Embedded Systems Design Lecture Notes B.Tech
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Cobia Database Articles Final Revision 2.0, 2-1-2017
Revision 2.0 (2/1/2017) University of Miami Article TITLE DESCRIPTION AUTHORS SOURCE YEAR TOPICS Number Habitat 1 Gasterosteus canadus Linné [Latin] [No Abstract Available - First known description of cobia morphology in Carolina habitat by D. Garden.] Linnaeus, C. Systema Naturæ, ed. 12, vol. 1, 491 1766 Wild (Atlantic/Pacific) Ichthyologie, vol. 10, Iconibus ex 2 Scomber niger Bloch [No Abstract Available - Description and alternative nomenclature of cobia.] Bloch, M. E. 1793 Wild (Atlantic/Pacific) illustratum. Berlin. p . 48 The Fisheries and Fishery Industries of the Under this head was to be carried on the study of the useful aquatic animals and plants of the country, as well as of seals, whales, tmtles, fishes, lobsters, crabs, oysters, clams, etc., sponges, and marine plants aml inorganic products of U.S. Commission on Fisheries, Washington, 3 United States. Section 1: Natural history of Goode, G.B. 1884 Wild (Atlantic/Pacific) the sea with reference to (A) geographical distribution, (B) size, (C) abundance, (D) migrations and movements, (E) food and rate of growth, (F) mode of reproduction, (G) economic value and uses. D.C., 895 p. useful aquatic animals Notes on the occurrence of a young crab- Proceedings of the U.S. National Museum 4 eater (Elecate canada), from the lower [No Abstract Available - A description of cobia in the lower Hudson Eiver.] Fisher, A.K. 1891 Wild (Atlantic/Pacific) 13, 195 Hudson Valley, New York The nomenclature of Rachicentron or Proceedings of the U.S. National Museum Habitat 5 Elacate, a genus of acanthopterygian The universally accepted name Elucate must unfortunately be supplanted by one entirely unknown to fame, overlooked by all naturalists, and found in no nomenclator. -

Common Errors in English by Paul Brians [email protected]
Common Errors in English by Paul Brians [email protected] http://www.wsu.edu/~brians/errors/ (Brownie points to anyone who catches inconsistencies between the main site and this version.) Note that italics are deliberately omitted on this page. What is an error in English? The concept of language errors is a fuzzy one. I'll leave to linguists the technical definitions. Here we're concerned only with deviations from the standard use of English as judged by sophisticated users such as professional writers, editors, teachers, and literate executives and personnel officers. The aim of this site is to help you avoid low grades, lost employment opportunities, lost business, and titters of amusement at the way you write or speak. But isn't one person's mistake another's standard usage? Often enough, but if your standard usage causes other people to consider you stupid or ignorant, you may want to consider changing it. You have the right to express yourself in any manner you please, but if you wish to communicate effectively you should use nonstandard English only when you intend to, rather than fall into it because you don't know any better. I'm learning English as a second language. Will this site help me improve my English? Very likely, though it's really aimed at the most common errors of native speakers. The errors others make in English differ according to the characteristics of their first languages. Speakers of other languages tend to make some specific errors that are uncommon among native speakers, so you may also want to consult sites dealing specifically with English as a second language (see http://www.cln.org/subjects/esl_cur.html and http://esl.about.com/education/adulted/esl/). -

What We Know About Testing Embedded Software
What we know about testing embedded software Vahid Garousi, Hacettepe University and University of Luxembourg Michael Felderer, University of Innsbruck Çağrı Murat Karapıçak, KUASOFT A.Ş. Uğur Yılmaz, ASELSAN A.Ş. Abstract. Embedded systems have overwhelming penetration around the world. Innovations are increasingly triggered by software embedded in automotive, transportation, medical-equipment, communication, energy, and many other types of systems. To test embedded software in a cost effective manner, a large number of test techniques, approaches, tools and frameworks have been proposed by both practitioners and researchers in the last several decades. However, reviewing and getting an overview of the entire state-of-the- art and the –practice in this area is challenging for a practitioner or a (new) researcher. Also unfortunately, we often see that some companies reinvent the wheel (by designing a test approach new to them, but existing in the domain) due to not having an adequate overview of what already exists in this area. To address the above need, we conducted a systematic literature review (SLR) in the form of a systematic mapping (classification) in this area. After compiling an initial pool of 560 papers, a systematic voting was conducted among the authors, and our final pool included 272 technical papers. The review covers the types of testing topics studied, types of testing activity, types of test artifacts generated (e.g., test inputs or test code), and the types of industries in which studies have focused on, e.g., automotive and home appliances. Our article aims to benefit the readers (both practitioners and researchers) by serving as an “index” to the vast body of knowledge in this important and fast-growing area. -

Massachusetts Institute of Technology Bulletin
d 7I THE DEAN OF SCIEN<C OCT 171972 MASSACHUSETTS INSTITUTE OF TECHNOLOGY BULLETIN REPORT OF THE PRESIDENT 1971 MASSACHUSETTS INSTITUTE OF TECHNOLOGY BULLETIN REPORT OF THE PRESIDENT FOR THE ACADEMIC YEAR 1970-1971 MASSACHUSETTS INSTITUTE OF TECHNOLOGY BULLETIN VOLUME 107, NUMBER 2, SEPTEMBER, 1972 Published by the Massachusetts Institute of Technology 77 MassachusettsAvenue, Cambridge, Massachusetts, five times yearly in October, November, March, June, and September Second class postage paid at Boston, Massachusetts. Issues of the Bulletin include REPORT OF THE TREASURER REPORT OF THE PRESIDENT SUMMER SESSION CATALOGUE PUBLICATIONS AND THESES and GENERAL CATALOGUE Send undeliverable copies and changes of address to Room 5-133 Massachusetts Institute of Technology Cambridge,Massachusetts 02139. THE CORPORATION Honorary Chairman:James R. Killian, Jr. Chairman:Howard W. Johnson President:Jerome B. Wiesner Chancellor: Paul E. Gray Vice Presidentand Treasurer:Joseph J. Snyder Secretary:John J. Wilson LIFE MEMBERS Bradley Dewey, Vannevai Bush, James M. Barker, Thomas C. Desmond, Marshall B. Dalton, Donald F. Carpenter, Thomas D. Cabot, Crawford H. Greenewalt, Lloyd D. Brace, William A. Coolidge, Robert C. Sprague, Charles A. Thomas, David A. Shepard, George J. Leness, Edward J. Hanley, Cecil H. Green, John J. Wilson, Gilbert M. Roddy, James B. Fisk, George P. Gardner, Jr., Robert C. Gunness, Russell DeYoung, William Webster, William B. Murphy, Laurance S. Rockefeller, Uncas A. Whitaker, Julius A. Stratton, Luis A. Ferr6, Semon E. Knudsen, Robert B. Semple, Ir6n6e du Pont, Jr., Eugene McDermott, James R. Killian, Jr. MEMBERS Albert H. Bowker, George P. Edmonds, Ralph F. Gow, Donald A. Holden, H. I. Romnes, William E. -

Embedded Sensors System Applied to Wearable Motion Analysis in Sports
Embedded Sensors System Applied to Wearable Motion Analysis in Sports Aurélien Valade1, Antony Costes2, Anthony Bouillod1,3, Morgane Mangin4, P. Acco1, Georges Soto-Romero1,4, Jean-Yves Fourniols1 and Frederic Grappe3 1LAAS-CNRS, N2IS, 7, Av. du Colonel Roche 31077, Toulouse, France 2University of Toulouse, UPS, PRiSSMH, Toulouse, France 3EA4660, C3S - Université de Franche Comté, 25000 Besançon, France 4 ISIFC – Génie Biomédical - Université de Franche Comté, 23 Rue Alain Savary, 25000 Besançon, France Keywords: IMU, FPGA, Motion Analysis, Sports, Wearable. Abstract: This paper presents two different wearable motion capture systems for motion analysis in sports, based on inertial measurement units (IMU). One system, called centralized processing, is based on FPGA + microcontroller architecture while the other, called distributed processing, is based on multiple microcontrollers + wireless communication architecture. These architectures are designed to target multi- sports capabilities, beginning with tri-athlete equipment and thus have to be non-invasive and integrated in sportswear, be waterproofed and autonomous in energy. To characterize them, the systems are compared to lab quality references. 1 INTRODUCTION electronics (smartphones, game controllers...), in an autonomous embedded system to monitor the Electronics in sports monitoring has been a growing sportive activity, even in field conditions. field of studies for the last decade. From the heart rate Our IMU based monitoring system allows monitors to the power meters, sportsmen -

Embedded Systems Supporting by Different Operating Systems
A Survey: Embedded Systems Supporting By Different Operating Systems Qamar Jabeen, Fazlullah Khan, Muhammad Tahir, Shahzad Khan, Syed Roohullah Jan Department of Computer Science, Abdul Wali Khan University Mardan [email protected], [email protected] -------------------------------------------------------------------------------------------------------------------------------------- Abstract: In these days embedded systems used in industrial, commercial system have an important role in different areas. e.g Mobile Phones and different Fields and applications like Network type of Network Bridges are embedded embedded system , Real-time embedded used by telecommunication systems for systems which supports the mission- giving better requirements to their users. critical domains, mostly having the time We use digital cameras, MP3 players, DVD constraints, Stand-alone systems which players are the example of embedded includes the network router etc. A great consumer electronics. In our daily life its deployment in the processors made for provided us efficiency and flexibility and completing the demanding needs of the many features which includes microwave users. There is also a large-scale oven, washing machines dishwashers. deployment occurs in sensor networks for Embedded system are also used in providing the advance facilities, for medical, transportation and also used in handled such type of embedded systems wireless sensor network area respectively a specific operating system must provide. medical imaging, vital signs, automobile This paper presents some software electric vehicles and Wi-Fi modules. infrastructures that have the ability of supporting such types of embedded systems. 1. Introduction: Embedded system are computer systems designed for specific purpose, to increase functionality and reliability for achieving a specific task, like general Figure 1: Taxonomy of Embedded Software’s purpose computer system it does not use for multiple tasks. -

New Approach for Testing and Providing Security Mechanism for Embedded Systems
Available online at www.sciencedirect.com ScienceDirect Procedia Computer Science 78 ( 2016 ) 851 – 858 International Conference on Information Security & Privacy (ICISP2015), 11-12 December 2015, Nagpur, INDIA New Approach for Testing and providing Security Mechanism for Embedded Systems Swapnili P. Karmorea, Anjali R. Mahajanb Research Scholar, Department of Computer Science and enginnering, G. H. Raisoni College of Engineering, Nagpur, India. Head, Department of Information Technology, Government Polytechnic, Nagpur, India. Abstract Assuring the quality of embedded system is posing a big challenge for software testers around the globe. Testing of one embedded system widely differs from another. The approach presented in the paper is used for the testing of safety critical feature of embedded system. The input and outputs are trained validated and tested via ANN. Security is provided via skipping invalid and critical classes and by embedding secret key in the Ram of embedded device. The work contributes simulating environment where cost and time required for testing of embedded systems will be minimized, which removes drawback of traditional approaches. Keywords: Embedded system testing; Black box testing; Safety critical embedded systems; Artificial neural network. 1. Introduction Testing is the most common process used to determine the quality and providing security for embedded systems. In the embedded world, testing is an immense challenge. In the test plan, the distinguished characteristics of embedded systems must be reflected as these are application specific. They give embedded system exclusive and distinct flavor. Real-time systems have to meet the challenge of assuring the correct implementation of an application not only dependent upon its logical accuracy, but also its ability to meet the constraints of timing. -

Objective Is
Lehigh Preserve Institutional Repository Design of a microprocessor-based emulsion polymerization process control facility Dimitratos, John N. 1987 Find more at https://preserve.lib.lehigh.edu/ This document is brought to you for free and open access by Lehigh Preserve. It has been accepted for inclusion by an authorized administrator of Lehigh Preserve. For more information, please contact [email protected]. Design of a Microprocessor-based Emulsion Polymerization Process Control Facility A research report written in partial fulfillment of the requirements for the degree of Master of Science in Chemical F:ngim·ering, Lehigh University, Bethlehem, Pennsylvania by John N. Dimitratos June 1987 ,. Design of a Microprocessor-based Emulsion Polymerization .. ,_.,,-•• ·, ,, -i •:>:.·.:':' Process Control Facility ' A research report written in partial fulfillment of the requirements for the degree of Master of Science in Chemical Engineering, Lehigh University, Bethlehem, Pennsylvania by John N. Dimitratos June 1987 •1 to my father and my brother there art times when it is hard to decide what should be chosen at what price, and what endured in return for what reward. Perhaps it is still harder to stick to the decision Aristotle (384-322 B.C) Ethics, Book Ill. Abstract The explosion of microcomputer technology and the recent developments in software and hardware products introduce a new horizon of capabilities for the process control engineer. However, taking advantage of this new technology is not something easily done. H the process control engineer has to undertake such a project soon he will have to deal with the different languages the software engineer and the plant operator use. -
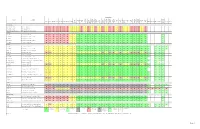
Operating System Support Matrix
Operating System Win Win Win Win Win Win Win Win THEOS Product Description Win Win Win Win Windows Win XP Win XP Server Server Server Server Server Server Win 7 Win 7 Win 8 Win 8 Server Server Win 8.1 Win 8.1 Corona DOS Win 3.x Win NT4 Win 95 Win 98 Win 98SE Win Me Win 2000 Server Server Vista Vista Thin a Mac 8.6+ QNX 6.2 THEOS SCO 5.07 SCO 6.0 32 64 2003 2003 R2 2003 R2 2008 2008 2008 R2 32 64 32 64 2012 2012 R2 32 64 Linux Ver. 5.0 2000 2003 64 32 64 Client 32 32 64 32 64 64 64 64 PL182 USB-Serial Links USB-Serial Link 2-232-DB9 Two RS-232, 9-pin DB-9s USB-Serial Link 4-232-DB9 Four RS-232, 9-pin DB-9s USB-Serial Link 4-232-DB9 Cabled Four RS-232, 9-pin DB-9s with fan-out cable Serial PCIe SSerial-PCIe One 25-pin port, 16550 UART SSerial-PCIe/LP One 25-pin port, 16550 UART, low-profile DSerial-PCIe Two 9-pin ports, 16550 UARTs DSerial-PCIe/LP Two 9-pin ports, 16550 UARTs, low-profile Quattro-PCIe Four 9-pin ports, 16550 UARTs Serial PCI SSerial-PCI One 9-pin port, 16550 UART ? SSerial-PCI/LP One 25-pin port, 16550 UART, low-profile ? RS422 SS-PCI One 9-pin port, 16550 UART, RS-422 pinout ? LavaPort-650 One 9-pin port, 16650 UART ? DSerial-PCI Two 9-pin ports, 16550 UARTs -
What Is Embedded Computing?
EMBEDDED COMPUTING more stringent cost and power con- straints. PDA design requires careful What Is Embedded attention to both hardware and soft- ware. In the next decade, some micro- processors, largely invisible to users, Computing? will be used for signal processing and control—for example, to enable home Wayne Wolf, Princeton University networking across noisy, low-quality media such as power lines. Others will be used to create advanced user inter- or those who think a lot about embedded computing, as well as Evolving from a craft to an the uninitiated, it’s important to engineering discipline over F define exactly what the term means. In brief, an embedded the past decade, embedded system is any computer that is a com- ponent in a larger system and that relies computing continues to on its own microprocessor. mature. But is embedded computing a field or just a fad? The purpose of this new bimonthly column is to give researchers difficult to implement in mechanical faces—for example, for the entire clus- as well as practitioners an opportunity controllers. ter of home entertainment devices. to demonstrate that embedded com- Laser and inkjet printers also Microprocessors have also enabled puting is an established engineering dis- emerged in the 1980s. Print engines new categories of portable devices cipline with principles and knowledge require computational support for that will assume roles and perform at its core. both typesetting and real-time control. functions yet to be determined. The First, users generate characters and cell phone and PDA combinations A LONG HISTORY lines that a computation must convert that hit the market in 2001 are a People have been building embedded into pixels. -

Embedded Hardware
Lecture #2 Embedded Hardware 18-348 Embedded System Engineering Philip Koopman Friday, 15-Jan-2016 Electrical& Computer ENGINEERING © Copyright 2006-2016, Philip Koopman, All Rights Reserved Announcements Many posted materials are accessible only from a CMU IP Address • Look for this on course web page: If you can't access a file due to access restrictions, you need to get a campus IP address for your web browsing requests. Use Cisco VPN Anyconnect... Course web page has schedules, assignments, other important info • http://www.ece.cmu.ecu/~ece348 • Blackboard will have grades, announcements, sample tests • Look at blackboard announcements before sending e-mail to course staff Lab board handouts in progress • See Blackboard/admin page for TA office hours • OK to go to any scheduled lab section (but, give priority to scheduled students) • For Friday prelab give a good faith attempt to get things working by the deadline – If you hit a showstopper get it fixed on Tuesday so you can do Prelab 2 on time. 2 Design Example: Rack-Mount Power Supply Power supply for server • AC to DC conversion (750-1000W) • Coordinates 2 redundant supplies to maximize uptime • Safeguard against power problems (under/over-voltage; over-current; over-temp) Typical approach: • General microcontroller for AC, alarms, housekeeping • DSP runs control loop on DC side at > 10 KHz to provide stable DC http://accessories.us.dell.com Dell 870W Power Supply for PowerEdge R710 Server power Key requirement: “Doesn’t emit smoke” 3 Apple USB Power Adapter Teardown iPhone -

Embedded Smart Health Monitoring System-Wearable Devices
Volume 4, Issue 5, May – 2019 International Journal of Innovative Science and Research Technology ISSN No:-2456-2165 Embedded Smart Health Monitoring System-Wearable Devices A Sushmitha, Anusha N S, Anusha S Raj Vidyashree. C Student, Dept of ECE, Assistant Professor, Dept of ECE, Dr. Ambedkar Institute of Technology, Dr. Ambedkar Institute of Technology, Bangalore, India. Bangalore, India. Abstract:- This paper gives an insight towards current The objective of developing monitoring systems is to trends and employed methodologies in wearable device reduce health care costs by reducing physician office visits, technology. In the present era it is essential to design a hospitalizations, and diagnostic testing procedure. The cost-effective healthcare system as it is essential to make doctors can continuously monitor the health of the patients the smart health systems available to all the people from any location. around the world. In this project we have developed a healthcare monitoring system which bears the track of II. OVERVIEW patient’s exercising postures, breathing patterns, glucose level detection along with the implementation of A wearable health monitoring system are being Peltier. With the advancement of technology and usage beneficial to common people as well as the health care of Cloud computing, it becomes easy for updation of systems in maintaining the patient‟s activeness or fitness these measured data. This automatic updation of data level and also for self-health tracking. The usage of prevents all the errors which can be caused by embedded systems along the recent technologies such as manually entering the data. IoT and Cloud Computing in healthcare systems has widened the scope of assessing the health of an individual Keywords:- Cloud, Wearable Device, Embedded patient‟s health conditions.