EE 418 Network Security and Cryptography Lecture #5 Outline: 1
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
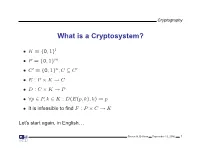
What Is a Cryptosystem?
Cryptography What is a Cryptosystem? • K = {0, 1}l • P = {0, 1}m • C′ = {0, 1}n,C ⊆ C′ • E : P × K → C • D : C × K → P • ∀p ∈ P, k ∈ K : D(E(p, k), k) = p • It is infeasible to find F : P × C → K Let’s start again, in English. Steven M. Bellovin September 13, 2006 1 Cryptography What is a Cryptosystem? A cryptosystem is pair of algorithms that take a key and convert plaintext to ciphertext and back. Plaintext is what you want to protect; ciphertext should appear to be random gibberish. The design and analysis of today’s cryptographic algorithms is highly mathematical. Do not try to design your own algorithms. Steven M. Bellovin September 13, 2006 2 Cryptography A Tiny Bit of History • Encryption goes back thousands of years • Classical ciphers encrypted letters (and perhaps digits), and yielded all sorts of bizarre outputs. • The advent of military telegraphy led to ciphers that produced only letters. Steven M. Bellovin September 13, 2006 3 Cryptography Codes vs. Ciphers • Ciphers operate syntactically, on letters or groups of letters: A → D, B → E, etc. • Codes operate semantically, on words, phrases, or sentences, per this 1910 codebook Steven M. Bellovin September 13, 2006 4 Cryptography A 1910 Commercial Codebook Steven M. Bellovin September 13, 2006 5 Cryptography Commercial Telegraph Codes • Most were aimed at economy • Secrecy from casual snoopers was a useful side-effect, but not the primary motivation • That said, a few such codes were intended for secrecy; I have some in my collection, including one intended for union use Steven M. -

A Covert Encryption Method for Applications in Electronic Data Interchange
Technological University Dublin ARROW@TU Dublin Articles School of Electrical and Electronic Engineering 2009-01-01 A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan Blackledge Technological University Dublin, [email protected] Dmitry Dubovitskiy Oxford Recognition Limited, [email protected] Follow this and additional works at: https://arrow.tudublin.ie/engscheleart2 Part of the Digital Communications and Networking Commons, Numerical Analysis and Computation Commons, and the Software Engineering Commons Recommended Citation Blackledge, J., Dubovitskiy, D.: A Covert Encryption Method for Applications in Electronic Data Interchange. ISAST Journal on Electronics and Signal Processing, vol: 4, issue: 1, pages: 107 -128, 2009. doi:10.21427/D7RS67 This Article is brought to you for free and open access by the School of Electrical and Electronic Engineering at ARROW@TU Dublin. It has been accepted for inclusion in Articles by an authorized administrator of ARROW@TU Dublin. For more information, please contact [email protected], [email protected]. This work is licensed under a Creative Commons Attribution-Noncommercial-Share Alike 4.0 License A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan M Blackledge, Fellow, IET, Fellow, BCS and Dmitry A Dubovitskiy, Member IET Abstract— A principal weakness of all encryption systems is to make sure that the ciphertext is relatively strong (but not that the output data can be ‘seen’ to be encrypted. In other too strong!) and that the information extracted is of good words, encrypted data provides a ‘flag’ on the potential value quality in terms of providing the attacker with ‘intelligence’ of the information that has been encrypted. -

Amy Bell Abilene, TX December 2005
Compositional Cryptology Thesis Presented to the Honors Committee of McMurry University In partial fulfillment of the requirements for Undergraduate Honors in Math By Amy Bell Abilene, TX December 2005 i ii Acknowledgements I could not have completed this thesis without all the support of my professors, family, and friends. Dr. McCoun especially deserves many thanks for helping me to develop the idea of compositional cryptology and for all the countless hours spent discussing new ideas and ways to expand my thesis. Because of his persistence and dedication, I was able to learn and go deeper into the subject matter than I ever expected. My committee members, Dr. Rittenhouse and Dr. Thornburg were also extremely helpful in giving me great advice for presenting my thesis. I also want to thank my family for always supporting me through everything. Without their love and encouragement I would never have been able to complete my thesis. Thanks also should go to my wonderful roommates who helped to keep me motivated during the final stressful months of my thesis. I especially want to thank my fiancé, Gian Falco, who has always believed in me and given me so much love and support throughout my college career. There are many more professors, coaches, and friends that I want to thank not only for encouraging me with my thesis, but also for helping me through all my pursuits at school. Thank you to all of my McMurry family! iii Preface The goal of this research was to gain a deeper understanding of some existing cryptosystems, to implement these cryptosystems in a computer programming language of my choice, and to discover whether the composition of cryptosystems leads to greater security. -

A New Cryptosystem for Ciphers Using Transposition Techniques
Published by : International Journal of Engineering Research & Technology (IJERT) http://www.ijert.org ISSN: 2278-0181 Vol. 8 Issue 04, April-2019 A New Cryptosystem for Ciphers using Transposition Techniques U. Thirupalu Dr. E. Kesavulu Reddy FCSRC (USA) Research Scholar Assistant Professor, Dept. of Computer Science Dept. of Computer Science S V U CM&CS – Tirupati S V U CM&CS - Tirupati India – 517502 India – 517502 Abstract:- Data Encryption techniques is used to avoid the performs the decryption. Cryptographic algorithms are unauthorized access original content of a data in broadly classified as Symmetric key cryptography and communication between two parties, but the data can be Asymmetric key cryptography. recovered only through using a key known as decryption process. The objective of the encryption is to secure or save data from unauthorized access in term of inspecting or A. Symmetric Cryptography adapting the data. Encryption can be implemented occurs by In the symmetric key encryption, same key is used for both using some substitute technique, shifting technique, or encryption and decryption process. Symmetric algorithms mathematical operations. By adapting these techniques we more advantageous with low consuming with more can generate a different form of that data which can be computing power and it works with high speed in encrypt difficult to understand by any person. The original data is them. The symmetric key encryption takes place in two referred to as the plaintext and the encrypted data as the modes either as the block ciphers or as the stream ciphers. cipher text. Several symmetric key base algorithms have been The block cipher mode provides, whole data is divided into developed in the past year. -

Affine Cipher Project 1 Introduction
Affine Cipher Project 141KECBZ0H5CRK1HUZK1CGPCR.5PUGUZU1WCU.CM1CUBHUCAK.6.Z5WCP1RK1UCH5 WC0EPU1KECU.C141KEC.UB1KXC,,RBHKV1PCWGRQ15P7CHCUHV1C.6CU9.CRGUG1P Directions: • Answer all numbered questions completely. • Show non-trivial work, and put your final answer in the box provided. • Questions without boxes should be answered in complete sentences in the space provided. 1 Introduction Cryptography is the study of secret codes, or the secure transmission of information that nobody except the desired recipient can read. By the end of this project, you will be able to decipher the quote printed above. The mathematical study of ciphers will lead us through a world in which the number line is a closed curve, and fractions do not exist. This project is designed to help you to: • read and understand definitions and notation • observe patterns and generalize • think logically, analytically, and abstractly • express problems and solutions precisely • follow examples • combine ideas to solve problems and create applications 1 2 Caesar Cipher A cipher is a function or algorithm for translating plaintext into encrypted ciphertext. Throughout history, governments and merchants have used ciphers to safely transmit sensitive information. Julius Caesar is said to have use a simple system of substituting each letter with the letter 3 spots over, wrapping around the alphabet if necessary. Here is the mapping: A B C D E F G H I J K L M N O P Q R S T U V W X Y Z # # # # # # # # # # # # # # # # # # # # # # # # # # D E F G H I J K L M N O P Q R S T U V W X Y Z A B C Space and punctuation are discarded. -

Caesar's Cipher Is a Monoalphabetic
Mathematical summer in Paris - Cryptography Exercise 1 (Caesar’s cipher ?) Caesar’s cipher is a monoalphabetic encryption method where all letters in the alphabet are shifted by a certain constant d. For example, with d = 3, we obtain A ! D; B ! E;:::; Y ! B; Z ! C: 1. Translate the encryption function f in algebraic terms. What is the decryption function g? 2. What is the key in Caesar’s cipher? How many keys are possible? 3. Decrypt the ciphertext LIPPSASVPH. Exercise 2 (Affine encryption ?) We now want to study a more general kind of encryption method, called affine encryption. We represent each letter in the latin alphabet by its position in the alphabet, starting with 0, i.e. A ! 0; B ! 1; C ! 2;:::; Z ! 25; and we consider the map f : x ! ax + b mod 26; where a and b are fixed integers between 0 and 25. We want to use the map f to encrypt each letter in the plaintext. 1. What happens if we choose a = 1? We now choose a = 10 and b = 3. def 2. Let 0 ≤ y ≤ 25 such that y = f(x) = 10x + 3 mod 26. Prove that there exists k 2 Z such that y = 10x + 26k + 3. 3. Prove that y is always odd. 4. What can we say about this encryption method? We now choose a = 9 and b = 4. 5. Find an integer u 2 Z such that 9u = 1 mod 26. 6. Explain why the equation y = 9x + 4 mod 26, with 0 ≤ y ≤ 25, always has a solution. -

The Mathemathics of Secrets.Pdf
THE MATHEMATICS OF SECRETS THE MATHEMATICS OF SECRETS CRYPTOGRAPHY FROM CAESAR CIPHERS TO DIGITAL ENCRYPTION JOSHUA HOLDEN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright c 2017 by Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TR press.princeton.edu Jacket image courtesy of Shutterstock; design by Lorraine Betz Doneker All Rights Reserved Library of Congress Cataloging-in-Publication Data Names: Holden, Joshua, 1970– author. Title: The mathematics of secrets : cryptography from Caesar ciphers to digital encryption / Joshua Holden. Description: Princeton : Princeton University Press, [2017] | Includes bibliographical references and index. Identifiers: LCCN 2016014840 | ISBN 9780691141756 (hardcover : alk. paper) Subjects: LCSH: Cryptography—Mathematics. | Ciphers. | Computer security. Classification: LCC Z103 .H664 2017 | DDC 005.8/2—dc23 LC record available at https://lccn.loc.gov/2016014840 British Library Cataloging-in-Publication Data is available This book has been composed in Linux Libertine Printed on acid-free paper. ∞ Printed in the United States of America 13579108642 To Lana and Richard for their love and support CONTENTS Preface xi Acknowledgments xiii Introduction to Ciphers and Substitution 1 1.1 Alice and Bob and Carl and Julius: Terminology and Caesar Cipher 1 1.2 The Key to the Matter: Generalizing the Caesar Cipher 4 1.3 Multiplicative Ciphers 6 -

With Answers
Module 10.4: Exploring Some Historical Ciphers Gregory V. Bard January 30, 2020 • This is a practice workbook the Affine Cipher, touching on some shift ciphers (such as the Caesar cipher, the ROT-13 cipher), the Atbash cipher, and the Vigen`ereCipher. • The Affine Cipher was introduced in Module 10-2: The Basics of Modular Arithmetic, and some skills from Module 10-3: Modular Inverses are needed. • There is a with-answers version, and a without-answers version. • In the with-answers version of this workbook, the black ink represents the question, and the blue ink represents the answer. Question 10-4-1 Suppose Boris normally communicates with his handlers in Moscow using the affine cipher, and the encryption function c = fB(p) = 7p + 20 mod 26, while Natasha normally uses c = fN (p) = 11p + 8 mod 26. They have a very secret message to send back to Moscow, so they're going to encrypt the message twice, for added security. As you can probably guess, this is equivalent to using the affine cipher only once, but with a different function. • If Boris encrypts the plaintext first, followed by Natasha second, then what would BAT encrypt to? (B, A, T) becomes (1, 0, 19) and encrypts to (fB(1); fB(0); fB(19)) ≡ (1; 20; 23). We encrypt again to (fN (1); fN (20); fN (23)) ≡ (19; 20; 1), which becomes (T, U, B) or TUB. • If Natasha encrypts the plaintext first, followed by Boris second, then what would BAT encrypt to? (B, A, T) becomes (1, 0, 19) and encrypts to (fN (1); fN (0); fN (19)) ≡ (19; 8; 9). -

A Secure Variant of the Hill Cipher
† A Secure Variant of the Hill Cipher Mohsen Toorani ‡ Abolfazl Falahati Abstract the corresponding key of each block but it has several security problems [7]. The Hill cipher is a classical symmetric encryption In this paper, a secure cryptosystem is introduced that algorithm that succumbs to the know-plaintext attack. overcomes all the security drawbacks of the Hill cipher. Although its vulnerability to cryptanalysis has rendered it The proposed scheme includes an encryption algorithm unusable in practice, it still serves an important that is a variant of the Affine Hill cipher for which a pedagogical role in cryptology and linear algebra. In this secure cryptographic protocol is introduced. The paper, a variant of the Hill cipher is introduced that encryption core of the proposed scheme has the same makes the Hill cipher secure while it retains the structure of the Affine Hill cipher but its internal efficiency. The proposed scheme includes a ciphering manipulations are different from the previously proposed core for which a cryptographic protocol is introduced. cryptosystems. The rest of this paper is organized as follows. Section 2 briefly introduces the Hill cipher. Our 1. Introduction proposed scheme is introduced and its computational costs are evaluated in Section 3, and Section 4 concludes The Hill cipher was invented by L.S. Hill in 1929 [1]. It is the paper. a famous polygram and a classical symmetric cipher based on matrix transformation but it succumbs to the 2. The Hill Cipher known-plaintext attack [2]. Although its vulnerability to cryptanalysis has rendered it unusable in practice, it still In the Hill cipher, the ciphertext is obtained from the serves an important pedagogical role in both cryptology plaintext by means of a linear transformation. -

MAT 302: LECTURE SUMMARY Last Class We Discussed Two Classical Ciphers, Both of Which Turned out to Be Rather Insecure (As Evide
MAT 302: LECTURE SUMMARY Last class we discussed two classical ciphers, both of which turned out to be rather insecure (as evidenced by your cracking them manually during lecture): • The Scytale cipher • The Caesar (aka shift) cipher We began today’s lecture by writing the latter down in mathematical notation. To this end, it is convenient to use the set A = f0; 1; 2;:::; 25g to represent the English alphabet, i.e. 0 represents A, 1 represents B, etc. The Caesar Cipher. The Caesar cipher (or shift cipher) consists of a key k 2 Z, an encryption function ek : A −! A x 7−! x + k (mod 26) and a decryption function dk : A −! A x 7−! x − k (mod 26): The Caesar cipher is insecure because the space of all possible keys is rather small (how many are there?), so it is a trivial matter for Oscar to check all possible keys. We next discussed a variant of this, whose key space is somewhat larger: the affine cipher. The Affine Cipher. The affine cipher consists of a key (a; b) 2 Z2, an encryption function e(a;b) : A −! A x 7−! ax + b (mod 26) and a decryption function d(a;b) : A −! A x 7−! a−1(x − b) (mod 26) Actually, as stated this isn’t well-defined: a−1 doesn’t always exist (mod 26). Recall that a−1 is the element of A satisfying a−1a ≡ 1 (mod 26): For example, 0 has no (multiplicative) inverse (mod 26). Less trivially, 2 has no multiplicative inverse. -
An Introduction to Cryptography
abstract examples cryptanalysis harder cryptography schemes An Introduction to Cryptography Joe Fields http://www.southernct.edu/~fields/ Joe Fields Cryptography abstract examples Terminology cryptanalysis harder cryptography schemes Cryptography is the study of "secret writing." This is the only branch of mathematics to be designated by the U.S. government as export-controlled. Cryptographic knowledge is considered to be "war materials!" While we won't head off into TOP SECRET territory we will have a bit of fun working out how to make (and to break) good secret codes. Joe Fields Cryptography abstract examples Terminology cryptanalysis harder cryptography schemes the enigma Joe Fields Cryptography abstract examples Terminology cryptanalysis harder cryptography schemes WACs Joe Fields Cryptography Cryptology means \the study of secrets" practically speaking, they are synonyms... abstract examples Terminology cryptanalysis harder cryptography schemes Cryptography or Cryptology? Cryptography means \secret writing" Joe Fields Cryptography practically speaking, they are synonyms... abstract examples Terminology cryptanalysis harder cryptography schemes Cryptography or Cryptology? Cryptography means \secret writing" Cryptology means \the study of secrets" Joe Fields Cryptography abstract examples Terminology cryptanalysis harder cryptography schemes Cryptography or Cryptology? Cryptography means \secret writing" Cryptology means \the study of secrets" practically speaking, they are synonyms... Joe Fields Cryptography Bob (the recipient) but they are afraid that. Eve (the eavesdropper) will snoop on them and learn their secrets. abstract examples Terminology cryptanalysis harder cryptography schemes Cast of Characters Alice (the sender) wants to send a message to. Joe Fields Cryptography Eve (the eavesdropper) will snoop on them and learn their secrets. abstract examples Terminology cryptanalysis harder cryptography schemes Cast of Characters Alice (the sender) wants to send a message to. -

A Hybrid Cryptosystem Based on Vigenère Cipher and Columnar Transposition Cipher
International Journal of Advanced Technology & Engineering Research (IJATER) www.ijater.com A HYBRID CRYPTOSYSTEM BASED ON VIGENÈRE CIPHER AND COLUMNAR TRANSPOSITION CIPHER Quist-Aphetsi Kester, MIEEE, Lecturer Faculty of Informatics, Ghana Technology University College, PMB 100 Accra North, Ghana Phone Contact +233 209822141 Email: [email protected] / [email protected] graphy that use the same cryptographic keys for both en- Abstract cryption of plaintext and decryption of cipher text. The keys may be identical or there may be a simple transformation to Privacy is one of the key issues addressed by information go between the two keys. The keys, in practice, represent a Security. Through cryptographic encryption methods, one shared secret between two or more parties that can be used can prevent a third party from understanding transmitted raw to maintain a private information link [5]. This requirement data over unsecured channel during signal transmission. The that both parties have access to the secret key is one of the cryptographic methods for enhancing the security of digital main drawbacks of symmetric key encryption, in compari- contents have gained high significance in the current era. son to public-key encryption. Typical examples symmetric Breach of security and misuse of confidential information algorithms are Advanced Encryption Standard (AES), Blow- that has been intercepted by unauthorized parties are key fish, Tripple Data Encryption Standard (3DES) and Serpent problems that information security tries to solve. [6]. This paper sets out to contribute to the general body of Asymmetric or Public key encryption on the other hand is an knowledge in the area of classical cryptography by develop- encryption method where a message encrypted with a reci- ing a new hybrid way of encryption of plaintext.