North Korean Strategic Strategy: Combining Conventional Warfare with The
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Digital Trenches
Martyn Williams H R N K Attack Mirae Wi-Fi Family Medicine Healthy Food Korean Basics Handbook Medicinal Recipes Picture Memory I Can Be My Travel Weather 2.0 Matching Competition Gifted Too Companion ! Agricultural Stone Magnolia Escpe from Mount Baekdu Weather Remover ERRORTelevision the Labyrinth Series 1.25 Foreign apps not permitted. Report to your nearest inminban leader. Business Number Practical App Store E-Bookstore Apps Tower Beauty Skills 2.0 Chosun Great Chosun Global News KCNA Battle of Cuisine Dictionary of Wisdom Terms DIGITAL TRENCHES North Korea’s Information Counter-Offensive DIGITAL TRENCHES North Korea’s Information Counter-Offensive Copyright © 2019 Committee for Human Rights in North Korea Printed in the United States of America All rights reserved. No part of this publication may be reproduced, distributed, or transmitted in any form or by any means, including photocopying, recording, or other electronic or mechanical methods, without the prior permission of the Committee for Human Rights in North Korea, except in the case of brief quotations embodied in critical reviews and certain other noncommercial uses permitted by copyright law. Committee for Human Rights in North Korea 1001 Connecticut Avenue, NW, Suite 435 Washington, DC 20036 P: (202) 499-7970 www.hrnk.org Print ISBN: 978-0-9995358-7-5 Digital ISBN: 978-0-9995358-8-2 Library of Congress Control Number: 2019919723 Cover translations by Julie Kim, HRNK Research Intern. BOARD OF DIRECTORS Gordon Flake, Co-Chair Katrina Lantos Swett, Co-Chair John Despres, -

North Korea's SA
JUNE 1, 2020 North Korea’s Strategic Situational Awareness Capabilities A Country Primer BY JASON ARTERBURN Executive Summary North Korea’s developing strategic situational awareness (SA) capabilities incorporate technologies that could introduce new risks in a conflict or crisis on the Korean Peninsula. North Korea possesses multifaceted command, control, communications, computers, intelligence, surveillance, and reconnaissance (C4ISR) systems that support a range of provocative asymmetric operations, including but not limited to GPS jamming, communications spoofing, cyberespionage, and cyberattacks. 1 While North Korea has rapidly developed its domestic telecommunications infrastructure and advanced computing capability in recent years, its systems continue to face technical and operational limitations that may constrain North Korea’s SA in engagements across the spectrum of conflict. This report synthesizes publicly available information on North Korea’s C4ISR systems and capabilities in order to consider how technology could affect escalatory dynamics or crisis stability during conflict in East Asia. The author prioritized primary sources from North Korean institutions or companies, official reports from governments, technical reports from specialist research firms, and articles from English-, Korean-, and Chinese-language media.2 Wherever possible, the author also attempted to corroborate information across multiple sources in different languages. Because the public domain contains little information on North Korea’s C4ISR equipment, -

The Dprk As an Example of the Potential Utility of Internet Sanctions
\\server05\productn\B\BIN\25-1\BIN104.txt unknown Seq: 1 31-MAR-08 10:18 USING INTERNET “BORDERS” TO COERCE OR PUNISH: THE DPRK AS AN EXAMPLE OF THE POTENTIAL UTILITY OF INTERNET SANCTIONS BENJAMIN BROCKMAN-HAW E * INTRODUCTION ................................................... 163 R I. BACKGROUND INFORMATION .............................. 166 R A. Escalation ............................................. 167 R B. The Internet in North Korea ........................... 173 R II. SANCTIONS ................................................ 181 R A. General Information ................................... 182 R B. Telecommunications Sanctions Already Considered .... 184 R C. Multilateral Sanctions In Place Against the DPRK ..... 187 R III. THE UTILITY OF INTERNET SANCTIONS .................... 187 R A. Obtaining a desired result through the imposition of Internet sanctions ...................................... 187 R B. The Benefits and Costs of Imposing Internet Sanctions . 198 R C. General Concerns Associated with the Use of Internet Sanctions .............................................. 200 R 1. International Human Rights ....................... 200 R 2. Internet sanctions could harm regime opponents . 203 R 3. Internet sanctions could impair the ability of UN operations and NGO’s to function within the target country ..................................... 204 R IV. CONCLUSION .............................................. 205 R INTRODUCTION Speech is civilization itself. The word. preserves contact—it is silence which isolates. - Thomas Mann1 * J.D. Candidate 2008, Boston University School of Law. This article is dedicated to the memory of Dr. Robert Brockman, a man who surveyed this new world with the eyes of an old soul. 1 THOMAS MANN, THE MAGIC MOUNTAIN (1924) quoted in CHARLES R. BURGER & JAMES J. BRADAC, LANGUAGE AND SOCIAL KNOWLEDGE 112 (Edward Arnold Publishers Ltd. 1982). 163 \\server05\productn\B\BIN\25-1\BIN104.txt unknown Seq: 2 31-MAR-08 10:18 164 BOSTON UNIVERSITY INTERNATIONAL LAW JOURNAL [Vol. -
1:14-Mc-00648-UNA Document 7 Filed 07/29/14 Page 1 of 3
Case 1:14-mc-00648-UNA Document 7 Filed 07/29/14 Page 1 of 3 IN THE UNITED STATES DISTRICT COURT FOR THE DISTRICT OF COLUMBIA Ruth Calderon-Cardona, et al., ) ) Plaintiffs, ) ) v. ) CIVIL ACTION NO. 14-mc-648 ) Democratic People's Republic of Korea, et ) HEARING REQUEST al., ) ) Defendants. ) ) ) INTERNET CORPORATION FOR ASSIGNED NAME AND NUMBERS’ MOTION TO QUASH WRIT OF ATTACHMENT The Internet Corporation for Assigned Names and Numbers (“ICANN”), a non-party, by counsel, respectfully moves this Court to quash the Writ of Attachment on Judgment Other Than Wages, Salary And Commissions (“Writ of Attachment”) issued by Plaintiffs in the above- entitled action, for the reasons set forth in ICANN’s accompanying Memorandum.1 Furthermore, ICANN, in accordance with Local Civil Rule 78.1, requests that an oral hearing be scheduled to inform the Court’s ruling on the Motion. 1 Plaintiffs issued to ICANN, and ICANN is moving to quash, writs of attachment in seven actions: (1) Rubin, et al. v. Islamic Republic of Iran, et al., Case No. 01-1655-RMU; (2) Haim, et al. v. Islamic Republic of Iran, et al., Case No. 02-1811-RCL; (3) Haim, et al. v. Islamic Republic of Iran, et al., Case No. 08-520-RCL; (4) Stern, et al. v. Islamic Republic of Iran, et al., Case No. 00-2602-RCL; (5) Weinstein, et al. v. Islamic Republic of Iran, et al., Case No. 00- 2601-RCL; (6) Wyatt, et al. v. Syrian Arab Republic, et al., Case No. 08-502-RCL; and (7) Calderon-Cardona, et al. -

Generic Top-Level Domains (Gtld)
An essential pillar for any business is its brand. Brand presence on the Web is a key factor in a business appearing in Internet searches and being found by existing and prospective customers. For small business owners, the essential ingredients for building a strong brand are: o A memorable business name o brand identity elements: o domain name o logo o email address o business card o social Web presence ( Linkedin, Facebook, Twitter, et Generic Top-Level Domains (gTLD) The following table represents the generic top-level domains (i.e. including .com, .org, etc). Domain Purpose / Sponsoring Organization Generic top-level domain .COM VeriSign Global Registry Services Generic top-level domain .INFO Afilias Limited Generic top-level domain .NET VeriSign Global Registry Services Generic top-level domain .ORG Public Interest Registry (PIR) Generic-Restricted Top-Level Domains Generic-restricted top-level domain names are similar to the generic top-level domains, only eligibility is intended to be restricted and ascertained more stringently. Domain Purpose / Sponsoring Organization Restricted for Business .BIZ NeuStar, Inc. Reserved for individuals .NAME The Global Name Registry Ltd. Restricted to credentialed professionals and related entities .PRO Registry Services Corporation dba RegistryPro Sponsored Top-Level Domains (sTLD) These domains are proposed and sponsored by private agencies or organizations that establish and enforce rules restricting the eligibility to use the TLD. IANA also groups sTLDs with the generic top-level domains. Domain Purpose / Sponsoring Organization Reserved for members of the air-transport industry .AERO Societe Internationale de Telecommunications Aeronautique S.C. (SITA SC) Restricted to the Pan-Asia and Asia Pacific community .ASIA DotAsia Organization Ltd. -

VBI Vulnerabilities Portfolio
VBI Vulnerabilities Portfolio October 28, 2013 <[email protected]> http://www.vulnbroker.com/ CONFIDENTIAL VBI Vulnerabilities Portfolio Contents 1 Foreword 6 1.1 Document Formatting.................................... 6 1.2 Properties and Definitions.................................. 6 1.2.1 Vulnerability Properties............................ 6 1.2.2 Vulnerability Test Matrix........................... 8 1.2.3 Exploit Properties............................... 8 2 Adobe Systems Incorporated 12 2.1 Flash Player......................................... 12 VBI-12-033 Adobe Flash Player Client-side Remote Code Execution........... 12 2.2 Photoshop CS6....................................... 15 VBI-13-011 Adobe Photoshop CS6 Client-side Remote Code Execution......... 15 3 Apple, Inc. 17 3.1 iOS.............................................. 17 VBI-12-036 Apple iOS Remote Forced Access-Point Association............. 17 VBI-12-037 Apple iOS Remote Forced Firmware Update Avoidance........... 18 4 ASUS 21 4.1 BIOS Device Driver..................................... 21 VBI-13-015 ASUS BIOS Device Driver Local Privilege Escalation............ 22 5 AVAST Software a.s. 24 5.1 avast! Anti-Virus...................................... 24 October 28, 2013 CONFIDENTIAL Page 1 of 120 VBI Vulnerabilities Portfolio VBI-13-005 avast! Local Information Disclosure..................... 24 VBI-13-010 avast! Anti-Virus Local Privilege Escalation................. 26 6 Barracuda Networks, Inc. 28 6.1 Web Filter.......................................... 28 VBI-13-000 -

North Korea: U.S. Relations, Nuclear Diplomacy, and Internal Situation Emma Chanlett-Avery, Coordinator Specialist in Asian Affairs
North Korea: U.S. Relations, Nuclear Diplomacy, and Internal Situation Emma Chanlett-Avery, Coordinator Specialist in Asian Affairs Ian E. Rinehart Analyst in Asian Affairs Mary Beth D. Nikitin Specialist in Nonproliferation January 15, 2016 Congressional Research Service 7-5700 www.crs.gov R41259 Summary North Korea has presented one of the most vexing and persistent problems in U.S. foreign policy in the post-Cold War period. The United States has never had formal diplomatic relations with the Democratic People’s Republic of Korea (the official name for North Korea), although since 2000 contact at a lower level has ebbed and flowed. Negotiations over North Korea’s nuclear weapons program have occupied the past three U.S. administrations, even as some analysts anticipated a collapse of the isolated authoritarian regime. North Korea has been the recipient of over $1 billion in U.S. aid (though none since 2009) and the target of dozens of U.S. sanctions. Negotiations over North Korea’s nuclear weapons program began in the early 1990s under the Clinton Administration. As U.S. policy toward Pyongyang evolved through the 2000s, the negotiations moved from a bilateral format to the multilateral Six-Party Talks (made up of China, Japan, Russia, North Korea, South Korea, and the United States). Although the talks reached some key agreements that laid out deals for aid and recognition to North Korea in exchange for denuclearization, major problems with implementation persisted. The talks have been suspended throughout the Obama Administration. As diplomacy remains stalled, North Korea continues to develop its nuclear and missile programs in the absence of any agreement it considers binding. -

North Korea Security Briefing
Companion report HP Security Briefing Episode 16, August 2014 Profiling an enigma: The mystery of North Korea’s cyber threat landscape HP Security Research Table of Contents Introduction .................................................................................................................................................... 3 Research roadblocks ...................................................................................................................................... 4 Ideological and political context .................................................................................................................... 5 Juche and Songun ...................................................................................................................................... 5 Tension and change on the Korean Peninsula .......................................................................................... 8 North Korean cyber capabilities and limitations ......................................................................................... 10 North Korean infrastructure.................................................................................................................... 10 An analysis of developments in North Korean cyberspace since 2010 .................................................. 14 North Korean cyber war and intelligence structure ................................................................................ 21 North Korean cyber and intelligence organizational chart .................................................................... -

CELL PHONES in NORTH KOREA Has North Korea Entered the Telecommunications Revolution?
CELL PHONES IN NORTH KOREA Has North Korea Entered the Telecommunications Revolution? Yonho Kim ABOUT THE AUTHOR Yonho Kim is a Staff Reporter for Voice of America’s Korea Service where he covers the North Korean economy, North Korea’s illicit activities, and economic sanctions against North Korea. He has been with VOA since 2008, covering a number of important developments in both US-DPRK and US-ROK relations. He has received a “Superior Accomplishment Award,” from the East Asia Pacific Division Director of the VOA. Prior to joining VOA, Mr. Kim was a broadcaster for Radio Free Asia’s Korea Service, focused on developments in and around North Korea and US-ROK alliance issues. He has also served as a columnist for The Pressian, reporting on developments on the Korean peninsula. From 2001-03, Mr. Kim was the Assistant Director of The Atlantic Council’s Program on Korea in Transition, where he conducted in-depth research on South Korean domestic politics and oversaw program outreach to US government and media interested in foreign policy. Mr. Kim has worked for Intellibridge Corporation as a freelance consultant and for the Hyundai Oil Refinery Co. Ltd. as a Foreign Exchange Dealer. From 1995-98, he was a researcher at the Hyundai Economic Research Institute in Seoul, focused on the international economy and foreign investment strategies. Mr. Kim holds a B.A. and M.A. in International Relations from Seoul National University and an M.A. in International Relations and International Economics from the Paul H. Nitze School of Advanced International Studies, Johns Hopkins University. -

North Korean Leadership Dynamics and Decision-Making Under Kim Jong-Un a Second Year Assessment
North Korean Leadership Dynamics and Decision-making under Kim Jong-un A Second Year Assessment Ken E. Gause Cleared for public release COP-2014-U-006988-Final March 2014 Strategic Studies is a division of CNA. This directorate conducts analyses of security policy, regional analyses, studies of political-military issues, and strategy and force assessments. CNA Strategic Studies is part of the glob- al community of strategic studies institutes and in fact collaborates with many of them. On the ground experience is a hallmark of our regional work. Our specialists combine in-country experience, language skills, and the use of local primary-source data to produce empirically based work. All of our analysts have advanced degrees, and virtually all have lived and worked abroad. Similarly, our strategists and military/naval operations experts have either active duty experience or have served as field analysts with operating Navy and Marine Corps commands. They are skilled at anticipating the “prob- lem after next” as well as determining measures of effectiveness to assess ongoing initiatives. A particular strength is bringing empirical methods to the evaluation of peace-time engagement and shaping activities. The Strategic Studies Division’s charter is global. In particular, our analysts have proven expertise in the follow- ing areas: The full range of Asian security issues The full range of Middle East related security issues, especially Iran and the Arabian Gulf Maritime strategy Insurgency and stabilization Future national security environment and forces European security issues, especially the Mediterranean littoral West Africa, especially the Gulf of Guinea Latin America The world’s most important navies Deterrence, arms control, missile defense and WMD proliferation The Strategic Studies Division is led by Dr. -

Discrepant Kisses: the Reception and Remediation of North Korean Children’S Performances Circulated on Social Media
Discrepant Kisses: The Reception and Remediation of North Korean Children’s Performances Circulated on Social Media DONNA LEE KWON Abstract This article explores the burgeoning realm of videos uploaded on YouTube generated from content produced in North Korea otherwise known as the DPRK (Democratic People’s Republic of Korea). Through state-sanctioned and individual channels, thousands of videos of North Korean music and dance have been uploaded, some resulting in over 57 million hits on YouTube. Taking a cue from this fascination, I employ digital ethnography to investigate the online reception and remediation of North Korean children’s performances alongside their online comments on YouTube. I also draw from fieldwork conducted in North Korea in 2007. Theories that espouse the democratic participatory effects of social media platforms do not apply in North Korea where most of the uploaded material is produced and controlled by the state. Given this, I argue that North Korea’s engagement with social media is marked by a profound disjuncture where the majority of videos portray ideological North Korean subjects in an online context where very few North Korean citizens are able to engage with this material as social media. I analyze how this disjuncture plays out as international users respond to and remediate these videos in various ways or by creating mash-ups that subvert their original ideological content. A young North Korean girl in a red, babydoll dress sings a song called “Kiss” (Ppo-ppo) [figure 1].1 Another girl, this time in white, extolls the virtues of the “King Potato” (Wang Kamja). Five North Korean boys and girls—noticeably dwarfed by their guitars—perform a song called “Our Kindergarten Teacher” (Yuch’iwŏn uri sŏnsaengnim) garnering over 57 million views on YouTube.2 All three of these memorable children’s performances have become subject to intense online reception and have generated various creative and discrepant remediations. -
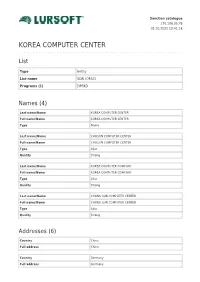
Korea Computer Center
Sanction catalogue 170.106.35.76 02.10.2021 12:41:16 KOREA COMPUTER CENTER List Type Entity List name SDN (OFAC) Programs (1) DPRK3 Names (4) Last name/Name KOREA COMPUTER CENTER Full name/Name KOREA COMPUTER CENTER Type Name Last name/Name CHOSON COMPUTER CENTER Full name/Name CHOSON COMPUTER CENTER Type Alias Quality Strong Last name/Name KOREA COMPUTER COMPANY Full name/Name KOREA COMPUTER COMPANY Type Alias Quality Strong Last name/Name CHUNG SUN COMPUTER CENTER Full name/Name CHUNG SUN COMPUTER CENTER Type Alias Quality Strong Addresses (6) Country China Full address China Country Germany Full address Germany Country Syria Full address Syria Country India Full address India Country United Arab Emirates Full address United Arab Emirates City Pyongyang Country North Korea Full address Pyongyang, Korea, North Identification documents (2) Type Secondary sanctions risk:: North Korea Sanctions Regulations, sections 510.201 and 510.210 Type Transactions Prohibited For Persons Owned or Controlled By U.S. Financial Institutions:: North Korea Sanctions Regulations section 510.214 Updated: 02.10.2021. 05:15 The Sanction catalog includes Latvian, United Nations, European Union, United Kingdom and Office of Foreign Assets Control subjects included in sanction list. © Lursoft IT 1997-2021 Lursoft is the re-user of information from the Enterprise Register of Latvia. The user is obliged to observe the Copyright law, Personal Data Processing Law requirements and Terms of Use of the Lursoft system. The user is forbidden to use any automatic systems or equipment (robots) in order to access the system without a written approval from Lursoft.