CIS Microsoft Windows Server 2012 Benchmarkv1.0.0
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Since Sliced Bread?
Douglas A. Hamilton WINDOWS NT NT: The Greatest Thing Since Sliced Bread? T'S OFFICIAL. Windows unlike OS/2, is not the only product in the family. Right around the corner is the NT is finally out of the Chicago technology that Microsoft will be using in DOS 7.0 and Windows 4.0. Earli oven. The pricing has est betas for software developers are I scheduled for early fall and products been set and delivery dates based on it should be out in 1994. Chicago is a rewrite of the same Win32 have been promised. Those API (application programming interface) seen on NT. Compared with NT, it leaves promises (back in May) out the security (how many of us need government-certified C2 security on our were that the base system personal machines?), portability to RISC processors and the OS/2 character-mode would ship within 60 days and POSIX subsystems. And it wouldn't surprise me if Unicode support were trimmed out or if the networking were and the Advanced Server version would ship 30 days unbundled. What Chicago leaves in is 32- bit flat virtual memory, preemptive multi later. So there's every chance that by the time you read tasking, threads, pipes and semaphores all the really good stuff in Win32. That be this, there'll be piles of Windows NT packages at your comes Windows 4.0. Subtract the graphi cal user interface and you get DOS 7.0. local computer store. Is there anyone left who wonders why developers are so excited about NT? It's After a false rumor that Microsoft might price NT at not just because NT is expected to do ex tremely well. -

Windows NT Architecture Previous Screen Gilbert Held Payoff Windows NT Is a Sophisticated Operating System for Workstations and Network Servers
50-30-19 Windows NT Architecture Previous screen Gilbert Held Payoff Windows NT is a sophisticated operating system for workstations and network servers. This article helps network managers to understand the communications capability of workstations and servers running on Windows NT, and data base administrators to determine the suitability of this platform for a structured query language (SQL) data base server. Introduction Windows NT is a 32-bit, preemptive multitasking operating system that includes comprehensive networking capabilities and several levels of security. Microsoft markets two version of Windows NT: one for workstations—appropriately named Windows NT Workstation—and a second for servers—Windows NT Server. This article, which describes the workings of the NT architecture, collectively references both versions as Windows NT when information is applicable to both versions of the operating system. Similarly, it references a specific version of the operating system when the information presented is specific to either Windows NT Workstation or Windows NT Server. Architecture Windows NT consists of nine basic modules. The relationship of those modules to one another, as well as to the hardware platform on which the operating system runs, is illustrated in Exhibit 1. Windows NT Core Modules Hardware Abstraction Layer The hardware abstraction layer (HAL) is located directly above the hardware on which Windows NT operates. HAL actually represents a software module developed by hardware manufacturers that is bundled into Windows NT to allow it to operate on a specific hardware platform, such as Intel X86, DEC Alpha, or IBM PowerPC. HAL hides the specifics of the hardware platform from the rest of the operating system and represents the lowest level of Windows NT. -

Supporting Operating System Installation | 3
cc01SupportingOperatingSystemInstallation.indd01SupportingOperatingSystemInstallation.indd PagePage 1 08/10/1408/10/14 4:334:33 PMPM martinmartin //208/WB01410/XXXXXXXXXXXXX/ch01/text_s208/WB01410/XXXXXXXXXXXXX/ch01/text_s Supporting Operating LESSON 1 System Installation 70-688 EXAM OBJECTIVE Objective 1.1 – Support operating system installation. This objective may include but is not limited to: Support Windows To Go; manage boot settings, including native virtual hard disk (VHD) and multi-boot; manage desktop images; customize a Windows installation by using Windows Preinstallation Environment (PE). LESSON HEADING EXAM OBJECTIVE Using a Troubleshooting Methodology Viewing System Information Using the Event Viewer Supporting Windows To Go Support Windows To Go Creating and Deploying a Windows To Go Workspace Drive Booting into a Windows To Go Workspace Managing Boot Settings Manage boot settings, including native virtual hard disk (VHD) and multi-boot Using BCDEdit and BCDBoot Configuring a Multi-Boot System Manage boot settings, including native virtual hard disk (VHD) and multi-boot Configuring a Native VHD Boot File Manage boot settings, including native virtual hard disk (VHD) and multi-boot Understanding VHD Formats Installing Windows 8.1 on a VHD with an Operating System Present Installing Windows 8.1 on a VHD Without an Operating SystemCOPYRIGHTED Present MATERIAL Managing Desktop Images Manage desktop images Capturing Images Modifying Images using DISM Customizing a Windows Installation by Using Windows PE Customize a Windows -

Windows 7 Bitlocker™ Drive Encryption Security Policy for FIPS 140-2 Validation
Windows 7 BitLocker™ Security Policy Page 1 of 16 Windows 7 BitLocker™ Drive Encryption Security Policy For FIPS 140-2 Validation For Windows 7 Document version 1.0 08/31/2011 1. Table of Contents 1. TABLE OF CONTENTS ......................................................................................................................... 1 2. INTRODUCTION .................................................................................................................................. 2 2.1 List of Cryptographic Modules ........................................................................................................................... 2 2.2 Brief Module Description ................................................................................................................................... 3 2.3 Validated Platforms ........................................................................................................................................... 4 3. INTEGRITY CHAIN OF TRUST .......................................................................................................... 4 4. CRYPTOGRAPHIC BOUNDARIES ..................................................................................................... 5 4.1 Overall Cryptographic Boundary........................................................................................................................ 5 4.2 BitLocker™ Components Included in the Boundary .......................................................................................... 5 4.3 Other Windows -

System Requirements
Trend Micro Incorporated reserves the right to make changes to this document and to the products described herein without notice. Before installing and using the software, please review the readme files, release notes, and the latest version of the applicable user documentation, which are available from the Trend Micro website at: http://docs.trendmicro.com/en-us/enterprise/officescan.aspx Trend Micro, the Trend Micro t-ball logo, and OfficeScan are trademarks or registered trademarks of Trend Micro Incorporated. All other product or company names may be trademarks or registered trademarks of their owners. Copyright © 2017 Trend Micro Incorporated. All rights reserved. Release Date: October 2017 Protected by U.S. Patent No. 5,623,600; 5,889,943; 5,951,698; 6,119,165 Table of Contents Chapter 1: OfficeScan Server Installations Fresh Installations on Windows Server 2008 R2 Platforms .............................................................................................................................................................................. 1-2 Fresh Installations on Windows Server 2012 Platforms ..................................................................................................................................................................................... 1-3 Fresh Installations on Windows Server 2016 Platforms ..................................................................................................................................................................................... 1-4 Fresh Installations -
Guidelines for Designing Embedded Systems with Windows 10 Iot Enterprise
Guidelines for Designing Embedded Systems with Windows 10 IoT Enterprise Version 2.0 Published July 15, 2016 Guidelines for designing embedded systems 1 CONFIDENTIAL Contents Overview .................................................................................................................................................................................................... 4 Building a task-specific experience ............................................................................................................................................ 4 General Group Policy settings ....................................................................................................................................................... 4 Application control ................................................................................................................................................................................ 5 Application boot options ................................................................................................................................................................. 5 Auto-boot Universal Windows apps ...................................................................................................................................... 5 Auto-boot Classic Windows apps ........................................................................................................................................... 5 Limit application access with AppLocker ............................................................................................................................... -

Installing the IPM Client on Windows NT
CHAPTER 6 Installing the IPM Client on Windows NT IPM supports running only the IPM client software on a Windows NT system. However, you can run the IPM client on Windows NT with an IPM server that resides on a different operating system platform such as Sun Solaris. The IPM client software can be installed from the CD-ROM or it can be downloaded for installation using the IPM server’s web server. This chapter provides the following information about installing the IPM client software on Windows NT: • Requirements for the IPM Client on Windows NT on page 6-2 • Installing the IPM Client on Windows NT from the CD-ROM on page 6-3 • Installing the IPM Client on Windows NT Using the Web Server on page 6-4 • Verifying the IPM Client Installation on Windows NT on page 6-6 • Modifying the IPM Client Configuration on Windows NT on page 6-7 • Uninstalling the IPM Client on Windows NT on page 6-10 Installing the IPM Client on Windows NT 6-1 Requirements for the IPM Client on Windows NT Requirements for the IPM Client on Windows NT The following hardware and software is required to install the IPM client on a Windows NT system: • Windows NT version 4.0 with Service Pack 3 Note IPM software release 2.0 has not been tested with Windows NT Service Pack 4. • 64 MB RAM minimum (128 MB recommended) • 30 MB hard disk space Before you install the IPM client on a workstation running Windows NT, you should know the following information: • IPM server port number for the Naming server (the default is 44342) • Name of the host where the IPM server software is installed Tips The IPM server port number is obtained using the pkgparam -v CSCOcwbS | grep OSAGENT_PORT command on the Solaris server system. -
Level One Benchmark Windows NT 4.0 Operating Systems V1.0.5
Level One Benchmark Windows NT 4.0 Operating Systems V1.0.5 Copyright 2003, The Center for Internet Security www.cisecurity.org Page 2 of 32 Terms of Use Agreement Background. CIS provides benchmarks, scoring tools, software, data, information, suggestions, ideas, and other services and materials from the CIS website or elsewhere (“Products”) as a public service to Internet users worldwide. Recommendations contained in the Products (“Recommendations”) result from a consensus-building process that involves many security experts and are generally generic in nature. The Recommendations are intended to provide helpful information to organizations attempting to evaluate or improve the security of their networks, systems and devices. Proper use of the Recommendations requires careful analysis and adaptation to specific user requirements. The Recommendations are not in any way intended to be a “quick fix” for anyone’s information security needs. No representations, warranties and covenants. CIS makes no representations, warranties or covenants whatsoever as to (i) the positive or negative effect of the Products or the Recommendations on the operation or the security of any particular network, computer system, network device, software, hardware, or any component of any of the foregoing or (ii) the accuracy, reliability, timeliness or completeness of any Product or Recommendation. CIS is providing the Products and the Recommendations “as is” and “as available” without representations, warranties or covenants of any kind. User agreements. By using the Products and/or the Recommendations, I and/or my organization (“we”) agree and acknowledge that: 1. No network, system, device, hardware, software or component can be made fully secure; 2. -
Windows 95 & NT
Windows 95 & NT Configuration Help By Marc Goetschalckx Version 1.48, September 19, 1999 Copyright 1995-1999 Marc Goetschalckx. All rights reserved Version 1.48, September 19, 1999 Marc Goetschalckx 4031 Bradbury Drive Marietta, GA 30062-6165 tel. (770) 565-3370 fax. (770) 578-6148 Contents Chapter 1. System Files 1 MSDOS.SYS..............................................................................................................................1 WIN.COM..................................................................................................................................2 Chapter 2. Windows Installation 5 Setup (Windows 95 only)...........................................................................................................5 Internet Services Manager (Windows NT Only)........................................................................6 Dial-Up Networking and Scripting Tool....................................................................................6 Direct Cable Connection ..........................................................................................................16 Fax............................................................................................................................................17 Using Device Drivers of Previous Versions.............................................................................18 Identifying Windows Versions.................................................................................................18 User Manager (NT Only) .........................................................................................................19 -
Microsoft Windows Server 2012 R2
MICROSOFT WINDOWS SERVER 2012 R2 APPLICATION-FOCUSED SERVICES TOP 3 BENEFITS Windows Server 2012 R2 enables you to build and deploy applications in your data center that utilize higher-level, ❒4 Comprehensive Cloud Platform cloud-based application services and APIs that are ❒4 Cost Savings and Increased Efficiencies compatible with service provider clouds and Windows Azure. This functionality provides improved application ❒4 Support for a Modern Work Style portability between on-premises, public and partner- hosted clouds, increasing the flexibility and elasticity of your IT services. OPTIMIZE YOUR CLOUD BUSINESS Windows Server 2012 R2 also provides frameworks, With the world of IT changing rapidly, traditional services and tools to increase scalability and elasticity approaches to solving infrastructure problems are for multitenant-aware applications and websites. inadequate. The Microsoft vision for this new era of IT is to provide one consistent platform for infrastructure, apps, and data: the Cloud OS. The Cloud OS spans customer data centers, service provider data centers and the Microsoft PEOPLE WHO GET IT public cloud. At the heart of the solution is Windows Server 2012 R2. With Windows Server 2012 R2, you gain Along with your dedicated account manager, an enterprise-grade platform to cost-effectively optimize CDW has Microsoft trained and certified your business with a cloud. experts who can help find the right data center technologies for you, including: SIMPLE AND COST-EFFECTIVE DESIGN Windows Server 2012 R2 enables you to blend your Professional Services: on-premises solutions with the cloud without having • 500 engineers and project managers, to reengineer infrastructure, systems management or including 90+ Microsoft engineers applications. -

Disabling Windows Logon Optimization
Network : connection failures during startup : disabling Windows logon optimization 379 Camille Garick Wed, May 13, 2020 Authentication Accounting Module AAM)™ 61 Warning Modify the registry at your own risk. EnvisionWare does not provide Windows support. Serious problems might occur if you modify the registry incorrectly by using Registry Editor or by using another method. These problems might require that you reinstall the operating system. We recommend that your Operating System support team undertake these changes. Microsoft optimized Windows to enhance the user experience by creating the impression that the operating system starts up faster. This is achieved by having the login prompt display before the network is fully initialized. Additionally, existing users may be logged in with cached credentials. Drawbacks in a domain or corporate environment are that login scripts might not run, drives and printers might not be mapped, policies might not get applied until after logon and GPO software distribution may be delayed. This logon optimization can affect some EnvisionWare Products. EnvisionWare products that make connections across a network may fail to start correctly if the application or associated Windows service starts before the network is fully initialized. We recommend turning off Windows Logon Optimization on PC’s where EnvisionWare products are running. The Logon optimization can be disabled in the following ways: 1. Via Local Policy - Computer Configuration\Administrative Templates\System\Logon\Always wait for the network at computer startup and logon 2. Via Group Policy - Computer Configuration\Administrative Templates\System\Logon\Always wait for the network at computer startup and logon 3. As a Policy via Windows registry - HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows NT\CurrentVersion\Winlogon with registry value SyncForegroundPolicy=dword:00000001 4. -
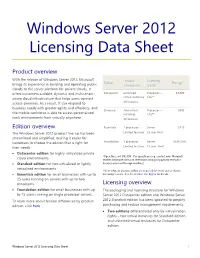
Windows Server 2012 Licensing Data Sheet
Windows Server 2012 Licensing Data Sheet Product overview With the release of Windows Server 2012, Microsoft Feature Licensing Edition Pricing* brings its experience in building and operating public comparison model clouds to the server platform for private clouds. It offers customers scalable, dynamic and multitenant- Datacenter Unlimited Processor + $4,809 aware cloud infrastructure that helps users connect virtual instances CAL** across-premises. As a result, IT can respond to All features business needs with greater agility and efficiency, and Standard Two virtual Processor + $882 the mobile workforce is able to access personalized instances CAL** work environments from virtually anywhere. All features Edition overview Essentials 2 processor Server $425 The Windows Server 2012 product line-up has been Limited features 25 user limit streamlined and simplified, making it easier for customers to choose the edition that is right for Foundation 1 processor Server OEM Only their needs. Limited features 15 user limit Datacenter edition for highly-virtualized private *Open No Level (NL) ERP. (For specific pricing, contact your Microsoft cloud environments. reseller. Microsoft does not determine pricing or payment terms for Standard edition for non-virtualized or lightly licenses acquired through resellers.) virtualized environments. **Client Access Licenses (CALs) are required for every user or device Essentials edition for small businesses with up to accessing a server. See the Product Use Rights for details. 25 users running on servers with up to two processors. Licensing overview Foundation edition for small businesses with up The packaging and licensing structure for Windows to 15 users running on single processor servers. Server 2012 Datacenter edition and Windows Server To learn more about feature differences by product 2012 Standard edition has been updated to simplify edition, click here.