Towards (Better!) Linux Kernel Security: the Journey of Past 10 Years About Myself
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Tizen IVI “From Scratch” Customizing, Building and Testing
Tizen IVI “from scratch” Customizing, building and testing Stéphane Desneux Senior Software Engineer Eurogiciel <[email protected]> Eurogiciel ● Open source development and integration: ● Maintainers in multiple domains on tizen.org ● Embedded systems for real-time multimedia: ▪ Widi/Miracast stack ▪ Wayland/Weston ▪ Webkit2 browser with HW acceleration ● Applications: HTML5/CSS3, jquery, jqmobi, Cordova ● Location : Vannes (Brittany), France 14 2 FOSDEM' Automotive devroom – Tizen “from scratch” : customize, build, test ! Agenda ● Tizen & Tizen:IVI : short introduction ● From source code to target devices ● Customize ● Build ● Flash, Run, Test ! 14 3 FOSDEM' Automotive devroom – Tizen “from scratch” : customize, build, test ! Tizen: a short introduction Definition ● Open source project ● Hosted at the Linux Foundation ● Innovative Web-based platform for multiple devices ● Sponsored by worldwide companies ● Samsung & Intel are two big contributors ● Built on industry standards: ● GNU/Linux kernel, GNU libc ● POSIX ● W3C ● Many upstream Open Source projects 14 5 FOSDEM' Automotive devroom – Tizen “from scratch” : customize, build, test ! Tizen Profiles ● Multiple vertical profiles (derived from Tizen:Generic) ● IVI ● Mobile ● Future: other devices (TV, ...) ● Each profile adds its own enhancements ● Tizen packaging format: RPM 14 6 FOSDEM' Automotive devroom – Tizen “from scratch” : customize, build, test ! From source code … … to target devices 1: Source code GIT Repositories Remote Local Clone source repo Developers -

Create an Email with Subject Title “Embedded Software Engineer”, Email a Copy of Your Resume to [email protected]
To Apply for This Position: Create an email with subject title “Embedded Software Engineer”, email a copy of your resume to [email protected] Location Address: ALLEN PARK, MI,48101 Position Description: TITLE: Embedded Software Engineer ‐ Hypervisor OS technologies This position is responsible to develop QNX and Android operating system images for Ford infotainment products. This includes creating and integrating code for: bootloader, kernel, drivers, type 1 hypervisor, and build environment. Skills Required: • Lead the design, bring‐up and support of QNX and Android operating system images • Create virt‐io drivers for QNX or Android guest operating systems • Participate in root cause analysis of hardware quality problems and software defects • Participate in system design, documentation, and testing to deliver a best‐in‐class infotainment system Experience Required: • 5+ years operating system experience involving Linux or QNX • 5+ years C/C++ software development experience on embedded, mobile, or consumer electronic platforms Experience Preferred: • Experience with Type 1 hypervisors • Experience creating virt‐io drivers • Mastery of C/C++ language, GNU tool chain, and Unix (QNX, Linux, or equivalent) • Experience with embedded build systems including QNX system builder, buildroot, yocto, or equivalent • Knowledge of in‐vehicle signaling and communication mechanisms such as CAN • Proficiency with revision control including Git, Subversion, or equivalent • Multi‐site software project team experience Education Required: • Bachelor's degree in Computer Engineering, Electrical Engineering, Computer Science, or related Education Preferred: • Master's degree in Computer Engineering, Electrical Engineering or Computer Science Additional Information: Web Based Assessment not required for this position. Visa Sponsorship and Domestic Relocation is available for this position. -
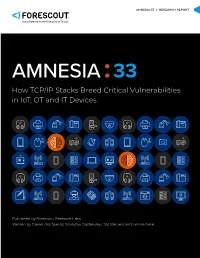
AMNESIA 33: How TCP/IP Stacks Breed Critical Vulnerabilities in Iot
AMNESIA:33 | RESEARCH REPORT How TCP/IP Stacks Breed Critical Vulnerabilities in IoT, OT and IT Devices Published by Forescout Research Labs Written by Daniel dos Santos, Stanislav Dashevskyi, Jos Wetzels and Amine Amri RESEARCH REPORT | AMNESIA:33 Contents 1. Executive summary 4 2. About Project Memoria 5 3. AMNESIA:33 – a security analysis of open source TCP/IP stacks 7 3.1. Why focus on open source TCP/IP stacks? 7 3.2. Which open source stacks, exactly? 7 3.3. 33 new findings 9 4. A comparison with similar studies 14 4.1. Which components are typically flawed? 16 4.2. What are the most common vulnerability types? 17 4.3. Common anti-patterns 22 4.4. What about exploitability? 29 4.5. What is the actual danger? 32 5. Estimating the reach of AMNESIA:33 34 5.1. Where you can see AMNESIA:33 – the modern supply chain 34 5.2. The challenge – identifying and patching affected devices 36 5.3. Facing the challenge – estimating numbers 37 5.3.1. How many vendors 39 5.3.2. What device types 39 5.3.3. How many device units 40 6. An attack scenario 41 6.1. Other possible attack scenarios 44 7. Effective IoT risk mitigation 45 8. Conclusion 46 FORESCOUT RESEARCH LABS RESEARCH REPORT | AMNESIA:33 A note on vulnerability disclosure We would like to thank the CERT Coordination Center, the ICS-CERT, the German Federal Office for Information Security (BSI) and the JPCERT Coordination Center for their help in coordinating the disclosure of the AMNESIA:33 vulnerabilities. -

Symbian OS Platform Security Model
THE SYMBIAN OS BECAME FULLY OPEN sourced in February 2010, which opens even BO LI, ELENA RESHETOVA, AND T U O M A S A U R A more possibilities for application develop- ers to understand and analyze its security Symbian OS solution. We present a short introduction to the software features of Symbian plat- platform form security: three trust tiers, capability model, data caging, and the Symbian signed security model process. We also try to compare the security Bo Li is a second-year student in the master’s solution with the classical design principles program in security and mobile computing in this area, as well as briefly discuss gen- at Aalto University, Finland. He got his bach- elor’s degree in communications engineering eral design challenges and potential weak- in 2008 from Fudan University, China. nesses. [email protected] Elena Reshetova is a senior security engineer Introduction at Nokia, as well as a postgraduate student at Aalto University. She is interested in With the development of mobile devices and mo- various research areas related to platform bile computers, more and more people rely strongly security, security aspects of networking, and on them. People use mobile devices and mobile cryptography. computers to arrange their schedules, contact each [email protected] other, process emails, and share rich media con- tent. People believe it is safe to do so because it Tuomas Aura is a professor at Aalto Uni- versity, Finland. His research interests are feels secure just knowing it is “right there with security and privacy in communications you” [8]. -

OS Selection for Dummies
OS SELECTION HOW TO CHOOSE HOW TO CHOOSE Choosing your OS is the first step, so take the time to consider your choice fully. There are many parameters to take into account: l Is this a new project or the evolution of an existing product? l Using the same SW stack? Re-using existing code? l Is your team familiar with a particular OS? Ø Using an OS you are already comfortable with can help l What are the HW constraints of your system? Ø Some operating systems require more memory/processing power than others l Have no SW team? Not sure about the above? Ø Contact us so we can help you decide! Ø We can also introduce you to one of our many partners! 1 OS SELECTION OPEN SOURCE VS. COMMERCIAL OS Embedded OS BSP Provider $ Cost Open-Source OS Boundary Devices • Embedded Linux / Android Embedded Linux $0, included • Large pool of developers available with Board Purchase • Strong community • Royalty-free And / or partners 3rd Party - Commercial OS Partners • QNX / Win10 IoT / Green Hills $>0, depends on • Professional support requirements • Unique set of development tools 2 OS SELECTION OPEN SOURCE SELECTION OS SELECTION PROS CONS Embedded Linux Most powerful / optimized Complexity for newcomers solution, maintained by NXP • Build systems Ø Yocto / Buildroot Simpler solution, makefile- Not as flexible as Yocto Ø Everything built from scratch based, maintained by BD Desktop-like approach, Harder to customize, non- Package-based distribution easy-to-use atomic updates, no cross- • Ubuntu / Debian compilation SDK Apt install / update, millions • Packages installed from server of prebuilt packages available Android Millions of apps available, same number of developers, Resource-hungry, complex • AOSP-based (no GMS) development environment, BSP modifications (HAL) • APK applications IDE + debugging tools 3 SOFTWARE PARTNERS Boundary Devices has an industry-leading group of software partners. -

Symbian Foundation Press Conference
Symbian Foundation Press conference M/C – Merran Wrigley Exciting Internet experiences for the aspirations of billions 2 © 2008 Symbian Foundation Mobile software set free Symbian Foundation Kai Öistämö Executive Vice President, Nokia Shared vision for an unparalleled open mobile software platform 4 © 2008 Symbian Foundation That unites Symbian OS, S60, UIQ and MOAP(S) 5 © 2008 Symbian Foundation Creating the most proven, open, complete mobile software platform 6 © 2008 Symbian Foundation With over 200 million devices already shipped 7 © 2008 Symbian Foundation For free. 8 © 2008 Symbian Foundation Creating one platform, royalty-free Foundation Differentiated Member experience MOAP(S) 9 © 2008 Symbian Foundation Creating one platform, royalty-free Foundation Differentiated Member experience Symbian Foundation Platform Applications suite Runtimes UI framework Middleware Operating system Tools & SDK 10 © 2008 Symbian Foundation The first step to our goal • Acquiring Symbian Ltd • Closing expected in Q4 2008 • Symbian Ltd to be part of Nokia • Nokia will contribute Symbian OS and S60 to Symbian Foundation 11 © 2008 Symbian Foundation Fulfilling the Symbian mission Symbian Foundation Nigel Clifford CEO, Symbian Symbian Ltd Mission To become the most widely used software platform on the planet 13 © 2008 Symbian Foundation The leading global open platform 12% Symbian Linux 11% Microsoft RIM 60% Apple 11% Other Source Canalys – Cumulative 4% 12 month period to Q1 2008 2% 14 © 2008 Symbian Foundation The choice for the top vendors Samsung MOTO -

B.Tech. CSE CBCS W.E.F. July, 2019
The Curriculum Book BACHELOR OF TECHNOLOGY I tn COMPUTER SCIENCE AND ENGINEERING FOUR YEAR PROGRAMME Choice Based Credit System vy. e. f. JuIy ZAlg (70:30) . ,_i 1 .I DEPARTMENT OF COMPUTER SCIENCE AI\D BNGINEERING GURU JAMBHESHWAR UNIVERSITY OF SCIENCE & TECHNOLOGY tr j HISAR.125OO1, HARYANA scheme & syllabi2019 GURU JAMBHESHWAR UNIVERSITY OF SCIENCE & TECHNOLOGY, HISAR (Established by state Legistature 'A',Grade,. Act 17 of lggs) NA.AC Accreditid state Govt. university Acad /AC-ilt,tFqc_1 Vot. 3DAlgJf 7 7 Dated: Ulfr:f To The Controller of Examinations GJUS&T, Hisar. sub: Approval of scheme of examination & syllabi of various B.Tech. progralle(sJ being run in university Teachiig Departments as welt as affil iated En g i neeri ng c oilege(s)/r nstitutelsy. AND Recommendations of Faculty Engineering open & Technology regarding Elective, Format of Minor Quu.ti;;-of papei Mooc strength for programme courses, minimum Erective, semester Registration etc. Sir, I am directed to inform you that the vice-chancellor, on the recommendations of the Faculty of Engineering & Technology, vide resolutions no. 2to 13 in its meeting held on 1B 07'2a19, is pleased to approve . the following scheme & syllabi of B.Tech. programme(s) w'e'f' the academic session batch / mentioned against each being run in University Teaching Departments as well as affiliated colleges/institutions and recommendations of Faculty of Engineering & Technolcgy, regarding open Elective, format of Minor Question Paper, Mooc courses, minimum strength for programme Elective' semester Registration etc under sectio n 11(5) in anticipation of approvat of the Acadenric councir of the University Act, 1995.- 1' B'Tech (Printing Technology), B Tec.h (Packaging Technology) (Printing & Packaging i""r'norogD-ath ""un',i""o,,,& B.Tech. -

Long Comment Regarding a Proposed Exemption Under 17 U.S.C. 1201 for Software Freedom Conservancy Proposed Class: 20 – Smart T
Long Comment Regarding a Proposed Exemption Under 17 U.S.C. 1201 For Software Freedom Conservancy Proposed Class: 20 – Smart TVs No multimedia evidence is being provided in connection with this comment Item 1. Commenter Information The Petition submitter is Software Freedom Conservancy (“Conservancy”), a 501(c)(3) not-for-profit organization that helps promote, improve, develop, and defend Free, Libre, and Open Source Software (“FLOSS”)—software developed by volunteer communities and licensed for the benefit of everyone. Conservancy is the nonprofit home for dozens of FLOSS projects representing well over a thousand volunteer contributors. Conservancy's communities maintain some of the most fundamental utilities in computing today, and introduce innovations that will shape how software will be created in the future. Among the projects for which Conservancy provides logistical, administrative, and legal support are BusyBox and Samba, both of which are commonly installed on “smart” or computer- embedded consumer electronics devices. BusyBox provides a number of key system utilities that enable such devices to run applications, interact with files, access network services, and more.1 It is also used by community projects focused on unlocking and improving Samsung-2 and LG- manufactured Smart TVs.3 Samba permits devices to interact with files stored on other networked devices.4 Conservancy also represents the interests of several contributors to the Linux kernel, the core component of the operating system of most Smart TVs. Conservancy may be contacted through its authorized representatives and pro bono counsel at Tor Ekeland, P.C., 195 Plymouth Street, Brooklyn, New York 11201: Aaron Williamson Frederic Jennings (718) 285-9349 (718) 514-2075 [email protected] [email protected] Item 2. -
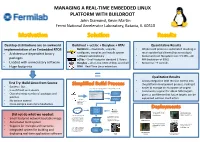
MANAGING a REAL-TIME EMBEDDED LINUX PLATFORM with BUILDROOT John Diamond, Kevin Martin Fermi National Accelerator Laboratory, Batavia, IL 60510
MANAGING A REAL-TIME EMBEDDED LINUX PLATFORM WITH BUILDROOT John Diamond, Kevin Martin Fermi National Accelerator Laboratory, Batavia, IL 60510 Desktop distributions are an awkward Buildroot + ucLibc + Busybox + RTAI Quantitative Results implementation of an Embedded RTOS Buildroot – downloads, unpacks, • Whole build process is automated resulting in • Architecture-dependent binary configures, compiles and installs system much quicker build times (hours not days) software automatically • Kernel and root filesystem size: 3.5 MB – 20 packages uClibc – Small-footprint standard C library MB (reduction of 99%) • Loaded with unnecessary software Busybox – all-in-one UNIX utilities and shell • Boot-time: ~9 seconds • Huge footprints RTAI – Real-Time Linux extensions = Qualitative Results • Allows integration with revision control into First Try: Build Linux from Source the platform development process, making it • Success! But.. 2. Buildroot’s menuconfig generates a package configuration file easier to manage an ecosystem of targets • Is as difficult as it sounds and kernel configuration file • Community support for x86 & ARM targets Linux Kernel • Overwhelming number of packages and Configuration gives us confidence that future targets can be patches Package supported without much effort 1. Developer Configuration • No version control configures build via Buildroot’s • Cross-compile even more headaches menuconfig Internet Build Process Power Supply Control Quench Protection Git / CVS / SVN and Regulation for the System for Tevatron Did not do what we needed: Fermilab Linac Electron Lens (TEL II) 3. The build process pulls 4. The output from the software packages from build process is a kernel • Small-footprint network bootable image the internet and custom bzImage bzImage file with an softare packages from a integrated root filesystem ARM Cortex A-9 source code repository file PC/104 AMD • Automated build system Geode SBC Beam Position Monitor Power Supply Control prototype for Fermilab and Regulation for • Support for multiple architectures 5. -

Tizen Based Remote Controller CAR Using Raspberry Pi2
#ELC2016 Tizen based remote controller CAR using raspberry pi2 Pintu Kumar ([email protected], [email protected]) Samsung Research India – Bangalore : Tizen Kernel/BSP Team Embedded Linux Conference – 06th April/2016 1 CONTENT #ELC2016 • INTRODUCTION • RASPBERRY PI2 OVERVIEW • TIZEN OVERVIEW • HARDWARE & SOFTWARE REQUIREMENTS • SOFTWARE CUSTOMIZATION • SOFTWARE SETUP & INTERFACING • HARDWARE INTERFACING & CONNECTIONS • ROBOT CONTROL MECHANISM • SOME RESULTS • CONCLUSION • REFERENCES Embedded Linux Conference – 06th April/2016 2 INTRODUCTION #ELC2016 • This talk is about designing a remote controller robot (toy car) using the raspberry pi2 hardware, pi2 Linux Kernel and Tizen OS as platform. • In this presentation, first we will see how to replace and boot Tizen OS on Raspberry Pi using the pre-built Tizen images. Then we will see how to setup Bluetooth, Wi-Fi on Tizen and finally see how to control a robot remotely using Tizen smart phone application. Embedded Linux Conference – 06th April/2016 3 RASPBERRY PI2 - OVERVIEW #ELC2016 1 GB RAM Embedded Linux Conference – 06th April/2016 4 Raspberry PI2 Features #ELC2016 • Broadcom BCM2836 900MHz Quad Core ARM Cortex-A7 CPU • 1GB RAM • 4 USB ports • 40 GPIO pins • Full HDMI port • Ethernet port • Combined 3.5mm audio jack and composite video • Camera interface (CSI) • Display interface (DSI) • Micro SD card slot • Video Core IV 3D graphics core Embedded Linux Conference – 06th April/2016 5 PI2 GPIO Pins #ELC2016 Embedded Linux Conference – 06th April/2016 6 TIZEN OVERVIEW #ELC2016 Embedded Linux Conference – 06th April/2016 7 TIZEN Profiles #ELC2016 Mobile Wearable IVI TV TIZEN Camera PC/Tablet Printer Common Next?? • TIZEN is the OS of everything. -
Linux Based Mobile Operating Systems
INSTITUTO SUPERIOR DE ENGENHARIA DE LISBOA Área Departamental de Engenharia de Electrónica e Telecomunicações e de Computadores Linux Based Mobile Operating Systems DIOGO SÉRGIO ESTEVES CARDOSO Licenciado Trabalho de projecto para obtenção do Grau de Mestre em Engenharia Informática e de Computadores Orientadores : Doutor Manuel Martins Barata Mestre Pedro Miguel Fernandes Sampaio Júri: Presidente: Doutor Fernando Manuel Gomes de Sousa Vogais: Doutor José Manuel Matos Ribeiro Fonseca Doutor Manuel Martins Barata Julho, 2015 INSTITUTO SUPERIOR DE ENGENHARIA DE LISBOA Área Departamental de Engenharia de Electrónica e Telecomunicações e de Computadores Linux Based Mobile Operating Systems DIOGO SÉRGIO ESTEVES CARDOSO Licenciado Trabalho de projecto para obtenção do Grau de Mestre em Engenharia Informática e de Computadores Orientadores : Doutor Manuel Martins Barata Mestre Pedro Miguel Fernandes Sampaio Júri: Presidente: Doutor Fernando Manuel Gomes de Sousa Vogais: Doutor José Manuel Matos Ribeiro Fonseca Doutor Manuel Martins Barata Julho, 2015 For Helena and Sérgio, Tomás and Sofia Acknowledgements I would like to thank: My parents and brother for the continuous support and being the drive force to my live. Sofia for the patience and understanding throughout this challenging period. Manuel Barata for all the guidance and patience. Edmundo Azevedo, Miguel Azevedo and Ana Correia for reviewing this document. Pedro Sampaio, for being my counselor and college, helping me on each step of the way. vii Abstract In the last fifteen years the mobile industry evolved from the Nokia 3310 that could store a hopping twenty-four phone records to an iPhone that literately can save a lifetime phone history. The mobile industry grew and thrown way most of the proprietary operating systems to converge their efforts in a selected few, such as Android, iOS and Windows Phone. -

Operating System Components for an Embedded Linux System
INSTITUTEFORREAL-TIMECOMPUTERSYSTEMS TECHNISCHEUNIVERSITATM¨ UNCHEN¨ PROFESSOR G. F ARBER¨ Operating System Components for an Embedded Linux System Martin Hintermann Studienarbeit ii Operating System Components for an Embedded Linux System Studienarbeit Executed at the Institute for Real-Time Computer Systems Technische Universitat¨ Munchen¨ Prof. Dr.-Ing. Georg Farber¨ Advisor: Prof.Dr.rer.nat.habil. Thomas Braunl¨ Author: Martin Hintermann Kirchberg 34 82069 Hohenschaftlarn¨ Submitted in February 2007 iii Acknowledgements At first, i would like to thank my supervisor Prof. Dr. Thomas Braunl¨ for giving me the opportunity to take part at a really interesting project. Many thanks to Thomas Sommer, my project partner, for his contribution to our good work. I also want to thank also Bernard Blackham for his assistance by email and phone at any time. In my opinion, it was a great cooperation of all persons taking part in this project. Abstract Embedded systems can be found in more and more devices. Linux as a free operating system is also becoming more and more important in embedded applications. Linux even replaces other operating systems in certain areas (e.g. mobile phones). This thesis deals with the employment of Linux in embedded systems. Various architectures of embedded systems are introduced and the characteristics of common operating systems for these devices are reviewed. The architecture of Linux is examined by looking at the particular components such as kernel, standard C libraries and POSIX tools for embedded systems. Furthermore, there is a survey of real-time extensions for the Linux kernel. The thesis also treats software development for embedded Linux ranging from the prerequi- sites for compiling software to the debugging of binaries.