System Upgrade with Swupdate ELC 2017 02/2017
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Create an Email with Subject Title “Embedded Software Engineer”, Email a Copy of Your Resume to [email protected]
To Apply for This Position: Create an email with subject title “Embedded Software Engineer”, email a copy of your resume to [email protected] Location Address: ALLEN PARK, MI,48101 Position Description: TITLE: Embedded Software Engineer ‐ Hypervisor OS technologies This position is responsible to develop QNX and Android operating system images for Ford infotainment products. This includes creating and integrating code for: bootloader, kernel, drivers, type 1 hypervisor, and build environment. Skills Required: • Lead the design, bring‐up and support of QNX and Android operating system images • Create virt‐io drivers for QNX or Android guest operating systems • Participate in root cause analysis of hardware quality problems and software defects • Participate in system design, documentation, and testing to deliver a best‐in‐class infotainment system Experience Required: • 5+ years operating system experience involving Linux or QNX • 5+ years C/C++ software development experience on embedded, mobile, or consumer electronic platforms Experience Preferred: • Experience with Type 1 hypervisors • Experience creating virt‐io drivers • Mastery of C/C++ language, GNU tool chain, and Unix (QNX, Linux, or equivalent) • Experience with embedded build systems including QNX system builder, buildroot, yocto, or equivalent • Knowledge of in‐vehicle signaling and communication mechanisms such as CAN • Proficiency with revision control including Git, Subversion, or equivalent • Multi‐site software project team experience Education Required: • Bachelor's degree in Computer Engineering, Electrical Engineering, Computer Science, or related Education Preferred: • Master's degree in Computer Engineering, Electrical Engineering or Computer Science Additional Information: Web Based Assessment not required for this position. Visa Sponsorship and Domestic Relocation is available for this position. -

OS Selection for Dummies
OS SELECTION HOW TO CHOOSE HOW TO CHOOSE Choosing your OS is the first step, so take the time to consider your choice fully. There are many parameters to take into account: l Is this a new project or the evolution of an existing product? l Using the same SW stack? Re-using existing code? l Is your team familiar with a particular OS? Ø Using an OS you are already comfortable with can help l What are the HW constraints of your system? Ø Some operating systems require more memory/processing power than others l Have no SW team? Not sure about the above? Ø Contact us so we can help you decide! Ø We can also introduce you to one of our many partners! 1 OS SELECTION OPEN SOURCE VS. COMMERCIAL OS Embedded OS BSP Provider $ Cost Open-Source OS Boundary Devices • Embedded Linux / Android Embedded Linux $0, included • Large pool of developers available with Board Purchase • Strong community • Royalty-free And / or partners 3rd Party - Commercial OS Partners • QNX / Win10 IoT / Green Hills $>0, depends on • Professional support requirements • Unique set of development tools 2 OS SELECTION OPEN SOURCE SELECTION OS SELECTION PROS CONS Embedded Linux Most powerful / optimized Complexity for newcomers solution, maintained by NXP • Build systems Ø Yocto / Buildroot Simpler solution, makefile- Not as flexible as Yocto Ø Everything built from scratch based, maintained by BD Desktop-like approach, Harder to customize, non- Package-based distribution easy-to-use atomic updates, no cross- • Ubuntu / Debian compilation SDK Apt install / update, millions • Packages installed from server of prebuilt packages available Android Millions of apps available, same number of developers, Resource-hungry, complex • AOSP-based (no GMS) development environment, BSP modifications (HAL) • APK applications IDE + debugging tools 3 SOFTWARE PARTNERS Boundary Devices has an industry-leading group of software partners. -
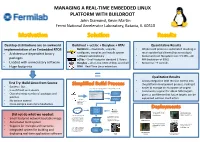
MANAGING a REAL-TIME EMBEDDED LINUX PLATFORM with BUILDROOT John Diamond, Kevin Martin Fermi National Accelerator Laboratory, Batavia, IL 60510
MANAGING A REAL-TIME EMBEDDED LINUX PLATFORM WITH BUILDROOT John Diamond, Kevin Martin Fermi National Accelerator Laboratory, Batavia, IL 60510 Desktop distributions are an awkward Buildroot + ucLibc + Busybox + RTAI Quantitative Results implementation of an Embedded RTOS Buildroot – downloads, unpacks, • Whole build process is automated resulting in • Architecture-dependent binary configures, compiles and installs system much quicker build times (hours not days) software automatically • Kernel and root filesystem size: 3.5 MB – 20 packages uClibc – Small-footprint standard C library MB (reduction of 99%) • Loaded with unnecessary software Busybox – all-in-one UNIX utilities and shell • Boot-time: ~9 seconds • Huge footprints RTAI – Real-Time Linux extensions = Qualitative Results • Allows integration with revision control into First Try: Build Linux from Source the platform development process, making it • Success! But.. 2. Buildroot’s menuconfig generates a package configuration file easier to manage an ecosystem of targets • Is as difficult as it sounds and kernel configuration file • Community support for x86 & ARM targets Linux Kernel • Overwhelming number of packages and Configuration gives us confidence that future targets can be patches Package supported without much effort 1. Developer Configuration • No version control configures build via Buildroot’s • Cross-compile even more headaches menuconfig Internet Build Process Power Supply Control Quench Protection Git / CVS / SVN and Regulation for the System for Tevatron Did not do what we needed: Fermilab Linac Electron Lens (TEL II) 3. The build process pulls 4. The output from the software packages from build process is a kernel • Small-footprint network bootable image the internet and custom bzImage bzImage file with an softare packages from a integrated root filesystem ARM Cortex A-9 source code repository file PC/104 AMD • Automated build system Geode SBC Beam Position Monitor Power Supply Control prototype for Fermilab and Regulation for • Support for multiple architectures 5. -
Linux Based Mobile Operating Systems
INSTITUTO SUPERIOR DE ENGENHARIA DE LISBOA Área Departamental de Engenharia de Electrónica e Telecomunicações e de Computadores Linux Based Mobile Operating Systems DIOGO SÉRGIO ESTEVES CARDOSO Licenciado Trabalho de projecto para obtenção do Grau de Mestre em Engenharia Informática e de Computadores Orientadores : Doutor Manuel Martins Barata Mestre Pedro Miguel Fernandes Sampaio Júri: Presidente: Doutor Fernando Manuel Gomes de Sousa Vogais: Doutor José Manuel Matos Ribeiro Fonseca Doutor Manuel Martins Barata Julho, 2015 INSTITUTO SUPERIOR DE ENGENHARIA DE LISBOA Área Departamental de Engenharia de Electrónica e Telecomunicações e de Computadores Linux Based Mobile Operating Systems DIOGO SÉRGIO ESTEVES CARDOSO Licenciado Trabalho de projecto para obtenção do Grau de Mestre em Engenharia Informática e de Computadores Orientadores : Doutor Manuel Martins Barata Mestre Pedro Miguel Fernandes Sampaio Júri: Presidente: Doutor Fernando Manuel Gomes de Sousa Vogais: Doutor José Manuel Matos Ribeiro Fonseca Doutor Manuel Martins Barata Julho, 2015 For Helena and Sérgio, Tomás and Sofia Acknowledgements I would like to thank: My parents and brother for the continuous support and being the drive force to my live. Sofia for the patience and understanding throughout this challenging period. Manuel Barata for all the guidance and patience. Edmundo Azevedo, Miguel Azevedo and Ana Correia for reviewing this document. Pedro Sampaio, for being my counselor and college, helping me on each step of the way. vii Abstract In the last fifteen years the mobile industry evolved from the Nokia 3310 that could store a hopping twenty-four phone records to an iPhone that literately can save a lifetime phone history. The mobile industry grew and thrown way most of the proprietary operating systems to converge their efforts in a selected few, such as Android, iOS and Windows Phone. -

Operating System Components for an Embedded Linux System
INSTITUTEFORREAL-TIMECOMPUTERSYSTEMS TECHNISCHEUNIVERSITATM¨ UNCHEN¨ PROFESSOR G. F ARBER¨ Operating System Components for an Embedded Linux System Martin Hintermann Studienarbeit ii Operating System Components for an Embedded Linux System Studienarbeit Executed at the Institute for Real-Time Computer Systems Technische Universitat¨ Munchen¨ Prof. Dr.-Ing. Georg Farber¨ Advisor: Prof.Dr.rer.nat.habil. Thomas Braunl¨ Author: Martin Hintermann Kirchberg 34 82069 Hohenschaftlarn¨ Submitted in February 2007 iii Acknowledgements At first, i would like to thank my supervisor Prof. Dr. Thomas Braunl¨ for giving me the opportunity to take part at a really interesting project. Many thanks to Thomas Sommer, my project partner, for his contribution to our good work. I also want to thank also Bernard Blackham for his assistance by email and phone at any time. In my opinion, it was a great cooperation of all persons taking part in this project. Abstract Embedded systems can be found in more and more devices. Linux as a free operating system is also becoming more and more important in embedded applications. Linux even replaces other operating systems in certain areas (e.g. mobile phones). This thesis deals with the employment of Linux in embedded systems. Various architectures of embedded systems are introduced and the characteristics of common operating systems for these devices are reviewed. The architecture of Linux is examined by looking at the particular components such as kernel, standard C libraries and POSIX tools for embedded systems. Furthermore, there is a survey of real-time extensions for the Linux kernel. The thesis also treats software development for embedded Linux ranging from the prerequi- sites for compiling software to the debugging of binaries. -
Building Meego with OBS an Introduction to the Meego Build Infrastructure
» The Linux Foundation Building MeeGo with OBS An Introduction to the MeeGo Build Infrastructure .................. By Rudolf Streif, The Linux Foundation June 2011 A Publication By The Linux Foundation Characters from the MeeGo Project (http://www.meego.com) http://www.linuxfoundation.org Background Building a Linux distribution from scratch can be a daunting task. Besides the obligatory Linux kernel itself with its myriad of configuration options, a working Linux distribution requires hundreds if not thousands of additional packages to form a viable platform for desktop, server, mobile or any other type of specialized applications. For embedded Linux solutions, the complexity scales with the need to support multiple and different processor architectures, hardware platforms with limited resources, requirements for cross toolchains, and more. The MeeGo project leverages the strengths of the Open Build Service (OBS) for distribution and application development. MeeGo has established a 6-months release cadence mounting two releases per year in April and October in addition to maintenance releases in-between. To support this, the MeeGo OBS environment builds bootable MeeGo images for the various MeeGo device categories and user experiences (Handset, Netbook, Tablet PC, In-vehicle Infotainment, and Smart TV) targeting multiple different hardware platforms for IA, ARM, etc. For application development, the MeeGo OBS allows developers to easily build their software packages utilizing the same infrastructure the MeeGo distributions were built with, validating dependencies and providing binary compliance. In this whitepaper, we will provide a brief introduction to the MeeGo build infrastructure and how it is utilized to support the MeeGo development process. Then we demonstrate the use of the OBS WebUI and the command-line client osc with step-by-step instructions. -

Full Virtualization on Low-End Hardware: a Case Study
Full Virtualization on Low-End Hardware: a Case Study Adriano Carvalho∗, Vitor Silva∗, Francisco Afonsoy, Paulo Cardoso∗, Jorge Cabral∗, Mongkol Ekpanyapongz, Sergio Montenegrox and Adriano Tavares∗ ∗Embedded Systems Research Group Universidade do Minho, 4800–058 Guimaraes˜ — Portugal yInstituto Politecnico´ de Coimbra (ESTGOH), 3400–124 Oliveira do Hospital — Portugal zAsian Institute of Technology, Pathumthani 12120 — Thailand xUniversitat¨ Wurzburg,¨ 97074 Wurzburg¨ — Germany Abstract—Most hypervisors today rely either on (1) full virtua- a hypervisor-specific, often proprietary, interface. Full virtua- lization on high-end hardware (i.e., hardware with virtualization lization on low-end hardware, on the other end, has none of extensions), (2) paravirtualization, or (3) both. These, however, those disadvantages. do not fulfill embedded systems’ requirements, or require legacy software to be modified. Full virtualization on low-end hardware Full virtualization on low-end hardware (i.e., hardware with- (i.e., hardware without virtualization extensions), on the other out dedicated support for virtualization) must be accomplished end, has none of those disadvantages. However, it is often using mechanisms which were not originally designed for it. claimed that it is not feasible due to an unacceptably high Therefore, full virtualization on low-end hardware is not al- virtualization overhead. We were, nevertheless, unable to find ways possible because the hardware may not fulfill the neces- real-world quantitative results supporting those claims. In this paper, performance and footprint measurements from a sary requirements (i.e., “the set of sensitive instructions for that case study on low-end hardware full virtualization for embedded computer is a subset of the set of privileged instructions” [1]). -

Instituto Tecnológico De Costa Rica Escuela De Ingenier´Ia En
Instituto Tecnol´ogicode Costa Rica Escuela de Ingenier´ıaen Electr´onica Improvement of small satellite's software design with build system and continuous integration tools para optar por el t´ıtulode Ingeniero en Electr´onicacon ´enfasisen sistemas empotrados con el grado acad´emicode Maestr´ıa Allan Granados [email protected] Cartago, Diciembre, 2015 2 Contents 1 Introduction 8 1.1 Previous work focus on small satellites . .9 1.2 Problem statement . 11 1.3 Proposed solution . 13 1.3.1 Proposed development . 13 2 Software development approaches for small satellites 15 2.1 Software methodologies used for satellites design . 15 2.2 Small satellite design and structure . 17 2.3 Central computation system in satellites. Homogeneous and Het- erogeneous systems . 18 2.4 Different approach on software development for small satellites . 20 2.4.1 Software development: Monolithic approach . 20 2.4.2 Software development: Development by component . 21 2.5 Open Source tools on the design and implementation of software satellite . 23 3 Integration of build system for small satellite missions 24 3.1 Build systems as an improvement on the design methodology . 24 3.1.1 Yocto build system . 29 4 Development platforms 32 4.1 Beagleboard XM . 32 4.2 Pandaboard . 35 4.3 Beaglebone . 38 5 Design and implementation of the construction system 41 5.1 Construction System . 41 5.1.1 The hardware independent layer: meta-tecSat . 42 5.1.2 The hardware dependent later: meta-tecSat-target . 43 5.1.3 Integration of the dependent and independent hardware layers in the construction system . 44 5.1.4 Adding a new recipe to a layer . -
Embedded Operating Systems
7 Embedded Operating Systems Claudio Scordino1, Errico Guidieri1, Bruno Morelli1, Andrea Marongiu2,3, Giuseppe Tagliavini3 and Paolo Gai1 1Evidence SRL, Italy 2Swiss Federal Institute of Technology in Zurich (ETHZ), Switzerland 3University of Bologna, Italy In this chapter, we will provide a description of existing open-source operating systems (OSs) which have been analyzed with the objective of providing a porting for the reference architecture described in Chapter 2. Among the various possibilities, the ERIKA Enterprise RTOS (Real-Time Operating System) and Linux with preemption patches have been selected. A description of the porting effort on the reference architecture has also been provided. 7.1 Introduction In the past, OSs for high-performance computing (HPC) were based on custom-tailored solutions to fully exploit all performance opportunities of supercomputers. Nowadays, instead, HPC systems are being moved away from in-house OSs to more generic OS solutions like Linux. Such a trend can be observed in the TOP500 list [1] that includes the 500 most powerful supercomputers in the world, in which Linux dominates the competition. In fact, in around 20 years, Linux has been capable of conquering all the TOP500 list from scratch (for the first time in November 2017). Each manufacturer, however, still implements specific changes to the Linux OS to better exploit specific computer hardware features. This is especially true in the case of computing nodes in which lightweight kernels are used to speed up the computation. 173 174 Embedded Operating Systems Figure 7.1 Number of Linux-based supercomputers in the TOP500 list. Linux is a full-featured OS, originally designed to be used in server or desktop environments. -

Designing Ostree Based Embedded Linux Systems with the Yocto Project
Yocto Project Summit 2021 Designing OSTree based embedded Linux systems with the Yocto Project Sergio Prado Toradex $ WHOAMI ✗ Designing and developing embedded software for 25+ years. ✗ Software Team Lead at Toradex (https://www.toradex.com/). ✗ Consultant/trainer at Embedded Labworks (e-labworks.com/en). ✗ Open source software contributor, including Buildroot, Yocto Project and the Linux kernel. ✗ Sometimes write technical stuff at https://embeddedbits.org/. ✗ Social networks: Twitter: @sergioprado Linkedin: https://linkedin.com/in/sprado AGENDA 1. Introduction to OSTree 2. Booting and running an OSTree-based system 3. Building an OSTree-based system with meta-updater 4. Remote updates with OSTree-based systems WHAT IS OSTREE? ✗ OStree, also known as libostree, provides a "git-like" model for committing and downloading bootable filesystem trees (rootfs). ✗ It’s like Git, in a sense that it stores checksum'ed files (SHA256) in a content-addressed object-store. ✗ It’s different from Git, because files are checked out via hard links, and they are immutable (read-only) to prevent corruption. ✗ Designed and currently maintained by Colin Walters (GNOME, OpenShift, RedHat CoreOS developer) A FEW OSTREE USERS ✗ Linux distributions: ✗ GNOME Continuous, Gnome OS ✗ Fedora CoreOS, Fedora Silverblue, Fedora IoT ✗ Endless OS ✗ Linux microPlatform ✗ TorizonCore ✗ Package management systems: ✗ rpm-ostree ✗ flatpak OSTREE IN A NUTSHELL ✗ A Git-like content-addressed object store, where we can store individual files or full filesystem trees. ✗ Provides a mechanism to commit and checkout branches (or "refs"). ✗ Manages bootloader configuration via The Boot Loader Specification, a standard on how different operating systems can cooperatively manage a boot loader configuration (GRUB and U-Boot supported). -
Yocto Project and Embedded OS
Yocto Project and Jeffrey Osier-Mixon Embedded OS •What is the Yocto Project and why is it important? •Working with an open source collaborative project & community Kevin McGrath •Yocto Project concepts in a nutshell: environment, metadata, tools • Using Yocto cross-compiler • Running kernel via qemu th • Module installation, virtio, etc. July 28 2015 • Lessons learned, capabilities 11:00 PDT (GMT -7) 1 Yocto Project and Embedded OS Our guests Jeffrey Osier-Mixon: Jeff "Jefro" Osier-Mixon works for Intel Corporation in Intel's Open Source Technology Center, where his current role is community manager for the Yocto Project.. Jefro also works as a community architect and consultant for a number of open source projects and speaks regularly at open source conferences worldwide. He has been deeply involved with open source since the early 1990s. Kevin McGrath : Instructor at Oregon State University. I primarily teach the operating systems sequence and the senior capstone project sequence, but have taught architecture, assembly programming, introductory programming classes, and just about anything else that needs someone to teach it. While my background is in network security and high performance computing (computational physics), today I mostly live in the embedded space, leading to the “ECE wannabe” title in my department. Oleg Verge (Moderator): Technical Program Manager Intel Higher Education, System Engineer MCSE,CCNA, VCP Intel® IoT Developer Kit v1.0 Hardware components = + + Helpful Linux* tools (GCC tool chain, perf, oProfile, Software image + etc.), required drivers (Wi-Fi*, Bluetooth®, etc.), useful = API libraries, and daemons like LighttPD and Node.js. + Intel XDK Support for various IDEs = + + + For C/C++ For java, For Arduino* For Visual + node.js.,html5 sketches Programming Cloud services = Intel IoT Analytics includes capabilities for data collection, + storage, visualization, and analysis of sensor data. -

Is Android the New Embedded Linux?
Is Android the new Embedded Linux? AnDevCon 2013 Karim Yaghmour [email protected] 1 These slides are made available to you under a Creative Commons Share- Delivered and/or customized by Alike 3.0 license. The full terms of this license are here: https://creativecommons.org/licenses/by-sa/3.0/ Attribution requirements and misc., PLEASE READ: ● This slide must remain as-is in this specific location (slide #2), everything else you are free to change; including the logo :-) ● Use of figures in other documents must feature the below “Originals at” URL immediately under that figure and the below copyright notice where appropriate. ● You are free to fill in the “Delivered and/or customized by” space on the right as you see fit. ● You are FORBIDEN from using the default “About” slide as-is or any of its contents. rd ● You are FORBIDEN from using any content provided by 3 parties without the EXPLICIT consent from those parties. (C) Copyright 2013, Opersys inc. These slides created by: Karim Yaghmour Originals at: www.opersys.com/community/docs 2 About ● Author of: ● Introduced Linux Trace Toolkit in 1999 ● Originated Adeos and relayfs (kernel/relay.c) ● Training, Custom Dev, Consulting, ... 3 1. Why are we asking this question? ● Android is based on Linux ● Android is “embedded” ● Android is extremely popular ● Android enjoys good support from SoC vendors Mostly - The trends are there 4 1.1. Why did Embedded Linux rise? ● EETimes 2005 survey ... http://www.embedded.com/electronics-blogs/- include/4025539/Embedded-systems-survey-Operating- systems-up-for-grabs ● EETimes 2013 survey http://www.slideshare.net/MTKDMI/2013-embedded-market- study-final http://www.eetimes.com/electronics-news/4407897/Android-- FreeRTOS-top-EE-Times--2013-embedded-survey 5 1.2.