Evolving Patterns of Human Interactions
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uila Supported Apps
Uila Supported Applications and Protocols updated Oct 2020 Application/Protocol Name Full Description 01net.com 01net website, a French high-tech news site. 050 plus is a Japanese embedded smartphone application dedicated to 050 plus audio-conferencing. 0zz0.com 0zz0 is an online solution to store, send and share files 10050.net China Railcom group web portal. This protocol plug-in classifies the http traffic to the host 10086.cn. It also 10086.cn classifies the ssl traffic to the Common Name 10086.cn. 104.com Web site dedicated to job research. 1111.com.tw Website dedicated to job research in Taiwan. 114la.com Chinese web portal operated by YLMF Computer Technology Co. Chinese cloud storing system of the 115 website. It is operated by YLMF 115.com Computer Technology Co. 118114.cn Chinese booking and reservation portal. 11st.co.kr Korean shopping website 11st. It is operated by SK Planet Co. 1337x.org Bittorrent tracker search engine 139mail 139mail is a chinese webmail powered by China Mobile. 15min.lt Lithuanian news portal Chinese web portal 163. It is operated by NetEase, a company which 163.com pioneered the development of Internet in China. 17173.com Website distributing Chinese games. 17u.com Chinese online travel booking website. 20 minutes is a free, daily newspaper available in France, Spain and 20minutes Switzerland. This plugin classifies websites. 24h.com.vn Vietnamese news portal 24ora.com Aruban news portal 24sata.hr Croatian news portal 24SevenOffice 24SevenOffice is a web-based Enterprise resource planning (ERP) systems. 24ur.com Slovenian news portal 2ch.net Japanese adult videos web site 2Shared 2shared is an online space for sharing and storage. -

Metadefender Core V4.12.2
MetaDefender Core v4.12.2 © 2018 OPSWAT, Inc. All rights reserved. OPSWAT®, MetadefenderTM and the OPSWAT logo are trademarks of OPSWAT, Inc. All other trademarks, trade names, service marks, service names, and images mentioned and/or used herein belong to their respective owners. Table of Contents About This Guide 13 Key Features of Metadefender Core 14 1. Quick Start with Metadefender Core 15 1.1. Installation 15 Operating system invariant initial steps 15 Basic setup 16 1.1.1. Configuration wizard 16 1.2. License Activation 21 1.3. Scan Files with Metadefender Core 21 2. Installing or Upgrading Metadefender Core 22 2.1. Recommended System Requirements 22 System Requirements For Server 22 Browser Requirements for the Metadefender Core Management Console 24 2.2. Installing Metadefender 25 Installation 25 Installation notes 25 2.2.1. Installing Metadefender Core using command line 26 2.2.2. Installing Metadefender Core using the Install Wizard 27 2.3. Upgrading MetaDefender Core 27 Upgrading from MetaDefender Core 3.x 27 Upgrading from MetaDefender Core 4.x 28 2.4. Metadefender Core Licensing 28 2.4.1. Activating Metadefender Licenses 28 2.4.2. Checking Your Metadefender Core License 35 2.5. Performance and Load Estimation 36 What to know before reading the results: Some factors that affect performance 36 How test results are calculated 37 Test Reports 37 Performance Report - Multi-Scanning On Linux 37 Performance Report - Multi-Scanning On Windows 41 2.6. Special installation options 46 Use RAMDISK for the tempdirectory 46 3. Configuring Metadefender Core 50 3.1. Management Console 50 3.2. -

List of NMAP Scripts Use with the Nmap –Script Option
List of NMAP Scripts Use with the nmap –script option Retrieves information from a listening acarsd daemon. Acarsd decodes ACARS (Aircraft Communication Addressing and Reporting System) data in real time. The information retrieved acarsd-info by this script includes the daemon version, API version, administrator e-mail address and listening frequency. Shows extra information about IPv6 addresses, such as address-info embedded MAC or IPv4 addresses when available. Performs password guessing against Apple Filing Protocol afp-brute (AFP). Attempts to get useful information about files from AFP afp-ls volumes. The output is intended to resemble the output of ls. Detects the Mac OS X AFP directory traversal vulnerability, afp-path-vuln CVE-2010-0533. Shows AFP server information. This information includes the server's hostname, IPv4 and IPv6 addresses, and hardware type afp-serverinfo (for example Macmini or MacBookPro). Shows AFP shares and ACLs. afp-showmount Retrieves the authentication scheme and realm of an AJP service ajp-auth (Apache JServ Protocol) that requires authentication. Performs brute force passwords auditing against the Apache JServ protocol. The Apache JServ Protocol is commonly used by ajp-brute web servers to communicate with back-end Java application server containers. Performs a HEAD or GET request against either the root directory or any optional directory of an Apache JServ Protocol ajp-headers server and returns the server response headers. Discovers which options are supported by the AJP (Apache JServ Protocol) server by sending an OPTIONS request and lists ajp-methods potentially risky methods. ajp-request Requests a URI over the Apache JServ Protocol and displays the result (or stores it in a file). -

Manuale Per L'utente
Vivavoce personale CHAT 50 MANUALE PER L’UTENTE SOMMARIO TEL +1.800.283.5936 +1.801.974.3760 FAX +1.801.977.0087 EMAIL [email protected] MANUALE PER L’UTENTE DEL CHAT 50 CLEARONE NUMERO PARTE 800-159-001. MARZO 2006 (REV 1.0) © 2005 ClearOne Communications, inc. Tutti i diritti riservati. È vietata la riproduzione di qualsiasi parte di questo documento in qualunque formato e con qualunque mezzo senza autorizzazione scritta da parte di ClearOne Communications. Stampato negli Stati Uniti. ClearOne si riserva specifici privilegi. Le informazioni contenute in questo documento sono soggette a modifiche senza preavviso. SOMMARIO CONTINUA CAPITOLO 1: INTRODUZIONE Presentazione del prodotto . 1 Servizio e Assistenza . 1 Informazioni importanti sulla sicurezza . 2 Apertura della confezione . 3 CAPITOLO 2: PER INIZIARE Installazione del software del Chat 50. 5 Configurazione e prova del Chat 50 . 10 Come collegare il Chat 50 . 14 Come collegare il Chat 50 con un telefono . 14 Come collegare il Chat 50 con un telefono cellulare . 15 Come collegare il Chat 50 con un riproduttore MP3 . 16 Come collegare il Chat 50 con un sistema per videoconferenze . 17 CAPITOLO 3: USO DEL SOFTWARE DI CONFIGURAZIONE DEL CHAT 50 Device Setup . 19 My Devices. 20 Update Firmware . 21 Help . 24 Advanced . 24 Advanced Settings: Audio Settings . 25 Advanced Settings: Database . 26 Advanced Settings: Log . 28 CAPITOLO 4: USO DI CHAT 50 Indicatore LED di alimentazione . 29 Tasti volume su/giù e Mute . 29 CAPITOLO 5: MANUTENZIONE Come prendersi cura del Chat 50 . 31 Risoluzione dei problemi . 31 Ripristino in caso di aggiornamento firmware interrotto. -

Hyperx Cloud Pro Gaming Headset
HyperX Cloud Pro Gaming Headset hyperxgaming.com Comfortable headset with in-line audio control for serious console gamers. HyperX Cloud™ is designed to meet the demands of serious console gamers. Cloud in silver has convenient in-line audio control that saves you from navigating through system menus and puts control at your ngertips. The durable aluminum frame is designed for long-lasting reliability and to withstand the damage of daily gaming. The 100% memory foam ear cushions and leatherette-padded headband provide award-winning comfort for those long weekends and late nights of gaming. HiFi capable 53mm drivers and enhanced bass reproduction pump out crystal clear high, mids and lows, and the closed cup design silences the outside world to completely immerse you in your game. Cloud’s microphone can be adjusted the way you like it, and it eliminates background noise so you come across loud and clear. When you’re ready to listen to music, simply unplug the microphone and stow it for later. HyperX Cloud has been certi ed by TeamSpeak™ and Discord and is compatible with Skype™, Ventrilo, Mumble, RaidCall and many more chat applications. During HyperX Cloud testing, no audible echoes, background noise or voice distortions were detected, so you and your team will be able to communicate clearly. HyperX Cloud’s 3.5mm plug (4 pole) is compatible with PS4™, Xbox One™, Wii U™, Mac® and mobile devices, and it comes with a 2M extension cable with stereo and mic plugs for PC use. > In-line audio volume control and microphone mute > Durable aluminum -

Hyperx Cloud Revolver S
HyperX Cloud Revolver S hyperxgaming.com/headsets Premium-grade headset featuring virtual Dolby Surround 7.1 audio with Push-to-Dolby convenience. HyperX Cloud Revolver™ S is primed for action with Plug N Play virtual Dolby® Surround 7.1 audio – no software required. Hear every footstep, explosion and gunshot with cinematic clarity as the simulated seven positional speakers provide precise sound with distance and depth. The advanced USB digital signal processing sound card handles everything, delivering consistent premium-quality sound, no matter what system you’re playing on. Backlit buttons on the clippable audio control box allow you to quickly activate Dolby audio, mute and regulate mic and output levels. New bass boost, flat and vocal equaliser modes let you swap between setups tuned for games, streaming, music or movies. Revolver S has a studio-grade sound stage that excels in FPS and open-environment settings, letting you hear sounds further away more accurately. The unique Revolver S driver design separates the lows, mids and highs, and the re-engineered profiles produce sounds that audiophiles will rave about. Serious gamers and streamers will love the higher- quality, dense HyperX signature memory foam and the new wider headband that reduces head pressure and more evenly distributes weight. The German-designed Cloud Revolver S has a solid-steel frame for long-lasting durability and stability and is built to deliver sonic perfection for years. HyperX Cloud Revolver S features next-gen 50mm directional drivers aligned parallel to the ears for precise audio output. Closed ear cups block out outside noise to fully immerse you in Cloud’s signature crisp, clear sound quality and enhanced bass. -

Firmware Analysis of Linksys E900 V. 1.0.09.002
Firmware Analysis of Linksys E900 v. 1.0.09.002 HID Linksys E900 v. 1.0.09.002 Device Name E900 Vendor Linksys Device Class Routers Version 1.0.09.002 Release Date 1970-01-01 Size 7.39 MiB (7,746,560 Byte) Unpacker (v. 0.7) Plugin generic carver Extracted 2 Output: DECIMAL HEXADECIMAL DESCRIPTION ——————————————————————————– 0 0x0 BIN-Header, board ID: E900, hardware version: 4702, firmware v ersion: 1.0.0, build date: 2018-08-08 32 0x20 TRX firmware header, little endian, image size: 7745536 bytes, CRC32: 0x756770AD, flags: 0x0, version: 1, header size: 28 bytes, loader offset: 0x1C, linux kernel offset: 0x14FDFC, rootfs offset: 0x0 60 0x3C gzip compressed data, maximum compression, has original file n ame: ”piggy”, from Unix, last modified: 2018-08-08 05:28:28 1375772 0x14FE1C Squashfs filesystem, little endian, non-standard signature, ve rsion 3.0, size: 6365444 bytes, 1718 inodes, blocksize: 65536 bytes, created: 2018-08-08 05:33:15 Entropy 0.89 1 File Type (v. 1.0) File Type data MIME application/octet-stream Containing Files application/CDFV2 (2) application/gzip (1) application/octet-stream (3) application/x-executable (67) application/x-object (27) application/x-sharedlib (116) filesystem/squashfs (1) image/gif (42) image/jpeg (8) image/png (17) image/x-icon (1) inode/symlink (7) text/plain (990) 2 Binwalk (v. 0.5.2) Signature Analysis: DECIMAL HEXADECIMAL DESCRIPTION ——————————————————————————– 0 0x0 BIN-Header, board ID: E900, hardware version: 4702, firmware version: 1.0.0, build date: 2018-08-08 32 0x20 TRX firmware header, little endian, -

Assets Portfolio
Assets Portfolio October 6, 2014 CONFIDENTIAL Assets Portfolio Contents 1 Foreword 7 1.1 Document Formatting.................................... 7 1.2 Properties and Definitions.................................. 7 1.2.1 Vulnerability Properties............................ 7 1.2.2 Vulnerability Test Matrix........................... 9 1.2.3 Asset Deliverables............................... 9 1.2.4 Exploit Properties............................... 10 2 Adobe Systems Incorporated 13 2.1 Adobe Reader........................................ 13 14-004 Adobe Reader Client-side Remote Code Execution............. 13 2.2 Flash Player......................................... 15 12-033 Adobe Flash Player Client-side Remote Code Execution........... 15 2.3 Photoshop CS6....................................... 17 13-011 Adobe Photoshop CS6 Client-side Remote Code Execution......... 18 3 Apple, Inc. 20 3.1 Mac OS X.......................................... 20 14-010 Apple Mac OS X Local Privileged Command Execution........... 20 4 ASUS 22 4.1 BIOS Device Driver..................................... 22 13-015 ASUS BIOS Device Driver Local Privilege Escalation............ 23 October 6, 2014 CONFIDENTIAL Page 1 of 134 Assets Portfolio 5 AVAST Software a.s. 25 5.1 avast! Anti-Virus...................................... 25 13-005 avast! Local Information Disclosure..................... 25 13-010 avast! Anti-Virus Local Privilege Escalation................. 27 6 Barracuda Networks, Inc. 29 6.1 Web Filter.......................................... 29 13-000 Barracuda -

Download Mumble Client
Download mumble client Mumble is an open source, low-latency, high quality voice chat software primarily intended for use while gaming. You can download for free! The Mumble Client Download Mumble Free · Mumble Server Trial · Windows Manually. Download Mumble for free. Download mumblemsi Mumble setup on Windows 7 Mumble on Windows 7 Mumble Mumble is an open source, low-latency, high quality voice chat software primarily intended for use while gaming. Download Mumble If you are looking for a client for an operating system we do not officially support ourselves, or if you are. Download the Mumble client for free. Mumble is available for the PC, Mac and Linux. Mumble is a voice chat application for groups. It has low latency and superb voice quality, and features an in-game overlay. While it can be used for any kind. A description for this result is not available because of this site's Mumble VoIP Client/Server Clone or download . On Mac OS X, to install Mumble, drag the application from the downloaded disk. There are two modules in the Mumble package: the client (Mumble) and the server (Murmur). The superior audio quality comes in large parts from Speex, a high. Mumble is a free and open source audio chat software that has a goal to offer everyone ability to chat in a group environment. This includes. Mumble ist ein Open-Source-Client für Voice-Chat, der sich nicht nur schonend auf die für Onlinespiele so wichtige Latenz der Verbindung auswirkt, sondern mit. Mumble Deutsch: Mit der kostenlosen Telefon-Software Mumble Download . -
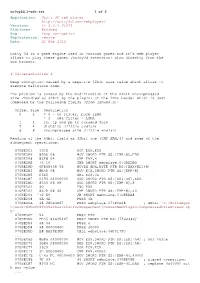
Application: Unity 3D Web Player
unity3d_1-adv.txt 1 of 2 Application: Unity 3D web player http://unity3d.com/webplayer/ Versions: <= 3.2.0.61061 Platforms: Windows Bug: heap corruption Exploitation: remote Date: 21 Feb 2012 Unity 3d is a game engine used in various games and it’s web player allows to play these games (unity3d extension) also directly from the web browser. # Vulnerabilities # Heap corruption caused by a negative 32bit size value which allows to execute malicious code. The problem is caused by the modification of the 64bit uncompressed size (handled as 32bit by the plugin) of the lzma header which is just composed by the following fields (from lzma86.h): Offset Size Description 0 1 = 0 - no filter, pure LZMA = 1 - x86 filter + LZMA 1 1 lc, lp and pb in encoded form 2 4 dictSize (little endian) 6 8 uncompressed size (little endian) Reading of the 64bit field as 32bit one (CMP EAX,4) and some of the subsequent operations: 070BEDA3 33C0 XOR EAX,EAX 070BEDA5 895D 08 MOV DWORD PTR SS:[EBP+8],EBX 070BEDA8 83F8 04 CMP EAX,4 070BEDAB 73 10 JNB SHORT webplaye.070BEDBD 070BEDAD 0FB65438 05 MOVZX EDX,BYTE PTR DS:[EAX+EDI+5] 070BEDB2 8B4D 08 MOV ECX,DWORD PTR SS:[EBP+8] 070BEDB5 D3E2 SHL EDX,CL 070BEDB7 0196 A4000000 ADD DWORD PTR DS:[ESI+A4],EDX 070BEDBD 8345 08 08 ADD DWORD PTR SS:[EBP+8],8 070BEDC1 40 INC EAX 070BEDC2 837D 08 40 CMP DWORD PTR SS:[EBP+8],40 070BEDC6 ^72 E0 JB SHORT webplaye.070BEDA8 070BEDC8 6A 4A PUSH 4A 070BEDCA 68 280A4B07 PUSH webplaye.074B0A28 ; ASCII "C:/BuildAgen t/work/b0bcff80449a48aa/PlatformDependent/CommonWebPlugin/CompressedFileStream.cp p" 070BEDCF 53 PUSH EBX 070BEDD0 FF35 84635407 PUSH DWORD PTR DS:[7546384] 070BEDD6 6A 04 PUSH 4 070BEDD8 68 00000400 PUSH 40000 070BEDDD E8 BA29E4FF CALL webplaye.06F0179C .. -

Discord Through Discord, Unity?
Discord Through Discord, Unity? If you have a gamer in your family, you’ve probably heard of Discord, the increasingly preferred method of chat for gaming communities. In fact, the platform has become so popular in the last year or so that many have focked to it for all kinds of communication around every imaginable subject. And while Discord solves many problems and even makes communication easier and more fun, it brings to the table interesting problems—some seen throughout the internet and some entirely unique. Not only do we need to know about these issues to protect our kids, but also to utilize them in our eforts to disciple our kids into wise, Christ-like, loving citizens of our increasingly virtual world. What is Discord? An “all-in-one voice and text chat for gamers that’s free, secure, and works on both your desktop and phone,” according to its website. Basically, it’s a way to chat specifcally with other gamers about, well, video games (though it’s not limited to that). According to their description on the iOS app store: Discord is the only cross-platform voice and text chat app designed specifcally for gamers. With the iOS app you can stay connected to all your Discord voice and text channels even while AFK [away from keyboard, a common PC gaming slang term]. It is perfect for chatting with team members, seeing who is playing online, and catching up on text conversations you may have missed. The app works on iPhone, iPad, Android, Mac, and PC (on the last two via browser or desktop app) and therefore can be used in tandem with all sorts of video games, including mobile games. -

Manual Do Usuário Índice
Telefone pessoal viva voz CHAT 50 MANUAL DO USUÁRIO ÍNDICE TELEFONE +1.800.283.5936 +1.801.974.3760 FAX +1.801.977.0087 EMAIL [email protected] MANUAL DO USUÁRIO DO CHAT 50 CLEARONE PART NO. 800-159-001. MARÇO DE 2006 (REV. 1.0) © 2005 ClearOne Communications, inc. Todos os direitos reservados. Nenhuma parte deste documento pode ser reproduzida, de qualquer forma ou por qualquer meio, sem a permissão por escrito da ClearOne Communications. Impresso nos Estados Unidos da América. A ClearOne Communications reserve-se privilégios específicos as informações contidas neste documento estão sujeitas à alteração sem aviso prévio. ÍNDICE CONTINUAÇÃO CAPÍTULO 1: INTRODUÇÃO Visão geral do produto . 1 Serviço e suporte . 1 Informações importantes sobre segurança . 2 Desembalagem . 3 CAPÍTULO 2: PREPARAÇÃO PARA USO Instalação do software do Chat 50 . 5 Configuração e teste do Chat 50 . 10 Conexão ao Chat 50 . 14 Conexão do Chat 50 a um telefone . 14 Conexão do Chat 50 a um telefone celular . 15 Conexão Chat 50 A UM Reprodutor MP3 . 16 Conexão do Chat 50 a um dispositivo de mesa para conferência com vídeo . 17 CAPÍTULO 3: UTILIZAÇÃO DO SOFTWARE DE CONFIGURAÇÃO DO CHAT 50 Device Setup . 19 My Devices. 20 Update Firmware . 21 Help . 24 Advanced . 24 Advanced Settings: Audio Settings . 25 Advanced Settings: Database . 26 Advanced Settings: Log . 28 CAPÍTULO 4: UTILIZAÇÃO DO CHAT 50 Indicador LED de alimentação . 29 Botões para aumentar/diminuir volume e o botão Mute . 29 CAPÍTULO 5: MANUTENÇÃO Cuidados com o Chat 50 . 31 Solução de problemas. 31 Recuperação de uma atualização de firmware interrompida .