thus far been historically incomplete, leading to distorted analyses of its precedential significance. Dating back to World War II, national security investigations have involved warrantless surveillance and searches-conduct clearly impermissible in the traditional law-enforcement context- authorized under the theory of a "national security" or "foreign intelligence" exception to the Fourth Amendment. -
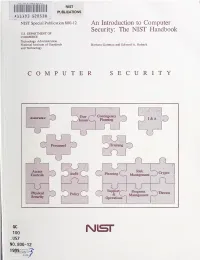
An Introduction to Computer Security: the NIST Handbook U.S
HATl INST. OF STAND & TECH R.I.C. NIST PUBLICATIONS AlllOB SEDS3fl NIST Special Publication 800-12 An Introduction to Computer Security: The NIST Handbook U.S. DEPARTMENT OF COMMERCE Technology Administration National Institute of Standards Barbara Guttman and Edward A. Roback and Technology COMPUTER SECURITY Contingency Assurance User 1) Issues Planniii^ I&A Personnel Trairang f Access Risk Audit Planning ) Crypto \ Controls O Managen»nt U ^ J Support/-"^ Program Kiysfcal ~^Tiireats Policy & v_ Management Security Operations i QC 100 Nisr .U57 NO. 800-12 1995 The National Institute of Standards and Technology was established in 1988 by Congress to "assist industry in the development of technology . needed to improve product quality, to modernize manufacturing processes, to ensure product reliability . and to facilitate rapid commercialization ... of products based on new scientific discoveries." NIST, originally founded as the National Bureau of Standards in 1901, works to strengthen U.S. industry's competitiveness; advance science and engineering; and improve public health, safety, and the environment. One of the agency's basic functions is to develop, maintain, and retain custody of the national standards of measurement, and provide the means and methods for comparing standards used in science, engineering, manufacturing, commerce, industry, and education with the standards adopted or recognized by the Federal Government. As an agency of the U.S. Commerce Department's Technology Administration, NIST conducts basic and applied research in the physical sciences and engineering, and develops measurement techniques, test methods, standards, and related services. The Institute does generic and precompetitive work on new and advanced technologies. NIST's research facilities are located at Gaithersburg, MD 20899, and at Boulder, CO 80303. -
Signals Intelligence in the Public Domain
Perspective C O R P O R A T I O N Expert insights on a timely policy issue SIGINT for Anyone The Growing Availability of Signals Intelligence in the Public Domain Cortney Weinbaum, Steven Berner, and Bruce McClintock IGINT, or signals intelligence, is intelligence gathered government-only paradigm. We identified ways these capabilities from communications, electronics, or foreign instrumen- and trends may impact the U.S. government in terms of emerging Station1 and has traditionally been considered an inher- threats, policy implications, technology repercussions, human capi- ently governmental function. Historically, only govern- tal considerations, and financial effects. Finally, we identified areas ment had the financial means and the legal authority to conduct for future study for U.S. and allied government leaders to respond SIGINT activities, and, in our experience, many members of to these changes. the U.S. government still hold this opinion today. We tested this During our market scan, we found examples of SIGINT viewpoint by conducting a market scan to seek examples of how capabilities outside of government that are available to anyone. The new technologies, innovations, and behaviors are challenging the capabilities we found have applications in maritime domain aware- existing government-only paradigm. We examined the breadth of ness; radio frequency (RF) spectrum mapping; eavesdropping, jam- technologies available now and reported to be released in the near ming, and hijacking of satellite communications; and cyber surveil- future to understand the capabilities each provides, which audience lance. Most of these capabilities are commercially available, many or market each serves, and what implications each may have for are free, and some are illegal. -

Types of Fraud
Types of Fraud Phishing A form of identity theft in which a scammer uses an authentic-looking e-mail to trick recipients into giving out sensitive personal information, such as a credit card numbers, bank account numbers, Social Security numbers or other sensitive personal information. Vishing Voice phishing is the criminal practice of using social engineering over the telephone system, most often using features facilitated by Voice over IP (VoIP), to gain access to private personal and financial information from the public for the purpose of financial reward. The term is a combination of "voice" and phishing. Voice phishing exploits the public's trust in landline telephone services, which have traditionally terminated in physical locations known to the telephone company, and associated with a bill-payer. The victim is often unaware that VoIP makes formerly difficult-to-abuse tools/features of caller ID spoofing, complex automated systems (IVR), low cost, and anonymity for the bill-payer widely available. Voice phishing is typically used to steal credit card numbers or other information used in identity theft schemes from individuals. SMiShing In computing, SMS phishing or smishing is a form of criminal activity using social engineering techniques. Phishing is the act of attempting to acquire personal information such as passwords and credit card details by masquerading as a trustworthy entity in an electronic communication. SMS (Short Message Service) is the technology used for text messages on cell phones. SMS phishing uses cell phone text messages to deliver the bait to induce people to divulge their personal information. The hook (the method used to actually capture people's information) in the text message may be a website URL, but it has become more common to see a telephone number that connects to an automated voice response system. -

Eavesdropping and Modification
York 978-1-59749-547-9 00003 CHAPTER Eavesdropping and c0020 Modifi cation 3 INFORMATION IN THIS CHAPTER • Anatomy of Eavesdropping and Modifi cation Attacks p0010 • Dangers of Eavesdropping and Modifi cation Attacks p0015 • The Future of Eavesdropping and Modifi cation Attacks p0020 • How to Defend against Eavesdropping and Modifi cation Attacks p0025 Imagine that somewhere within your IT organization you have someone with too p0030 much time on his or her hands or who has issues with the way current management is running things…or hates his job…or dislikes her boss…. Whatever the reason may be, he or she is in a position with access to the core Internet Protocol (IP) network running through your organization. Let’s give this person a name and call him Joe. One day, when working with Wireshark, the network protocol analyzer, Joe, notices the menu item Telephony | VoIP Calls . In trying it out, he discovers that…ta da… AQ1 he can listen to any call going to and from the IP-Private branch exchange (PBX). Naturally, he starts fi guring out how to listen in to the more interesting calls, and in particular to target calls to and from the CEO. Once he is able to isolate these calls, he automates his setup a bit. He fi nds a number of other tools and writes a script so that any calls to or from the CEO are saved to disk and converted into MP3 fi les. He then downloads those fi les onto his iPod and can listen to corporate conversations on his daily commute to and from work.