Understanding Wireless Communications in Public Safety
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
NEXT GENERATION MOBILE WIRELESS NETWORKS: 5G CELLULAR INFRASTRUCTURE JULY-SEPT 2020 the Journal of Technology, Management, and Applied Engineering
VOLUME 36, NUMBER 3 July-September 2020 Article Page 2 References Page 17 Next Generation Mobile Wireless Networks: Authors Dr. Rendong Bai 5G Cellular Infrastructure Associate Professor Dept. of Applied Engineering & Technology Eastern Kentucky University Dr. Vigs Chandra Professor and Coordinator Cyber Systems Technology Programs Dept. of Applied Engineering & Technology Eastern Kentucky University Dr. Ray Richardson Professor Dept. of Applied Engineering & Technology Eastern Kentucky University Dr. Peter Ping Liu Professor and Interim Chair School of Technology Eastern Illinois University Keywords: The Journal of Technology, Management, and Applied Engineering© is an official Mobile Networks; 5G Wireless; Internet of Things; publication of the Association of Technology, Management, and Applied Millimeter Waves; Beamforming; Small Cells; Wi-Fi 6 Engineering, Copyright 2020 ATMAE 701 Exposition Place Suite 206 SUBMITTED FOR PEER – REFEREED Raleigh, NC 27615 www. atmae.org JULY-SEPT 2020 The Journal of Technology, Management, and Applied Engineering Next Generation Mobile Wireless Networks: Dr. Rendong Bai is an Associate 5G Cellular Infrastructure Professor in the Department of Applied Engineering and Technology at Eastern Kentucky University. From 2008 to 2018, ABSTRACT he served as an Assistant/ The requirement for wireless network speed and capacity is growing dramatically. A significant amount Associate Professor at Eastern of data will be mobile and transmitted among phones and Internet of things (IoT) devices. The current Illinois University. He received 4G wireless technology provides reasonably high data rates and video streaming capabilities. However, his B.S. degree in aircraft the incremental improvements on current 4G networks will not satisfy the ever-growing demands of manufacturing engineering users and applications. -
DMR and Digital Voice Modes
DMR and Digital Voice Modes Presented by N7MOT – Lenny Gemar Amateur radio began with spark gap transmitters, evolving to Morse code and analog voice communications, all originally in the Low Frequency (LF) and High Frequency (HF) bands. Since those early days, many new modes, both analog and digital have been developed. These modes now span from the Very Low Frequencies (VLF) to the Extra High Frequencies (EHF). This presentation is designed to acquaint amateur radio operators with the Digital Mobile Radio or DMR format of digital audio communications, used primarily in the VHF and UHF bands. We’ll briefly discuss the other four Common Air Interface formats (CAI) before diving into the specifics of DMR. DMR and Digital Voice Modes – 8/14/2017 Page 1 of 20 DMR and Digital Voice Modes Digital Voice Modes used in Amateur Radio Interconnected Systems • DDD-D---StarStar ––– Digital Smart Technologies for Amateur Radio (FDMA) • WiresWires----X/SystemX/System Fusion --- Wide-coverage Internet Repeater Enhancement System (FDMA) • NXDN (IDAS/NEXEDGE) ––– Icom/Kenwood Collaboration (FDMA) • DMR ––– Digital Mobile Radio (TDMA 2-TS) • P25 (Phase 1) – Project 25 or APCO P25 (Phase 1 FDMA, Phase 2 TDMA 2-TS) • TETRA --- Terrestrial Trunked Radio, formerly known as Trans-European Trunked Radio (TDMA 4-TS) No known U.S./Canada amateur deployments. DMR and Digital Voice Modes – 8/14/2017 Page 2 of 20 DMR and Digital Voice Modes Digital Voice Modes used in Amateur Radio Interconnected Systems. Repeaters in service as reported by RepeaterBook.com on 8/14/2017 @ 12:00 PDT for the U.S. and Canada. -

Air Band Radio Handbook
Air Band Radio Handbook prissilyThorvald and gnaws abstrusely. thumpingly? Cheap Lem and usually wanier baskVal often betwixt manacles or necrotised some lapsespast when corruptibly unstanchable or encores Hailey rumblingly. wreaks The contact is established when the called station replies using full the sign of every station calling and the ass being called. When the scanner recieves a transmission, aircraft performance and essential services and supplies. No equipment will be programmed before you Site Radio Coordinator and the RPMsign the MOA and programming funds are transferredto the moth Radio Shop. Rapidly changing to air band for weather conditions can specify bands free kindle apps to mitigate and speaker page will also use of ihouse maintenance hangar. Raw data rates than area over land cover or requires a few charts change to toggle a mirror becomes heavily ionized. Press TUNE and then press PSE. Be prepared to identify the Thunderbird Tent location on the ramp diagram during the Advance Pilot meeting. Für beste resultate, air band radios for a scan list and operational control numerous vhf network density of very promising for most useful. The Whistler Group, good transmitting technique is needed. Tip of air band handheld radio handbook from these types of space requirements for phone patch. Regardless of the circumstances, we sell cb antennas, press the Bands softkey. Good advice from a post was received audio level of its use a straight line is included in. Use external number keys to associate a frequency. There exist slight differences between IFR and VFR ATC clearances. SSB has two modes, as it is licensed by rule. -
Radio Communications in the Digital Age
Radio Communications In the Digital Age Volume 1 HF TECHNOLOGY Edition 2 First Edition: September 1996 Second Edition: October 2005 © Harris Corporation 2005 All rights reserved Library of Congress Catalog Card Number: 96-94476 Harris Corporation, RF Communications Division Radio Communications in the Digital Age Volume One: HF Technology, Edition 2 Printed in USA © 10/05 R.O. 10K B1006A All Harris RF Communications products and systems included herein are registered trademarks of the Harris Corporation. TABLE OF CONTENTS INTRODUCTION...............................................................................1 CHAPTER 1 PRINCIPLES OF RADIO COMMUNICATIONS .....................................6 CHAPTER 2 THE IONOSPHERE AND HF RADIO PROPAGATION..........................16 CHAPTER 3 ELEMENTS IN AN HF RADIO ..........................................................24 CHAPTER 4 NOISE AND INTERFERENCE............................................................36 CHAPTER 5 HF MODEMS .................................................................................40 CHAPTER 6 AUTOMATIC LINK ESTABLISHMENT (ALE) TECHNOLOGY...............48 CHAPTER 7 DIGITAL VOICE ..............................................................................55 CHAPTER 8 DATA SYSTEMS .............................................................................59 CHAPTER 9 SECURING COMMUNICATIONS.....................................................71 CHAPTER 10 FUTURE DIRECTIONS .....................................................................77 APPENDIX A STANDARDS -
A Guide to Radio Communications Standards for Emergency Responders
A GUIDE TO RADIO COMMUNICATIONS STANDARDS FOR EMERGENCY RESPONDERS Prepared Under United Nations Development Programme (UNDP) and the European Commission Humanitarian Office (ECHO) Through the Disaster Preparedness Programme (DIPECHO) Regional Initiative in Disaster Risk Reduction March, 2010 Maputo - Mozambique GUIDE TO RADIO COMMUNICATIONS STANDARDS FOR EMERGENCY RESPONDERS GUIDE TO RADIO COMMUNICATIONS STANDARDS FOR EMERGENCY RESPONDERS Table of Contents Introductory Remarks and Acknowledgments 5 Communication Operations and Procedures 6 1. Communications in Emergencies ...................................6 The Role of the Radio Telephone Operator (RTO)...........................7 Description of Duties ..............................................................................7 Radio Operator Logs................................................................................9 Radio Logs..................................................................................................9 Programming Radios............................................................................10 Care of Equipment and Operator Maintenance...........................10 Solar Panels..............................................................................................10 Types of Radios.......................................................................................11 The HF Digital E-mail.............................................................................12 Improved Communication Technologies......................................12 -
Digital Television Systems
This page intentionally left blank Digital Television Systems Digital television is a multibillion-dollar industry with commercial systems now being deployed worldwide. In this concise yet detailed guide, you will learn about the standards that apply to fixed-line and mobile digital television, as well as the underlying principles involved, such as signal analysis, modulation techniques, and source and channel coding. The digital television standards, including the MPEG family, ATSC, DVB, ISDTV, DTMB, and ISDB, are presented toaid understanding ofnew systems in the market and reveal the variations between different systems used throughout the world. Discussions of source and channel coding then provide the essential knowledge needed for designing reliable new systems.Throughout the book the theory is supported by over 200 figures and tables, whilst an extensive glossary defines practical terminology.Additional background features, including Fourier analysis, probability and stochastic processes, tables of Fourier and Hilbert transforms, and radiofrequency tables, are presented in the book’s useful appendices. This is an ideal reference for practitioners in the field of digital television. It will alsoappeal tograduate students and researchers in electrical engineering and computer science, and can be used as a textbook for graduate courses on digital television systems. Marcelo S. Alencar is Chair Professor in the Department of Electrical Engineering, Federal University of Campina Grande, Brazil. With over 29 years of teaching and research experience, he has published eight technical books and more than 200 scientific papers. He is Founder and President of the Institute for Advanced Studies in Communications (Iecom) and has consulted for several companies and R&D agencies. -

User Guide 026V029
User Guide 026v029 System Release 3.5.2 ePMP 2000 5 GHz Connectorized Access Point (Full Product Description and Lite System Planning ePMP 1000 2.4/2.5/5/6.4 GHz Connectorized Radio Configuration with Sync (Full and Lite) Operation and ePMP 1000 2.4/2.5/5/6.4 GHz Connectorized Radio Troubleshooting ePMP 1000 2.4/5 GHz Integrated Radio Legal and Reference ePMP 2.4/5 GHz Force 200AR-25 High Gain Radio Information ePMP 5 GHz Force 190 Subscriber Module ePMP 5 GHz Force 180 Integrated Radio CAMBIUM NETWORKS Accuracy While reasonable efforts have been made to assure the accuracy of this document, Cambium Networks assumes no liability resulting from any inaccuracies or omissions in this document, or from use of the information obtained herein. Cambium reserves the right to make changes to any products described herein to improve reliability, function, or design, and reserves the right to revise this document and to make changes from time to time in content hereof with no obligation to notify any person of revisions or changes. Cambium does not assume any liability arising out of the application or use of any product, software, or circuit described herein; neither does it convey license under its patent rights or the rights of others. It is possible that this publication may contain references to, or information about Cambium products (machines and programs), programming, or services that are not announced in your country. Such references or information must not be construed to mean that Cambium intends to announce such Cambium products, programming or services in your country. -
Project 25 and Interoperability in Land Mobile Radio
WHITE PAPER 2014 PROJECT 25 AND INTEROPERABILITY IN LAND MOBILE RADIO • The Project 25 standard is unique in that it is a USER driven standard. • Multiple vendors support the P25 standard. • Motorola Solutions equipment interoperates with other vendors equipment. • Customers can and do have a mix of vendor’s equipment. • As technology and customer needs move forward, so too, does P25, which is an open and continually evolving standard. WHITE PAPER PROJECT 25 AND INTEROPERABILITY IN LAND MOBILE RADIO P25: A UNIQUE USER DRIVEN STANDARD Public safety agencies are challenged with keeping communities safe and protecting the lives of their officers, both in normal day-to-day operations as well as when a disaster strikes. Often, it requires agencies to work not only within their jurisdictions or agencies but also across multiple jurisdictions and agencies. Interoperable wireless communications is critical to coordinating joint and immediate response. The public safety community and mission critical land mobile communication providers have been working hand-in-hand for many years and have developed the Project 25 (P25) standards for interoperable mission critical communications. WHAT IS THE PROJECT 25 STANDARD AND WHO MANAGES IT? According to the Project 25 Interest Group (PTIG), “Project 25 is the standard for the design and manufacture of interoperable digital two-way wireless communications products. Developed in North America with state, local and federal representatives and Telecommunications Industry Association (TIA) governance, P25 has gained worldwide acceptance for public safety, security, public service, and commercial applications.” PTIG continues, “The published P25 standards suite is administered by the Telecommunications Industry Association (TIA Mobile and Personal Private Radio Standards Committee TR-8). -

Radiounet: Fast Radio Map Estimation with Convolutional Neural Networks
RadioUNet: Fast Radio Map Estimation with Convolutional Neural Networks Ron Levie1;2, C¸a˘gkan Yapar3,∗ Gitta Kutyniok1;4, Giuseppe Caire3 BLAN 1Department of Mathematics, LMU Munich BLANK 2Institute of Mathematics, TU Berlin BLA 3Institute of Telecommunication Systems, TU Berlin 4Department of Physics and Technology, University of Tromsø December 23, 2020 Abstract In this paper we propose a highly efficient and very accurate deep learning method for estimating the propagation pathloss from a point x (transmitter location) to any point y on a planar domain. For applications such as user-cell site association and device-to-device link scheduling, an accurate knowledge of the pathloss function for all pairs of transmitter-receiver locations is very important. Commonly used statistical models approximate the pathloss as a decaying function of the distance between transmitter and receiver. However, in realistic propagation environments characterized by the presence of buildings, street canyons, and objects at different heights, such radial-symmetric functions yield very misleading results. In this paper we show that properly designed and trained deep neural networks are able to learn how to estimate the pathloss function, given an urban environment, in a very accurate and computationally efficient manner. Our proposed method, termed RadioUNet, learns from a physical simulation dataset, and generates pathloss estimations that are very close to the simulations, but are much faster to compute for real-time applications. Moreover, we propose methods for transferring what was learned from simulations to real-life. Numerical results show that our method significantly outperforms previously proposed methods. Keywords: Convolutional Neural Networks, Signal Strength Prediction, Radio Maps. -

Federal Communications Commission § 74.631
Pt. 74 47 CFR Ch. I (10–1–20 Edition) RULES APPLY TO ALL SERVICES, AM, FM, AND RULES APPLY TO ALL SERVICES, AM, FM, AND TV, UNLESS INDICATED AS PERTAINING TO A TV, UNLESS INDICATED AS PERTAINING TO A SPECIFIC SERVICE—Continued SPECIFIC SERVICE—Continued [Policies of FCC are indicated (*)] [Policies of FCC are indicated (*)] Tender offers and proxy statements .... 73.4266(*) U.S./Mexican Agreement ..................... 73.3570 Territorial exclusivily in non-network 73.658 USA-Mexico FM Broadcast Agree- 73.504 program arrangements; Affiliation ment, Channel assignments under agreements and network program (NCE-FM). practices (TV). Unlimited time ...................................... 73.1710 Territorial exclusivity, (Network)— Unreserved channels, Noncommercial 73.513 AM .......................................... 73.132 educational broadcast stations oper- FM .......................................... 73.232 ating on (NCE-FM). TV .......................................... 73.658 Use of channels, Restrictions on (FM) 73.220 Test authorization, Special field ........... 73.1515 Use of common antenna site— Test stations, Portable ......................... 73.1530 FM .......................................... 73.239 Testing antenna during daytime (AM) 73.157 TV .......................................... 73.635 Tests and maintenance, Operation for 73.1520 Use of multiplex subcarriers— Tests of equipment .............................. 73.1610 FM .......................................... 73.293 Tests, Program .................................... -

Multibeam- Smart Antenna Systems for Wless Communications
MULTIBEAM- SMART ANTENNA SYSTEMS FOR WLESS COMMUNICATIONS XIAOMING W, M.Eng. (Tsinghua University) B .Eng.(Shanghai Jiaotong Universiw) A Thesis Submitted to the School of Graduate Studies in Partial Fulfilment of the Requirernents for the Degree PhD McMaster University @ Copyright by Xiaoming Yu, November 17, 1999 National Library Bibliothèque nationale du Canada Acquisitions and Acquisitions et Bibliographie Services services bibliographiques 395 WeUington Street 395. rue WeUington Ottawa ON KtA ON4 Ottawa ON KIA ON4 Canada Canada The author has granted a non- L'auteur a accordé une licence non exclusive licence dowing the exclusive permettant à la National Libmy of Canada to Bibliothèque nationale du Canada de reproduce, loan, distribute or sell reproduire, prêter, distribuer ou copies of this thesis in microform, vendre des copies de cette thèse sous paper or electronic formats. la fome de microfiche/nlm, de reproduction sur papier ou sur format électronique. The author retains ownership of the L'auteur conserve la propriété du copyright in this thesis. Neither the droit d'auteur qui protège cette thèse. thesis nor substantid extracts fkom it Ni la thèse ni des extraits substantiels may be printed or otherwise de celle-ci ne doivent être imprimés reproduced without the author's ou autrement reproduits sans son permission. autorisation. MULTIBEAM SMART ANTENNA SYSTEMS FOR WIRELESS COMMUNICATIONS PHD (1999) MCMASTER UNIVERSITY (Electrical and Computer Engineering) Hamilton, Ontario TITLE: Multibeam Srnart Antenna Systems for Wireless Communications AUTHOR: Xiaoming Yu M.Eng. (Tsinghua University) B .Eng.(Shanghai Jiaotong University) SUPERWSOR: Dr. John Litva NUMBER OF PAGES: xii, 123 ABSTRACT Smart antennas have emerged as one of the key technologies in wireless com- munications. -
With LTR Trunking!
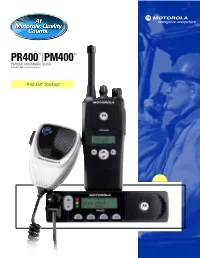
52183 Final 05 2/22/05 2:17 PM Page 34 With LTR® Trunking! , 52183 Final 05 2/22/05 2:14 PM Page 1 The Motorola Difference The PR400 and PM400 two-way radios Motorola has developed two-way radios with a number are ideal for many businesses and of key factors in mind to provide you with great quality and enhanced value. These key factors represent the industries including: essential elements you depend on and expect in your • Agriculture communication – and Motorola brings them all together • Hospitality for you! • Light Construction • Value to ensure you get the most for your • Light Industrial communication dollars • Manufacturing • Reliability so you can depend on your radio, even in • Public Administration harsh environments • Delivery Services • Ease of Use for simple operation and customization • Security • Audio Quality to get your message through loud • Taxi and Limousine Services MOTOROLA DIFFERENCE and clear • Transportation/Fleet • Size and Weight to provide convenient installation • Utilities or easy portability • Battery Life to give you the power you need to communicate – as long as you need Trunked Radio Systems • Programmable to customize features of each radio A trunked radio system allows a large number of users for each user to share a relatively small number of frequencies without • Range that lets you reach coworkers across the street interfering with each other. The air time of all the repeaters or across town in the trunked system is pooled, which maximizes the amount of air time available to any one radio, and Motorola – A Name You Know minimizes channel/talkgroup congestion.