Syncovery User Manual
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Easy Slackware
1 Создание легкой системы на базе Slackware I - Введение Slackware пользуется заслуженной популярностью как классический linux дистрибутив, и поговорка "кто знает Red Hat тот знает только Red Hat, кто знает Slackware тот знает linux" несмотря на явный снобизм поклонников "бога Патре га" все же имеет под собой основания. Одним из преимуществ Slackware является возможность простого создания на ее основе практически любой системы, в том числе быстрой и легкой десктопной, о чем далее и пойдет речь. Есть дис трибутивы, клоны Slackware, созданные именно с этой целью, типа Аbsolute, но все же лучше создавать систему под себя, с максимальным учетом именно своих потребностей, и Slackware пожалуй как никакой другой дистрибутив подходит именно для этой цели. Легкость и быстрота системы определяется выбором WM (DM) , набором программ и оптимизацией программ и системы в целом. Первое исключает KDE, Gnome, даже новые версии XFCЕ, остается разве что LXDE, но набор программ в нем совершенно не устраивает. Оптимизация наиболее часто используемых про грамм и нескольких базовых системных пакетов осуществляется их сборкой из сорцов компилятором, оптимизированным именно под Ваш комп, причем каж дая программа конфигурируется исходя из Ваших потребностей к ее возможно стям. Оптимизация системы в целом осуществляется ее настройкой согласно спе цифическим требованиям к десктопу. Такой подход был выбран по банальной причине, возиться с gentoo нет ни какого желания, комп все таки создан для того чтобы им пользоваться, а не для компиляции программ, в тоже время у каждого есть минимальный набор из не большого количества наиболее часто используемых программ, на которые стоит потратить некоторое, не такое уж большое, время, чтобы довести их до ума. Кро ме того, такой подход позволяет иметь самые свежие версии наиболее часто ис пользуемых программ. -

Forescout Counteract® Endpoint Support Compatibility Matrix Updated: October 2018
ForeScout CounterACT® Endpoint Support Compatibility Matrix Updated: October 2018 ForeScout CounterACT Endpoint Support Compatibility Matrix 2 Table of Contents About Endpoint Support Compatibility ......................................................... 3 Operating Systems ....................................................................................... 3 Microsoft Windows (32 & 64 BIT Versions) ...................................................... 3 MAC OS X / MACOS ...................................................................................... 5 Linux .......................................................................................................... 6 Web Browsers .............................................................................................. 8 Microsoft Windows Applications ...................................................................... 9 Antivirus ................................................................................................. 9 Peer-to-Peer .......................................................................................... 25 Instant Messaging .................................................................................. 31 Anti-Spyware ......................................................................................... 34 Personal Firewall .................................................................................... 36 Hard Drive Encryption ............................................................................. 38 Cloud Sync ........................................................................................... -

MSDN Magazine (ISSN 1528-4859) Is Published Monthly by 1105 Media, Inc., 9201 Oakdale Avenue, Infoworld Ste
Introducing There’s no better time to discover DevExpress. Visual Studio 11 beta is here and DevExpress tools are ready to run. DXv2 is the next generation of tools that will take your applications to a new level. Build stunning, touch enabled applications today. Download your free 30-day trial at www.DevExpress.com © 1998-2012 Developer Express Inc. ALL RIGHTS RESERVED. All trademarks or registered trademarks are property of their respective owners. Untitled-2 1 3/8/12 10:58 AM THE MICROSOFT JOURNAL FOR DEVELOPERS APRIL 2012 VOL 27 NO 4 Using CSS3 Media Queries to Build COLUMNS a More Responsive Web Brandon Satrom ....................................................................... 20 CUTTING EDGE Long Polling and SignalR A Code-Based Introduction to C++ AMP Dino Esposito, page 6 Daniel Moth ............................................................................ 28 DATA POINTS Let Power Users Create Their Introduction to Tiling in C++ AMP Own OData Feeds Daniel Moth ............................................................................ 40 Julie Lerman, page 14 Lowering the Barriers to Code Generation with T4 TEST RUN Peter Vogel .............................................................................. 48 Bacterial Foraging Optimization James McCaffrey, page 82 Integrating Windows Workfl ow Foundation CLIENT INSIGHT with the OpenXML SDK Using JsRender with JavaScript Rick Spiewak ............................................................................ 56 and HTML John Papa, page 86 Context-Aware Dialogue with Kinect -

Insight MFR By
Manufacturers, Publishers and Suppliers by Product Category 11/6/2017 10/100 Hubs & Switches ASCEND COMMUNICATIONS CIS SECURE COMPUTING INC DIGIUM GEAR HEAD 1 TRIPPLITE ASUS Cisco Press D‐LINK SYSTEMS GEFEN 1VISION SOFTWARE ATEN TECHNOLOGY CISCO SYSTEMS DUALCOMM TECHNOLOGY, INC. GEIST 3COM ATLAS SOUND CLEAR CUBE DYCONN GEOVISION INC. 4XEM CORP. ATLONA CLEARSOUNDS DYNEX PRODUCTS GIGAFAST 8E6 TECHNOLOGIES ATTO TECHNOLOGY CNET TECHNOLOGY EATON GIGAMON SYSTEMS LLC AAXEON TECHNOLOGIES LLC. AUDIOCODES, INC. CODE GREEN NETWORKS E‐CORPORATEGIFTS.COM, INC. GLOBAL MARKETING ACCELL AUDIOVOX CODI INC EDGECORE GOLDENRAM ACCELLION AVAYA COMMAND COMMUNICATIONS EDITSHARE LLC GREAT BAY SOFTWARE INC. ACER AMERICA AVENVIEW CORP COMMUNICATION DEVICES INC. EMC GRIFFIN TECHNOLOGY ACTI CORPORATION AVOCENT COMNET ENDACE USA H3C Technology ADAPTEC AVOCENT‐EMERSON COMPELLENT ENGENIUS HALL RESEARCH ADC KENTROX AVTECH CORPORATION COMPREHENSIVE CABLE ENTERASYS NETWORKS HAVIS SHIELD ADC TELECOMMUNICATIONS AXIOM MEMORY COMPU‐CALL, INC EPIPHAN SYSTEMS HAWKING TECHNOLOGY ADDERTECHNOLOGY AXIS COMMUNICATIONS COMPUTER LAB EQUINOX SYSTEMS HERITAGE TRAVELWARE ADD‐ON COMPUTER PERIPHERALS AZIO CORPORATION COMPUTERLINKS ETHERNET DIRECT HEWLETT PACKARD ENTERPRISE ADDON STORE B & B ELECTRONICS COMTROL ETHERWAN HIKVISION DIGITAL TECHNOLOGY CO. LT ADESSO BELDEN CONNECTGEAR EVANS CONSOLES HITACHI ADTRAN BELKIN COMPONENTS CONNECTPRO EVGA.COM HITACHI DATA SYSTEMS ADVANTECH AUTOMATION CORP. BIDUL & CO CONSTANT TECHNOLOGIES INC Exablaze HOO TOO INC AEROHIVE NETWORKS BLACK BOX COOL GEAR EXACQ TECHNOLOGIES INC HP AJA VIDEO SYSTEMS BLACKMAGIC DESIGN USA CP TECHNOLOGIES EXFO INC HP INC ALCATEL BLADE NETWORK TECHNOLOGIES CPS EXTREME NETWORKS HUAWEI ALCATEL LUCENT BLONDER TONGUE LABORATORIES CREATIVE LABS EXTRON HUAWEI SYMANTEC TECHNOLOGIES ALLIED TELESIS BLUE COAT SYSTEMS CRESTRON ELECTRONICS F5 NETWORKS IBM ALLOY COMPUTER PRODUCTS LLC BOSCH SECURITY CTC UNION TECHNOLOGIES CO FELLOWES ICOMTECH INC ALTINEX, INC. -

Microsoft Windows 7
IT Services Training Guide Microsoft Windows 7 IT Services Training Team The University of Manchester email: [email protected] www.itservices.manchester.ac.uk/trainingcourses/coursesforstaff Version 1.0 Table of Contents Starting and Exiting Windows ......................................................................................... 6 Objectives .................................................................................................................... 6 Starting your computer and logging on ......................................................................... 6 Restarting your computer .............................................................................................. 8 Ending your Windows session ...................................................................................... 10 Locking your computer ............................................................................................... 10 Logging off ................................................................................................................. 10 Putting the computer to sleep ..................................................................................... 11 Shutting down your computer ..................................................................................... 11 The Desktop ............................................................................................................... 11 Objectives ................................................................................................................. -
Pres Workflow User Guide
User Guide Version: 8.8 User Guide Version 8.8 Last Revision: 5/23/2019 Objectif Lune, Inc. 2030 Pie-IX, Suite 500 Montréal, QC, Canada, H1V 2C8 +1 (514) 875-5863 www.objectiflune.com All trademarks displayed are the property of their respective owners. © Objectif Lune, Inc. 1994-2019. All rights reserved. No part of this documentation may be reproduced, transmitted or distributed outside of Objectif Lune Inc. by any means whatsoever without the express written permission of Objectif Lune Inc. Inc. Objectif Lune Inc. Inc. disclaims responsibility for any errors and omissions in this documentation and accepts no responsibility for damages arising from such inconsistencies or their further consequences of any kind. Objectif Lune Inc. Inc reserves the right to alter the information contained in this documentation without notice. Table of Contents Table of Contents 4 Welcome to PReS Workflow 8.8 10 Icons used in this guide 10 System Requirements 12 Operating System (64-bit only) 12 Minimum Hardware Requirements 12 Known Issues 12 Basics 16 Setting Up the Working Environment 16 Setting Up Preferences 16 Create a New Process 16 Considerations 17 Send your Configuration 17 Features 19 The Nature of PReS Workflow 19 About Branches and Conditions 19 Branches 20 Conditions 20 Configuration Components 20 Connect Resources 20 Available Resources 21 Resource Save Location 21 Resource Archives 22 About Data 22 Data File and Job File 23 Job File Names and Output File Names 24 Data selections 25 About Data Emulation 34 Using the File Viewer 35 Sample -
Therecord Player™ User's Guide
TheRecord Player™ User’s Guide ® ForTheRecord GETTING STARTED Installation Refer to the Quick Setup Guide that accompanied this product. At some point you may need to configure Player to suit your requirements. See Configuring Player later in this guide. Starting You can start TheRecord Player from the Start menu or from the desktop. To start Player: 1. Do one of the following: a. From the desktop, double-click the Player icon or b. Click Start, point to All Programs, then ForTheRecord and click TheRecord Player. 2. Observe that the program starts with an empty Player. Note: When started for the first time a license agreement is displayed. If you accept the terms of the agreement you can continue. If not, Player does not start. You can also select an option to prevent the license being displayed again. Page 3 ® ForTheRecord Getting Help There are four ways to get help. Tutorial – contained on a separate CD that can be installed on your computer. TheRecord Player User’s Guide - this is stored on your computer and requires Acrobat Reader. On-line help - provides detailed descriptions of the features of Player. What’s This? help - provides instant access to help for information about each screen element. Viewing TheRecord Player Tutorial This tutorial guides you through the basic steps needed to open and play recordings. You can run the tutorials from the CD or from your local machine (if you have installed them). To run the TheRecord Player tutorial from CD or to install the tutorial: 1. Place the TheRecord Learning CD into the CD-ROM drive of your computer. -

Tinkertool System 6 Reference Manual Ii
Documentation 0632-1969/2 TinkerTool System 6 Reference Manual ii Version 6.99, July 21, 2021. US-English edition. MBS Documentation 0632-1969/2 © Copyright 2003 – 2021 by Marcel Bresink Software-Systeme Marcel Bresink Software-Systeme Ringstr. 21 56630 Kretz Germany All rights reserved. No part of this publication may be redistributed, translated in other languages, or transmitted, in any form or by any means, electronic, mechanical, recording, or otherwise, without the prior written permission of the publisher. This publication may contain examples of data used in daily business operations. To illustrate them as completely as possible, the examples include the names of individuals, companies, brands, and products. All of these names are fictitious and any similarity to the names and addresses used by an actual business enterprise is entirely coincidental. This publication could include technical inaccuracies or typographical errors. Changes are periodically made to the information herein; these changes will be incorporated in new editions of the publication. The publisher may make improvements and/or changes in the product(s) and/or the program(s) described in this publication at any time without notice. Make sure that you are using the correct edition of the publication for the level of the product. The version number can be found at the top of this page. Apple, macOS, iCloud, and FireWire are registered trademarks of Apple Inc. Intel is a registered trademark of Intel Corporation. UNIX is a registered trademark of The Open Group. Broadcom is a registered trademark of Broadcom, Inc. Trademarks or service marks are used for identification purposes only. -

Recycle Bin Documents Folder, Etc
UNIT- I TOPIC No: 4 Basic Computer Applications WINDOWS COMPONENTS Suneel Kumar Duvvuri Govt. College (A), Rajahmundry Email. Id : [email protected] DESKTOP When a computer is switched on, booting process will start, after the completion of booting process you can saw a screen is called desktop. Desktop is the first screen when computer is turned on. Desktop has icons, mouse pointer, and taskbar. WINDOWS-10 DESKTOP TASKBAR Taskbar: The rectangular bar that runs horizontally across the bottom of the screen is called taskbar. It provides access to all programs, it include start button, time, etc. You can also switch one program to another program here by using the task bar. Task bar also has quick launch it allows you to open frequently used programs quickly. DEFAULT DESKTOP ICONS Icons are small graphical images that can represent computer programs, files, folders. To activate the icon you double click on it with the left mouse button. The standard icons in windows operating system includes- This PC Network Recycle Bin Documents folder, etc. RECYCLE BIN The files removed by the user in the computer will go to this Recycle bin. Do you want to remove the files permanently from the computer then select ―deletea‖ option in the recycle bin. If you want to get back files from recycle bin to the original location where the file is actually deleted, then select ―restorea‖ option from the recycle bin. THIS PC /MY COMPUTER This is a standard icon and is very useful; it contains all the resources available in your computer. Generally it consists of hard disk drives, removable storage devices, network drives, and user documents and shared documents folder of your computer. -

CD-ROM, CD-RW, Or DVD-ROM Drive
Contents Chapter 1 Introduction . .1-1 Who Should Read This Guide?. .1-2 Using My Presario - Getting Started and Beyond . .1-2 Symbols and Graphics Used. .1-3 Computer Illustrations and Features . .1-3 Where Can I Find Information?. .1-4 Safety. 1-5 Safety and Comfort . 1-5 Chapter 2 Setting Up Your Computer . 2-1 Your Presario 5000 Series at a Glance . 2-2 What’s at the Front? (5000 Series) . 2-2 What’s at the Back? (5000 Series) . 2-2 Your Presario 7000 Series at a Glance . 2-3 What’s at the Front? (7000 Series) . 2-3 What’s at the Back? (7000 Series) . 2-3 Plug In and Go! . 2-4 Setting Up Your Computer . 2-4 MY PRESARIO—GETTING STARTED AND BEYOND CONTENTS i Registration . 2-5 Registering your PC . 2-5 Microsoft product registration key . 2-5 Printer Setup . .2-6 Setting Up Your Printer . .2-6 Connecting your TV to your Computer . 2-7 Networking Computers . 2-8 What is a Home Network? . 2-8 Setting Up a Network . .2-9 Installing the Network Protocols . 2-9 Mapping a Network Drive . 2-11 Securing Files . 2-11 Sharing Folders and Files . 2-12 Sharing a Printer . 2-12 Sharing Internet Access . 2-12 Chapter 3 Windows Basics . .3-1 Features of the Windows Desktop . 3-2 Viewing the Windows Desktop . 3-2 Using the Start Menu . 3-3 Help . 3-4 Accessing Online Help . 3-4 Chapter 4 Using Your Computer . 4-1 Keyboard Basics. .4-2 Getting to Know the Standard Keyboard Keys . -
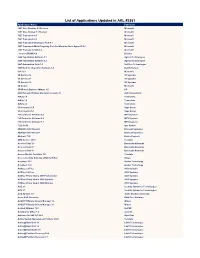
List of Applications Updated in ARL #2581
List of Applications Updated in ARL #2581 Application Name Publisher .NET Core Runtime 3.0 Preview Microsoft .NET Core Toolset 3.1 Preview Microsoft .NET Framework 4.5 Microsoft .NET Framework 4.6 Microsoft .NET Framework Developer Pack 4.7 Microsoft .NET Framework Multi-Targeting Pack for Windows Store Apps 4.5 RC Microsoft .NET Framework SDK 4.8 Microsoft _connect.BRAIN 4.8 Bizerba 2200 TapeStation Software 3.1 Agilent Technologies 2200 TapeStation Software 3.2 Agilent Technologies 24x7 Automation Suite 3.6 SoftTree Technologies 3500 Rack Configuration Software 6.0 Bently Nevada 365 16.0 Microsoft 3D Sprint 2.10 3D Systems 3D Sprint 2.11 3D Systems 3D Sprint 2.12 3D Systems 3D Viewer Microsoft 3PAR Host Explorer VMware 4.0 HP 4059 Extended Edition Attendant Console 2.1 ALE International 4uKey 1.4 Tenorshare 4uKey 1.6 Tenorshare 4uKey 2.2 Tenorshare 50 Accounts 21.0 Sage Group 50 Accounts 25.1 Sage Group 793 Controller Software 5.8 MTS Systems 793 Controller Software 5.9 MTS Systems 793 Controller Software 6.1 MTS Systems 7-Zip 19.00 Igor Pavlov ABAQUS 2018 Student Dassault Systemes ABAQUS 2019 Student Dassault Systemes Abstract 73.0 Elastic Projects ABU Service 14.10 Teradata Access Client 3.5 Barracuda Networks Access Client 3.7 Barracuda Networks Access Client 4.1 Barracuda Networks Access Module for Azure 15.1 Teradata Access Security Gateway (ASG) Soft Key Avaya AccuNest 10.3 Gerber Technology AccuNest 11.0 Gerber Technology ACDSee 2.3 Free ACD Systems ACDSee 2.4 Free ACD Systems ACDSee Photo Studio 2019 Professional ACD Systems -

REMOTE MOBILE SCREEN (RMS): an APPROACH for SECURE BYOD ENVIRONMENTS Santiago Manuel Gimenez Ocano University of Nebraska-Lincoln, [email protected]
University of Nebraska - Lincoln DigitalCommons@University of Nebraska - Lincoln Computer Science and Engineering: Theses, Computer Science and Engineering, Department of Dissertations, and Student Research Spring 4-2015 REMOTE MOBILE SCREEN (RMS): AN APPROACH FOR SECURE BYOD ENVIRONMENTS Santiago Manuel Gimenez Ocano University of Nebraska-Lincoln, [email protected] Follow this and additional works at: http://digitalcommons.unl.edu/computerscidiss Part of the Digital Communications and Networking Commons, and the Hardware Systems Commons Gimenez Ocano, Santiago Manuel, "REMOTE MOBILE SCREEN (RMS): AN APPROACH FOR SECURE BYOD ENVIRONMENTS" (2015). Computer Science and Engineering: Theses, Dissertations, and Student Research. 86. http://digitalcommons.unl.edu/computerscidiss/86 This Article is brought to you for free and open access by the Computer Science and Engineering, Department of at DigitalCommons@University of Nebraska - Lincoln. It has been accepted for inclusion in Computer Science and Engineering: Theses, Dissertations, and Student Research by an authorized administrator of DigitalCommons@University of Nebraska - Lincoln. REMOTE MOBILE SCREEN (RMS): AN APPROACH FOR SECURE BYOD ENVIRONMENTS by Santiago Gimenez Ocano A THESIS Presented to the Faculty of The Graduate College at the University of Nebraska In Partial Fulfillment of Requirements For the Degree of Master of Science Major: Computer Science Under the Supervision of Professor Byrav Ramamurthy Lincoln, Nebraska April, 2015 REMOTE MOBILE SCREEN (RMS): AN APPROACH FOR SECURE BYOD ENVIRONMENTS Santiago Gimenez Ocano, M.S. University of Nebraska, 2015 Adviser: Byrav Ramamurthy Bring Your Own Device (BYOD) is a policy where employees use their own personal mobile devices to perform work-related tasks. Enterprises reduce their costs since they do not have to purchase and provide support for the mobile devices.