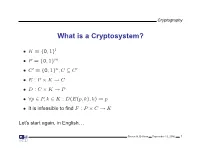
Cryptosystem
Top View
- 1402 Hill Cipher.Pdf
- A New Cryptography Method Based on Hill and Rail Fence Algorithms
- Principle and Computer Simulation Model of Variation of Delastell's
- Polybius Square in Cryptography: a Brief Review of Literature
- German Cipher Machines of World War II This Publication Is a Product of the National Security Agency History Program
- Cmput 210 W2016 Study Guide Chapter 1 Part B 1. Explain Kerchoff's Principle of Cryptosystem Security. 2. Encrypt This Is an E
- A New Attack on the KMOV Cryptosystem
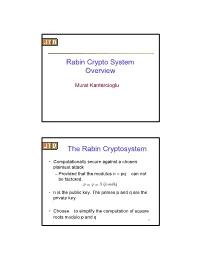
- H-Rabin Cryptosystem
- A Methodology for the Cryptanalysis of Classical Ciphers with Search
- Zigzag Ciphers: a Novel Transposition Method
- Hill Cipher Security Application to Multimedia
- Cryptanalysis of Classical Cryptosystems
- CSE543 - Introduction to Computer and Network Security Module: Cryptography
- Algebra for Cryptology
- Part IV Secret-Key Cryptosystems
- Crypt Analysis of DES Cryptosystem Over Man in the Middle Attack
- Introduction to Cryptography