Analysis of Password Cracking Methods & Applications
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

GPU-Based Password Cracking on the Security of Password Hashing Schemes Regarding Advances in Graphics Processing Units
Radboud University Nijmegen Faculty of Science Kerckhoffs Institute Master of Science Thesis GPU-based Password Cracking On the Security of Password Hashing Schemes regarding Advances in Graphics Processing Units by Martijn Sprengers [email protected] Supervisors: Dr. L. Batina (Radboud University Nijmegen) Ir. S. Hegt (KPMG IT Advisory) Ir. P. Ceelen (KPMG IT Advisory) Thesis number: 646 Final Version Abstract Since users rely on passwords to authenticate themselves to computer systems, ad- versaries attempt to recover those passwords. To prevent such a recovery, various password hashing schemes can be used to store passwords securely. However, recent advances in the graphics processing unit (GPU) hardware challenge the way we have to look at secure password storage. GPU's have proven to be suitable for crypto- graphic operations and provide a significant speedup in performance compared to traditional central processing units (CPU's). This research focuses on the security requirements and properties of prevalent pass- word hashing schemes. Moreover, we present a proof of concept that launches an exhaustive search attack on the MD5-crypt password hashing scheme using modern GPU's. We show that it is possible to achieve a performance of 880 000 hashes per second, using different optimization techniques. Therefore our implementation, executed on a typical GPU, is more than 30 times faster than equally priced CPU hardware. With this performance increase, `complex' passwords with a length of 8 characters are now becoming feasible to crack. In addition, we show that between 50% and 80% of the passwords in a leaked database could be recovered within 2 months of computation time on one Nvidia GeForce 295 GTX. -
NSA Vs. Encryption Article Written by Datto Developer Dan Fuhry First Appeared on Mspmentor.Com in November 2013
SuccessArticle: EncryptionStory NSA vs. Encryption Article written by Datto developer Dan Fuhry first appeared on MSPmentor.com in November 2013. If you’ve been watching the news lately, there is no doubt you have heard about the National Security Agency’s (NSA) surveillance scandal. “We will stand in our firm Recent months have seen a revelation of programs commitment to protect you and that capture domestic and international traffic indiscriminately. Encrypted data gets saved for a your customers.” certain number of years, in case they ever decide to decrypt it. If this alarms you, that’s good. You should be alarmed. I was too, on a very personal level, and have actively been working on changing some long-established habits in order to protect the information that is private and personal to me. For MSPs not in the United States you should be even more alarmed. It’s not even your own government that has the encrypted data, and since you don’t have constitutional protection in the U.S., there is nothing legally standing in the NSA’s way to prevent them from using their dark magical cryptographic powers to obtain your confidential business or personal data. This is a frightening proposition indeed, which is why I want to talk about the position Datto has taken regarding the recent revelations. Before we go any further, allow me to briefly describe my role here. I’m a developer with Datto, and I designed the encryption feature for Datto SIRIS. I picked the ciphers, hash algorithm parameters, and random number generator algorithm, had them peer-reviewed, and then wrote the code. -

Truecrack Bruteforcing Per Volumi Truecrypt
Luca Vaccaro http://code.google.com/p/truecrack/ [email protected] User development guide. TrueCrypt © . software application used for on-the-fly encryption (OTFE). TrueCrack . bruteforce password cracker for TrueCrypt © (Copyrigth) volume files, optimazed with Nvidia Cuda technology. This software is Based on TrueCrypt, freely available athttp://www.truecrypt.org/ Master key . Crypt the volume of data. Generated one time in the volume creation phase from random value. Write inside the header section of the volume file. Header key . Crypt the header section of the volume file. Generated from a user password and a random salt (64 bytes). The salt is write in plain text in the first 64 bytes of volume file. Hard disk encryption: . Standard block cipher: XTS . Hash availables: AES, Serpent, Twofish . Default: AES Key derivation function: . Standard algorithm: PBKDF2 . Hash availables: RIPEMD160, SHA-512, Whirpool . Default: RIPEMD160 Master Header Key Key Plain Cipher Volume data data + file header Opening a TrueCrypt volume means to retrieve the Master Key from the Header section In the Header there are some fields (true, crc32) for checking the success of the decipher operation . If the password is right or wrong Header key User password salt Volume Master file key CUDA or Compute Unified Device Architecture is a parallel computing architecture developed by Nvidia. CUDA gives developers access to the virtual instruction set and memory of the parallel computational elements in CUDA GPUs. Each GPU is a collection of multicores. Each core can run mmore cuda «block», and each block can run a numbers of parallel «thread» 1. Level of parallilism : block 2. -

Study on Massive-Scale Slow-Hash Recovery Using Unified
S S symmetry Article Study on Massive-Scale Slow-Hash Recovery Using Unified Probabilistic Context-Free Grammar and Symmetrical Collaborative Prioritization with Parallel Machines Tianjun Wu 1,*,†, Yuexiang Yang 1,†, Chi Wang 2,† and Rui Wang 2,† 1 College of Computer, National University of Defense Technology, Changsha 410073, China; [email protected] 2 VeriClouds Co., Seattle, WA 98105, USA; [email protected] (C.W.); [email protected] (R.W.) * Correspondence: [email protected]; Tel.: +86-13-54-864-2846 † The authors contribute equally to this work and are co-first authors. Received: 23 February 2019; Accepted: 26 March 2019; Published: 1 April 2019 Abstract: Slow-hash algorithms are proposed to defend against traditional offline password recovery by making the hash function very slow to compute. In this paper, we study the problem of slow-hash recovery on a large scale. We attack the problem by proposing a novel concurrent model that guesses the target password hash by leveraging known passwords from a largest-ever password corpus. Previously proposed password-reused learning models are specifically designed for targeted online guessing for a single hash and thus cannot be efficiently parallelized for massive-scale offline recovery, which is demanded by modern hash-cracking tasks. In particular, because the size of a probabilistic context-free grammar (PCFG for short) model is non-trivial and keeping track of the next most probable password to guess across all global accounts is difficult, we choose clever data structures and only expand transformations as needed to make the attack computationally tractable. Our adoption of max-min heap, which globally ranks weak accounts for both expanding and guessing according to unified PCFGs and allows for concurrent global ranking, significantly increases the hashes can be recovered within limited time. -
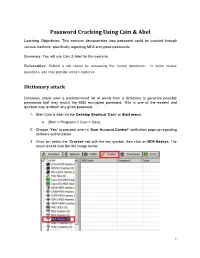
Password Cracking Using Cain & Abel
Password Cracking Using Cain & Abel Learning Objectives: This exercise demonstrates how password could be cracked through various methods, specifically regarding MD5 encrypted passwords. Summary: You will use Cain & Abel for this exercise. Deliverables: Submit a lab report by answering the review questions. In some review questions, you may provide screen captures. Dictionary attack Dictionary attack uses a predetermined list of words from a dictionary to generate possible passwords that may match the MD5 encrypted password. This is one of the easiest and quickest way to obtain any given password. 1. Start Cain & Abel via the Desktop Shortcut ‘Cain’ or Start menu. a. (Start > Programs > Cain > Cain). 2. Choose ‘Yes’ to proceed when a ‘User Account Control’ notification pops up regarding software authorization. 3. Once on, select the ‘Cracker’ tab with the key symbol, then click on MD5 Hashes. The result should look like the image below. 1 Collaborative Virtual Computer Lab (CVCLAB) Penn State Berks 4. As you might have noticed we don’t have any passwords to crack, thus for the next few steps we will create our own MD5 encrypted passwords. First, locate the Hash Calculator among a row of icons near the top. Open it. 5. Next, type into ‘Text to Hash’ the word password. It will generate a list of hashes pertaining to different types of hash algorithms. We will be focusing on MD5 hash so copy it. Then exit calculator by clicking ‘Cancel’ (Fun Fact: Hashes are case sensitive so any slight changes to the text will change the hashes generated, try changing a letter or two and you will see. -
User Authentication and Cryptographic Primitives
User Authentication and Cryptographic Primitives Brad Karp UCL Computer Science CS GZ03 / M030 16th November 2016 Outline • Authenticating users – Local users: hashed passwords – Remote users: s/key – Unexpected covert channel: the Tenex password- guessing attack • Symmetric-key-cryptography • Public-key cryptography usage model • RSA algorithm for public-key cryptography – Number theory background – Algorithm definition 2 Dictionary Attack on Hashed Password Databases • Suppose hacker obtains copy of password file (until recently, world-readable on UNIX) • Compute H(x) for 50K common words • String compare resulting hashed words against passwords in file • Learn all users’ passwords that are common English words after only 50K computations of H(x)! • Same hashed dictionary works on all password files in world! 3 Salted Password Hashes • Generate a random string of bytes, r • For user password x, store [H(r,x), r] in password file • Result: same password produces different result on every machine – So must see password file before can hash dictionary – …and single hashed dictionary won’t work for multiple hosts • Modern UNIX: password hashes salted; hashed password database readable only by root 4 Salted Password Hashes • Generate a random string of bytes, r Dictionary• For user password attack still x, store possible [H(r,x after), r] in attacker seespassword password file file! Users• Result: should same pick password passwords produces that different aren’t result close to ondictionary every machine words. – So must see password file -
Cryptanalytic Tools
Cryptanalytic Tools Authors: Prof. Dr.-Ing. Tim Güneysu Dipl. Ing. Alexander Wild B. Sc. Tobias Schneider Ruhr-Universität Bochum Module Cryptanalytic Tools Chapter 3: Introduction to Cryptanalysis Chapter 4: Computational Complexity and Parallelism Chapter 5: Secret Parameters and Keys Chapter 6: Tools for Symmetric Cryptanalysis Chapter 7: Tools for Asymmetric Cryptanalysis Authors: Prof. Dr.-Ing. Tim Güneysu Dipl. Ing. Alexander Wild B. Sc. Tobias Schneider 1. edition Ruhr-Universität Bochum © 2015 Ruhr-Universität Bochum Universitätsstraße 150 44801 Bochum 1. edition (31. March 2015) Das Werk einschließlich seiner Teile ist urheberrechtlich geschützt. Jede Ver- wendung außerhalb der engen Grenzen des Urheberrechtsgesetzes ist ohne Zustimmung der Verfasser unzulässig und strafbar. Das gilt insbesondere für Vervielfältigungen, Übersetzungen, Mikroverfilmungen und die Einspe- icherung und Verarbeitung in elektronischen Systemen. Um die Lesbarkeit zu vereinfachen, wird auf die zusätzliche Formulierung der weiblichen Form bei Personenbezeichnungen verzichtet. Wir weisen deshalb darauf hin, dass die Verwendung der männlichen Form explizit als geschlechtsunabhängig verstanden werden soll. Das diesem Bericht zugrundeliegende Vorhaben wurde mit Mitteln des Bundesministeriums für Bildung, und Forschung unter dem Förderkennze- ichen 16OH12026 gefördert. Die Verantwortung für den Inhalt dieser Veröf- fentlichung liegt beim Autor. Contents Page3 Contents Introduction to the module books 5 I. Icons and colour codes . 5 Chapter 3 Introduction to Cryptanalysis 7 3.1 Definition of Security . 7 3.1.1 Security of Cryptographic Systems . 7 3.1.2 Categories of Attacks . 8 3.1.3 Categories of Attackers . 9 3.1.4 Secret Key Lengths . 10 3.2 Outline of this Lecture . 11 3.3 Further Reading Materials . 11 Chapter 4 Computational Complexity and Parallelism 13 4.1 Asymptotic Computational Complexity . -

Implementation and Performance Analysis of PBKDF2, Bcrypt, Scrypt Algorithms
Implementation and Performance Analysis of PBKDF2, Bcrypt, Scrypt Algorithms Levent Ertaul, Manpreet Kaur, Venkata Arun Kumar R Gudise CSU East Bay, Hayward, CA, USA. [email protected], [email protected], [email protected] Abstract- With the increase in mobile wireless or data lookup. Whereas, Cryptographic hash functions are technologies, security breaches are also increasing. It has used for building blocks for HMACs which provides become critical to safeguard our sensitive information message authentication. They ensure integrity of the data from the wrongdoers. So, having strong password is that is transmitted. Collision free hash function is the one pivotal. As almost every website needs you to login and which can never have same hashes of different output. If a create a password, it’s tempting to use same password and b are inputs such that H (a) =H (b), and a ≠ b. for numerous websites like banks, shopping and social User chosen passwords shall not be used directly as networking websites. This way we are making our cryptographic keys as they have low entropy and information easily accessible to hackers. Hence, we need randomness properties [2].Password is the secret value from a strong application for password security and which the cryptographic key can be generated. Figure 1 management. In this paper, we are going to compare the shows the statics of increasing cybercrime every year. Hence performance of 3 key derivation algorithms, namely, there is a need for strong key generation algorithms which PBKDF2 (Password Based Key Derivation Function), can generate the keys which are nearly impossible for the Bcrypt and Scrypt. -
Hash Crack: Password Cracking Manual
Hash Crack. Copyright © 2017 Netmux LLC All rights reserved. Without limiting the rights under the copyright reserved above, no part of this publication may be reproduced, stored in, or introduced into a retrieval system, or transmitted in any form or by any means (electronic, mechanical, photocopying, recording, or otherwise) without prior written permission. ISBN-10: 1975924584 ISBN-13: 978-1975924584 Netmux and the Netmux logo are registered trademarks of Netmux, LLC. Other product and company names mentioned herein may be the trademarks of their respective owners. Rather than use a trademark symbol with every occurrence of a trademarked name, we are using the names only in an editorial fashion and to the benefit of the trademark owner, with no intention of infringement of the trademark. The information in this book is distributed on an “As Is” basis, without warranty. While every precaution has been taken in the preparation of this work, neither the author nor Netmux LLC, shall have any liability to any person or entity with respect to any loss or damage caused or alleged to be caused directly or indirectly by the information contained in it. While every effort has been made to ensure the accuracy and legitimacy of the references, referrals, and links (collectively “Links”) presented in this book/ebook, Netmux is not responsible or liable for broken Links or missing or fallacious information at the Links. Any Links in this book to a specific product, process, website, or service do not constitute or imply an endorsement by Netmux of same, or its producer or provider. The views and opinions contained at any Links do not necessarily express or reflect those of Netmux. -

Key Derivation Functions and Their GPU Implementation
MASARYK UNIVERSITY FACULTY}w¡¢£¤¥¦§¨ OF I !"#$%&'()+,-./012345<yA|NFORMATICS Key derivation functions and their GPU implementation BACHELOR’S THESIS Ondrej Mosnáˇcek Brno, Spring 2015 This work is licensed under a Creative Commons Attribution- NonCommercial-ShareAlike 4.0 International License. https://creativecommons.org/licenses/by-nc-sa/4.0/ cbna ii Declaration Hereby I declare, that this paper is my original authorial work, which I have worked out by my own. All sources, references and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Ondrej Mosnáˇcek Advisor: Ing. Milan Brož iii Acknowledgement I would like to thank my supervisor for his guidance and support, and also for his extensive contributions to the Cryptsetup open- source project. Next, I would like to thank my family for their support and pa- tience and also to my friends who were falling behind schedule just like me and thus helped me not to panic. Last but not least, access to computing and storage facilities owned by parties and projects contributing to the National Grid In- frastructure MetaCentrum, provided under the programme “Projects of Large Infrastructure for Research, Development, and Innovations” (LM2010005), is also greatly appreciated. v Abstract Key derivation functions are a key element of many cryptographic applications. Password-based key derivation functions are designed specifically to derive cryptographic keys from low-entropy sources (such as passwords or passphrases) and to counter brute-force and dictionary attacks. However, the most widely adopted standard for password-based key derivation, PBKDF2, as implemented in most applications, is highly susceptible to attacks using Graphics Process- ing Units (GPUs). -

Password Security - When Passwords Are There for the World to See
Password Security - When Passwords are there for the World to see Eleanore Young Marc Ruef (Editor) Offense Department, scip AG Research Department, scip AG [email protected] [email protected] https://www.scip.ch https://www.scip.ch Keywords: Bitcoin, Exchange, GitHub, Hashcat, Leak, OWASP, Password, Policy, Rapid, Storage 1. Preface password from a hash without having to attempt a reversal of the hashing algorithm. This paper was written in 2017 as part of a research project at scip AG, Switzerland. It was initially published online at Furthermore, if passwords are fed through hashing https://www.scip.ch/en/?labs.20170112 and is available in algorithms as is, two persons who happen to use the same English and German. Providing our clients with innovative password, will also have the same hash value. As a research for the information technology of the future is an countermeasure, developers have started adding random essential part of our company culture. user-specific values (the salt) to the password before calculating the hash. The salt will then be stored alongside 2. Introduction the password hash in the user account database. As such, even if two persons use the same password, their resulting The year 2016 has seen many reveals of successful attacks hash value will be different due to the added salt. on user account databases; the most notable cases being the attacks on Yahoo [1] and Dropbox [2]. Thanks to recent Modern GPU architectures are designed for large scale advances not only in graphics processing hardware (GPUs), parallelism. Currently, a decent consumer-grade graphics but also in password cracking software, it has become card is capable of performing on the order of 1000 dangerously cheap to determine the actual passwords from calculations simultaneously. -

Cisco Live / DEFCON / RSA / (ISC)2
#CLUS Penetration Testing For Network Engineers Know Yourself and Enemy, Need Not Fear 100 Battles Joseph Muniz – Architect Americas BRKSEC-2460 #CLUS Cisco Webex Teams Questions? Use Cisco Webex Teams (formerly Cisco Spark) to chat with the speaker after the session How 1 Find this session in the Cisco Events App 2 Click “Join the Discussion” 3 Install Webex Teams or go directly to the team space 4 Enter messages/questions in the team space Webex Teams will be moderated cs.co/ciscolivebot#BRKSEC-2460 by the speaker until June 18, 2018. #CLUS BRKSEC-2460 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 3 WHY DO WEFAIL? #CLUS BRKSEC-2460 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 4 Behind the Headlines #CLUS BRKSEC-2460 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 5 #CLUS BRKSEC-2460 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 6 More than Computer and Phones 500B In 2030 50B In 2020 15B Devices Today #CLUS BRKSEC-2460 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 7 More than Computer and Phones 500B In 2030 50B In 2020 15B Devices Today #CLUS BRKSEC-2460 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 8 More than Computer and Phones 500B In 2030 50B In 2020 15B Devices Today #CLUS BRKSEC-2460 © 2018 Cisco and/or its affiliates. All rights reserved. Cisco Public 9 IoT Challenges Patch Delays Limited Security Development Rogue Devices #CLUS BRKSEC-2460 © 2018 Cisco and/or its affiliates.