Buffer Overflow Attacks: Detect, Exploit, Prevent
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Latexsample-Thesis
INTEGRAL ESTIMATION IN QUANTUM PHYSICS by Jane Doe A dissertation submitted to the faculty of The University of Utah in partial fulfillment of the requirements for the degree of Doctor of Philosophy Department of Mathematics The University of Utah May 2016 Copyright c Jane Doe 2016 All Rights Reserved The University of Utah Graduate School STATEMENT OF DISSERTATION APPROVAL The dissertation of Jane Doe has been approved by the following supervisory committee members: Cornelius L´anczos , Chair(s) 17 Feb 2016 Date Approved Hans Bethe , Member 17 Feb 2016 Date Approved Niels Bohr , Member 17 Feb 2016 Date Approved Max Born , Member 17 Feb 2016 Date Approved Paul A. M. Dirac , Member 17 Feb 2016 Date Approved by Petrus Marcus Aurelius Featherstone-Hough , Chair/Dean of the Department/College/School of Mathematics and by Alice B. Toklas , Dean of The Graduate School. ABSTRACT Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. -

Pipenightdreams Osgcal-Doc Mumudvb Mpg123-Alsa Tbb
pipenightdreams osgcal-doc mumudvb mpg123-alsa tbb-examples libgammu4-dbg gcc-4.1-doc snort-rules-default davical cutmp3 libevolution5.0-cil aspell-am python-gobject-doc openoffice.org-l10n-mn libc6-xen xserver-xorg trophy-data t38modem pioneers-console libnb-platform10-java libgtkglext1-ruby libboost-wave1.39-dev drgenius bfbtester libchromexvmcpro1 isdnutils-xtools ubuntuone-client openoffice.org2-math openoffice.org-l10n-lt lsb-cxx-ia32 kdeartwork-emoticons-kde4 wmpuzzle trafshow python-plplot lx-gdb link-monitor-applet libscm-dev liblog-agent-logger-perl libccrtp-doc libclass-throwable-perl kde-i18n-csb jack-jconv hamradio-menus coinor-libvol-doc msx-emulator bitbake nabi language-pack-gnome-zh libpaperg popularity-contest xracer-tools xfont-nexus opendrim-lmp-baseserver libvorbisfile-ruby liblinebreak-doc libgfcui-2.0-0c2a-dbg libblacs-mpi-dev dict-freedict-spa-eng blender-ogrexml aspell-da x11-apps openoffice.org-l10n-lv openoffice.org-l10n-nl pnmtopng libodbcinstq1 libhsqldb-java-doc libmono-addins-gui0.2-cil sg3-utils linux-backports-modules-alsa-2.6.31-19-generic yorick-yeti-gsl python-pymssql plasma-widget-cpuload mcpp gpsim-lcd cl-csv libhtml-clean-perl asterisk-dbg apt-dater-dbg libgnome-mag1-dev language-pack-gnome-yo python-crypto svn-autoreleasedeb sugar-terminal-activity mii-diag maria-doc libplexus-component-api-java-doc libhugs-hgl-bundled libchipcard-libgwenhywfar47-plugins libghc6-random-dev freefem3d ezmlm cakephp-scripts aspell-ar ara-byte not+sparc openoffice.org-l10n-nn linux-backports-modules-karmic-generic-pae -

Integral Estimation in Quantum Physics
INTEGRAL ESTIMATION IN QUANTUM PHYSICS by Jane Doe A dissertation submitted to the faculty of The University of Utah in partial fulfillment of the requirements for the degree of Doctor of Philosophy in Mathematical Physics Department of Mathematics The University of Utah May 2016 Copyright c Jane Doe 2016 All Rights Reserved The University of Utah Graduate School STATEMENT OF DISSERTATION APPROVAL The dissertation of Jane Doe has been approved by the following supervisory committee members: Cornelius L´anczos , Chair(s) 17 Feb 2016 Date Approved Hans Bethe , Member 17 Feb 2016 Date Approved Niels Bohr , Member 17 Feb 2016 Date Approved Max Born , Member 17 Feb 2016 Date Approved Paul A. M. Dirac , Member 17 Feb 2016 Date Approved by Petrus Marcus Aurelius Featherstone-Hough , Chair/Dean of the Department/College/School of Mathematics and by Alice B. Toklas , Dean of The Graduate School. ABSTRACT Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. Blah blah blah blah blah blah blah blah blah blah blah blah blah blah blah. -

Email-Verschlüsselung Mit Gnu Privacy Guard
Email‐Verschlüsselung mit Gnu Privacy Guard Inhaltsverzeichnis Email‐Verschlüsselung mit Gnu Privacy Guard ........................................................................ 1 Kryptographie ......................................................................................................................... 2 Geschichte der Kryptographie ................................................................................................. 3 Gnu Privacy Guard ( GnuPG) ................................................................................................... 5 Installation .............................................................................................................................. 7 Schlüsselpaar .......................................................................................................................... 8 Schlüssel auflisten ................................................................................................................ 8 “Fingerprint” anzeigen ......................................................................................................... 8 Schlüsselpaar erzeugen ....................................................................................................... 9 Schlüssel importieren ........................................................................................................ 11 Schlüssel exportieren ......................................................................................................... 11 Schlüssel signieren ............................................................................................................ -

Gnupg Características Cuestiones Legales
GnuPg Características GnuPG en sí mismo es una utilidad de línea de comandos sin ninguna característica gráfica. Se trata del motor de cifrado, en sí mismo, que puede ser utilizado directamente desde la línea de comandos, desde programas (guiones) de shell (shell scripts) o por otros programas. Por lo tanto GnuPG puede ser considerado como un motor (backend) para otras aplicaciones. De todos modos, incluso si se utiliza desde la línea de comandos, proporciona toda la funcionalidad necesaria, lo que incluye un sistema interactivo de menús. El conjunto de órdenes de esta herramienta siempre será un superconjunto del que proporcione cualquier interfaz de usuario (frontend). • Reemplazo completo de PGP. • No utiliza algoritmos patentados. • Con licencia GPL, escrito desde cero. • Puede utilizarse como filtro. • Implementación completa de OpenPGP (vea RFC 2440 en RFC Editor ). • Funcionalidad mejorada con respecto a PGP y mejoras de seguridad con respecto a PGP 2. • Descifra y verifica mensajes de PGP 5, 6 y 7. • Soporta ElGamal, DSA, RSA, AES, 3DES, Blowfish, Twofish, CAST5, MD5, SHA-1, RIPE-MD-160 y TIGER. • Facilidad de implementación de nuevos algoritmos utilizando módulos. • Fuerza que el identificador de usuario (User ID) esté en un formato estándar. • Soporta fechas de caducidad de claves y firmas. • Soporta inglés, danés, holandés, esperanto, estonio, francés, alemán, japonés, italiano, polaco, portugués (brasileño), portugués (de Portugal), ruso, español, sueco y turco. • Sistema de ayuda en línea. • Receptores de mensajes anónimos, opcionalmente. • Soporte integrado para servidores de claves HKP (wwwkeys.pgp.net). • Limpia ficheros firmados con "firma en claro", que pueden ser procesados en lotes. • y muchas cosas más.. -
Gnupg: Open Encryption, Signing and Authentication
GnuPG: Open Encryption, Signing and Authentication David Tomaschik, RHCE, LPIC-1 <[email protected]> http://systemoverlord.com What is GnuPG? GnuPG is the GNU project's complete and free implementation of the OpenPGP standard as defined by RFC4880 . GnuPG allows to encrypt and sign your data and communication, features a versatile key management system as well as access modules for all kinds of public key directories. GnuPG, also known as GPG, is a command line tool with features for easy integration with other applications. A wealth of frontend applications and libraries are available. Version 2 of GnuPG also provides support for S/MIME. OK. What is GnuPG? Implementation of public-key cryptography Conforms to an open standard (OpenPGP) Allows for: Encryption of Data & Communication Signing of Data & Communication Authentication About this presentation Not a ”cookbook” for GPG Overview of what you can do Some technical points simplified GPG has excellent man pages and documentation Outline Background Best Practices Terminology Threat Modeling Motivations Key Separation General Theory Integration & UIs Getting Started UIs Key Generation E-mail Choices Advanced Topics Key Signing Smart Cards Authentication Terminology PGP – Pretty Good Privacy Original implementation, 1991, by Phil Zimmerman Source Available until 2000 OpenPGP – Standard for implementations RFC 4880 (Replaced RFC 2440) (Message format) RFC 3156 (e-mail format, PGP/MIME) GnuPG – GNU-Project, GPL Implementation Mostly PGP Compatible Implements all of RFC 4880 Motivations: Encryption Protect messages against being read except by intended recipient(s). Intended recipient could be yourself. Can exchange secret communications without needing any pre-shared secrets. Motivations: Signing Digital signatures prove that you wrote/signed a given chunk of data. -

Mailfromd Mail Filter Version 8.12, 23 July 2021
Mailfromd mail filter version 8.12, 23 July 2021 Sergey Poznyakoff. Published by the Free Software Foundation, 51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA Copyright c 2005–2021 Sergey Poznyakoff Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.3 or any later version published by the Free Software Foundation; with no Invariant Sections, no Front-Cover Texts, and no Back-Cover Texts. A copy of the license is included in the section entitled “GNU Free Documentation License”. Dedico aquest treball a Lluis Llach, per obrir els nous horitzons. i Short Contents Preface ................................................. 1 1 Introduction to mailfromd.............................. 5 2 Building the Package .................................. 9 3 Tutorial ............................................ 13 4 Mail Filtering Language ............................... 51 5 The MFL Library Functions .......................... 111 6 Using the GNU Emacs MFL Mode ..................... 195 7 Configuring mailfromd ............................... 199 8 Mailfromd Command Line Syntax ..................... 209 9 Using mailfromd with Various MTAs ................... 217 10 calloutd .......................................... 223 11 mfdbtool .......................................... 231 12 mtasim — a testing tool .............................. 233 13 Pmilter multiplexer program. .......................... 243 14 How to Report a Bug ................................ 251 A -

GNU Anubis an SMTP Message Submission Daemon
GNU Anubis An SMTP message submission daemon. GNU Anubis Version 4.2.90 6 June 2020 Wojciech Polak and Sergey Poznyakoff Copyright c 2001, 2002, 2003, 2004, 2007, 2008, 2009, 2011, 2014 Wojciech Polak and Sergey Poznyakoff. Permission is granted to copy, distribute and/or modify this document un- der the terms of the GNU Free Documentation License, Version 1.2 or any later version published by the Free Software Foundation; with no Invariant Sections, with the Front-Cover texts being “A GNU Manual”, and with the Back-Cover Texts as in (a) below. A copy of the license is included in the section entitled “GNU Free Documentation License”. (a) The FSF’s Back-Cover Text is: “You have freedom to copy and modify this GNU Manual, like GNU software. Copies published by the Free Software Foundation raise funds for GNU development.” i Short Contents 1 Overview ............................................ 1 2 Glossary of Frequently Used Terms ....................... 3 3 Authentication ....................................... 5 4 Configuration ....................................... 15 5 The Rule System .................................... 27 6 Invoking GNU Anubis ................................ 45 7 Quick Start ......................................... 47 8 Using the TLS/SSL Encryption ......................... 49 9 Using S/MIME Signatures ............................. 51 10 Using Anubis to Process Incoming Mail .................. 53 11 Using Mutt with Anubis............................... 55 12 Reporting Bugs ..................................... -

Abstract GEGICK, MICHAEL CHARLES. Analyzing Security
Abstract GEGICK, MICHAEL CHARLES. Analyzing Security Attacks to Generate Signatures from Vulnerable Architectural Patterns. (Under the direction of Dr. Laurie Williams.) Current techniques for software security vulnerability identification include the use of abstract, graph-based models to represent information about an attack. These models can be in the form of attack trees or attack nets and can be accompanied with a supporting text- based profile. Matching the abstract models to specific system architectures for effective vulnerability identification can be a challenging process. This thesis suggests that abstract regular expressions can be used to represent events of known attacks for the identification of security vulnerabilities in future applications. The process of matching the events in the regular expression to a sequence of components in a system design may facilitate the means of identifying vulnerabilities. Performing the approach in the design phase of a software process encourages security to be integrated early into a software application. Students in an undergraduate security course demonstrated a strong ability to accurately match regular expressions to a system design. The identification of vulnerabilities is limited to known attacks of other systems and does not offer descriptions of what new attacks are possible to a future application. Extending the approach to incorporate new attacks is an avenue of future work. Analyzing Security Attacks to Generate Signatures from Vulnerable Architectural Patterns by Michael Charles -

Unix Et Programmation Shell
Unix et Programmation Shell Philippe Langevin d´epartment d'informatique UFR sciences et technique universit´edu sud Toulon Var Automne 2013 Philippe Langevin (imath/ustv) Unix et Programmation Shell Automne 2013 1 / 33 document brouillon en r´evision site du cours : http://langevin.univ-tln.fr/cours/UPS/upsh.html localisation du fichier : http://langevin.univ-tln.fr/cours/UPS/doc/intro.pdf Philippe Langevin (imath/ustv) Unix et Programmation Shell Automne 2013 2 / 33 derni`eresmodifications intro.tex 2013-06-23 10:07:23.697660496 +0200 macros.tex 2013-06-22 23:42:16.868263946 +0200 prologue.tex 2013-06-22 22:10:45.967471216 +0200 upsh.tex 2013-06-22 11:24:27.941744751 +0200 tools.tex 2013-06-22 11:24:27.940741957 +0200 term.tex 2013-06-22 11:24:27.934741399 +0200 syntaxe.tex 2013-06-22 11:24:27.931741678 +0200 proc.tex 2013-06-22 11:24:27.927741678 +0200 piped.tex 2013-06-22 11:24:27.922741399 +0200 perm.tex 2013-06-22 11:24:27.921741678 +0200 part.tex 2013-06-22 11:24:27.918742237 +0200 man.tex 2013-06-22 11:24:27.911741957 +0200 langage.tex 2013-06-23 10:04:58.364659987 +0200 file.tex 2013-06-22 11:24:27.896741119 +0200 dup.tex 2013-06-22 11:24:27.885741678 +0200 fic.tex 2013-06-22 11:24:27.885741678 +0200 bash.tex 2013-06-22 11:24:27.881741957 +0200 Philippe Langevin (imath/ustv) Unix et Programmation Shell Automne 2013 3 / 33 shell unix 1 - shell unix origine unices GNU/linux distribution shell unix GUI vs CLI exemple Philippe Langevin (imath/ustv) Unix et Programmation Shell Automne 2013 4 / 33 1969 Ken Thompson cr´eele syst`eme UNICS 1971 Dennis Ritchie cr´ee Le langage C utile pour le d´eveloppement d'unix. -
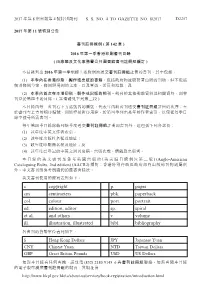
2017 年第8 期憲報第4 號特別副刊ss No. 4 to Gazette No. 8/2017
2017 年第 8 期憲報第 4 號特別副刊 S. S. NO. 4 TO GAZETTE NO. 8/2017 D2257 2017 年第 11 號特別公告 書刊註冊條例 ( 第 142 章 ) 2016 年第一季香港印刷書刊目錄 ( 由康樂及文化事務署公共圖書館書刊註冊組編訂 ) 本目錄列出 2016 年第一季根據上述條例而送交書刊註冊組註冊的書刊。其中包括: (1) 本季內在香港印刷、製作或出版的書籍,包括政府物流服務署出版的刊物,但不包括 個別條例草案、條例與規例的文本,以及單張、活頁和海報;及 (2) 本季內首次在本港印刷、製作或出版的期刊。期刊的其他期數資料及相關資料,則會 刊登於第四季的目錄。( 詳情請見下列第三段 ) 本目錄內每一書刊右下方括號內的編號,代表年內該書刊送交書刊註冊組註冊的次序;至 於書刊左上方的順序編號,則純粹是排序用途,於第四季列出是年的作者索引,以便從每季目 錄中搜尋所需書刊。 每年第四季目錄除載列該季度送交書刊註冊組註冊的書刊外,還包括下列各部份: (1) 該年度中英文作者索引; (2) 該年度出版社名稱及地址; (3) 該年度印刷商名稱及地址;及 (4) 該年度已登記的中英文期刊名稱、出版次數、價錢及出版者。 本目錄的英文書刊是參考英國出版的《英美編目條例》( 第二版) (Anglo-American Cataloguing Rules, 2nd edition) (AACR2) 編訂;香港特別行政區政府部門出版的刊物則屬例 外。中文書刊則參考劉國鈞的圖書著錄法。 英文書刊使用的簡寫表列如下: c copyright p. pages cm centimeters pbk. paperback col. colour port. portrait ed. edition, editor sp. spiral et al. and others v volume ill. illustration, illustrated bibl. bibliography 各書刊的貨幣單位表列如下: $ Hong Kong Dollars JPY Japanese Yuan CNY Chinese Yuan NTD Taiwan Dollars GBP Great Britain Pounds USD US Dollars 如對本目錄有任何查詢,請致電 (852) 2180 9145–6 與書刊註冊組聯絡。如需查閱本目錄 的電子版可瀏覽書刊註冊組的網頁,其網址為 http://www.hkpl.gov.hk/tc/about-us/services/book-registration/introduction.html 2017 年第 8 期憲報第 4 號特別副刊 S. S. NO. 4 TO GAZETTE NO. 8/2017 D2259 ENGLISH BOOKS AND PERIODICALS 5 ABERDEEN KAI-FONG WELFARE 1 ASSOCIATION SOCIAL SERVICE 1ST international conference on geo-energy & Aberdeen Kai-fong Welfare Association geo-environment : 4-5th December 2015 / Social Service annual report 2014-2015 = 香 edited by Charles W.W. Ng ... [et al.]. — 港仔坊會社會服務年報2014-2015. — Hong Hong Kong : Hong Kong University of Kong : Aberdeen Kai-fong Welfare Science and Technology. Publishing Association Social Service, 2015. — 60 p. : Technology Center, 2015. — ix, 193 p. : ill. col. ill., col. chart ; 30 cm. (some col.), charts ; 30 cm. Text in Chinese and English Includes bibliographical references Unpriced (pbk.) ISBN 978-988-14032-2-3 (pbk.) : Unpriced (2016-00700) (2016-02889) 6 2 ACTIVE physics for HKDSE. -

Unix Et Programmation Shell
Unix et Programmation Shell Philippe Langevin d´epartment d'informatique UFR sciences et technique universit´edu sud Toulon Var Automne 2013 Philippe Langevin (imath/ustv) Unix et Programmation Shell Automne 2013 1 / 50 document brouillon en r´evision site du cours : http://langevin.univ-tln.fr/cours/UPS/upsh.html localisation du fichier : http://langevin.univ-tln.fr/cours/UPS/doc/shell.pdf Philippe Langevin (imath/ustv) Unix et Programmation Shell Automne 2013 2 / 50 derni`eresmodifications man.tex 2017−09−07 12:27:47.738251920 +0200 perm.tex 2016−09−30 09:41:54.766553521 +0200 file .tex 2016−09−30 09:19:02.810595120 +0200 bash.tex 2016−09−15 12:09:09.887948313 +0200 term.tex 2016−09−14 18:50:05.124091515 +0200 upsh.tex 2015−10−25 18:09:36.027434338 +0100 proc.tex 2015−10−20 22:09:35.450391618 +0200 shell.tex 2015−09−10 19:31:04.581529236 +0200 prologue.tex 2015−09−07 09:06:31.773157847 +0200 tools.tex 2015−07−11 09:04:38.890915266 +0200 pipe.tex 2014−10−02 19:10:22.426127326 +0200 direct.tex 2014−10−02 07:49:17.162784238 +0200 syntaxe.tex 2014−10−01 23:52:29.859357485 +0200 part.tex 2014−10−01 23:52:29.372363438 +0200 Philippe Langevin (imath/ustv) Unix et Programmation Shell Automne 2013 3 / 50 shell unix 1 - shell unix origine unices GNU/linux distribution shell unix GUI vs CLI C-production Philippe Langevin (imath/ustv) Unix et Programmation Shell Automne 2013 4 / 50 1969 Ken Thompson cr´eele syst`eme UNICS 1971 Dennis Ritchie cr´eele langage C [PSLC] prog.