CSC 443 – Database Management Systems Data and Its Structure
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
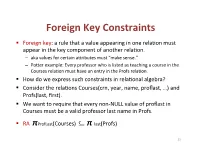
Foreign(Key(Constraints(
Foreign(Key(Constraints( ! Foreign(key:(a(rule(that(a(value(appearing(in(one(rela3on(must( appear(in(the(key(component(of(another(rela3on.( – aka(values(for(certain(a9ributes(must("make(sense."( – Po9er(example:(Every(professor(who(is(listed(as(teaching(a(course(in(the( Courses(rela3on(must(have(an(entry(in(the(Profs(rela3on.( ! How(do(we(express(such(constraints(in(rela3onal(algebra?( ! Consider(the(rela3ons(Courses(crn,(year,(name,(proflast,(…)(and( Profs(last,(first).( ! We(want(to(require(that(every(nonLNULL(value(of(proflast(in( Courses(must(be(a(valid(professor(last(name(in(Profs.( ! RA((πProfLast(Courses)((((((((⊆ π"last(Profs)( 23( Foreign(Key(Constraints(in(SQL( ! We(want(to(require(that(every(nonLNULL(value(of(proflast(in( Courses(must(be(a(valid(professor(last(name(in(Profs.( ! In(Courses,(declare(proflast(to(be(a(foreign(key.( ! CREATE&TABLE&Courses&(& &&&proflast&VARCHAR(8)&REFERENCES&Profs(last),...);& ! CREATE&TABLE&Courses&(& &&&proflast&VARCHAR(8),&...,&& &&&FOREIGN&KEY&proflast&REFERENCES&Profs(last));& 24( Requirements(for(FOREIGN(KEYs( ! If(a(rela3on(R(declares(that(some(of(its(a9ributes(refer( to(foreign(keys(in(another(rela3on(S,(then(these( a9ributes(must(be(declared(UNIQUE(or(PRIMARY(KEY(in( S.( ! Values(of(the(foreign(key(in(R(must(appear(in(the( referenced(a9ributes(of(some(tuple(in(S.( 25( Enforcing(Referen>al(Integrity( ! Three(policies(for(maintaining(referen3al(integrity.( ! Default(policy:(reject(viola3ng(modifica3ons.( ! Cascade(policy:(mimic(changes(to(the(referenced( a9ributes(at(the(foreign(key.( ! SetLNULL(policy:(set(appropriate(a9ributes(to(NULL.( -
SAP IQ Administration: User Management and Security Company
ADMINISTRATION GUIDE | PUBLIC SAP IQ 16.1 SP 04 Document Version: 1.0.0 – 2019-04-05 SAP IQ Administration: User Management and Security company. All rights reserved. All rights company. affiliate THE BEST RUN 2019 SAP SE or an SAP SE or an SAP SAP 2019 © Content 1 Security Management........................................................ 5 1.1 Plan and Implement Role-Based Security............................................6 1.2 Roles......................................................................7 User-Defined Roles.........................................................8 System Roles............................................................ 30 Compatibility Roles........................................................38 Views, Procedures, and Tables That Are Owned by Roles..............................38 Display Roles Granted......................................................39 Determining the Roles and Privileges Granted to a User...............................40 1.3 Privileges..................................................................40 Privileges Versus Permissions.................................................41 System Privileges......................................................... 42 Object-Level Privileges......................................................64 System Procedure Privileges..................................................81 1.4 Passwords.................................................................85 Password and user ID Restrictions and Considerations...............................86 -

Is Uncountable the Open Interval (0, 1)
Section 2.4:R is uncountable (0, 1) is uncountable This assertion and its proof date back to the 1890’s and to Georg Cantor. The proof is often referred to as “Cantor’s diagonal argument” and applies in more general contexts than we will see in these notes. Our goal in this section is to show that the setR of real numbers is uncountable or non-denumerable; this means that its elements cannot be listed, or cannot be put in bijective correspondence with the natural numbers. We saw at the end of Section 2.3 that R has the same cardinality as the interval ( π , π ), or the interval ( 1, 1), or the interval (0, 1). We will − 2 2 − show that the open interval (0, 1) is uncountable. Georg Cantor : born in St Petersburg (1845), died in Halle (1918) Theorem 42 The open interval (0, 1) is not a countable set. Dr Rachel Quinlan MA180/MA186/MA190 Calculus R is uncountable 143 / 222 Dr Rachel Quinlan MA180/MA186/MA190 Calculus R is uncountable 144 / 222 The open interval (0, 1) is not a countable set A hypothetical bijective correspondence Our goal is to show that the interval (0, 1) cannot be put in bijective correspondence with the setN of natural numbers. Our strategy is to We recall precisely what this set is. show that no attempt at constructing a bijective correspondence between It consists of all real numbers that are greater than zero and less these two sets can ever be complete; it can never involve all the real than 1, or equivalently of all the points on the number line that are numbers in the interval (0, 1) no matter how it is devised. -

Referential Integrity in Sqlite
CS 564: Database Management Systems University of Wisconsin - Madison, Fall 2017 Referential Integrity in SQLite Declaring Referential Integrity (Foreign Key) Constraints Foreign key constraints are used to check referential integrity between tables in a database. Consider, for example, the following two tables: create table Residence ( nameVARCHARPRIMARY KEY, capacityINT ); create table Student ( idINTPRIMARY KEY, firstNameVARCHAR, lastNameVARCHAR, residenceVARCHAR ); We can enforce the constraint that a Student’s residence actually exists by making Student.residence a foreign key that refers to Residence.name. SQLite lets you specify this relationship in several different ways: create table Residence ( nameVARCHARPRIMARY KEY, capacityINT ); create table Student ( idINTPRIMARY KEY, firstNameVARCHAR, lastNameVARCHAR, residenceVARCHAR, FOREIGNKEY(residence) REFERENCES Residence(name) ); or create table Residence ( nameVARCHARPRIMARY KEY, capacityINT ); create table Student ( idINTPRIMARY KEY, firstNameVARCHAR, lastNameVARCHAR, residenceVARCHAR REFERENCES Residence(name) ); or create table Residence ( nameVARCHARPRIMARY KEY, 1 capacityINT ); create table Student ( idINTPRIMARY KEY, firstNameVARCHAR, lastNameVARCHAR, residenceVARCHAR REFERENCES Residence-- Implicitly references the primary key of the Residence table. ); All three forms are valid syntax for specifying the same constraint. Constraint Enforcement There are a number of important things about how referential integrity and foreign keys are handled in SQLite: • The attribute(s) referenced by a foreign key constraint (i.e. Residence.name in the example above) must be declared UNIQUE or as the PRIMARY KEY within their table, but this requirement is checked at run-time, not when constraints are declared. For example, if Residence.name had not been declared as the PRIMARY KEY of its table (or as UNIQUE), the FOREIGN KEY declarations above would still be permitted, but inserting into the Student table would always yield an error. -

Keys Are, As Their Name Suggests, a Key Part of a Relational Database
The key is defined as the column or attribute of the database table. For example if a table has id, name and address as the column names then each one is known as the key for that table. We can also say that the table has 3 keys as id, name and address. The keys are also used to identify each record in the database table . Primary Key:- • Every database table should have one or more columns designated as the primary key . The value this key holds should be unique for each record in the database. For example, assume we have a table called Employees (SSN- social security No) that contains personnel information for every employee in our firm. We’ need to select an appropriate primary key that would uniquely identify each employee. Primary Key • The primary key must contain unique values, must never be null and uniquely identify each record in the table. • As an example, a student id might be a primary key in a student table, a department code in a table of all departments in an organisation. Unique Key • The UNIQUE constraint uniquely identifies each record in a database table. • Allows Null value. But only one Null value. • A table can have more than one UNIQUE Key Column[s] • A table can have multiple unique keys Differences between Primary Key and Unique Key: • Primary Key 1. A primary key cannot allow null (a primary key cannot be defined on columns that allow nulls). 2. Each table can have only one primary key. • Unique Key 1. A unique key can allow null (a unique key can be defined on columns that allow nulls.) 2. -

*** Check Constraints - 10G
*** Check Constraints - 10g *** Create table and poulated with a column called FLAG that can only have a value of 1 or 2 SQL> CREATE TABLE check_const (id NUMBER, flag NUMBER CONSTRAINT check_flag CHECK (flag IN (1,2))); Table created. SQL> INSERT INTO check_const SELECT rownum, mod(rownum,2)+1 FROM dual CONNECT BY level <=10000; 10000 rows created. SQL> COMMIT; Commit complete. SQL> exec dbms_stats.gather_table_stats(ownname=>NULL, tabname=>'CHECK_CONST', estimate_percent=> NULL, method_opt=> 'FOR ALL COLUMNS SIZE 1'); PL/SQL procedure successfully completed. *** Now perform a search for a value of 3. There can be no such value as the Check constraint only permits values 1 or 2 ... *** The exection plan appears to suggest a FTS is being performed (remember, there are no indexes on the flag column) *** But the statistics clearly show no LIOs were performed, none SQL> SELECT * FROM check_const WHERE flag = 3; no rows selected Execution Plan ---------------------------------------------------------- Plan hash value: 1514750852 ---------------------------------------------------------------------------------- | Id | Operation | Name | Rows | Bytes | Cost (%CPU)| Time | ---------------------------------------------------------------------------------- | 0 | SELECT STATEMENT | | 1 | 6 | 0 (0)| | |* 1 | FILTER | | | | | | |* 2 | TABLE ACCESS FULL| CHECK_CONST | 1 | 6 | 6 (0)| 00:00:01 | ---------------------------------------------------------------------------------- Predicate Information (identified by operation id): --------------------------------------------------- -

CANDIDATE KEYS a Candidate Key of a Relation Schema R Is a Subset X
CANDIDATEKEYS A candidate key of a relation schema R is a subset X of the attributes of R with the following twoproperties: 1. Every attribute is functionally dependent on X, i.e., X + =all attributes of R (also denoted as X + =R). 2. No proper subset of X has the property (1), i.e., X is minimal with respect to the property (1). A sub-key of R: asubset of a candidate key; a super-key:aset of attributes containing a candidate key. We also use the abbreviation CK to denote "candidate key". Let R(ABCDE) be a relation schema and consider the fol- lowing functional dependencies F = {AB → E, AD → B, B → C, C → D}. Since (AC)+ =ABCDE, A+ =A,and C+ =CD, we knowthat ACisacandidate key,both A and C are sub-keys, and ABC is a super-key.The only other candidate keysare AB and AD. Note that since nothing determines A, A is in every can- didate key. -2- Computing All Candidate Keys of a Relation R. Givenarelation schema R(A1, A2,..., An)and a set of functional dependencies F which hold true on R, howcan we compute all candidate keysofR? Since each candidate key must be a minimal subset Z of {A1,..., + An}such that Z =R,wehav e the following straightforward (and brute-force) algorithm: (1) Construct alist L consisting of all non-empty subsets of {A1, n − ..., An}(there are 2 1ofthem). These subsets are arranged in L in ascending order of the size of the subset: 〈 〉 ≤ We get L = Z1, Z2,..., Z2n−1 ,such that |Zi| |Zi+1|. -
Cardinality of Sets
Cardinality of Sets MAT231 Transition to Higher Mathematics Fall 2014 MAT231 (Transition to Higher Math) Cardinality of Sets Fall 2014 1 / 15 Outline 1 Sets with Equal Cardinality 2 Countable and Uncountable Sets MAT231 (Transition to Higher Math) Cardinality of Sets Fall 2014 2 / 15 Sets with Equal Cardinality Definition Two sets A and B have the same cardinality, written jAj = jBj, if there exists a bijective function f : A ! B. If no such bijective function exists, then the sets have unequal cardinalities, that is, jAj 6= jBj. Another way to say this is that jAj = jBj if there is a one-to-one correspondence between the elements of A and the elements of B. For example, to show that the set A = f1; 2; 3; 4g and the set B = {♠; ~; }; |g have the same cardinality it is sufficient to construct a bijective function between them. 1 2 3 4 ♠ ~ } | MAT231 (Transition to Higher Math) Cardinality of Sets Fall 2014 3 / 15 Sets with Equal Cardinality Consider the following: This definition does not involve the number of elements in the sets. It works equally well for finite and infinite sets. Any bijection between the sets is sufficient. MAT231 (Transition to Higher Math) Cardinality of Sets Fall 2014 4 / 15 The set Z contains all the numbers in N as well as numbers not in N. So maybe Z is larger than N... On the other hand, both sets are infinite, so maybe Z is the same size as N... This is just the sort of ambiguity we want to avoid, so we appeal to the definition of \same cardinality." The answer to our question boils down to \Can we find a bijection between N and Z?" Does jNj = jZj? True or false: Z is larger than N. -

Normalization Exercises
DATABASE DESIGN: NORMALIZATION NOTE & EXERCISES (Up to 3NF) Tables that contain redundant data can suffer from update anomalies, which can introduce inconsistencies into a database. The rules associated with the most commonly used normal forms, namely first (1NF), second (2NF), and third (3NF). The identification of various types of update anomalies such as insertion, deletion, and modification anomalies can be found when tables that break the rules of 1NF, 2NF, and 3NF and they are likely to contain redundant data and suffer from update anomalies. Normalization is a technique for producing a set of tables with desirable properties that support the requirements of a user or company. Major aim of relational database design is to group columns into tables to minimize data redundancy and reduce file storage space required by base tables. Take a look at the following example: StdSSN StdCity StdClass OfferNo OffTerm OffYear EnrGrade CourseNo CrsDesc S1 SEATTLE JUN O1 FALL 2006 3.5 C1 DB S1 SEATTLE JUN O2 FALL 2006 3.3 C2 VB S2 BOTHELL JUN O3 SPRING 2007 3.1 C3 OO S2 BOTHELL JUN O2 FALL 2006 3.4 C2 VB The insertion anomaly: Occurs when extra data beyond the desired data must be added to the database. For example, to insert a course (CourseNo), it is necessary to know a student (StdSSN) and offering (OfferNo) because the combination of StdSSN and OfferNo is the primary key. Remember that a row cannot exist with NULL values for part of its primary key. The update anomaly: Occurs when it is necessary to change multiple rows to modify ONLY a single fact. -

Chapter 10. Declarative Constraints and Database Triggers
Chapter 10. Declarative Constraints and Database Triggers Table of contents • Objectives • Introduction • Context • Declarative constraints – The PRIMARY KEY constraint – The NOT NULL constraint – The UNIQUE constraint – The CHECK constraint ∗ Declaration of a basic CHECK constraint ∗ Complex CHECK constraints – The FOREIGN KEY constraint ∗ CASCADE ∗ SET NULL ∗ SET DEFAULT ∗ NO ACTION • Changing the definition of a table – Add a new column – Modify an existing column’s type – Modify an existing column’s constraint definition – Add a new constraint – Drop an existing constraint • Database triggers – Types of triggers ∗ Event ∗ Level ∗ Timing – Valid trigger types • Creating triggers – Statement-level trigger ∗ Option for the UPDATE event – Row-level triggers ∗ Option for the row-level triggers – Removing triggers – Using triggers to maintain referential integrity – Using triggers to maintain business rules • Additional features of Oracle – Stored procedures – Function and packages – Creating procedures – Creating functions 1 – Calling a procedure from within a function and vice versa • Discussion topics • Additional content and activities Objectives At the end of this chapter you should be able to: • Know how to capture a range of business rules and store them in a database using declarative constraints. • Describe the use of database triggers in providing an automatic response to the occurrence of specific database events. • Discuss the advantages and drawbacks of the use of database triggers in application development. • Explain how stored procedures can be used to implement processing logic at the database level. Introduction In parallel with this chapter, you should read Chapter 8 of Thomas Connolly and Carolyn Begg, “Database Systems A Practical Approach to Design, Imple- mentation, and Management”, (5th edn.). -
Clarion & ANSI SQL Standard Referential Integrity and Referential
Clarion & ANSI SQL Standard Referential Integrity and Referential Actions November 12, 2018 Whitemarsh Information Systems Corporation 2008 Althea Lane Bowie, Maryland 20716 Tele: 301-249-1142 Email: [email protected] Web: www.wiscorp.com Referential Integrity and Referential Actions Fundamental Definition: Actions resulting from instruction to the database engine created in the dictionary (i.e., schema) associated with “Relationship” specifications. For SQL-engine DBMSs, these relationship-specifications and actions relate to value congruence between the value-set of a primary key’s column(s) and the value-set of a Foreign key’s column(s). When either a Update or Delete action occurs that violates the value congruence, a Referential Action occurs. The actions depend on whether the Referential Action is specified. In ANSI SQL Standards, the four referential integrity actions: No Action, Cascade, or Set Null or Set Default. In Clarion, the five referential integrity actions are: None, Restrict, Cascade, Clear, Cascade Server, ClearServer and Restrict Server. Copyright 2018, Whitemarsh Information Systems Corporation Proprietary Data, All Rights Reserved 2 Referential Integrity and Referential Actions Referential Integrity and Actions Referential Action taken when violation occurs On Update On Delete Referential Action Parent Child Parent Child Function ANSI Clarion Table Table Table Table Parent Table No equivalent None: Instructs the Primary No change Row is Nothing. Primary Key Application Generator not key in the deleted Effect is to Column value can to generate any code to column foreign key make the change. Foreign maintain referential value can value child table Key Column value integrity between any change row an does not change. -

2.4. Constraints
PostgreSQL 7.3 Documentation Prev Chapter 2. Data Definition Next 2.4. Constraints Data types are a way to limit the kind of data that can be stored in a table. For many applications, however, the constraint they provide is too coarse. For example, a column containing a product price should probably only accept positive values. But there is no data type that accepts only positive numbers. Another issue is that you might want to constrain column data with respect to other columns or rows. For example, in a table containing product information, there should only be one row for each product number. To that end, SQL allows you to define constraints on columns and tables. Constraints give you as much control over the data in your tables as you wish. If a user attempts to store data in a column that would violate a constraint, an error is raised. This applies even if the value came from the default value definition. 2.4.1. Check Constraints A check constraint is the most generic constraint type. It allows you to specify that the value in a certain column must satisfy an arbitrary expression. For instance, to require positive product prices, you could use: CREATE TABLE products ( product_no integer, name text, price numeric CHECK (price > 0) ); As you see, the constraint definition comes after the data type, just like default value definitions. Default values and constraints can be listed in any order. A check constraint consists of the key word CHECK followed by an expression in parentheses. The check constraint expression should involve the column thus constrained, otherwise the constraint would not make too much sense.