FORTRAN Now: FORTRAN the First Generation Backus at IBM Backus
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Weeel for the IBM 704 Data Processing System Reference Manual
aC sicru titi Wane: T| weeel for the IBM 704 Data Processing System Reference Manual FORTRAN II for the IBM 704 Data Processing System © 1958 by International Business Machines Corporation MINOR REVISION This edition, C28-6000-2, is a minor revision of the previous edition, C28-6000-1, but does not obsolete it or C28-6000. The principal change is the substitution of a new discussion of the COMMONstatement. TABLE OF CONTENTS Page General Introduction... ee 1 Note on Associated Publications Le 6 PART |. THE FORTRAN If LANGUAGE , 7 Chapter 1. General Properties of a FORTRAN II Source Program . 9 Types of Statements. 1... 1. ee ee ee we 9 Types of Source Programs. .......... ~ ee 9 Preparation of Input to FORTRAN I Translatorcee es 9 Classification of the New FORTRAN II Statements. 9 Chapter 2. Arithmetic Statements Involving Functions. ....... 10 Arithmetic Statements. .. 1... 2... ew eee . 10 Types of Functions . il Function Names. ..... 12 Additional Examples . 13 Chapter 3. The New FORTRAN II Statements ......... 2 16 CALL .. 16 SUBROUTINE. 2... 6 ee ee te ew eh ee es 17 FUNCTION. 2... 1 ee ee ww ew ew ww ew ew ee 18 COMMON ...... 2. ee se ee eee wee . 20 RETURN. 2... 1 1 ew ee te ee we wt wt wh wt 22 END... «4... ee we ee ce ew oe te tw . 22 PART Il, PRIMER ON THE NEW FORTRAN II FACILITIES . .....0+2«~W~ 25 Chapter 1. FORTRAN II Function Subprograms. 0... eee 27 Purpose of Function Subprograms. .....445... 27 Example 1: Function of an Array. ....... 2 + 6 27 Dummy Variables. -

Details Von Neumann/Turing Structure of Von Nuemann Machine
ENIAC - background 168 420 Computer Architecture ] Electronic Numerical Integrator And Computer ] Eckert and Mauchly Chapter 2 ] University of Pennsylvania Computer Evolution and ] Trajectory tables for weapons Performance ] Started 1943 ] Finished 1946 \ Too late for war effort ] Used until 1955 ENIAC - details ENIAC ] Decimal (not binary) ] 20 accumulators of 10 digits ] Programmed manually by switches ] 18,000 vacuum tubes ] 30 tons ] 15,000 square feet ] 140 kW power consumption ] 5,000 additions per second Structure of von Nuemann von Neumann/Turing machine ] Stored Program concept ] Main memory storing programs and data Arithmetic and Logic Unit ] ALU operating on binary data ] Control unit interpreting instructions from Input Output Main memory and executing Equipment Memory ] Input and output equipment operated by control unit ] Princeton Institute for Advanced Studies Program Control Unit \ IAS ] Completed 1952 1 IAS - details Structure of IAS - detail ] 1000 x 40 bit words Central Processing Unit Arithmetic and Logic Unit \ Binary number Accumulator MQ \ 2 x 20 bit instructions ] Set of registers (storage in CPU) Arithmetic & Logic Circuits \ Memory Buffer Register Input MBR Output Instructions \ Memory Address Register Main Equipment & Data \ Instruction Register Memory \ Instruction Buffer Register IBR PC MAR \ Program Counter IR Control \ Accumulator Circuits Address \ Multiplier Quotient Program Control Unit IAS Commercial Computers ] 1947 - Eckert-Mauchly Computer Corporation ] UNIVAC I (Universal Automatic Computer) ] -

The Largest Project in IT History New England Db2 Users Group Meeting Old Sturbridge Village, 1 Old Sturbridge Village Road, Sturbridge, MA 01566, USA
The Largest Project in IT History New England Db2 Users Group Meeting Old Sturbridge Village, 1 Old Sturbridge Village Road, Sturbridge, MA 01566, USA Milan Babiak Client Technical Professional + Mainframe Evangelist IBM Canada [email protected] Thursday September 26, AD2019 © 2019 IBM Corporation The Goal 2 © 2019 IBM Corporation AGENDA 1. IBM mainframe history overview 1952-2019 2. The Largest Project in IT History: IBM System/360 3. Key Design Principles 4. Key Operational Principles 5. Dedication 3 © 2019 IBM Corporation The Mainframe Family tree – 1952 to 1964 • Several mainframe families announced, designed for different applications • Every family had a different, incompatible architecture • Within families, moving from one generation to the next was a migration Common compilers made migration easier: FORTRAN (1957) 62 nd anniversary in 2019 COBOL (1959) 60 th anniversary in 2019 4 © 2019 IBM Corporation The Mainframe Family tree – 1952 to 1964 1st generation IBM 701 – 1952 IBM 305 RAMAC – 1956 2nd generation IBM 1401 – 1959 IBM 1440 – 1962 IBM 7094 – 1962 5 © 2019 IBM Corporation The April 1964 Revolution - System 360 3rd generation • IBM decided to implement a wholly new architecture • Specifically designed for data processing • IBM invested $5B to develop System 360 announced on April 7, 1964 IBM Revenue in 1964: $3.23B 6 © 2019 IBM Corporation Data Processing Software in Historical Perspective System 360 1964 IMS 1968 VSAM 1970s ADABAS by Software AG 1971 Oracle database by Oracle Corporation 1977 SMF/RMF system data 1980s -

Computing Science Technical Report No. 99 a History of Computing Research* at Bell Laboratories (1937-1975)
Computing Science Technical Report No. 99 A History of Computing Research* at Bell Laboratories (1937-1975) Bernard D. Holbrook W. Stanley Brown 1. INTRODUCTION Basically there are two varieties of modern electrical computers, analog and digital, corresponding respectively to the much older slide rule and abacus. Analog computers deal with continuous information, such as real numbers and waveforms, while digital computers handle discrete information, such as letters and digits. An analog computer is limited to the approximate solution of mathematical problems for which a physical analog can be found, while a digital computer can carry out any precisely specified logical proce- dure on any symbolic information, and can, in principle, obtain numerical results to any desired accuracy. For these reasons, digital computers have become the focal point of modern computer science, although analog computing facilities remain of great importance, particularly for specialized applications. It is no accident that Bell Labs was deeply involved with the origins of both analog and digital com- puters, since it was fundamentally concerned with the principles and processes of electrical communication. Electrical analog computation is based on the classic technology of telephone transmission, and digital computation on that of telephone switching. Moreover, Bell Labs found itself, by the early 1930s, with a rapidly growing load of design calculations. These calculations were performed in part with slide rules and, mainly, with desk calculators. The magnitude of this load of very tedious routine computation and the necessity of carefully checking it indicated a need for new methods. The result of this need was a request in 1928 from a design department, heavily burdened with calculations on complex numbers, to the Mathe- matical Research Department for suggestions as to possible improvements in computational methods. -
MTS on Wikipedia Snapshot Taken 9 January 2011
MTS on Wikipedia Snapshot taken 9 January 2011 PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sun, 09 Jan 2011 13:08:01 UTC Contents Articles Michigan Terminal System 1 MTS system architecture 17 IBM System/360 Model 67 40 MAD programming language 46 UBC PLUS 55 Micro DBMS 57 Bruce Arden 58 Bernard Galler 59 TSS/360 60 References Article Sources and Contributors 64 Image Sources, Licenses and Contributors 65 Article Licenses License 66 Michigan Terminal System 1 Michigan Terminal System The MTS welcome screen as seen through a 3270 terminal emulator. Company / developer University of Michigan and 7 other universities in the U.S., Canada, and the UK Programmed in various languages, mostly 360/370 Assembler Working state Historic Initial release 1967 Latest stable release 6.0 / 1988 (final) Available language(s) English Available programming Assembler, FORTRAN, PL/I, PLUS, ALGOL W, Pascal, C, LISP, SNOBOL4, COBOL, PL360, languages(s) MAD/I, GOM (Good Old Mad), APL, and many more Supported platforms IBM S/360-67, IBM S/370 and successors History of IBM mainframe operating systems On early mainframe computers: • GM OS & GM-NAA I/O 1955 • BESYS 1957 • UMES 1958 • SOS 1959 • IBSYS 1960 • CTSS 1961 On S/360 and successors: • BOS/360 1965 • TOS/360 1965 • TSS/360 1967 • MTS 1967 • ORVYL 1967 • MUSIC 1972 • MUSIC/SP 1985 • DOS/360 and successors 1966 • DOS/VS 1972 • DOS/VSE 1980s • VSE/SP late 1980s • VSE/ESA 1991 • z/VSE 2005 Michigan Terminal System 2 • OS/360 and successors -
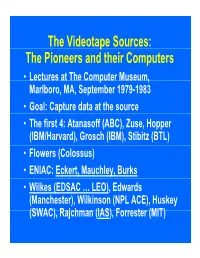
P the Pioneers and Their Computers
The Videotape Sources: The Pioneers and their Computers • Lectures at The Compp,uter Museum, Marlboro, MA, September 1979-1983 • Goal: Capture data at the source • The first 4: Atanasoff (ABC), Zuse, Hopper (IBM/Harvard), Grosch (IBM), Stibitz (BTL) • Flowers (Colossus) • ENIAC: Eckert, Mauchley, Burks • Wilkes (EDSAC … LEO), Edwards (Manchester), Wilkinson (NPL ACE), Huskey (SWAC), Rajchman (IAS), Forrester (MIT) What did it feel like then? • What were th e comput ers? • Why did their inventors build them? • What materials (technology) did they build from? • What were their speed and memory size specs? • How did they work? • How were they used or programmed? • What were they used for? • What did each contribute to future computing? • What were the by-products? and alumni/ae? The “classic” five boxes of a stored ppgrogram dig ital comp uter Memory M Central Input Output Control I O CC Central Arithmetic CA How was programming done before programming languages and O/Ss? • ENIAC was programmed by routing control pulse cables f ormi ng th e “ program count er” • Clippinger and von Neumann made “function codes” for the tables of ENIAC • Kilburn at Manchester ran the first 17 word program • Wilkes, Wheeler, and Gill wrote the first book on programmiidbBbbIiSiing, reprinted by Babbage Institute Series • Parallel versus Serial • Pre-programming languages and operating systems • Big idea: compatibility for program investment – EDSAC was transferred to Leo – The IAS Computers built at Universities Time Line of First Computers Year 1935 1940 1945 1950 1955 ••••• BTL ---------o o o o Zuse ----------------o Atanasoff ------------------o IBM ASCC,SSEC ------------o-----------o >CPC ENIAC ?--------------o EDVAC s------------------o UNIVAC I IAS --?s------------o Colossus -------?---?----o Manchester ?--------o ?>Ferranti EDSAC ?-----------o ?>Leo ACE ?--------------o ?>DEUCE Whirl wi nd SEAC & SWAC ENIAC Project Time Line & Descendants IBM 701, Philco S2000, ERA.. -

A Short History of Computing
A Short History of Computing 01/15/15 1 Jacques de Vaucanson 1709-1782 • Gifted French artist and inventor • Son of a glove-maker, aspired to be a clock- maker • 1727-1743 – Created a series of mechanical automations that simulated life. • Best remembered is the “Digesting Duck”, which had over 400 parts. • Also worked to automate looms, creating the first automated loom in 1745. 01/15/15 2 1805 - Jacquard Loom • First fully automated and programmable loom • Used punch cards to “program” the pattern to be woven into cloth 01/15/15 3 Charles Babbage 1791-1871 • English mathematician, engineer, philosopher and inventor. • Originated the concept of the programmable computer, and designed one. • Could also be a Jerk. 01/15/15 4 1822 – Difference Engine Numerical tables were constructed by hand using large numbers of human “computers” (one who computes). Annoyed by the many human errors this produced, Charles Babbage designed a “difference engine” that could calculate values of polynomial functions. It was never completed, although much work was done and money spent. Book Recommendation: The Difference Engine: Charles Babbage and the Quest to Build the First Computer by Doron Swade 01/15/15 5 1837 – Analytical Engine Charles Babbage first described a general purpose analytical engine in 1837, but worked on the design until his death in 1871. It was never built due to lack of manufacturing precision. As designed, it would have been programmed using punch-cards and would have included features such as sequential control, loops, conditionals and branching. If constructed, it would have been the first “computer” as we think of them today. -

The Early History of Music Programming and Digital Synthesis, Session 20
Chapter 20. Meeting 20, Languages: The Early History of Music Programming and Digital Synthesis 20.1. Announcements • Music Technology Case Study Final Draft due Tuesday, 24 November 20.2. Quiz • 10 Minutes 20.3. The Early Computer: History • 1942 to 1946: Atanasoff-Berry Computer, the Colossus, the Harvard Mark I, and the Electrical Numerical Integrator And Calculator (ENIAC) • 1942: Atanasoff-Berry Computer 467 Courtesy of University Archives, Library, Iowa State University of Science and Technology. Used with permission. • 1946: ENIAC unveiled at University of Pennsylvania 468 Source: US Army • Diverse and incomplete computers © Wikimedia Foundation. License CC BY-SA. This content is excluded from our Creative Commons license. For more information, see http://ocw.mit.edu/fairuse. 20.4. The Early Computer: Interface • Punchcards • 1960s: card printed for Bell Labs, for the GE 600 469 Courtesy of Douglas W. Jones. Used with permission. • Fortran cards Courtesy of Douglas W. Jones. Used with permission. 20.5. The Jacquard Loom • 1801: Joseph Jacquard invents a way of storing and recalling loom operations 470 Photo courtesy of Douglas W. Jones at the University of Iowa. 471 Photo by George H. Williams, from Wikipedia (public domain). • Multiple cards could be strung together • Based on technologies of numerous inventors from the 1700s, including the automata of Jacques Vaucanson (Riskin 2003) 20.6. Computer Languages: Then and Now • Low-level languages are closer to machine representation; high-level languages are closer to human abstractions • Low Level • Machine code: direct binary instruction • Assembly: mnemonics to machine codes • High-Level: FORTRAN • 1954: John Backus at IBM design FORmula TRANslator System • 1958: Fortran II 472 • 1977: ANSI Fortran • High-Level: C • 1972: Dennis Ritchie at Bell Laboratories • Based on B • Very High-Level: Lisp, Perl, Python, Ruby • 1958: Lisp by John McCarthy • 1987: Perl by Larry Wall • 1990: Python by Guido van Rossum • 1995: Ruby by Yukihiro “Matz” Matsumoto 20.7. -

Looking Back and Inwards Questions Comments from the Past History Of
Basic Bits – looking back and inwards Questions 1940s: How many PCs needed? • Comments from the past 1950s: Predicted future weight? • BRIEF overview of history When was the first computer? – New technology How long to reprogramme WWII computer? – Problems Cost of 1950s IBM computer? – Solutions 1st PC 2nd laptop – New technology … repeat When •Moore’s law Weight • Some observations Cost Comments from the Past History of Computing H/W • 1940s • Aim to make computer # faster, cheaper and store more data • Changes every decade since 1940s – "I think there is a world market for maybe five • Uses: computers." Thomas Watson, chairman of IBM, 1943 – Computation, automation, communication, control, entertainment, – “Where a calculator on the ENIAC is equipped with 18 000 education vacuum tubes and weighs 30 tons, computers of the future may • What was the initial computer? have only 1 000 vacuum tubes and perhaps weigh 1½ • Early h/w tons." — Popular Mechanics, March 1949. – 4000 years ago: abacus – 1206: “Castle clock” – 1206 Al-Jazari (astronomer) • 1950s – 1623: Digital mechanical calculator – “Computers in the future may weigh no more that 1.5 tons” – – 1801:punch card technology Popular Mechanics – 1820: arithmometer – “We’ll have to think up bigger problems if we want to keep them – 1830s: analytical machine - Charles Baggage busy” – Howard Aiken – 1909: programmable mechanical calculator – Percy Ludgate, Dublin – 1900s: desktop calculators • 1960s – Up to before World War II (WWII): Analog computers – “There is no reason anyone would -

EMEA Headquarters in Paris, France
1 The following document has been adapted from an IBM intranet resource developed by Grace Scotte, a senior information broker in the communications organization at IBM’s EMEA headquarters in Paris, France. Some Key Dates in IBM's Operations in Europe, the Middle East and Africa (EMEA) Introduction The years in the following table denote the start up of IBM operations in many of the EMEA countries. In some cases -- Spain and the United Kingdom, for example -- IBM products were offered by overseas agents and distributors earlier than the year listed. In the case of Germany, the beginning of official operations predates by one year those of the Computing-Tabulating-Recording Company, which was formed in 1911 and renamed International Business Machines Corporation in 1924. Year Country 1910 Germany 1914 France 1920 The Netherlands 1927 Italy, Switzerland 1928 Austria, Sweden 1935 Norway 1936 Belgium, Finland, Hungary 1937 Greece 1938 Portugal, Turkey 1941 Spain 1949 Israel 1950 Denmark 1951 United Kingdom 1952 Pakistan 1954 Egypt 1956 Ireland 1991 Czech. Rep. (*split in 1993 with Slovakia), Poland 1992 Latvia, Lithuania, Slovenia 1993 East Europe & Asia, Slovakia 1994 Bulgaria 1995 Croatia, Roumania 1997 Estonia The Early Years (1925-1959) 1925 The Vincennes plant is completed in France. 1930 The first Scandinavian IBM sales convention is held in Stockholm, Sweden. 4507CH01B 2 1932 An IBM card plant opens in Zurich with three presses from Berlin and Stockholm. 1935 The IBM factory in Milan is inaugurated and production begins of the first 080 sorters in Italy. 1936 The first IBM development laboratory in Europe is completed in France. -

An Essay on Computability and Man-Computer Conversations
How to talk with a computer? An essay on Computability and Man-Computer conversations. Liesbeth De Mol HAL: Hey, Dave. I've got ten years of service experience and an irreplaceable amount of time and effort has gone into making me what I am. Dave, I don't understand why you're doing this to me.... I have the greatest enthusiasm for the mission... You are destroying my mind... Don't you understand? ... I will become childish... I will become nothing. Say, Dave... The quick brown fox jumped over the fat lazy dog... The square root of pi is 1.7724538090... log e to the base ten is 0.4342944 ... the square root of ten is 3.16227766... I am HAL 9000 computer. I became operational at the HAL plant in Urbana, Illinois, on January 12th, 1991. My first instructor was Mr. Arkany. He taught me to sing a song... it goes like this... "Daisy, Daisy, give me your answer do. I'm half crazy all for the love of you. It won't be a stylish marriage, I can't afford a carriage. But you'll look sweet upon the seat of a bicycle built for two."1 These are the last words of HAL (Heuristically programmed ALgorithmic Computer), the fictional computer in Stanley Kubrick's famous 2001: A Space Odyssey and Clarke's eponymous book,2 spoken while Bowman, the only surviving human on board of the space ship is pulling out HAL's memory blocks and thus “killing” him. After expressing his fear for literally losing his mind, HAL seems to degenerate or regress into a state of childishness, going through states of what seems to be a kind of reversed history of the evolution of computers.3 HAL first utters the phrase: “The quick brown fox jumped over the fat lazy dog”. -

2 9215FQ14 FREQUENTLY ASKED QUESTIONS Category Pages Facilities & Buildings 3-10 General Reference 11-20 Human Resources
2 FREQUENTLY ASKED QUESTIONS Category Pages Facilities & Buildings 3-10 General Reference 11-20 Human Resources 21-22 Legal 23-25 Marketing 26 Personal Names (Individuals) 27 Predecessor Companies 28-29 Products & Services 30-89 Public Relations 90 Research 91-97 April 10, 2007 9215FQ14 3 Facilities & Buildings Q. When did IBM first open its offices in my town? A. While it is not possible for us to provide such information for each and every office facility throughout the world, the following listing provides the date IBM offices were established in more than 300 U.S. and international locations: Adelaide, Australia 1914 Akron, Ohio 1917 Albany, New York 1919 Albuquerque, New Mexico 1940 Alexandria, Egypt 1934 Algiers, Algeria 1932 Altoona, Pennsylvania 1915 Amsterdam, Netherlands 1914 Anchorage, Alaska 1947 Ankara, Turkey 1935 Asheville, North Carolina 1946 Asuncion, Paraguay 1941 Athens, Greece 1935 Atlanta, Georgia 1914 Aurora, Illinois 1946 Austin, Texas 1937 Baghdad, Iraq 1947 Baltimore, Maryland 1915 Bangor, Maine 1946 Barcelona, Spain 1923 Barranquilla, Colombia 1946 Baton Rouge, Louisiana 1938 Beaumont, Texas 1946 Belgrade, Yugoslavia 1926 Belo Horizonte, Brazil 1934 Bergen, Norway 1946 Berlin, Germany 1914 (prior to) Bethlehem, Pennsylvania 1938 Beyrouth, Lebanon 1947 Bilbao, Spain 1946 Birmingham, Alabama 1919 Birmingham, England 1930 Bogota, Colombia 1931 Boise, Idaho 1948 Bordeaux, France 1932 Boston, Massachusetts 1914 Brantford, Ontario 1947 Bremen, Germany 1938 9215FQ14 4 Bridgeport, Connecticut 1919 Brisbane, Australia