Understand and Troubleshoot Virtualized Domain Controller in Windows Server "8" Beta
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Supporting Operating System Installation | 3
cc01SupportingOperatingSystemInstallation.indd01SupportingOperatingSystemInstallation.indd PagePage 1 08/10/1408/10/14 4:334:33 PMPM martinmartin //208/WB01410/XXXXXXXXXXXXX/ch01/text_s208/WB01410/XXXXXXXXXXXXX/ch01/text_s Supporting Operating LESSON 1 System Installation 70-688 EXAM OBJECTIVE Objective 1.1 – Support operating system installation. This objective may include but is not limited to: Support Windows To Go; manage boot settings, including native virtual hard disk (VHD) and multi-boot; manage desktop images; customize a Windows installation by using Windows Preinstallation Environment (PE). LESSON HEADING EXAM OBJECTIVE Using a Troubleshooting Methodology Viewing System Information Using the Event Viewer Supporting Windows To Go Support Windows To Go Creating and Deploying a Windows To Go Workspace Drive Booting into a Windows To Go Workspace Managing Boot Settings Manage boot settings, including native virtual hard disk (VHD) and multi-boot Using BCDEdit and BCDBoot Configuring a Multi-Boot System Manage boot settings, including native virtual hard disk (VHD) and multi-boot Configuring a Native VHD Boot File Manage boot settings, including native virtual hard disk (VHD) and multi-boot Understanding VHD Formats Installing Windows 8.1 on a VHD with an Operating System Present Installing Windows 8.1 on a VHD Without an Operating SystemCOPYRIGHTED Present MATERIAL Managing Desktop Images Manage desktop images Capturing Images Modifying Images using DISM Customizing a Windows Installation by Using Windows PE Customize a Windows -

Windows 7 Bitlocker™ Drive Encryption Security Policy for FIPS 140-2 Validation
Windows 7 BitLocker™ Security Policy Page 1 of 16 Windows 7 BitLocker™ Drive Encryption Security Policy For FIPS 140-2 Validation For Windows 7 Document version 1.0 08/31/2011 1. Table of Contents 1. TABLE OF CONTENTS ......................................................................................................................... 1 2. INTRODUCTION .................................................................................................................................. 2 2.1 List of Cryptographic Modules ........................................................................................................................... 2 2.2 Brief Module Description ................................................................................................................................... 3 2.3 Validated Platforms ........................................................................................................................................... 4 3. INTEGRITY CHAIN OF TRUST .......................................................................................................... 4 4. CRYPTOGRAPHIC BOUNDARIES ..................................................................................................... 5 4.1 Overall Cryptographic Boundary........................................................................................................................ 5 4.2 BitLocker™ Components Included in the Boundary .......................................................................................... 5 4.3 Other Windows -
Internet Explorer 9 Features
m National Institute of Information Technologies NIIT White Paper On “What is New in Internet Explorer 9” Submitted by: Md. Yusuf Hasan Student ID: S093022200027 Year: 1st Quarter: 2nd Program: M.M.S Date - 08 June 2010 Dhaka - Bangladesh Internet Explorer History Abstract: In the early 90s—the dawn of history as far as the World Wide Web is concerned—relatively few users were communicating across this Internet Explorer 9 (abbreviated as IE9) is the upcoming global network. They used an assortment of shareware and other version of the Internet Explorer web browser from software for Microsoft Windows operating system. In 1995, Microsoft Microsoft. It is currently in development, but developer hosted an Internet Strategy Day and announced its commitment to adding Internet capabilities to all its products. In fulfillment of that previews have been released. announcement, Microsoft Internet Explorer arrived as both a graphical Web browser and the name for a set of technologies. IE9 will have complete or nearly complete support for all 1995: Internet Explorer 1.0: In July 1995, Microsoft released the CSS 3 selectors, border-radius CSS 3 property, faster Windows 95 operating system, which included built-in support for JavaScript and embedded ICC v2 or v4 color profiles dial-up networking and TCP/IP (Transmission Control support via Windows Color System. IE9 will feature Protocol/Internet Protocol), key technologies for connecting to the hardware accelerated graphics rendering using Direct2D, Internet. In response to the growing public interest in the Internet, Microsoft created an add-on to the operating system called Internet hardware accelerated text rendering using Direct Write, Explorer 1.0. -
Guidelines for Designing Embedded Systems with Windows 10 Iot Enterprise
Guidelines for Designing Embedded Systems with Windows 10 IoT Enterprise Version 2.0 Published July 15, 2016 Guidelines for designing embedded systems 1 CONFIDENTIAL Contents Overview .................................................................................................................................................................................................... 4 Building a task-specific experience ............................................................................................................................................ 4 General Group Policy settings ....................................................................................................................................................... 4 Application control ................................................................................................................................................................................ 5 Application boot options ................................................................................................................................................................. 5 Auto-boot Universal Windows apps ...................................................................................................................................... 5 Auto-boot Classic Windows apps ........................................................................................................................................... 5 Limit application access with AppLocker ............................................................................................................................... -

Security Policy Page 1 of 20
Security Policy Page 1 of 20 Security Policy This security policy contains data to configure services and network security based on the server’s role, as well as data to configure registry and auditing settings. Server: VENGWIN207 Services Service Name Startup Mode Description Issues, manages, and removes X.509 certificates for such applications such as Active Directory Certificate S/MIME and SSL. If the service is stopped, Disabled Services certificates will not be issued. If this service is disabled, any services that explicitly depend on it will fail to start. AD DS Domain Controller service. If this service is stopped, users will be unable to log Active Directory Domain Services Disabled on to the network. If this service is disabled, any services that explicitly depend on it will fail to start. AD FS Web Agent Authentication The AD FS Web Agent Authentication Service Disabled Service validates incoming tokens and cookies. Adobe Acrobat Updater keeps your Adobe Adobe Acrobat Update Service Automatic software up to date. Sends logging messages to the logging database when logging is enabled for the Active Directory Rights Management Services role. If this service is disabled or stopped AdRmsLoggingService Disabled when logging is enabled, logging messages will be stored in local message queues and sent to the logging database when the service is started. Processes application compatibility cache Application Experience Disabled requests for applications as they are launched Provides administrative services for IIS, for example configuration history and Application Pool account mapping. If this Application Host Helper Service Disabled service is stopped, configuration history and locking down files or directories with Application Pool specific Access Control Entries will not work. -

Page 1 of 2 KB296944
KB296944 - HOW TO: Use File Replication Service File and Folder Filters in Windows 2000 Page 1 of 2 Knowledge Base HOW TO: Use File Replication Service File and Folder Filters in Windows 2000 PSS ID Number: 296944 Article Last Modified on 10/28/2003 The information in this article applies to: l Microsoft Windows 2000 Server l Microsoft Windows 2000 Advanced Server This article was previously published under Q296944 IMPORTANT: This article contains information about modifying the registry. Before you modify the registry, make sure to back it up and make sure that you understand how to restore the registry if a problem occurs. For information about how to back up, restore, and edit the registry, click the following article number to view the article in the Microsoft Knowledge Base: 256986 Description of the Microsoft Windows Registry IN THIS TASK l SUMMARY l ¡ Overview ¡ Using Dfs File and Folder Filters ¡ Setting the File and Folder Filters on an FRS Replica in Active Directory ¡ n Setting Filters for Sysvol n Setting Filters for Dfs Replicas ¡ Using Registry Entries SUMMARY This article describes how to use file and folder filters for content that is replicated by the File Replication service (FRS). FRS is a multithreaded, multiple-master replication engine that replaces the LAN Manager Replication (LMREPL) service in Microsoft Windows NT versions 3.x and 4.0. Windows 2000-based domain controllers and servers use FRS to replicate system policies and logon scripts for Windows 2000-based and earlier clients. FRS can also replicate content between Windows 2000-based servers that host the same fault-tolerant distributed file system (Dfs) roots or child node replicas. -

Windows Poster 20-12-2013 V3
Microsoft® Discover the Open Specifications technical documents you need for your interoperability solutions. To obtain these technical documents, go to the Open Specifications Interactive Tiles: open specifications poster © 2012-2014 Microsoft Corporation. All rights reserved. http://msdn.microsoft.com/openspecifications/jj128107 Component Object Model (COM+) Technical Documentation Technical Documentation Presentation Layer Services Technical Documentation Component Object Model Plus (COM+) Event System Protocol Active Directory Protocols Overview Open Data Protocol (OData) Transport Layer Security (TLS) Profile Windows System Overview Component Object Model Plus (COM+) Protocol Active Directory Lightweight Directory Services Schema WCF-Based Encrypted Server Administration and Notification Protocol Session Layer Services Windows Protocols Overview Component Object Model Plus (COM+) Queued Components Protocol Active Directory Schema Attributes A-L Distributed Component Object Model (DCOM) Remote Protocol Windows Overview Application Component Object Model Plus (COM+) Remote Administration Protocol Directory Active Directory Schema Attributes M General HomeGroup Protocol Supplemental Shared Abstract Data Model Elements Component Object Model Plus (COM+) Tracker Service Protocol Active Directory Schema Attributes N-Z Peer Name Resolution Protocol (PNRP) Version 4.0 Windows Data Types Services General Application Services Services Active Directory Schema Classes Services Peer-to-Peer Graphing Protocol Documents Windows Error Codes ASP.NET -

Disabling Windows Logon Optimization
Network : connection failures during startup : disabling Windows logon optimization 379 Camille Garick Wed, May 13, 2020 Authentication Accounting Module AAM)™ 61 Warning Modify the registry at your own risk. EnvisionWare does not provide Windows support. Serious problems might occur if you modify the registry incorrectly by using Registry Editor or by using another method. These problems might require that you reinstall the operating system. We recommend that your Operating System support team undertake these changes. Microsoft optimized Windows to enhance the user experience by creating the impression that the operating system starts up faster. This is achieved by having the login prompt display before the network is fully initialized. Additionally, existing users may be logged in with cached credentials. Drawbacks in a domain or corporate environment are that login scripts might not run, drives and printers might not be mapped, policies might not get applied until after logon and GPO software distribution may be delayed. This logon optimization can affect some EnvisionWare Products. EnvisionWare products that make connections across a network may fail to start correctly if the application or associated Windows service starts before the network is fully initialized. We recommend turning off Windows Logon Optimization on PC’s where EnvisionWare products are running. The Logon optimization can be disabled in the following ways: 1. Via Local Policy - Computer Configuration\Administrative Templates\System\Logon\Always wait for the network at computer startup and logon 2. Via Group Policy - Computer Configuration\Administrative Templates\System\Logon\Always wait for the network at computer startup and logon 3. As a Policy via Windows registry - HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\CurrentVersion\Winlogon with registry value SyncForegroundPolicy=dword:00000001 4. -

Windows Server 2008 and Windows Vista Ebook
● ● ● ● ● ● ● ● ● ● ● How to access your CD files The print edition of this book includes a CD. To access the CD files, go to http://aka.ms/625143/files, and look for the Downloads tab. Note: Use a desktop web browser, as files may not be accessible from all ereader devices. Questions? Please contact: [email protected] Microsoft Press PUBLISHED BY Microsoft Press A Division of Microsoft Corporation One Microsoft Way Redmond, Washington 98052-6399 Copyright © 2008 by Derek Melber All rights reserved. No part of the contents of this book may be reproduced or transmitted in any form or by any means without the written permission of the publisher. Library of Congress Control Number: 2008920568 Printed and bound in the United States of America. 1 2 3 4 5 6 7 8 9 QWT 3 2 1 0 9 8 Distributed in Canada by H.B. Fenn and Company Ltd. A CIP catalogue record for this book is available from the British Library. Microsoft Press books are available through booksellers and distributors worldwide. For further infor- mation about international editions, contact your local Microsoft Corporation office or contact Microsoft Press International directly at fax (425) 936-7329. Visit our Web site at www.microsoft.com/mspress. Send comments to [email protected]. Microsoft, Microsoft Press, Active Desktop, Active Directory, ActiveX, BitLocker, Excel, FrontPage, HotStart, InfoPath, Internet Explorer, NetMeeting, OneNote, Outlook, PowerPoint, SideShow, Visio, Visual Basic, Visual Studio, Windows, Windows Live, Windows Media, Windows NT, Windows PowerShell, Windows Server, and Windows Vista are either registered trademarks or trademarks of Microsoft Corporation in the United States and/or other countries. -

AMP for Endpoints
Windows Process Starts Before AMP Connector Workaround - AMP for Endpoints Contents Introduction Requirements Components Used Limitations Background Information Troubleshoot Steps to delay a Windows service Delay the process with the command line Introduction This document describes the steps to troubleshoot in Advanced Malware Protection (AMP) for Endpoints when a Windows process starts before System Process Protection (SPP). Contributed by Nancy Perez and Uriel Torres, Cisco TAC Engineers. Requirements Cisco recommends that you have knowledge of these topics: ● Windows OS ● AMP connector's engines Components Used The information in this document is based on these software and hardware versions: ● Windows 10 device ● AMP connector 6.2.9 version The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command. Limitations This is a bug that affects the System Process Protection engine when a process starts before the AMP connector CSCvo90440. Background Information The AMP for Endpoints System Process Protection engine protects critical Windows system processes from memory injection attacks by other processes. In order to enable SPP, on the AMP console, navigate to Management > Policies > click on edit in the policy you want to modify > Modes and Engines > System Process Protection, here you can find three options: ● Protect: blocks attacks -
Windows XP Embedded Thin Client Manual
______________________________________________________________ Windows XP Embedded Thin Client Manual Version 1.2.1 ___________________________________________________________ Contents Contents Chapter 1 – Introduction 1 Overview 1 XPe File System 2 Chapter 2 - Startup and Configuration 2-1 Default Logon accounts 2-1 Logging On 2-1 XPe Management 2-3 1. Assign AutoLogon User 2-4 2. Setting Display Properties 2-4 3. Computer Management 2-5 4. XPe SNMP Control Utility 2-6 5. RAM Disk Size Properties 2-7 6. PopUp Main Menu 2-8 Network Connections 2-8 Microsoft Firewall 2-9 Chapter 3 - Applications 3-1 Installing New Applications / Device Drivers 3-1 Printer Driver Installation Example 3-1 Setup LPD printer on XPe 3-2 CITRIX Program Neighborhood 3-3 Remote Desktop Connection (RDP) 3-4 Internet Explorer 3-5 Kiosk Mode 3-6 Lock down IE using registry edits 3-6 TermPro Emulations 3-7 802.11a/b/g wireless adapter support 3-7 USB Device Support 3-7 GPEDIT (Group Edit) 3-7 SNMPadm - Remote Management 3-8 i Contents Chapter 4 – TermPro Emulations 4-1 Configure/Edit Sessions 4-3 Display Sessions 4-6 Printer Sessions 4-15 Using Emulation Sessions 4-20 Display Sessions 4-20 Printer Sessions 4-38 Appendix A – XPe Image Recovery A-1 Appendix B – Advanced Configuration Notes B-1 Expand User Access B-1 Auto-re-logon B-2 ii Introduction Chapter 1 – Introduction An overview of the XPe Thin Client is presented along with a description of its file system. Overview The XPe thin client, with its high quality, versatility, and flexibility, is an expandable high-performance terminal that gives users the ability to access Windows, Internet, multimedia, and legacy applications, at a lower total cost of ownership than PCs or other computing products. -
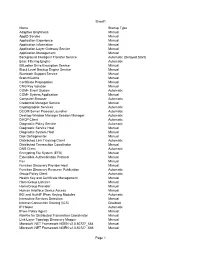
Tweakhound, Windows 7 Beta Default Services
Sheet1 Name Startup Type Adaptive Brightness Manual AppID Service Manual Application Experience Manual Application Information Manual Application Layer Gateway Service Manual Application Management Manual Background Intelligent Transfer Service Automatic (Delayed Start) Base Filtering Engine Automatic BitLocker Drive Encryption Service Manual Block Level Backup Engine Service Manual Bluetooth Support Service Manual BranchCache Manual Certificate Propagation Manual CNG Key Isolation Manual COM+ Event System Automatic COM+ System Application Manual Computer Browser Automatic Credential Manager Service Manual Cryptographic Services Automatic DCOM Server Process Launcher Automatic Desktop Window Manager Session Manager Automatic DHCP Client Automatic Diagnostic Policy Service Automatic Diagnostic Service Host Manual Diagnostic System Host Manual Disk Defragmenter Manual Distributed Link Tracking Client Automatic Distributed Transaction Coordinator Manual DNS Client Automatic Encrypting File System (EFS) Manual Extensible Authentication Protocol Manual Fax Manual Function Discovery Provider Host Manual Function Discovery Resource Publication Automatic Group Policy Client Automatic Health Key and Certificate Management Manual HomeGroup Listener Manual HomeGroup Provider Manual Human Interface Device Access Manual IKE and AuthIP IPsec Keying Modules Automatic Interactive Services Detection Manual Internet Connection Sharing (ICS) Disabled IP Helper Automatic IPsec Policy Agent Manual KtmRm for Distributed Transaction Coordinator Manual Link-Layer