An Introduction to Cryptography Copyright © 1990–2000 Network Associates, Inc
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Cryptography
56 Protecting Information With Cryptography Chapter by Peter Reiher (UCLA) 56.1 Introduction In previous chapters, we’ve discussed clarifying your security goals, determining your security policies, using authentication mechanisms to identify principals, and using access control mechanisms to enforce poli- cies concerning which principals can access which computer resources in which ways. While we identified a number of shortcomings and prob- lems inherent in all of these elements of securing your system, if we re- gard those topics as covered, what’s left for the operating system to worry about, from a security perspective? Why isn’t that everything? There are a number of reasons why we need more. Of particular im- portance: not everything is controlled by the operating system. But per- haps you respond, you told me the operating system is all-powerful! Not really. It has substantial control over a limited domain – the hardware on which it runs, using the interfaces of which it is given control. It has no real control over what happens on other machines, nor what happens if one of its pieces of hardware is accessed via some mechanism outside the operating system’s control. But how can we expect the operating system to protect something when the system does not itself control access to that resource? The an- swer is to prepare the resource for trouble in advance. In essence, we assume that we are going to lose the data, or that an opponent will try to alter it improperly. And we take steps to ensure that such actions don’t cause us problems. -

A History of End-To-End Encryption and the Death of PGP
25/05/2020 A history of end-to-end encryption and the death of PGP Hey! I'm David, a security engineer at the Blockchain team of Facebook (https://facebook.com/), previously a security consultant for the Cryptography Services of NCC Group (https://www.nccgroup.com). I'm also the author of the Real World Cryptography book (https://www.manning.com/books/real-world- cryptography?a_aid=Realworldcrypto&a_bid=ad500e09). This is my blog about cryptography and security and other related topics that I Ûnd interesting. A history of end-to-end encryption and If you don't know where to start, you might want to check these popular the death of PGP articles: posted January 2020 - How did length extension attacks made it 1981 - RFC 788 - Simple Mail Transfer Protocol into SHA-2? (/article/417/how-did-length- extension-attacks-made-it-into-sha-2/) (https://tools.ietf.org/html/rfc788) (SMTP) is published, - Speed and Cryptography the standard for email is born. (/article/468/speed-and-cryptography/) - What is the BLS signature scheme? (/article/472/what-is-the-bls-signature- This is were everything starts, we now have an open peer-to-peer scheme/) protocol that everyone on the internet can use to communicate. - Zero'ing memory, compiler optimizations and memset_s (/article/419/zeroing-memory- compiler-optimizations-and-memset_s/) 1991 - The 9 Lives of Bleichenbacher's CAT: New Cache ATtacks on TLS Implementations The US government introduces the 1991 Senate Bill 266, (/article/461/the-9-lives-of-bleichenbachers- which attempts to allow "the Government to obtain the cat-new-cache-attacks-on-tls- plain text contents of voice, data, and other implementations/) - How to Backdoor Di¸e-Hellman: quick communications when appropriately authorized by law" explanation (/article/360/how-to-backdoor- from "providers of electronic communications services di¸e-hellman-quick-explanation/) and manufacturers of electronic communications - Tamarin Prover Introduction (/article/404/tamarin-prover-introduction/) service equipment". -

PCI Assessment Evidence of PCI Policy Compliance
PCI Assessment Evidence of PCI Policy Compliance CONFIDENTIALITY NOTE: The information contained in this report document is for the Prepared for: exclusive use of the client specified above and may contain confidential, privileged and non-disclosable information. If the recipient of this report is not the client or Prospect or Customer addressee, such recipient is strictly prohibited from reading, photocopying, distributing or otherwise using this report or its contents in any way. Prepared by: Your Company Name Evidence of PCI Policy Compliance PCI ASSESSMENT Table of Contents 1 - Overview 1.1 - Security Officer 1.2 - Overall Risk 2 - PCI DSS Evidence of Compliance 2.1 - Install and maintain firewall to protect cardholder data 2.1.1.1 - Requirements for firewall at each Internet connections and between DMZ and internal network zone 2.1.1.2 - Business justification for use of all services, protocols and ports allowed 2.1.2 - Build firewall and router configurations that restrict connections between untrusted networks and the cardholder data environment 2.1.2.1 - Restrict inbound and outbound to that which is necessary for the cardholder data environment 2.1.2.3 - Do not allow unauthorized outbound traffic from the cardholder data environment to the Internet 2.1.2.4 - Implement stateful inspection (also known as dynamic packet filtering) 2.1.2.5 - Do not allow unauthorized outbound traffic from the cardholder data environment to the Internet 2.2 - Prohibition of vendor-supplied default password for systems and security parameters 2.2.1 -

Self-Encrypting Deception: Weaknesses in the Encryption of Solid State Drives
Self-encrypting deception: weaknesses in the encryption of solid state drives Carlo Meijer Bernard van Gastel Institute for Computing and Information Sciences School of Computer Science Radboud University Nijmegen Open University of the Netherlands [email protected] and Institute for Computing and Information Sciences Radboud University Nijmegen Bernard.vanGastel@{ou.nl,ru.nl} Abstract—We have analyzed the hardware full-disk encryption full-disk encryption. Full-disk encryption software, especially of several solid state drives (SSDs) by reverse engineering their those integrated in modern operating systems, may decide to firmware. These drives were produced by three manufacturers rely solely on hardware encryption in case it detects support between 2014 and 2018, and are both internal models using the SATA and NVMe interfaces (in a M.2 or 2.5" traditional form by the storage device. In case the decision is made to rely on factor) and external models using the USB interface. hardware encryption, typically software encryption is disabled. In theory, the security guarantees offered by hardware encryp- As a primary example, BitLocker, the full-disk encryption tion are similar to or better than software implementations. In software built into Microsoft Windows, switches off software reality, we found that many models using hardware encryption encryption and completely relies on hardware encryption by have critical security weaknesses due to specification, design, and implementation issues. For many models, these security default if the drive advertises support. weaknesses allow for complete recovery of the data without Contribution. This paper evaluates both internal and external knowledge of any secret (such as the password). -

Battle of the Clipper Chip - the New York Times
Battle of the Clipper Chip - The New York Times https://www.nytimes.com/1994/06/12/magazine/battle-of-the-clipp... https://nyti.ms/298zenN Battle of the Clipper Chip By Steven Levy June 12, 1994 See the article in its original context from June 12, 1994, Section 6, Page 46 Buy Reprints VIEW ON TIMESMACHINE TimesMachine is an exclusive benefit for home delivery and digital subscribers. About the Archive This is a digitized version of an article from The Times’s print archive, before the start of online publication in 1996. To preserve these articles as they originally appeared, The Times does not alter, edit or update them. Occasionally the digitization process introduces transcription errors or other problems; we are continuing to work to improve these archived versions. On a sunny spring day in Mountain View, Calif., 50 angry activists are plotting against the United States Government. They may not look subversive sitting around a conference table dressed in T-shirts and jeans and eating burritos, but they are self-proclaimed saboteurs. They are the Cypherpunks, a loose confederation of computer hackers, hardware engineers and high-tech rabble-rousers. The precise object of their rage is the Clipper chip, offically known as the MYK-78 and not much bigger than a tooth. Just another tiny square of plastic covering a silicon thicket. A computer chip, from the outside indistinguishable from thousands of others. It seems 1 of 19 11/29/20, 6:16 PM Battle of the Clipper Chip - The New York Times https://www.nytimes.com/1994/06/12/magazine/battle-of-the-clipp.. -

Zfone: a New Approach for Securing Voip Communication
Zfone: A New Approach for Securing VoIP Communication Samuel Sotillo [email protected] ICTN 4040 Spring 2006 Abstract This paper reviews some security challenges currently faced by VoIP systems as well as their potential solutions. Particularly, it focuses on Zfone, a vendor-neutral security solution developed by PGP’s creator, Phil Zimmermann. Zfone is based on the Z Real-time Transport Protocol (ZRTP), which is an extension of the Real-time Transport Protocol (RTP). ZRTP offers a very simple and robust approach to providing protection against the most common type of VoIP threats. Basically, the protocol offers a mechanism to guarantee high entropy in a Diffie- Hellman key exchange by using a session key that is computed through the hashing several secrets, including a short authentication string that is read aloud by callers. The common shared secret is calculated and used only for one session at a time. However, the protocol allows for a part of the shared secret to be cached for future sessions. The mechanism provides for protection for man-in-the-middle, call hijack, spoofing, and other common types of attacks. Also, this paper explores the fact that VoIP security is a very complicated issue and that the technology is far from being inherently insecure as many people usually claim. Introduction Voice over IP (VoIP) is transforming the telecommunication industry. It offers multiple opportunities such as lower call fees, convergence of voice and data networks, simplification of deployment, and greater integration with multiple applications that offer enhanced multimedia functionality [1]. However, notwithstanding all these technological and economic opportunities, VoIP also brings up new challenges. -
Cryptographic Control Standard, Version
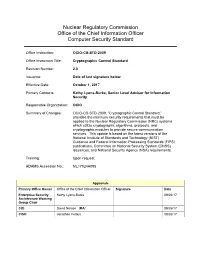
Nuclear Regulatory Commission Office of the Chief Information Officer Computer Security Standard Office Instruction: OCIO-CS-STD-2009 Office Instruction Title: Cryptographic Control Standard Revision Number: 2.0 Issuance: Date of last signature below Effective Date: October 1, 2017 Primary Contacts: Kathy Lyons-Burke, Senior Level Advisor for Information Security Responsible Organization: OCIO Summary of Changes: OCIO-CS-STD-2009, “Cryptographic Control Standard,” provides the minimum security requirements that must be applied to the Nuclear Regulatory Commission (NRC) systems which utilize cryptographic algorithms, protocols, and cryptographic modules to provide secure communication services. This update is based on the latest versions of the National Institute of Standards and Technology (NIST) Guidance and Federal Information Processing Standards (FIPS) publications, Committee on National Security System (CNSS) issuances, and National Security Agency (NSA) requirements. Training: Upon request ADAMS Accession No.: ML17024A095 Approvals Primary Office Owner Office of the Chief Information Officer Signature Date Enterprise Security Kathy Lyons-Burke 09/26/17 Architecture Working Group Chair CIO David Nelson /RA/ 09/26/17 CISO Jonathan Feibus 09/26/17 OCIO-CS-STD-2009 Page i TABLE OF CONTENTS 1 PURPOSE ............................................................................................................................. 1 2 INTRODUCTION .................................................................................................................. -

Transnationality, Morality, and Politics of Computing Expertise
UNIVERSITY OF CALIFORNIA Los Angeles Transnationality, Morality, and Politics of Co!"#ting Ex"ertise A dissertation s#%!i&ed in partial satis action o t'e re(#ire!ents for t'e degree )octor o P'iloso"'y in Anthro"ology %y L#is Feli"e Rosado M#rillo *+,- . Co"yright by L#is Feli"e Rosado M#rillo 2+,- A/STRACT OF T0E DISSERTATION Transnationality, Morality, and Politics o Co!"#ting E$"ertise %y L#is Feli"e Rosado M#rillo )octor o P'iloso"'y in Anthro"ology Uni1ersity o Cali ornia, Los Angeles, 2+,- Pro essor C'risto"'er M2 Kelty, C'air In this dissertation I e$amine t'e alterglo%alization o co!"#ter e$"ertise 5it' a oc#s on t'e creation o "olitical, econo!ic, !oral, and tec'nical ties among co!"#ter tec'nologists 5'o are identi6ed %y "eers and sel 7identi y as 8co!"#ter 'ac9ers2: ;e goal is to in1estigate 'o5 or!s o collaborati1e 5or9 are created on a local le1el alongside glo%al "ractices and disco#rses on co!"#ter 'ac9ing, linking local sites 5it' an e!ergent transnational do!ain o tec'nical e$c'ange and "olitical action. In order to ad1ance an #nderstanding o the e$"erience and "ractice o 'ac9ing %eyond its !ain axes o acti1ity in <estern Euro"e and the United States, I descri%e and analy4e "ro=ects and career trajectories o program!ers, engineers, and hac9er acti1ists w'o are ii !e!%ers o an international networ9 o co!!#nity s"aces called 8'ac9ers"aces: in the Paci6c region. -

Unlocking the Fifth Amendment: Passwords and Encrypted Devices
Fordham Law Review Volume 87 Issue 1 Article 9 2018 Unlocking the Fifth Amendment: Passwords and Encrypted Devices Laurent Sacharoff University of Arkansas School of Law, Fayetteville Follow this and additional works at: https://ir.lawnet.fordham.edu/flr Part of the Constitutional Law Commons, and the Criminal Procedure Commons Recommended Citation Laurent Sacharoff, Unlocking the Fifth Amendment: Passwords and Encrypted Devices, 87 Fordham L. Rev. 203 (2018). Available at: https://ir.lawnet.fordham.edu/flr/vol87/iss1/9 This Article is brought to you for free and open access by FLASH: The Fordham Law Archive of Scholarship and History. It has been accepted for inclusion in Fordham Law Review by an authorized editor of FLASH: The Fordham Law Archive of Scholarship and History. For more information, please contact [email protected]. UNLOCKING THE FIFTH AMENDMENT: PASSWORDS AND ENCRYPTED DEVICES Laurent Sacharoff* Each year, law enforcement seizes thousands of electronic devices— smartphones, laptops, and notebooks—that it cannot open without the suspect’s password. Without this password, the information on the device sits completely scrambled behind a wall of encryption. Sometimes agents will be able to obtain the information by hacking, discovering copies of data on the cloud, or obtaining the password voluntarily from the suspects themselves. But when they cannot, may the government compel suspects to disclose or enter their password? This Article considers the Fifth Amendment protection against compelled disclosures of passwords—a question that has split and confused courts. It measures this right against the legal right of law enforcement, armed with a warrant, to search the device that it has validly seized. -

Pgpfone Pretty Good Privacy Phone Owner’S Manual Version 1.0 Beta 7 -- 8 July 1996
Phil’s Pretty Good Software Presents... PGPfone Pretty Good Privacy Phone Owner’s Manual Version 1.0 beta 7 -- 8 July 1996 Philip R. Zimmermann PGPfone Owner’s Manual PGPfone Owner’s Manual is written by Philip R. Zimmermann, and is (c) Copyright 1995-1996 Pretty Good Privacy Inc. All rights reserved. Pretty Good Privacy™, PGP®, Pretty Good Privacy Phone™, and PGPfone™ are all trademarks of Pretty Good Privacy Inc. Export of this software may be restricted by the U.S. government. PGPfone software is (c) Copyright 1995-1996 Pretty Good Privacy Inc. All rights reserved. Phil’s Pretty Good engineering team: PGPfone for the Apple Macintosh and Windows written mainly by Will Price. Phil Zimmermann: Overall application design, cryptographic and key management protocols, call setup negotiation, and, of course, the manual. Will Price: Overall application design. He persuaded the rest of the team to abandon the original DOS command-line approach and designed a multithreaded event-driven GUI architecture. Also greatly improved call setup protocols. Chris Hall: Did early work on call setup protocols and cryptographic and key management protocols, and did the first port to Windows. Colin Plumb: Cryptographic and key management protocols, call setup negotiation, and the fast multiprecision integer math package. Jeff Sorensen: Speech compression. Will Kinney: Optimization of GSM speech compression code. Kelly MacInnis: Early debugging of the Win95 version. Patrick Juola: Computational linguistic research for biometric word list. -2- PGPfone Owner’s -

Case Study on the Official Scripts Electronic Applications in Bantul)
I.J. Information Engineering and Electronic Business, 2017, 4, 1-6 Published Online July 2017 in MECS (http://www.mecs-press.org/) DOI: 10.5815/ijieeb.2017.04.01 The Implementation of Pretty Good Privacy in eGovernment Applications (Case Study on the Official Scripts Electronic Applications in Bantul) Didit Suprihanto Department of Electrical Engineering Universitas Mulawarman, Kalimantan Timur, Indonesia, 75123 Email: [email protected] Tri Kuntoro Priyambodo Department of Computer Sciences & Electronics, Universitas Gadjah Mada, Yogyakarta, Indonesia, 55281 Corresponding Author Email: [email protected] Abstract—eGovernment application has evolved from the world [1]. The United Nations‘ global survey reports simply appearing as a website providing news and some ICT indicators that point to the measure of how far information, to the application that provides various a nation has gone in the implementation of e-governance services through online transactions. Provision of online such as: 1.E-readiness, 2.Web measure index, 3. transactions require the effectively and safely service, so Telecommunications infrastructure index, 4. Human the users can make sure that the entry data is secure and capital index, 5. E-participation index[2] will not be used by other parties which are not authorized. Information security is a major factor in the service of Security is also necessary for the service provider side of eGovernment. The using of the host to host in previous online transactions, it is necessary to keep the system, and services of eGovernment is considered as lacking in the data transactions sent through the communications security. Therefore, it needs more security to serve clients media and the data stored in the database are secured. -

The People Who Invented the Internet Source: Wikipedia's History of the Internet
The People Who Invented the Internet Source: Wikipedia's History of the Internet PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sat, 22 Sep 2012 02:49:54 UTC Contents Articles History of the Internet 1 Barry Appelman 26 Paul Baran 28 Vint Cerf 33 Danny Cohen (engineer) 41 David D. Clark 44 Steve Crocker 45 Donald Davies 47 Douglas Engelbart 49 Charles M. Herzfeld 56 Internet Engineering Task Force 58 Bob Kahn 61 Peter T. Kirstein 65 Leonard Kleinrock 66 John Klensin 70 J. C. R. Licklider 71 Jon Postel 77 Louis Pouzin 80 Lawrence Roberts (scientist) 81 John Romkey 84 Ivan Sutherland 85 Robert Taylor (computer scientist) 89 Ray Tomlinson 92 Oleg Vishnepolsky 94 Phil Zimmermann 96 References Article Sources and Contributors 99 Image Sources, Licenses and Contributors 102 Article Licenses License 103 History of the Internet 1 History of the Internet The history of the Internet began with the development of electronic computers in the 1950s. This began with point-to-point communication between mainframe computers and terminals, expanded to point-to-point connections between computers and then early research into packet switching. Packet switched networks such as ARPANET, Mark I at NPL in the UK, CYCLADES, Merit Network, Tymnet, and Telenet, were developed in the late 1960s and early 1970s using a variety of protocols. The ARPANET in particular led to the development of protocols for internetworking, where multiple separate networks could be joined together into a network of networks. In 1982 the Internet Protocol Suite (TCP/IP) was standardized and the concept of a world-wide network of fully interconnected TCP/IP networks called the Internet was introduced.