CSE543 - Introduction to Computer and Network Security Module: Cryptography
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Introduction to Cryptography Teachers' Reference
Introduction to Cryptography Teachers’ Reference Dear Teachers! Here I have mentioned some guidelines for your good self so that your students can benefit form these modules. I am very hopeful that you will enjoy conducting the session. After Module-1 1. Scytale Decryption In your class ask your students to devise a method to decrypt the message just been encrypted using Scytale. Encourage them to look around to find a decryption tool. Ask your students to cut a strip of paper some 4mm wide, 32cm long and light pencil lines drawn on it at 4mm distance. To give it the following shape. Now write cipher text on the paper strip in the following way. t i t i r s a e e e e e b h y w i t i l r f d n m g o e e o h v n t t r a a e c a g o o w d m h Encourage them once again to find a tool around them to decrypt it. Ask them to look for a very familiar thing they must have been using right from their early school days to do their work. Now many of them must have figured out that you are asking for a pencil. Now ask them to use the pencil to decrypt the cipher text by using pencil and the only reasonable way would be to wrap the paper strip around the strip. The plain text will be visible along the six side faces of the pencil. Encourage them to reason that how did it work? There is a connection between six rows of the table in which the plain text was filled and the six faces of the pencil. -

Classical Encryption Techniques
CPE 542: CRYPTOGRAPHY & NETWORK SECURITY Chapter 2: Classical Encryption Techniques Dr. Lo’ai Tawalbeh Computer Engineering Department Jordan University of Science and Technology Jordan Dr. Lo’ai Tawalbeh Fall 2005 Introduction Basic Terminology • plaintext - the original message • ciphertext - the coded message • key - information used in encryption/decryption, and known only to sender/receiver • encipher (encrypt) - converting plaintext to ciphertext using key • decipher (decrypt) - recovering ciphertext from plaintext using key • cryptography - study of encryption principles/methods/designs • cryptanalysis (code breaking) - the study of principles/ methods of deciphering ciphertext Dr. Lo’ai Tawalbeh Fall 2005 1 Cryptographic Systems Cryptographic Systems are categorized according to: 1. The operation used in transferring plaintext to ciphertext: • Substitution: each element in the plaintext is mapped into another element • Transposition: the elements in the plaintext are re-arranged. 2. The number of keys used: • Symmetric (private- key) : both the sender and receiver use the same key • Asymmetric (public-key) : sender and receiver use different key 3. The way the plaintext is processed : • Block cipher : inputs are processed one block at a time, producing a corresponding output block. • Stream cipher: inputs are processed continuously, producing one element at a time (bit, Dr. Lo’ai Tawalbeh Fall 2005 Cryptographic Systems Symmetric Encryption Model Dr. Lo’ai Tawalbeh Fall 2005 2 Cryptographic Systems Requirements • two requirements for secure use of symmetric encryption: 1. a strong encryption algorithm 2. a secret key known only to sender / receiver •Y = Ek(X), where X: the plaintext, Y: the ciphertext •X = Dk(Y) • assume encryption algorithm is known •implies a secure channel to distribute key Dr. -

Enhancing the Security of Caesar Cipher Substitution Method Using a Randomized Approach for More Secure Communication
International Journal of Computer Applications (0975 – 8887) Volume 129 – No.13, November2015 Enhancing the Security of Caesar Cipher Substitution Method using a Randomized Approach for more Secure Communication Atish Jain Ronak Dedhia Abhijit Patil Dept. of Computer Engineering Dept. of Computer Engineering Dept. of Computer Engineering D.J. Sanghvi College of D.J. Sanghvi College of D.J. Sanghvi College of Engineering Engineering Engineering Mumbai University, Mumbai, Mumbai University, Mumbai, Mumbai University, Mumbai, India India India ABSTRACT communication can be encoded to prevent their contents from Caesar cipher is an ancient, elementary method of encrypting being disclosed through various techniques like interception plain text message into cipher text protecting it from of message or eavesdropping. Different ways include using adversaries. However, with the advent of powerful computers, ciphers, codes, substitution, etc. so that only the authorized there is a need for increasing the complexity of such people can view and interpret the real message correctly. techniques. This paper contributes in the area of classical Cryptography concerns itself with four main objectives, cryptography by providing a modified and expanded version namely, 1) Confidentiality, 2) Integrity, 3) Non-repudiation for Caesar cipher using knowledge of mathematics and and 4) Authentication. [1] computer science. To increase the strength of this classical Cryptography is divided into two types, Symmetric key and encryption technique, the proposed modified algorithm uses Asymmetric key cryptography. In Symmetric key the concepts of affine ciphers, transposition ciphers and cryptography a single key is shared between sender and randomized substitution techniques to create a cipher text receiver. The sender uses the shared key and encryption which is nearly impossible to decode. -
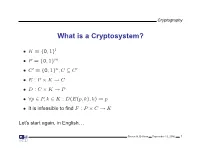
What Is a Cryptosystem?
Cryptography What is a Cryptosystem? • K = {0, 1}l • P = {0, 1}m • C′ = {0, 1}n,C ⊆ C′ • E : P × K → C • D : C × K → P • ∀p ∈ P, k ∈ K : D(E(p, k), k) = p • It is infeasible to find F : P × C → K Let’s start again, in English. Steven M. Bellovin September 13, 2006 1 Cryptography What is a Cryptosystem? A cryptosystem is pair of algorithms that take a key and convert plaintext to ciphertext and back. Plaintext is what you want to protect; ciphertext should appear to be random gibberish. The design and analysis of today’s cryptographic algorithms is highly mathematical. Do not try to design your own algorithms. Steven M. Bellovin September 13, 2006 2 Cryptography A Tiny Bit of History • Encryption goes back thousands of years • Classical ciphers encrypted letters (and perhaps digits), and yielded all sorts of bizarre outputs. • The advent of military telegraphy led to ciphers that produced only letters. Steven M. Bellovin September 13, 2006 3 Cryptography Codes vs. Ciphers • Ciphers operate syntactically, on letters or groups of letters: A → D, B → E, etc. • Codes operate semantically, on words, phrases, or sentences, per this 1910 codebook Steven M. Bellovin September 13, 2006 4 Cryptography A 1910 Commercial Codebook Steven M. Bellovin September 13, 2006 5 Cryptography Commercial Telegraph Codes • Most were aimed at economy • Secrecy from casual snoopers was a useful side-effect, but not the primary motivation • That said, a few such codes were intended for secrecy; I have some in my collection, including one intended for union use Steven M. -

Simple Substitution and Caesar Ciphers
Spring 2015 Chris Christensen MAT/CSC 483 Simple Substitution Ciphers The art of writing secret messages – intelligible to those who are in possession of the key and unintelligible to all others – has been studied for centuries. The usefulness of such messages, especially in time of war, is obvious; on the other hand, their solution may be a matter of great importance to those from whom the key is concealed. But the romance connected with the subject, the not uncommon desire to discover a secret, and the implied challenge to the ingenuity of all from who it is hidden have attracted to the subject the attention of many to whom its utility is a matter of indifference. Abraham Sinkov In Mathematical Recreations & Essays By W.W. Rouse Ball and H.S.M. Coxeter, c. 1938 We begin our study of cryptology from the romantic point of view – the point of view of someone who has the “not uncommon desire to discover a secret” and someone who takes up the “implied challenged to the ingenuity” that is tossed down by secret writing. We begin with one of the most common classical ciphers: simple substitution. A simple substitution cipher is a method of concealment that replaces each letter of a plaintext message with another letter. Here is the key to a simple substitution cipher: Plaintext letters: abcdefghijklmnopqrstuvwxyz Ciphertext letters: EKMFLGDQVZNTOWYHXUSPAIBRCJ The key gives the correspondence between a plaintext letter and its replacement ciphertext letter. (It is traditional to use small letters for plaintext and capital letters, or small capital letters, for ciphertext. We will not use small capital letters for ciphertext so that plaintext and ciphertext letters will line up vertically.) Using this key, every plaintext letter a would be replaced by ciphertext E, every plaintext letter e by L, etc. -

Cryptography in Modern World
Cryptography in Modern World Julius O. Olwenyi, Aby Tino Thomas, Ayad Barsoum* St. Mary’s University, San Antonio, TX (USA) Emails: [email protected], [email protected], [email protected] Abstract — Cryptography and Encryption have been where a letter in plaintext is simply shifted 3 places down used for secure communication. In the modern world, the alphabet [4,5]. cryptography is a very important tool for protecting information in computer systems. With the invention ABCDEFGHIJKLMNOPQRSTUVWXYZ of the World Wide Web or Internet, computer systems are highly interconnected and accessible from DEFGHIJKLMNOPQRSTUVWXYZABC any part of the world. As more systems get interconnected, more threat actors try to gain access The ciphertext of the plaintext “CRYPTOGRAPHY” will to critical information stored on the network. It is the be “FUBSWRJUASLB” in a Caesar cipher. responsibility of data owners or organizations to keep More recent derivative of Caesar cipher is Rot13 this data securely and encryption is the main tool used which shifts 13 places down the alphabet instead of 3. to secure information. In this paper, we will focus on Rot13 was not all about data protection but it was used on different techniques and its modern application of online forums where members could share inappropriate cryptography. language or nasty jokes without necessarily being Keywords: Cryptography, Encryption, Decryption, Data offensive as it will take those interested in those “jokes’ security, Hybrid Encryption to shift characters 13 spaces to read the message and if not interested you do not need to go through the hassle of converting the cipher. I. INTRODUCTION In the 16th century, the French cryptographer Back in the days, cryptography was not all about Blaise de Vigenere [4,5], developed the first hiding messages or secret communication, but in ancient polyalphabetic substitution basically based on Caesar Egypt, where it began; it was carved into the walls of cipher, but more difficult to crack the cipher text. -

A Covert Encryption Method for Applications in Electronic Data Interchange
Technological University Dublin ARROW@TU Dublin Articles School of Electrical and Electronic Engineering 2009-01-01 A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan Blackledge Technological University Dublin, [email protected] Dmitry Dubovitskiy Oxford Recognition Limited, [email protected] Follow this and additional works at: https://arrow.tudublin.ie/engscheleart2 Part of the Digital Communications and Networking Commons, Numerical Analysis and Computation Commons, and the Software Engineering Commons Recommended Citation Blackledge, J., Dubovitskiy, D.: A Covert Encryption Method for Applications in Electronic Data Interchange. ISAST Journal on Electronics and Signal Processing, vol: 4, issue: 1, pages: 107 -128, 2009. doi:10.21427/D7RS67 This Article is brought to you for free and open access by the School of Electrical and Electronic Engineering at ARROW@TU Dublin. It has been accepted for inclusion in Articles by an authorized administrator of ARROW@TU Dublin. For more information, please contact [email protected], [email protected]. This work is licensed under a Creative Commons Attribution-Noncommercial-Share Alike 4.0 License A Covert Encryption Method for Applications in Electronic Data Interchange Jonathan M Blackledge, Fellow, IET, Fellow, BCS and Dmitry A Dubovitskiy, Member IET Abstract— A principal weakness of all encryption systems is to make sure that the ciphertext is relatively strong (but not that the output data can be ‘seen’ to be encrypted. In other too strong!) and that the information extracted is of good words, encrypted data provides a ‘flag’ on the potential value quality in terms of providing the attacker with ‘intelligence’ of the information that has been encrypted. -

A New Cryptosystem for Ciphers Using Transposition Techniques
Published by : International Journal of Engineering Research & Technology (IJERT) http://www.ijert.org ISSN: 2278-0181 Vol. 8 Issue 04, April-2019 A New Cryptosystem for Ciphers using Transposition Techniques U. Thirupalu Dr. E. Kesavulu Reddy FCSRC (USA) Research Scholar Assistant Professor, Dept. of Computer Science Dept. of Computer Science S V U CM&CS – Tirupati S V U CM&CS - Tirupati India – 517502 India – 517502 Abstract:- Data Encryption techniques is used to avoid the performs the decryption. Cryptographic algorithms are unauthorized access original content of a data in broadly classified as Symmetric key cryptography and communication between two parties, but the data can be Asymmetric key cryptography. recovered only through using a key known as decryption process. The objective of the encryption is to secure or save data from unauthorized access in term of inspecting or A. Symmetric Cryptography adapting the data. Encryption can be implemented occurs by In the symmetric key encryption, same key is used for both using some substitute technique, shifting technique, or encryption and decryption process. Symmetric algorithms mathematical operations. By adapting these techniques we more advantageous with low consuming with more can generate a different form of that data which can be computing power and it works with high speed in encrypt difficult to understand by any person. The original data is them. The symmetric key encryption takes place in two referred to as the plaintext and the encrypted data as the modes either as the block ciphers or as the stream ciphers. cipher text. Several symmetric key base algorithms have been The block cipher mode provides, whole data is divided into developed in the past year. -

The Mathemathics of Secrets.Pdf
THE MATHEMATICS OF SECRETS THE MATHEMATICS OF SECRETS CRYPTOGRAPHY FROM CAESAR CIPHERS TO DIGITAL ENCRYPTION JOSHUA HOLDEN PRINCETON UNIVERSITY PRESS PRINCETON AND OXFORD Copyright c 2017 by Princeton University Press Published by Princeton University Press, 41 William Street, Princeton, New Jersey 08540 In the United Kingdom: Princeton University Press, 6 Oxford Street, Woodstock, Oxfordshire OX20 1TR press.princeton.edu Jacket image courtesy of Shutterstock; design by Lorraine Betz Doneker All Rights Reserved Library of Congress Cataloging-in-Publication Data Names: Holden, Joshua, 1970– author. Title: The mathematics of secrets : cryptography from Caesar ciphers to digital encryption / Joshua Holden. Description: Princeton : Princeton University Press, [2017] | Includes bibliographical references and index. Identifiers: LCCN 2016014840 | ISBN 9780691141756 (hardcover : alk. paper) Subjects: LCSH: Cryptography—Mathematics. | Ciphers. | Computer security. Classification: LCC Z103 .H664 2017 | DDC 005.8/2—dc23 LC record available at https://lccn.loc.gov/2016014840 British Library Cataloging-in-Publication Data is available This book has been composed in Linux Libertine Printed on acid-free paper. ∞ Printed in the United States of America 13579108642 To Lana and Richard for their love and support CONTENTS Preface xi Acknowledgments xiii Introduction to Ciphers and Substitution 1 1.1 Alice and Bob and Carl and Julius: Terminology and Caesar Cipher 1 1.2 The Key to the Matter: Generalizing the Caesar Cipher 4 1.3 Multiplicative Ciphers 6 -

Recommendation for Block Cipher Modes of Operation Methods
NIST Special Publication 800-38A Recommendation for Block 2001 Edition Cipher Modes of Operation Methods and Techniques Morris Dworkin C O M P U T E R S E C U R I T Y ii C O M P U T E R S E C U R I T Y Computer Security Division Information Technology Laboratory National Institute of Standards and Technology Gaithersburg, MD 20899-8930 December 2001 U.S. Department of Commerce Donald L. Evans, Secretary Technology Administration Phillip J. Bond, Under Secretary of Commerce for Technology National Institute of Standards and Technology Arden L. Bement, Jr., Director iii Reports on Information Security Technology The Information Technology Laboratory (ITL) at the National Institute of Standards and Technology (NIST) promotes the U.S. economy and public welfare by providing technical leadership for the Nation’s measurement and standards infrastructure. ITL develops tests, test methods, reference data, proof of concept implementations, and technical analyses to advance the development and productive use of information technology. ITL’s responsibilities include the development of technical, physical, administrative, and management standards and guidelines for the cost-effective security and privacy of sensitive unclassified information in Federal computer systems. This Special Publication 800-series reports on ITL’s research, guidance, and outreach efforts in computer security, and its collaborative activities with industry, government, and academic organizations. Certain commercial entities, equipment, or materials may be identified in this document in order to describe an experimental procedure or concept adequately. Such identification is not intended to imply recommendation or endorsement by the National Institute of Standards and Technology, nor is it intended to imply that the entities, materials, or equipment are necessarily the best available for the purpose. -

Polish Mathematicians Finding Patterns in Enigma Messages
Fall 2006 Chris Christensen MAT/CSC 483 Machine Ciphers Polyalphabetic ciphers are good ways to destroy the usefulness of frequency analysis. Implementation can be a problem, however. The key to a polyalphabetic cipher specifies the order of the ciphers that will be used during encryption. Ideally there would be as many ciphers as there are letters in the plaintext message and the ordering of the ciphers would be random – an one-time pad. More commonly, some rotation among a small number of ciphers is prescribed. But, rotating among a small number of ciphers leads to a period, which a cryptanalyst can exploit. Rotating among a “large” number of ciphers might work, but that is hard to do by hand – there is a high probability of encryption errors. Maybe, a machine. During World War II, all the Allied and Axis countries used machine ciphers. The United States had SIGABA, Britain had TypeX, Japan had “Purple,” and Germany (and Italy) had Enigma. SIGABA http://en.wikipedia.org/wiki/SIGABA 1 A TypeX machine at Bletchley Park. 2 From the 1920s until the 1970s, cryptology was dominated by machine ciphers. What the machine ciphers typically did was provide a mechanical way to rotate among a large number of ciphers. The rotation was not random, but the large number of ciphers that were available could prevent depth from occurring within messages and (if the machines were used properly) among messages. We will examine Enigma, which was broken by Polish mathematicians in the 1930s and by the British during World War II. The Japanese Purple machine, which was used to transmit diplomatic messages, was broken by William Friedman’s cryptanalysts. -
FROM JULIUS CAESAR to the BLOCKCHAIN: a BRIEF HISTORY of CRYPTOGRAPHY by Côme JEAN JARRY & Romain ROUPHAEL, Cofounders of BELEM
Corporate identity in the digital era #9 JANUARY 2017 FROM JULIUS CAESAR TO THE BLOCKCHAIN: A BRIEF HISTORY OF CRYPTOGRAPHY By Côme JEAN JARRY & Romain ROUPHAEL, cofounders of BELEM 22 The world’s most important asset is information. Now message was inscribed lengthwise. Once the parchment more than ever. With computer theft and hacking was unrolled, the letters of the message were mixed becoming a common threat, protecting information up and the message meaningless. The receiver would is crucial to ensure a trusted global economy. need an identical stick to decipher the text. The E-commerce, online banking, social networking or scytale transposition cipher relied on changing the emailing, online medical results checking, all our order of the letters, rather than the letters themselves. transactions made across digital networks and This cryptographic technique still prevails today. insecure channels of communication, such as the Internet, mobile phones or ATMs, are subjected to vulnerabilities. Our best answer is cryptography. And THE ART OF SUBSTITUTION it has always been. As a science and as an art, it is Julius Caesar was also known to use encryption to an essential way to protect communication. convey messages to his army generals posted in the Cryptography goes back to older times, as far back as war front. The Caesar cipher is a simple substitution the Ancient World. cipher in which each letter of the plaintext is rotated left or right by some number of positions down the alphabet. The receiver of the message would then Early cryptography was solely concerned with shift the letters back by the same number of positions concealing and protecting messages.