Creating Dictionary Attack Software Using a Powerful Server and Javafx
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Truecrack Bruteforcing Per Volumi Truecrypt
Luca Vaccaro http://code.google.com/p/truecrack/ [email protected] User development guide. TrueCrypt © . software application used for on-the-fly encryption (OTFE). TrueCrack . bruteforce password cracker for TrueCrypt © (Copyrigth) volume files, optimazed with Nvidia Cuda technology. This software is Based on TrueCrypt, freely available athttp://www.truecrypt.org/ Master key . Crypt the volume of data. Generated one time in the volume creation phase from random value. Write inside the header section of the volume file. Header key . Crypt the header section of the volume file. Generated from a user password and a random salt (64 bytes). The salt is write in plain text in the first 64 bytes of volume file. Hard disk encryption: . Standard block cipher: XTS . Hash availables: AES, Serpent, Twofish . Default: AES Key derivation function: . Standard algorithm: PBKDF2 . Hash availables: RIPEMD160, SHA-512, Whirpool . Default: RIPEMD160 Master Header Key Key Plain Cipher Volume data data + file header Opening a TrueCrypt volume means to retrieve the Master Key from the Header section In the Header there are some fields (true, crc32) for checking the success of the decipher operation . If the password is right or wrong Header key User password salt Volume Master file key CUDA or Compute Unified Device Architecture is a parallel computing architecture developed by Nvidia. CUDA gives developers access to the virtual instruction set and memory of the parallel computational elements in CUDA GPUs. Each GPU is a collection of multicores. Each core can run mmore cuda «block», and each block can run a numbers of parallel «thread» 1. Level of parallilism : block 2. -

Analysis of Password Cracking Methods & Applications
The University of Akron IdeaExchange@UAkron The Dr. Gary B. and Pamela S. Williams Honors Honors Research Projects College Spring 2015 Analysis of Password Cracking Methods & Applications John A. Chester The University Of Akron, [email protected] Please take a moment to share how this work helps you through this survey. Your feedback will be important as we plan further development of our repository. Follow this and additional works at: http://ideaexchange.uakron.edu/honors_research_projects Part of the Information Security Commons Recommended Citation Chester, John A., "Analysis of Password Cracking Methods & Applications" (2015). Honors Research Projects. 7. http://ideaexchange.uakron.edu/honors_research_projects/7 This Honors Research Project is brought to you for free and open access by The Dr. Gary B. and Pamela S. Williams Honors College at IdeaExchange@UAkron, the institutional repository of The nivU ersity of Akron in Akron, Ohio, USA. It has been accepted for inclusion in Honors Research Projects by an authorized administrator of IdeaExchange@UAkron. For more information, please contact [email protected], [email protected]. Analysis of Password Cracking Methods & Applications John A. Chester The University of Akron Abstract -- This project examines the nature of password cracking and modern applications. Several applications for different platforms are studied. Different methods of cracking are explained, including dictionary attack, brute force, and rainbow tables. Password cracking across different mediums is examined. Hashing and how it affects password cracking is discussed. An implementation of two hash-based password cracking algorithms is developed, along with experimental results of their efficiency. I. Introduction Password cracking is the process of either guessing or recovering a password from stored locations or from a data transmission system [1]. -
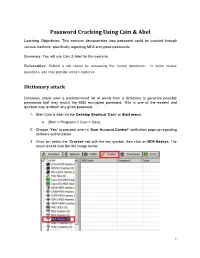
Password Cracking Using Cain & Abel
Password Cracking Using Cain & Abel Learning Objectives: This exercise demonstrates how password could be cracked through various methods, specifically regarding MD5 encrypted passwords. Summary: You will use Cain & Abel for this exercise. Deliverables: Submit a lab report by answering the review questions. In some review questions, you may provide screen captures. Dictionary attack Dictionary attack uses a predetermined list of words from a dictionary to generate possible passwords that may match the MD5 encrypted password. This is one of the easiest and quickest way to obtain any given password. 1. Start Cain & Abel via the Desktop Shortcut ‘Cain’ or Start menu. a. (Start > Programs > Cain > Cain). 2. Choose ‘Yes’ to proceed when a ‘User Account Control’ notification pops up regarding software authorization. 3. Once on, select the ‘Cracker’ tab with the key symbol, then click on MD5 Hashes. The result should look like the image below. 1 Collaborative Virtual Computer Lab (CVCLAB) Penn State Berks 4. As you might have noticed we don’t have any passwords to crack, thus for the next few steps we will create our own MD5 encrypted passwords. First, locate the Hash Calculator among a row of icons near the top. Open it. 5. Next, type into ‘Text to Hash’ the word password. It will generate a list of hashes pertaining to different types of hash algorithms. We will be focusing on MD5 hash so copy it. Then exit calculator by clicking ‘Cancel’ (Fun Fact: Hashes are case sensitive so any slight changes to the text will change the hashes generated, try changing a letter or two and you will see. -
User Authentication and Cryptographic Primitives
User Authentication and Cryptographic Primitives Brad Karp UCL Computer Science CS GZ03 / M030 16th November 2016 Outline • Authenticating users – Local users: hashed passwords – Remote users: s/key – Unexpected covert channel: the Tenex password- guessing attack • Symmetric-key-cryptography • Public-key cryptography usage model • RSA algorithm for public-key cryptography – Number theory background – Algorithm definition 2 Dictionary Attack on Hashed Password Databases • Suppose hacker obtains copy of password file (until recently, world-readable on UNIX) • Compute H(x) for 50K common words • String compare resulting hashed words against passwords in file • Learn all users’ passwords that are common English words after only 50K computations of H(x)! • Same hashed dictionary works on all password files in world! 3 Salted Password Hashes • Generate a random string of bytes, r • For user password x, store [H(r,x), r] in password file • Result: same password produces different result on every machine – So must see password file before can hash dictionary – …and single hashed dictionary won’t work for multiple hosts • Modern UNIX: password hashes salted; hashed password database readable only by root 4 Salted Password Hashes • Generate a random string of bytes, r Dictionary• For user password attack still x, store possible [H(r,x after), r] in attacker seespassword password file file! Users• Result: should same pick password passwords produces that different aren’t result close to ondictionary every machine words. – So must see password file -
Passwords CS 166: Information Security Authentication: Passwords
Passwords CS 166: Information Security Authentication: Passwords Prof. Tom Austin San José State University Access Control • Authentication: Are you who you say you are? – Determine whether access is allowed – human to machine, or machine to machine • Authorization: Are you allowed to do that? – Once you have access, what can you do? – Enforces limits on actions Chapter 7: Authentication Guard: Halt! Who goes there? Arthur: It is I, Arthur, son of Uther Pendragon, from the castle of Camelot. King of the Britons, defeater of the Saxons, sovereign of all England! ¾ Monty Python and the Holy Grail Then said they unto him, Say now Shibboleth: and he said Sibboleth: for he could not frame to pronounce it right. Then they took him, and slew him at the passages of Jordan: and there fell at that time of the Ephraimites forty and two thousand. ¾ Judges 12:6 Authentication: Are You Who You Say You Are? • How to authenticate human a machine? • Can be based on… –Something you know • e.g. password –Something you have • e.g. smartcard –Something you are • e.g. fingerprint Something You Know • Passwords • Lots of things act as passwords! –PIN –Social security number –Mother’s maiden name –Date of birth –Name of your pet, etc. Why Passwords? • Why is “something you know” more popular than “something you have” and “something you are”? • Cost: passwords are free • Convenience: easier for admin to reset pwd than to issue a new thumb Authenticating with Passwords I am Thor Prove it My password is Mjölnir Authenticating with Passwords I am Thor Prove it My -
UGRD 2015 Spring Bugg Chris.Pdf (464.4Kb)
We could consider using the Mighty Cracker Logo located in the Network Folder MIGHTY CRACKER Chris Bugg Chris Hamm Jon Wright Nick Baum Password Security • Password security is important. • Users • Weak and/or reused passwords • Developers and Admins • Choose insecure storage algorithms. • Mighty Cracker • Show real world impact of poor password security. OVERVIEW • We made a hash cracker. • Passwords are stored as hashes to protect them from intruders. • Our program uses several methods to ‘crack’ those hashes. • Networking • Spread work to multiple machines. • Cross Platform OTHER HASH CRACKING PRODUCTS • Hashcat • Cain and Abel • John the Ripper • THC-Hydra • Ophcrack • Network support is rare. WHAT IS HASHING • A way to encode a password to help protect it. • A mathematical one-way function. • MD5 hash • cf4ff726403b8a992fd43e09dd7b5717 • SHA-256 hash • 951e689364c979cc3aa17e6b0022ce6e4d0e3200d1c22dd68492c172241e0623 SUPPORTED HASHING ALGORITHMS • Current Algorithms • MD5 • SHA-1 • SHA-224 • SHA-256 • SHA-384 • SHA-512 WAYS TO CRACK • Cracking Modes • Single User • Network Mode • Methods of Cracking: • Brute Force • Dictionary • Rainbow Table • GUI or Console BRUTE FORCE • Systematically checking all possible keys until the correct one is found. • Worst case this would transverse the entire search space. • Slowest but will always find the solution if given enough time. DICTIONARY ATTACK • List of common passwords from leaks/hacks. • Many people choose common passwords • Written works of Shakespeare ~66,000 words • Oxford English Dictionary ~290,000 words • Small dictionary = 900,000 words • Medium dictionary = 14 million words • Large dictionary = 1.2 billion words RAINBOW TABLE • Can’t store all possible hash/key combinations. • 16 character key = 10^40th combinations • 10^50th atoms on earth • Rainbow tables • Reduced storage. -

Hao Xu; Title: Improving Rainbow Table Cracking Accuracy; Mentor(S): Xianping Wang, CITG
Student(s): Hao Xu; Title: Improving Rainbow Table Cracking Accuracy; Mentor(s): Xianping Wang, CITG. Abstract: Password cracking is the process of recovering plaintext passwords from data that has been stored in or transmitted by computing systems in cryptanalysis, computer security and digital forensics. There are many situations that require password cracking: helping users recover forgotten passwords, gaining unauthorized access to systems, checking password strength, etc. The most popular and applicable password cracking method is brute-force attack with various improvements such as dictionary attack, rainbow table attack. Usually they are accelerated with GPU, FPGA and ASIC. As passwords are usually stored in their hash codes instead of plaintext. to accelerate the password cracking process, caching the output of cryptographic hash codes of passwords, named as rainbow table, are used widely today. However, rainbow tables are usually created from exhaustive password dictionaries, in which many unusual combinations of letters, symbols and digits are contained, which decreased cracking efficiency and accuracy The efficiency and accuracy of rainbow table cracking can be improved from many aspects such as password patterns, computing engines, etc. In this research, we will employ many openly available leaked passwords, to find their distribution by maximum likelihood estimation, design a password generator based on the found distribution, generate rainbow tables on the passwords generated by the designed password generator. The accuracy of our rainbow table cracker will be compared with several popular password crackers --- John the Ripper password cracker, Cain and Abel, Hashcat , and Ophcrack " . -

A Survey of Password Attacks and Safe Hashing Algorithms
International Research Journal of Engineering and Technology (IRJET) e-ISSN: 2395-0056 Volume: 04 Issue: 12 | Dec-2017 www.irjet.net p-ISSN: 2395-0072 A Survey of Password Attacks and Safe Hashing Algorithms Tejaswini Bhorkar Student, Dept. of Computer Science and Engineering, RGCER, Nagpur, Maharashtra, India ---------------------------------------------------------------------***--------------------------------------------------------------------- Abstract - To authenticate users, most web services use pair of message that would generate the same hash as that of the username and password. When a user wish to login to a web first message. Thus, the hash function should be resistant to application of the service, he/she sends their user name and second-pre-image. password to the web server, which checks if the given username already exist in the database and that the password is identical to 1.2 Hashing Algorithms the password set by that user. This last step of verifying the password of the user can be performed in different ways. The user Different hash algorithms are used in order to generate hash password may be directly stored in the database or the hash value values. Some commonly used hash functions include the of the password may be stored. This survey will include the study following: of password hashing. It will also include the need of password hashing, algorithms used for password hashing along with the attacks possible on the same. • MD5 • SHA-1 Key Words: Password, Hashing, Algorithms, bcrypt, scrypt, • SHA-2 attacks, SHA-1 • SHA-3 1.INTRODUCTION MD5: Web servers store the username and password of its users to authenticate its users. If the web servers store the passwords of This algorithm takes data of arbitrary length and produces its users directly in the database, then in such case, password message digest of 128 bits (i.e. -

Lab 3: MD5 and Rainbow Tables
Lab 3: MD5 and Rainbow Tables 50.020 Security Hand-out: February 9 Hand-in: February 16, 9pm 1 Objective • Hash password using MD5 • Crack MD5 hashes using brute-force and rainbow tables • Strengthen MD5 hash using salt and crack again the salted hashes • Compete in the hash breaking competition 2 Hashing password using MD5 • To warm up, compute a couple of MD5 hashes of strings of your choice – Observe the length of the output, and whether it depends on length of input • To generate the MD5 hash using the shell, try echo -n "foobar" | md5sum to compute hash of foobar • To generate the MD5 hash using python, use import hashlib module and its hexdigest() function. 3 Brute-Force and dictionary attack • For this exercise, use the fifteen hash values from the hash5.txt • Create a md5fun.py Python 3 script to find the corresponding input to create the challenge hash values • You need only to consider passwords with 5 lowercase and or numeric characters. Compute the hash values for each possible combination. To help reduce the search space we provide a dictionary with newline separated common words in words5.txt. Notice a resulting hash may be generated by a permutation of any word in the list, e.g. hello -> lhelo • Both hash5.txt and words5.txt elements are newline separated • Take note of the computation time of your algorithm to reverse all fifteen hashes. Consider the timeit python module: https://docs.python.org/3.6/library/timeit.html 1 4 Creating Rainbow Tables • Install the program rainbrowcrack-1.6.1-linux64.zip (http://project-rainbowcrack.com/rainbowcrack-1.6.1-linux64.zip). -

CIS 4360 Introduction to Computer Security
CIS 4360 Introduction to Computer Security Home Assignment 9, Fall 2010 – with answers Due: Thu 12:30pm, 23/11/2010 This assignment concerns Key Establishment and Authentication. Examples taken from: Dieter Gollmann, Computer Security, 2nd Edition, John Wiley. 1. In the HTTP basic authentication protocol, analyze the security gains (if any) when the client sends a hash of the password instead of a base64 encoding of the password. Answer. No real gain. The attacker just intercepts the hash of the password and provides the hash later to imper- sonate the user. The protocol has to use some kind of nonce to avoid such replay attacks. N.B. In contrast, with the Digest Access Authentication the Server sends a nonce, which the client must include in the hash: request−digest = h(h(username||realm||password)||nonce||h(method||digest−uri)), and even though h(username||realm||password), h(method||digest−uri) are the same, the value of nonce (which the Server picks) changes. However this scheme can be broken with a dictionary attack. The dictionary will give the attacker a value for h(username||realm||password)||nonce||h(method||digest−uri), and if the attacker replaces the value of nonce, the hash of the new string is likely to have the correct value. 2. Justify that the AKEP2 protocol provides (a) mutual entity authentication and (b) implicit key authenti- cation. Answer. (a) Mutual entity authentication. A gets a reply hK (B, A, nA, nB) to its challenge nA that can only come from B (assuming the long term key K is not compromised). -

Authenticating People
© Jones & Bartlett Learning,© Jones LLC & Bartlett Learning LLC, an Ascend Learning© Jones Company. & NOT Bartlett FOR SALE Learning, OR DISTRIBUTION. LLC NOT FOR SALE OR DISTRIBUTION NOT FOR SALE OR DISTRIBUTION © Jones & Bartlett Learning, LLC © Jones & Bartlett Learning, LLC © Digital_Art/ShutterstockNOT FOR SALE OR DISTRIBUTION NOT FOR SALE OR DISTRIBUTION CHAPTER 6 © Jones & Bartlett Learning, LLC © Jones & Bartlett Learning, LLC NOT FORAuthenticating SALE OR DISTRIBUTION PeopleNOT FOR SALE OR DISTRIBUTION © Jones & Bartlett Learning, LLC © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION NOT FOR SALE OR DISTRIBUTION ▸ About This Chapter In this chapter, we look at techniques to accurately associate individuals with user identities inside a computer. The discussion will focus on passwords with an intro- duction to© other Jones methods. & Bartlett The chapter Learning, examines the LLC following topics: © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION NOT FOR SALE OR DISTRIBUTION ■ The three authentication factors: what you know, you have, and you are ■ Passwords, password bias, and search space calculations ■ Cryptographic building blocks: random choice, one-way hash ■ Authentication devices: personal tokens and biometrics ■ © Jones &Basic Bartlett issues in Learning, authentication LLC policy © Jones & Bartlett Learning, LLC NOT FOR SALE OR DISTRIBUTION NOT FOR SALE OR DISTRIBUTION ▸ 6.1 Unlocking a Door We use padlocks, deadbolts, and safes to protect unattended things. We arrange it so that only authorized users may open these locks. We either restrict copies of © Jones & Bartlett keysLearning, to the trusted LLC people, or we share lock combinations© Jones with& Bartlett only those Learning, trusted LLC NOT FOR SALE ORfew. DISTRIBUTION NOT FOR SALE OR DISTRIBUTION Bob shares his computer with his employees and with those of Alice’s Arts. -

Rainbow Tables & Rainbowcrack Introduction
Learn Security Online, Inc. © https://www.learnsecurityonline.com/ Rainbow Tables & RainbowCrack Introduction Rainbow tables reduce the difficulty in brute force cracking a single password by creating a large pre-generated data set of hashes from nearly every possible password. Rainbow Tables and RainbowCrack come from the work and subsequent paper by Philippe Oechslin.1 The method, known as the Faster Time-Memory Trade-Off Technique, is based on research by Martin Hellman & Ronald Rivest done in the early 1980’s on the performance trade-offs between processing time and the memory needed for cryptanalysis. In his paper published in 2003, Oechslin refined the techniques and showed that the attack could reduce the time to attack 99.9%of Microsoft's LAN Manager passwords (alpha characters only) to 13.6 seconds from 101 seconds. Further algorithm refinements also reduced the number of false positives produced by the system. The main benefit of Rainbow Tables is that while the actual creation of the rainbow tables takes much more time than cracking a single hash, after they are generated you can use the tables over and over again. Additionally, once you have generated the Rainbow Tables, RainbowCrack is faster than brute force attacks and needs less memory than full dictionary attacks. Rainbow Tables are popular with a particularly weak password algorithm known as Microsoft LM hash. LM stands for LAN Manager, this password algorithm was used in earlier days of Windows and still lives on only for compatibility reasons. By default Windows XP or even Windows Server 2003 keeps the LM hash of your passwords in addition to a more secure hash (NTLM or NTLMv2).