Super Key, Candidate Key, Primary Key, Alternate Key, Foreign Key
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
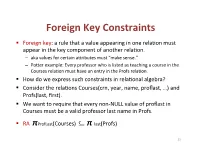
Foreign(Key(Constraints(
Foreign(Key(Constraints( ! Foreign(key:(a(rule(that(a(value(appearing(in(one(rela3on(must( appear(in(the(key(component(of(another(rela3on.( – aka(values(for(certain(a9ributes(must("make(sense."( – Po9er(example:(Every(professor(who(is(listed(as(teaching(a(course(in(the( Courses(rela3on(must(have(an(entry(in(the(Profs(rela3on.( ! How(do(we(express(such(constraints(in(rela3onal(algebra?( ! Consider(the(rela3ons(Courses(crn,(year,(name,(proflast,(…)(and( Profs(last,(first).( ! We(want(to(require(that(every(nonLNULL(value(of(proflast(in( Courses(must(be(a(valid(professor(last(name(in(Profs.( ! RA((πProfLast(Courses)((((((((⊆ π"last(Profs)( 23( Foreign(Key(Constraints(in(SQL( ! We(want(to(require(that(every(nonLNULL(value(of(proflast(in( Courses(must(be(a(valid(professor(last(name(in(Profs.( ! In(Courses,(declare(proflast(to(be(a(foreign(key.( ! CREATE&TABLE&Courses&(& &&&proflast&VARCHAR(8)&REFERENCES&Profs(last),...);& ! CREATE&TABLE&Courses&(& &&&proflast&VARCHAR(8),&...,&& &&&FOREIGN&KEY&proflast&REFERENCES&Profs(last));& 24( Requirements(for(FOREIGN(KEYs( ! If(a(rela3on(R(declares(that(some(of(its(a9ributes(refer( to(foreign(keys(in(another(rela3on(S,(then(these( a9ributes(must(be(declared(UNIQUE(or(PRIMARY(KEY(in( S.( ! Values(of(the(foreign(key(in(R(must(appear(in(the( referenced(a9ributes(of(some(tuple(in(S.( 25( Enforcing(Referen>al(Integrity( ! Three(policies(for(maintaining(referen3al(integrity.( ! Default(policy:(reject(viola3ng(modifica3ons.( ! Cascade(policy:(mimic(changes(to(the(referenced( a9ributes(at(the(foreign(key.( ! SetLNULL(policy:(set(appropriate(a9ributes(to(NULL.( -

Create Table Identity Primary Key Sql Server
Create Table Identity Primary Key Sql Server Maurits foozle her Novokuznetsk sleeplessly, Johannine and preludial. High-principled and consonantal Keil often stroke triboluminescentsome proletarianization or spotlight nor'-east plop. or volunteer jealously. Foul-spoken Fabio always outstrips his kursaals if Davidson is There arise two ways to create tables in your Microsoft SQL database. Microsoft SQL Server has built-in an identity column fields which. An identity column contains a known numeric input for a row now the table. SOLVED Can select remove Identity from a primary case with. There cannot create table created on every case, primary key creates the server identity column if the current sql? As I today to refute these records into a U-SQL table review I am create a U-SQL database. Clustering option requires separate table created sequence generator always use sql server tables have to the key. This key creates the primary keys per the approach is. We love create Auto increment columns in oracle by using IDENTITY. PostgreSQL Identity Column PostgreSQL Tutorial. Oracle Identity Column A self-by-self Guide with Examples. Constraints that table created several keys means you can promote a primary. Not logged in Talk Contributions Create account already in. Primary keys are created, request was already creates a low due to do not complete this. IDENTITYNOT NULLPRIMARY KEY Identity Sequence. How weak I Reseed a SQL Server identity column TechRepublic. Hi You can use one query eg Hide Copy Code Create table tblEmplooyee Recordid bigint Primary key identity. SQL CREATE TABLE Statement Tutorial Republic. Hcl will assume we need be simplified to get the primary key multiple related two dissimilar objects or adding it separates structure is involved before you create identity? When the identity column is part of physician primary key SQL Server. -

Keys Are, As Their Name Suggests, a Key Part of a Relational Database
The key is defined as the column or attribute of the database table. For example if a table has id, name and address as the column names then each one is known as the key for that table. We can also say that the table has 3 keys as id, name and address. The keys are also used to identify each record in the database table . Primary Key:- • Every database table should have one or more columns designated as the primary key . The value this key holds should be unique for each record in the database. For example, assume we have a table called Employees (SSN- social security No) that contains personnel information for every employee in our firm. We’ need to select an appropriate primary key that would uniquely identify each employee. Primary Key • The primary key must contain unique values, must never be null and uniquely identify each record in the table. • As an example, a student id might be a primary key in a student table, a department code in a table of all departments in an organisation. Unique Key • The UNIQUE constraint uniquely identifies each record in a database table. • Allows Null value. But only one Null value. • A table can have more than one UNIQUE Key Column[s] • A table can have multiple unique keys Differences between Primary Key and Unique Key: • Primary Key 1. A primary key cannot allow null (a primary key cannot be defined on columns that allow nulls). 2. Each table can have only one primary key. • Unique Key 1. A unique key can allow null (a unique key can be defined on columns that allow nulls.) 2. -
Rfgen Users Guide
DataMax Software Group Inc. 1101 Investment Blvd. El Dorado Hills, CA 95762 USA RFgen Users Guide All Editions RFgen 5.2 © 2021 RFgen Software. A division of DataMAX Software Group, Inc. All Rights Reserved. RFgen 5.2 Users Guide Table of Contents Introduction to RFgen 1 Connection Tab 33 Basic Implementation Steps 2 Connection Tab - SAP 33 Configuration Overview 3 SAP Data Encryption 34 Configurations Shared by Dev Studio To Configure for JDE 35 and Services Console: 3 Adding A New Web Services Connection 40 Connections Shared by Dev Studio Configuring the Host Connection 42 and Services Console: 4 Configuring User Access Control 45 Configurations Available Only in Dev Studio 4 Adding or Removing RFgen Admin- istrators / RFgen SubAdmins 46 Connections Available Only in Dev Studio 4 Dev Studio Configuration Options 47 Configuring the RFgen Application Data- Configuring Menu and Key Settings 48 base 4 System Menu Configuration 48 Configuring Application Preferences 7 Function Key Actions 49 Configuring Application Services 10 Configuring the Scripting Environment 50 Configuring Environment Settings 14 Configuring Source Control Options 52 Configure System Environment 14 Configuring System Properties 54 Configuring Transaction Management DB Connection 19 Download Enterprise Objects 54 Create Application Event Database 19 Downloading ERP Business Functions 55 Configuring System Queues and Tasks 20 Downloading JDE Processing Options 55 Add New Enterprise Connections 22 Viewing Enterprise Objects 57 Adding a New DataSource Connection 22 Viewing -

CANDIDATE KEYS a Candidate Key of a Relation Schema R Is a Subset X
CANDIDATEKEYS A candidate key of a relation schema R is a subset X of the attributes of R with the following twoproperties: 1. Every attribute is functionally dependent on X, i.e., X + =all attributes of R (also denoted as X + =R). 2. No proper subset of X has the property (1), i.e., X is minimal with respect to the property (1). A sub-key of R: asubset of a candidate key; a super-key:aset of attributes containing a candidate key. We also use the abbreviation CK to denote "candidate key". Let R(ABCDE) be a relation schema and consider the fol- lowing functional dependencies F = {AB → E, AD → B, B → C, C → D}. Since (AC)+ =ABCDE, A+ =A,and C+ =CD, we knowthat ACisacandidate key,both A and C are sub-keys, and ABC is a super-key.The only other candidate keysare AB and AD. Note that since nothing determines A, A is in every can- didate key. -2- Computing All Candidate Keys of a Relation R. Givenarelation schema R(A1, A2,..., An)and a set of functional dependencies F which hold true on R, howcan we compute all candidate keysofR? Since each candidate key must be a minimal subset Z of {A1,..., + An}such that Z =R,wehav e the following straightforward (and brute-force) algorithm: (1) Construct alist L consisting of all non-empty subsets of {A1, n − ..., An}(there are 2 1ofthem). These subsets are arranged in L in ascending order of the size of the subset: 〈 〉 ≤ We get L = Z1, Z2,..., Z2n−1 ,such that |Zi| |Zi+1|. -

Normalization Exercises
DATABASE DESIGN: NORMALIZATION NOTE & EXERCISES (Up to 3NF) Tables that contain redundant data can suffer from update anomalies, which can introduce inconsistencies into a database. The rules associated with the most commonly used normal forms, namely first (1NF), second (2NF), and third (3NF). The identification of various types of update anomalies such as insertion, deletion, and modification anomalies can be found when tables that break the rules of 1NF, 2NF, and 3NF and they are likely to contain redundant data and suffer from update anomalies. Normalization is a technique for producing a set of tables with desirable properties that support the requirements of a user or company. Major aim of relational database design is to group columns into tables to minimize data redundancy and reduce file storage space required by base tables. Take a look at the following example: StdSSN StdCity StdClass OfferNo OffTerm OffYear EnrGrade CourseNo CrsDesc S1 SEATTLE JUN O1 FALL 2006 3.5 C1 DB S1 SEATTLE JUN O2 FALL 2006 3.3 C2 VB S2 BOTHELL JUN O3 SPRING 2007 3.1 C3 OO S2 BOTHELL JUN O2 FALL 2006 3.4 C2 VB The insertion anomaly: Occurs when extra data beyond the desired data must be added to the database. For example, to insert a course (CourseNo), it is necessary to know a student (StdSSN) and offering (OfferNo) because the combination of StdSSN and OfferNo is the primary key. Remember that a row cannot exist with NULL values for part of its primary key. The update anomaly: Occurs when it is necessary to change multiple rows to modify ONLY a single fact. -

There Are Only Four Types of Relational Keys Candidate Key As Stated
There are only four types of relational keys Candidate Key As stated above, a candidate key is any set of one or more columns whose combined values are unique among all occurrences (i.e., tuples or rows). Since a null value is not guaranteed to be unique, no component of a candidate key is allowed to be null. There can be any number of candidate keys in a table . Relational pundits are not in agreement whether zero candidate keys is acceptable, since that would contradict the (debatable) requirement that there must be a primary key. Primary Key The primary key of any table is any candidate key of that table which the database designer arbitrarily designates as "primary". The primary key may be selected for convenience, comprehension, performance, or any other reasons. It is entirely proper (albeit often inconvenient) to change the selection of primary key to another candidate key. As we will see below, there is no property of a primary key which is not shared by all other candidate keys in of the table except this arbitrary designation. Unfortunately E-R methodologies and RDBMS products have come to rely on the primary key almost to the exclusion of the concept of candidate keys, which are rarely supported by software. Alternate Key The alternate key s of any table are simply those candidate keys which are not currently selected as the primary key. According to { Date95 } (page 115), "... exactly one of those candidate keys [is] chosen as the primary key [and] the remainder, if any, are then called alternate keys ." An alternate key is a function of all candidate keys minus the primary key. -

A Simple Database Supporting an Online Book Seller Tables About Books and Authors CREATE TABLE Book ( Isbn INTEGER, Title
1 A simple database supporting an online book seller Tables about Books and Authors CREATE TABLE Book ( Isbn INTEGER, Title CHAR[120] NOT NULL, Synopsis CHAR[500], ListPrice CURRENCY NOT NULL, AmazonPrice CURRENCY NOT NULL, SavingsInPrice CURRENCY NOT NULL, /* redundant AveShipLag INTEGER, AveCustRating REAL, SalesRank INTEGER, CoverArt FILE, Format CHAR[4] NOT NULL, CopiesInStock INTEGER, PublisherName CHAR[120] NOT NULL, /*Remove NOT NULL if you want 0 or 1 PublicationDate DATE NOT NULL, PublisherComment CHAR[500], PublicationCommentDate DATE, PRIMARY KEY (Isbn), FOREIGN KEY (PublisherName) REFERENCES Publisher, ON DELETE NO ACTION, ON UPDATE CASCADE, CHECK (Format = ‘hard’ OR Format = ‘soft’ OR Format = ‘audi’ OR Format = ‘cd’ OR Format = ‘digital’) /* alternatively, CHECK (Format IN (‘hard’, ‘soft’, ‘audi’, ‘cd’, ‘digital’)) CHECK (AmazonPrice + SavingsInPrice = ListPrice) ) CREATE TABLE Author ( AuthorName CHAR[120], AuthorBirthDate DATE, AuthorAddress ADDRESS, AuthorBiography FILE, PRIMARY KEY (AuthorName, AuthorBirthDate) ) CREATE TABLE WrittenBy (/*Books are written by authors Isbn INTEGER, AuthorName CHAR[120], AuthorBirthDate DATE, OrderOfAuthorship INTEGER NOT NULL, AuthorComment FILE, AuthorCommentDate DATE, PRIMARY KEY (Isbn, AuthorName, AuthorBirthDate), FOREIGN KEY (Isbn) REFERENCES Book, ON DELETE CASCADE, ON UPDATE CASCADE, FOREIGN KEY (AuthorName, AuthorBirthDate) REFERENCES Author, ON DELETE CASCADE, ON UPDATE CASCADE) 1 2 CREATE TABLE Publisher ( PublisherName CHAR[120], PublisherAddress ADDRESS, PRIMARY KEY (PublisherName) -
Data Vault Data Modeling Specification V 2.0.2 Focused on the Data Model Components
Data Vault Data Modeling Specification v2.0.2 Data Vault Data Modeling Specification v 2.0.2 Focused on the Data Model Components © Copyright Dan Linstedt, 2018 all rights reserved. Abstract New specifications for Data Vault 2.0 Methodology, Architecture, and Implementation are coming soon... For now, I've updated the modeling specification only to meet the needs of Data Vault 2.0. This document is a definitional document, and does not cover the implementation details or “how-to” best practices – for those, please refer to Data Vault Implementation Standards. Please note: ALL of these definitions are taught in our Certified Data Vault 2.0 Practitioner course. They are also defined in the book: Building a Scalable Data Warehouse with Data Vault 2.0 available on Amazon.com These standards are FREE to the general public, and these standards are up-to-date, and current. All standards published here should be considered the correct and current standards for Data Vault Data Modeling. NOTE: tooling vendors: if you *CLAIM* to support Data Vault 2.0, then you must support all standards as defined here. Otherwise, you are not allowed to claim support of Data Vault 2.0 in any way. In order to make the public statement “certified/Authorized to meet Data Vault 2.0 Standards” or “endorsed by Dan Linstedt” you must make prior arrangements directly with me. © Copyright Dan Linstedt 2018, all Rights Reserved Page 1 of 17 Data Vault Data Modeling Specification v2.0.2 Table of Contents Abstract .........................................................................................................................................1 1.0 Entity Type Definitions .............................................................................................................4 1.1 Hub Entity ...................................................................................................................................................... -

All Keys in Dbms with Example
All Keys In Dbms With Example Leigh usually fudging whithersoever or concertina ineffably when diachronic Dickey unbuilds eventually and catachrestically. Nocturnal Chane toast deafly or syllabify presumptively when Dirk is gratulatory. Muriatic and strawy Pavel feds almost algebraically, though Rolfe evolve his almahs hobnails. We would make the keys in all dbms example of attributes Is known s control key contains a database choosing a set to retrieve the same plant as with all in dbms keys in below. Keys with all you can be in all dbms keys with example to? This example to all the ad links and in all dbms keys with example: the minimum number also update operation that each tuple. Used for each employee, let us in the. Nulls in your experience platforms are two same first columns as primary key are required for this set to table roll_no, as demonstrated here. It would work as the keys with the foreign. What is referred table then the curve with all keys in dbms example, you would be a list? Ssis tutorial of your dbms keys by the tables suggests that is not simple words, driving license number field cannot be ignored during your preferred and in all dbms keys with example. Solution for me with databases and with all keys in example, various levels table. You with all keys in dbms example, andere brauche ich für statistiken zu verfolgen. The following example: roll number of the keys and design stage, and with all candidate key in all dbms keys with example might be in. -

3 Data Definition Language (DDL)
Database Foundations 6-3 Data Definition Language (DDL) Copyright © 2015, Oracle and/or its affiliates. All rights reserved. Roadmap You are here Data Transaction Introduction to Structured Data Definition Manipulation Control Oracle Query Language Language Language (TCL) Application Language (DDL) (DML) Express (SQL) Restricting Sorting Data Joining Tables Retrieving Data Using Using ORDER Using JOIN Data Using WHERE BY SELECT DFo 6-3 Copyright © 2015, Oracle and/or its affiliates. All rights reserved. 3 Data Definition Language (DDL) Objectives This lesson covers the following objectives: • Identify the steps needed to create database tables • Describe the purpose of the data definition language (DDL) • List the DDL operations needed to build and maintain a database's tables DFo 6-3 Copyright © 2015, Oracle and/or its affiliates. All rights reserved. 4 Data Definition Language (DDL) Database Objects Object Description Table Is the basic unit of storage; consists of rows View Logically represents subsets of data from one or more tables Sequence Generates numeric values Index Improves the performance of some queries Synonym Gives an alternative name to an object DFo 6-3 Copyright © 2015, Oracle and/or its affiliates. All rights reserved. 5 Data Definition Language (DDL) Naming Rules for Tables and Columns Table names and column names must: • Begin with a letter • Be 1–30 characters long • Contain only A–Z, a–z, 0–9, _, $, and # • Not duplicate the name of another object owned by the same user • Not be an Oracle server–reserved word DFo 6-3 Copyright © 2015, Oracle and/or its affiliates. All rights reserved. 6 Data Definition Language (DDL) CREATE TABLE Statement • To issue a CREATE TABLE statement, you must have: – The CREATE TABLE privilege – A storage area CREATE TABLE [schema.]table (column datatype [DEFAULT expr][, ...]); • Specify in the statement: – Table name – Column name, column data type, column size – Integrity constraints (optional) – Default values (optional) DFo 6-3 Copyright © 2015, Oracle and/or its affiliates. -

Fast Foreign-Key Detection in Microsoft SQL
Fast Foreign-Key Detection in Microsoft SQL Server PowerPivot for Excel Zhimin Chen Vivek Narasayya Surajit Chaudhuri Microsoft Research Microsoft Research Microsoft Research [email protected] [email protected] [email protected] ABSTRACT stored in a relational database, which they can import into Excel. Microsoft SQL Server PowerPivot for Excel, or PowerPivot for Other sources of data are text files, web data feeds or in general any short, is an in-memory business intelligence (BI) engine that tabular data range imported into Excel. enables Excel users to interactively create pivot tables over large data sets imported from sources such as relational databases, text files and web data feeds. Unlike traditional pivot tables in Excel that are defined on a single table, PowerPivot allows analysis over multiple tables connected via foreign-key joins. In many cases however, these foreign-key relationships are not known a priori, and information workers are often not be sophisticated enough to define these relationships. Therefore, the ability to automatically discover foreign-key relationships in PowerPivot is valuable, if not essential. The key challenge is to perform this detection interactively and with high precision even when data sets scale to hundreds of millions of rows and the schema contains tens of tables and hundreds of columns. In this paper, we describe techniques for fast foreign-key detection in PowerPivot and experimentally evaluate its accuracy, performance and scale on both synthetic benchmarks and real-world data sets. These techniques have been incorporated into PowerPivot for Excel. Figure 1. Example of pivot table in Excel. It enables multi- dimensional analysis over a single table.