I2P, the Invisible Internet Projekt
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Cryptography
56 Protecting Information With Cryptography Chapter by Peter Reiher (UCLA) 56.1 Introduction In previous chapters, we’ve discussed clarifying your security goals, determining your security policies, using authentication mechanisms to identify principals, and using access control mechanisms to enforce poli- cies concerning which principals can access which computer resources in which ways. While we identified a number of shortcomings and prob- lems inherent in all of these elements of securing your system, if we re- gard those topics as covered, what’s left for the operating system to worry about, from a security perspective? Why isn’t that everything? There are a number of reasons why we need more. Of particular im- portance: not everything is controlled by the operating system. But per- haps you respond, you told me the operating system is all-powerful! Not really. It has substantial control over a limited domain – the hardware on which it runs, using the interfaces of which it is given control. It has no real control over what happens on other machines, nor what happens if one of its pieces of hardware is accessed via some mechanism outside the operating system’s control. But how can we expect the operating system to protect something when the system does not itself control access to that resource? The an- swer is to prepare the resource for trouble in advance. In essence, we assume that we are going to lose the data, or that an opponent will try to alter it improperly. And we take steps to ensure that such actions don’t cause us problems. -

Looking up Data in P2p Systems
LOOKING UP DATA IN P2P SYSTEMS Hari Balakrishnan, M. Frans Kaashoek, David Karger, Robert Morris, Ion Stoica∗ MIT Laboratory for Computer Science 1. Introduction a good example of how the challenges of designing P2P systems The recent success of some widely deployed peer-to-peer (P2P) can be addressed. file sharing applications has sparked new research in this area. We The recent algorithms developed by several research groups for are interested in the P2P systems that have no centralized control the lookup problem present a simple and general interface, a dis- or hierarchical organization, where the software running at each tributed hash table (DHT). Data items are inserted in a DHT and node is equivalent in functionality. Because these completely de- found by specifying a unique key for that data. To implement a centralized systems have the potential to significantly change the DHT, the underlying algorithm must be able to determine which way large-scale distributed systems are built in the future, it seems node is responsible for storing the data associated with any given timely to review some of this recent research. key. To solve this problem, each node maintains information (e.g., The main challenge in P2P computing is to design and imple- the IP address) of a small number of other nodes (“neighbors”) in ment a robust distributed system composed of inexpensive com- the system, forming an overlay network and routing messages in puters in unrelated administrative domains. The participants in a the overlay to store and retrieve keys. typical P2P system might be home computers with cable modem One might believe from recent news items that P2P systems are or DSL links to the Internet, as well as computers in enterprises. -

PCI Assessment Evidence of PCI Policy Compliance
PCI Assessment Evidence of PCI Policy Compliance CONFIDENTIALITY NOTE: The information contained in this report document is for the Prepared for: exclusive use of the client specified above and may contain confidential, privileged and non-disclosable information. If the recipient of this report is not the client or Prospect or Customer addressee, such recipient is strictly prohibited from reading, photocopying, distributing or otherwise using this report or its contents in any way. Prepared by: Your Company Name Evidence of PCI Policy Compliance PCI ASSESSMENT Table of Contents 1 - Overview 1.1 - Security Officer 1.2 - Overall Risk 2 - PCI DSS Evidence of Compliance 2.1 - Install and maintain firewall to protect cardholder data 2.1.1.1 - Requirements for firewall at each Internet connections and between DMZ and internal network zone 2.1.1.2 - Business justification for use of all services, protocols and ports allowed 2.1.2 - Build firewall and router configurations that restrict connections between untrusted networks and the cardholder data environment 2.1.2.1 - Restrict inbound and outbound to that which is necessary for the cardholder data environment 2.1.2.3 - Do not allow unauthorized outbound traffic from the cardholder data environment to the Internet 2.1.2.4 - Implement stateful inspection (also known as dynamic packet filtering) 2.1.2.5 - Do not allow unauthorized outbound traffic from the cardholder data environment to the Internet 2.2 - Prohibition of vendor-supplied default password for systems and security parameters 2.2.1 -

Self-Encrypting Deception: Weaknesses in the Encryption of Solid State Drives
Self-encrypting deception: weaknesses in the encryption of solid state drives Carlo Meijer Bernard van Gastel Institute for Computing and Information Sciences School of Computer Science Radboud University Nijmegen Open University of the Netherlands [email protected] and Institute for Computing and Information Sciences Radboud University Nijmegen Bernard.vanGastel@{ou.nl,ru.nl} Abstract—We have analyzed the hardware full-disk encryption full-disk encryption. Full-disk encryption software, especially of several solid state drives (SSDs) by reverse engineering their those integrated in modern operating systems, may decide to firmware. These drives were produced by three manufacturers rely solely on hardware encryption in case it detects support between 2014 and 2018, and are both internal models using the SATA and NVMe interfaces (in a M.2 or 2.5" traditional form by the storage device. In case the decision is made to rely on factor) and external models using the USB interface. hardware encryption, typically software encryption is disabled. In theory, the security guarantees offered by hardware encryp- As a primary example, BitLocker, the full-disk encryption tion are similar to or better than software implementations. In software built into Microsoft Windows, switches off software reality, we found that many models using hardware encryption encryption and completely relies on hardware encryption by have critical security weaknesses due to specification, design, and implementation issues. For many models, these security default if the drive advertises support. weaknesses allow for complete recovery of the data without Contribution. This paper evaluates both internal and external knowledge of any secret (such as the password). -
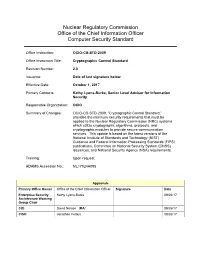
Cryptographic Control Standard, Version
Nuclear Regulatory Commission Office of the Chief Information Officer Computer Security Standard Office Instruction: OCIO-CS-STD-2009 Office Instruction Title: Cryptographic Control Standard Revision Number: 2.0 Issuance: Date of last signature below Effective Date: October 1, 2017 Primary Contacts: Kathy Lyons-Burke, Senior Level Advisor for Information Security Responsible Organization: OCIO Summary of Changes: OCIO-CS-STD-2009, “Cryptographic Control Standard,” provides the minimum security requirements that must be applied to the Nuclear Regulatory Commission (NRC) systems which utilize cryptographic algorithms, protocols, and cryptographic modules to provide secure communication services. This update is based on the latest versions of the National Institute of Standards and Technology (NIST) Guidance and Federal Information Processing Standards (FIPS) publications, Committee on National Security System (CNSS) issuances, and National Security Agency (NSA) requirements. Training: Upon request ADAMS Accession No.: ML17024A095 Approvals Primary Office Owner Office of the Chief Information Officer Signature Date Enterprise Security Kathy Lyons-Burke 09/26/17 Architecture Working Group Chair CIO David Nelson /RA/ 09/26/17 CISO Jonathan Feibus 09/26/17 OCIO-CS-STD-2009 Page i TABLE OF CONTENTS 1 PURPOSE ............................................................................................................................. 1 2 INTRODUCTION .................................................................................................................. -

Conducting and Optimizing Eclipse Attacks in the Kad Peer-To-Peer Network
Conducting and Optimizing Eclipse Attacks in the Kad Peer-to-Peer Network Michael Kohnen, Mike Leske, and Erwin P. Rathgeb University of Duisburg-Essen, Institute for Experimental Mathematics, Ellernstr. 29, 45326 Essen [email protected], [email protected], [email protected] Abstract. The Kad network is a structured P2P network used for file sharing. Research has proved that Sybil and Eclipse attacks have been possible in it until recently. However, the past attacks are prohibited by newly implemented secu- rity measures in the client applications. We present a new attack concept which overcomes the countermeasures and prove its practicability. Furthermore, we analyze the efficiency of our concept and identify the minimally required re- sources. Keywords: P2P security, Sybil attack, Eclipse attack, Kad. 1 Introduction and Related Work P2P networks form an overlay on top of the internet infrastructure. Nodes in a P2P network interact directly with each other, i.e., no central entity is required (at least in case of structured P2P networks). P2P networks have become increasingly popular mainly because file sharing networks use P2P technology. Several studies have shown that P2P traffic is responsible for a large share of the total internet traffic [1, 2]. While file sharing probably accounts for the largest part of the P2P traffic share, also other P2P applications exist which are widely used, e.g., Skype [3] for VoIP or Joost [4] for IPTV. The P2P paradigm is becoming more and more accepted also for professional and commercial applications (e.g., Microsoft Groove [5]), and therefore, P2P technology is one of the key components of the next generation internet. -

Hartkad: a Hard Real-Time Kademlia Approach
HaRTKad: A Hard Real-Time Kademlia Approach Jan Skodzik, Peter Danielis, Vlado Altmann, Dirk Timmermann University of Rostock Institute of Applied Microelectronics and Computer Engineering 18051 Rostock, Germany, Tel./Fax: +49 381 498-7284 / -1187251 Email: [email protected] Abstract—The Internet of Things is becoming more and time behavior. Additionally, many solutions leak flexibility and more relevant in industrial environments. As the industry itself need a dedicated instance for administrative tasks. These issues has different requirements like (hard) real-time behavior for will becomes more relevant in the future. As mentioned in many scenarios, different solutions are needed to fulfill future challenges. Common Industrial Ethernet solution often leak [3], the future for the industry will be more intelligent devices, scalability, flexibility, and robustness. Most realizations also which can act more dynamically. Facilities as one main area require special hardware to guarantee a hard real-time behavior. of application will consist of more devices still requiring real- Therefore, an approach is presented to realize a hard real- time or even hard real-time behavior. So we think, the existing time network for automation scenarios using Peer-to-Peer (P2P) solutions will not fulfill the future challenges in terms of technology. Kad as implementation variant of the structured decentralized P2P protocol Kademlia has been chosen as base scalability, flexibility, and robustness. for the realization. As Kad is not suitable for hard real-time Peer-to-Peer (P2P) networks instead offer an innovative applications per se, changes of the protocol are necessary. Thus, alternative to the typical Client-Server or Master-Slave concepts Kad is extended by a TDMA-based mechanism. -

I2P – (K)Eine Alternative Zu Tor
I2P – (K)Eine Alternative zu Tor 17. Augsburger Linux-Infotag 2018 21.04.2018 I2P – wasn das? • Low Latency Relay Netzwerk • Anonymes Netzwerk • „Black Box“ Tunnel zwischen Client und Server • Internes Netzwerk, fast keine OutProxies • Internationales Entwicklerteam mit ~10 Leuten • Keine Firma, kein Verein, alles rein privat • OpenSource • Start 2003 als Freenet Project Transport Grundsätze von I2P • I2P versteckt nicht die Nutzung von I2P • I2P versteckt die Nutzerspuren in I2P • User soll sicher mit anderen anonym kommunizieren können • Vertraue niemanden anderen, nur dir selber • Selbst regulierendes Netz ohne zentrale Instanzen • OpenSource • Möglichst wenig eigene Crypto – Peer & Academic Review nötig Funktionsweise, Teil 1 • Startup: Seeddatei von fixen Servern (oder alternative Quellen) holen • Connect zu anderen I2P Peers aus der Seeddatei • Aufbau lokaler netDB – Statistiken über bekannte I2P Peers • Inbetriebnahme von lokalen Hidden Services • Jeder Hidden Service erstellt per Default 2 Ein- & 2 Ausgangstunnel • Jeder Tunnel hat per Default 3 Hops • Tunnel werden aus bekannten, fähigen Peers der netDB erstellt • Clients und Server bauen Hidden Services auf Funktionsweise, Teil 2 • Nach Tunnelaufbau publizieren eines Leasesets an FloodFillDB • FloodFillDB: verteilte Datenbank auf ~1000 Peers • LeaseSet: Information welcher Eingangstunnel zu welchem Hidden Service weiterleitet • Client fragt FF-DB nach LeaseSet zu einem Hidden Service • Client sendet Daten an Server, Server antwortet, wenn erfolgreich • Roundtrip mit 12 Hops: -

Unlocking the Fifth Amendment: Passwords and Encrypted Devices
Fordham Law Review Volume 87 Issue 1 Article 9 2018 Unlocking the Fifth Amendment: Passwords and Encrypted Devices Laurent Sacharoff University of Arkansas School of Law, Fayetteville Follow this and additional works at: https://ir.lawnet.fordham.edu/flr Part of the Constitutional Law Commons, and the Criminal Procedure Commons Recommended Citation Laurent Sacharoff, Unlocking the Fifth Amendment: Passwords and Encrypted Devices, 87 Fordham L. Rev. 203 (2018). Available at: https://ir.lawnet.fordham.edu/flr/vol87/iss1/9 This Article is brought to you for free and open access by FLASH: The Fordham Law Archive of Scholarship and History. It has been accepted for inclusion in Fordham Law Review by an authorized editor of FLASH: The Fordham Law Archive of Scholarship and History. For more information, please contact [email protected]. UNLOCKING THE FIFTH AMENDMENT: PASSWORDS AND ENCRYPTED DEVICES Laurent Sacharoff* Each year, law enforcement seizes thousands of electronic devices— smartphones, laptops, and notebooks—that it cannot open without the suspect’s password. Without this password, the information on the device sits completely scrambled behind a wall of encryption. Sometimes agents will be able to obtain the information by hacking, discovering copies of data on the cloud, or obtaining the password voluntarily from the suspects themselves. But when they cannot, may the government compel suspects to disclose or enter their password? This Article considers the Fifth Amendment protection against compelled disclosures of passwords—a question that has split and confused courts. It measures this right against the legal right of law enforcement, armed with a warrant, to search the device that it has validly seized. -

Pgpfone Pretty Good Privacy Phone Owner’S Manual Version 1.0 Beta 7 -- 8 July 1996
Phil’s Pretty Good Software Presents... PGPfone Pretty Good Privacy Phone Owner’s Manual Version 1.0 beta 7 -- 8 July 1996 Philip R. Zimmermann PGPfone Owner’s Manual PGPfone Owner’s Manual is written by Philip R. Zimmermann, and is (c) Copyright 1995-1996 Pretty Good Privacy Inc. All rights reserved. Pretty Good Privacy™, PGP®, Pretty Good Privacy Phone™, and PGPfone™ are all trademarks of Pretty Good Privacy Inc. Export of this software may be restricted by the U.S. government. PGPfone software is (c) Copyright 1995-1996 Pretty Good Privacy Inc. All rights reserved. Phil’s Pretty Good engineering team: PGPfone for the Apple Macintosh and Windows written mainly by Will Price. Phil Zimmermann: Overall application design, cryptographic and key management protocols, call setup negotiation, and, of course, the manual. Will Price: Overall application design. He persuaded the rest of the team to abandon the original DOS command-line approach and designed a multithreaded event-driven GUI architecture. Also greatly improved call setup protocols. Chris Hall: Did early work on call setup protocols and cryptographic and key management protocols, and did the first port to Windows. Colin Plumb: Cryptographic and key management protocols, call setup negotiation, and the fast multiprecision integer math package. Jeff Sorensen: Speech compression. Will Kinney: Optimization of GSM speech compression code. Kelly MacInnis: Early debugging of the Win95 version. Patrick Juola: Computational linguistic research for biometric word list. -2- PGPfone Owner’s -

Research Article a P2P Framework for Developing Bioinformatics Applications in Dynamic Cloud Environments
Hindawi Publishing Corporation International Journal of Genomics Volume 2013, Article ID 361327, 9 pages http://dx.doi.org/10.1155/2013/361327 Research Article A P2P Framework for Developing Bioinformatics Applications in Dynamic Cloud Environments Chun-Hung Richard Lin,1 Chun-Hao Wen,1,2 Ying-Chih Lin,3 Kuang-Yuan Tung,1 Rung-Wei Lin,1 and Chun-Yuan Lin4 1 Department of Computer Science and Engineering, National Sun Yat-sen University, No. 70 Lien-hai Road, Kaohsiung City 80424, Taiwan 2 Department of Information Technology, Meiho University, No. 23 Pingkuang Road, Neipu, Pingtung 91202, Taiwan 3 Department of Applied Mathematics, Feng Chia University, No. 100 Wenhwa Road, Seatwen, Taichung City 40724, Taiwan 4 Department of Computer Science and Information Engineering, Chang Gung University, No. 259 Sanmin Road, Guishan Township, Taoyuan 33302, Taiwan Correspondence should be addressed to Ying-Chih Lin; [email protected] Received 22 January 2013; Revised 5 April 2013; Accepted 20 April 2013 Academic Editor: Che-Lun Hung Copyright © 2013 Chun-Hung Richard Lin et al. This is an open access article distributed under the Creative Commons Attribution License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited. Bioinformatics is advanced from in-house computing infrastructure to cloud computing for tackling the vast quantity of biological data. This advance enables large number of collaborative researches to share their works around the world. In view of that, retrieving biological data over the internet becomes more and more difficult because of the explosive growth and frequent changes. Various efforts have been made to address the problems of data discovery and delivery in the cloud framework, but most of them suffer the hindrance by a MapReduce master server to track all available data. -

Tor - Der Zwiebelrouter Übersicht Client Installieren & Einrichten Serverknoten & Hidden Services Betreiben
Anonym ins Internet Computerlabor im KuZeB Ubuntu-Workshop 10.9.2007 Kire www.kire.ch Template von Chih-Hao Tsai (chtsai.org) Creative Commons License (by-nc-sa) creativecommons.org/licenses/by-nc-sa/2.5/dee.de Inhaltsverzeichnis Spurensuche im Internet Programmübersicht JAP, I2P, Freenet Tor - der Zwiebelrouter Übersicht Client installieren & einrichten Serverknoten & Hidden Services betreiben 2 Spurensuche Server-Logs Webserver IP-Adresse, Browser, Betriebssystem, Referrer Mailserver Nameserver (DNS) Aufbewahrungspflicht der IP-Zuordnungen CH: 6 Monate durch Provider EU: 6 - 24 Monate Eindeutige Merkmale MAC-Adresse “Einwahl” Cookies & IDs lokaler Computer Cache & Browser-History 3 Programmübersicht JAP - Java Anon Proxy Web-Anonymizer für http, https und ftp TU Dresden, Uni Regensburg und Unabhängiges Landeszentrum für Datenschutz Schleswig-Holstein Opensource Plattformunabhängig, da in Java entwickelt benutzt fixe Mix-Kaskaden Verschlüsselung bis zum letzten Knoten der Kaskade neuer kommerzieller Dienste JonDonym 4 Programmübersicht I2P - Invisible Internet Project anonymes / pseudonymes VPN die meisten EntwicklerInnen sind anonym junges Projekt ebenfalls Opensource und Java Datenverkehr bleibt normalerweise im I2P End-zu-End-Verschlüsselung Peer-to-Peer Proxy oder Erweiterungen für vorhandene Clients Firefox (Proxy), Azureus (Erweiterung) Eigene Clients und Server Susimail (Client), jetty (Webserver), Syndie (Foren/Blogs) es kann aber auch ein I2P-Tunnel zu einem Apache Webserver eingerichtet werden 5 Programmübersicht Freenet zensurresistentes