An Improved Algorithm for Computing Logarithms Over GF(P)
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

New Algorithms and Architectures for Arithmetic in GF (2 M) Suitable For
AN ABSTRACT OF THE THESIS OF Francisco RodrIguez-HenrIquez for the degree of Doctor of Philosophy in Electrical & Computer Engineering presented on June 07, 2000. Title:New Algorithms and Architectures for Arithmetic in GF(2m Suitable for Elliptic Curve Cryptography Redacted for Privacy Abstract approved: cetin K. Koç During the last few years we have seen formidable advances in digital and mo- bile communication technologies such as cordless and cellular telephones, personal communication systems, Internet connection expansion, etc. The vast majority of digital information used in all these applications is stored and also processed within a computer system, and then transferred between computers via fiber optic, satellite systems, and/or Internet. In all these new scenarios, secure information transmission and storage has a paramount importance in the emerging interna- tional information infrastructure, especially, for supporting electronic commerce and other security related services. The techniques for the implementation of secure information handling and management are provided by cryptography, which can be succinctly defined as the study of how to establish secure communication in an adversarial environ- ment. Among the most important applications of cryptography, we can mention data encryption, digital cash, digital signatures, digital voting, network authenti- cation, data distribution and smart cards. The security of currently used cryptosystems is based on the computational complexity of an underlying mathematical problem, such as factoring largenum- bers or computing discrete logarithms for large numbers. These problems,are believed to be very hard to solve. In the practice, only a small number of mathe- matical structures could so far be applied to build public-key mechanisms. -
LAN Crypto Submission to the ECRYPT Stream Cipher Project
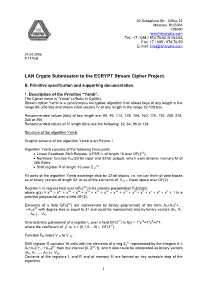
22 Schepkina Str., Office 22 Moscow, RUSSIA 129090 www.lancrypto.com Tel.: +7 / 095 / 974.76.60 /61/62/63 Fax: +7 / 095 / 974.76.59 E-mail: [email protected] 24.04.2005 # 7175-B LAN Crypto Submission to the ECRYPT Stream Cipher Project. B. Primitive specification and supporting documentation. 1. Description of the Primitive “Yamb”. The Cipher name is “Yamb” («Ямб» in Cyrillic) Stream cipher Yamb is a synchronous encryption algorithm that allows keys of any length in the range 80–256 bits and allows initial vectors IV of any length in the range 32-128 bits. Recommended values (bits) of key length are: 80, 96, 112, 128, 144, 160, 176, 192, 208, 224, 240 or 256 Recommended values of IV length (bits) are the following: 32, 64, 96 or 128. Structure of the algorithm Yamb. Graphic scheme of the algorithm Yamb is on Picture 1. Algorithm Yamb consists of the following three parts: • Linear Feedback Shift Register (LFSR) L of length 15 over GF(232), • Nonlinear function FM,(32-bit input and 32-bit output), which uses dinamic memory M of 256 Bytes, 32 • Shift register R of length 16 over Z 2 . All parts of the algorithm Yamb exchange data by 32-bit blocks, i.e. we can think of data blocks as of binary vectors of length 32, or as of the elements of V32 – linear space over GF(2). 32 Register L is represented over GF(2 ) in its canonic presentation F2[x]/g(x), where g(x) = x32 + x27 + x24 + x20 + x19 + x17 + x16 + x12 + x10 + x9 + x8 + x7 + x6 + x3 + 1 is a primitive polynomial over a field GF(2). -

Automatické Hledání Závislostí U Proudových Šifer Projektu Estream
MASARYKOVA UNIVERZITA F}w¡¢£¤¥¦§¨ AKULTA INFORMATIKY !"#$%&'()+,-./012345<yA| Automatické hledání závislostí u proudových šifer projektu eStream DIPLOMOVÁ PRÁCA Matej Prišt’ák Brno, Jaro 2012 Prehlásenie Prehlasujem, že táto diplomová práca je mojím pôvodným autorským dielom, ktoré som vypracoval samostatne. Všetky zdroje, pramene a literatúru, ktoré som pri vypracovaní po- užíval alebo z nich ˇcerpal,v práci riadne citujem s uvedením úplného odkazu na príslušný zdroj. Vedúci práce: Petr Švenda ii Pod’akovanie Rád by som pod’akoval v prvom rade vedúcemu práce RNDr. Petrovi Švendovi, Ph.D. za odborné vedenie, pravidelné zhodnotenie a pripomienky k práci. Pod’akovanie patrí aj ko- legovi Ondrejovi Dubovcovi za spoluprácu pri úpravách použitej aplikácie. Nakoniec by som chcel pod’akovat’ celej mojej rodine a priatel’ke Zuzke za podporu a trpezlivost’ poˇcas písania tejto práce. iii Zhrnutie Ciel’om práce je príprava existujúcich implementácií širšieho okruhu kandidátov na prú- dovú šifru v rámci projektu eSTREAM do jednotného rozhrania tak, aby bolo možné auto- matické hl’adanie nežiadúcich závislostí vo výstupe (ktoré by sa nemali vyskytovat’) všet- kých týchto kandidátnych funkcií naraz. Pre automatické hl’adanie bol využitý existujúci nástroj využívajúci techniky evoluˇcnýchobvodov. K dispozícii bola možnost’ spúšt’at’ vý- poˇctydistribuovane pomocou nástroja BOINC s využitím laboratórnych poˇcítaˇcov. Imple- mentaˇcnáˇcast’ je doplnená analýzou a diskusiou získaných výsledkov a porovnaním úspeš- nosti hl’adania závislostí evoluˇcnýmobvodom verzus závislosti nájdené bežnými batériami pre štatistické testovanie výstupu dát (Diehard a NIST). iv Kl’úˇcovéslová genetický algoritmus, genetic algorithm, prúdová šifra, stream cipher, ECRYPT, eSTREAM, kryptoanalýza, cryptoanalysis, štatistické testovanie, statistical testing v Obsah 1 Úvod .............................................1 2 Definícia pojmov ......................................2 2.1 Genetický algoritmus .................................2 2.1.1 Initializer . -

Ethnic and Religious Minorities in Stalin's Soviet Union: New Dimensions of Research
Ethnic and Religious Minorities in Stalin’s Soviet Union New Dimensions of Research Edited by Andrej Kotljarchuk Olle Sundström Ethnic and Religious Minorities in Stalin’s Soviet Union New Dimensions of Research Edited by Andrej Kotljarchuk & Olle Sundström Södertörns högskola (Södertörn University) Library SE-141 89 Huddinge www.sh.se/publications © Authors Attribution 4.0 International (CC BY 4.0) This publication is licensed under a Creative Commons Attribution 4.0 License. Cover image: Front page of the Finnish-language newspaper Polarnoin kollektivisti, 17 December 1937. Courtesy of Russian National Library. Graphic form: Per Lindblom & Jonathan Robson Printed by Elanders, Stockholm 2017 Södertörn Academic Studies 72 ISSN 1650-433X Northern Studies Monographs 5 ISSN 2000-0405 ISBN 978-91-7601-777-7 (print) Contents List of Illustrations ........................................................................................................................ 7 Abbreviations ................................................................................................................................ 9 Foreword ...................................................................................................................................... 13 Introduction ................................................................................................................................. 15 ANDREJ KOTLJARCHUK & OLLE SUNDSTRÖM PART 1 National Operations of the NKVD. A General Approach .................................... 31 CHAPTER 1 The -
The Estream Project
The eSTREAM Project Matt Robshaw Orange Labs 11.06.07 Orange Labs ECRYPT An EU Framework VI Network of Excellence > 5 M€ over 4.5 years More than 30 european institutions (academic and industry) ECRYPT activities are divided into Virtual Labs Which in turn are divided into Working Groups General SPEED eSTREAM Assembly Project Executive Strategic Coordinator Mgt Comm. Committee STVL AZTEC PROVILAB VAMPIRE WAVILA WG1 WG2 WG3 WG4 The eSTREAM Project – Matt Robshaw (2) Orange Labs 1 Cryptography (Overview!) Cryptographic algorithms often divided into two classes Symmetric (secret-key) cryptography • Participants using secret-key cryptography share the same key material Asymmetric (public-key) cryptography • Participants using public-key cryptography use different key material Symmetric encryption can be divided into two classes Block ciphers Stream ciphers The eSTREAM Project – Matt Robshaw (3) Orange Labs Stream Ciphers Stream encryption relies on the generation of a "random looking" keystream Encryption itself uses bitwise exclusive-or 0110100111000111001110000111101010101010101 keystream 1110111011101110111011101110111011100000100 plaintext 1000011100101001110101101001010001001010001 ciphertext Stream encryption offers some interesting properties They offer an attractive link with perfect secrecy (Shannon) No data buffering required Attractive error handling and propagation (for some applications) How do we generate keystream ? The eSTREAM Project – Matt Robshaw (4) Orange Labs 2 Stream Ciphers in a Nutshell Stream ciphers -

On Statistical Analysis of Synchronous Stream Ciphers
ON STATISTICAL ANALYSIS OF SYNCHRONOUS STREAM CIPHERS MELTEM SONMEZ¨ TURAN APRIL 2008 ON STATISTICAL ANALYSIS OF SYNCHRONOUS STREAM CIPHERS A THESIS SUBMITTED TO THE GRADUATE SCHOOL OF APPLIED MATHEMATICS OF THE MIDDLE EAST TECHNICAL UNIVERSITY BY MELTEM SONMEZ¨ TURAN IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF DOCTOR OF PHILOSOPHY IN THE DEPARTMENT OF CRYPTOGRAPHY APRIL 2008 Approval of the Graduate School of Applied Mathematics Prof. Dr. Ersan AKYILDIZ Director I certify that this thesis satisfies all the requirements as a thesis for the degree of Doctor of Philosophy. Prof. Dr. Ferruh OZBUDAK¨ Head of Department This is to certify that we have read this thesis and that in our opinion it is fully adequate, in scope and quality, as a thesis for the degree of Doctor of Philosophy. Assoc. Prof. Dr. Ali DOGANAKSOY˘ Supervisor Examining Committee Members Prof. Dr. Ersan AKYILDIZ Prof. Dr. Ferruh OZBUDAK¨ Prof. Dr. Semih Koray Assoc. Prof. Dr. Ali DOGANAKSOY˘ Dr. Orhun KARA I hereby declare that all information in this document has been obtained and presented in accordance with academic rules and ethical conduct. I also declare that, as required by these rules and conduct, I have fully cited and referenced all material and results that are not original to this work. Name, Last name : Signature : iii Abstract ON STATISTICAL ANALYSIS OF SYNCHRONOUS STREAM CIPHERS S¨onmez Turan, Meltem Ph.D., Department of Cryptography Supervisor: Assoc. Prof. Ali Do˘ganaksoy April 2008, 146 pages Synchronous stream ciphers constitute an important class of symmetric ciphers. After the call of the eSTREAM project in 2004, 34 stream ciphers with different design approaches were proposed. -

High-Speed and Secure PRNG for Cryptographic Applications
I. J. Computer Network and Information Security, 2020, 3, 1-10 Published Online June 2020 in MECS (http://www.mecs-press.org/) DOI: 10.5815/ijcnis.2020.03.01 High-Speed and Secure PRNG for Cryptographic Applications Zhengbing Hu School of Educational Information Technology, Central China Normal University, Wuhan, China E-mail: [email protected] Sergiy Gnatyuk, Tetiana Okhrimenko Faculty of Cybersecurity, Computer and Software Engineering, National Aviation University, Kyiv, Ukraine E-mail: [email protected], [email protected] Sakhybay Tynymbayev Almaty University of Power Engineering and Telecommunication, Almaty, Kazakhstan E-mail: [email protected] Maksim Iavich Scientific Cyber Security Association, Caucasus University, Tbilisi, Georgia E-mail: [email protected] Received: 24 March 2020; Accepted: 30 March 2020; Published: 08 June 2020 Abstract—Due to the fundamentally different approach underlying quantum cryptography (QC), it has not only I. INTRODUCTION become competitive, but also has significant advantages With the rapid development of information and over traditional cryptography methods. Such significant communication technologies (ICT), most of the world is advantage as theoretical and informational stability is faced with the problem of supporting cybersecurity achieved through the use of unique quantum particles and the inviolability of quantum physics postulates, in addition it (information security). On the one hand, new powerful ICT does not depend on the intruder computational capabilities. contribute to the cybersecurity development, and on the other, they create new threats. For the past few years, However, even with such impressive reliability results, QC number of reported cybersecurity incidents of confidential methods have some disadvantages. For instance, such information leaks increases every month. -

A Secure Communication Platform Based on Gemstone Yanjiao Chen, Jian Wang, and Ruming Yin Bo Liang
201O 3rd InternationalConference on AdvancedComputer Theoryand Engineering(ICACTE) A Secure Communication Platform Based on Gemstone Yanjiao Chen, Jian Wang, and Ruming Yin Bo Liang Dept. of Electronic Engineering, Tsinghua University AQSIQ Information Center Beijing 100084, China Beijing 100088, China [email protected] [email protected] Abstract-In this paper, we have implemented a secure FUBUKI based on a non-secure pseudo-random number communication platform based on a new stream cipher called generator (the mother generator) [9]. Gemstone which stems from coupled map lattices (CML), a Gemstone is also a candidate of eSTREAM, motivated nonlinear system of coupled chaotic maps. On the platform, we have realized duplex text, image and voice transmission. We by coupled map lattice (CML), a real-valued nonlinear have also analyzed the randomness of the keystream generated system of coupled chaotic maps [10]. While preserving good by the platform based on the statistical tests suggested by the confusion and diffusion property of CML, Gemstone National Institute of Standards and Technology (NIST). The properly discretizes the CML, improving the security as well test results are compared with other four stream ciphers'. as the performance. In addition, Gemstone is robust against Moreover, a series of experiments of duplex text, image and voice transmissions were made through university local IV setup attacks since there are no high probability network. Both the statistical test and the transmission difference propagations or high correlations over the IV experiments have shown that the platform is highly secure with setup scheme [10]. fast encryption speed, which confirms that the Gemstone In this paper, we have built a secure communication platform is promising for cryptographic applications. -

Latin Dances Revisited: New Analytic Results of Salsa20 and Chacha”
Modified version of “Latin Dances Revisited: New Analytic Results of Salsa20 and ChaCha” Tsukasa Ishiguro KDDI R&D Laboratories Inc. 2-1-15 Ohara, Fujimino, Saitama 356-8502, Japan [email protected] 1 Contents of modification This paper is a modified version of own paper “Latin Dances Revisited: New Analytic Results of Salsa20 and ChaCha” presented in ICICS2011. In the original paper, there are incorrect data because of software bug in the experimental program. Therefore, we conducted with a correct program. Additionally, we modified the algorithm with a view to improvement of analysis precision. Table1 shows the maximum values per round of Salsa20 and ChaCha, and output of Mersenne Twister as PRF. This table show there are no double bit biases of 5 or more round Salsa20 and ChaCha (see Section 4). Therefore, these ciphers are not presently under threat. Table 1. Double bit differentials of Salsa20 ∆0 ∆r ∆r j"ej Type Round Key length [ i ] j [ p]q [ s]t d ∆0 ∆4 ∆4 Salsa20 4 256 [ 8]17 [ 6]23 [ 7]0 0.177887 Salsa20 5 256 - - - Not Found Salsa20 6 256 - - - Not Found Salsa20 7 256 - - - Not Found Salsa20 8 256 - - - Not Found Salsa20 9 256 - - - Not Found ChaCha 4 256 - - - Not Found ChaCha 5 256 - - - Not Found ChaCha 6 256 - - - Not Found ChaCha 7 256 - - - Not Found ChaCha 8 256 - - - Not Found Latin Dances Revisited: New Analytic Results of Salsa20 and ChaCha Tsukasa Ishiguro, Shinsaku Kiyomoto, and Yutaka Miyake KDDI R&D Laboratories Inc. 2-1-15 Ohara, Fujimino, Saitama 356-8502, Japan ftsukasa,kiyomoto,[email protected] Abstract. -

Hardware Evaluation of Estream Candidates
Hardware Evaluation of eSTREAM Candidates Frank K. G¨urkaynak, Peter Luethi, Nico Bernold, Ren´eBlattmann,Victoria Goode, Marcel Marghitola, Hubert Kaeslin, Norbert Felber, Wolfgang Fichtner Integrated Systems Laboratory ETH Zurich 2. February 2006 Table of Contents 1 Overview 2 Methodology 3 Algorithms 4 Efficiency in Hardware 5 Results 6 Conclusions 2 / 28 Department of Information Technology Integrated Systems Laboratory and Electrical Engineering Zurich Algorithms that support only Profile-II Algorithms without any cryptological issues Algorithms which are not likely to get updates Once these are completed, look for additional algorithms that seem easy to implement. Implementing eSTREAM Candidates eSTREAM candidates (34) ABC Achterbahn CryptMT/Fubuki DECIM DICING DRAGON Edon80 F-FCSR Frogbit Grain HC-256 Hermes8 LEX MAG MICKEY Mir-1 MOSQUITO NLS Phelix Polar Bear POMARANCH Py Rabbit Salsa20 SFINKS SOSEMANUK SSS TRBDK3 YAEA Trivium TSC-3 VEST WG Yamb ZK-Crypt 3 / 28 Department of Information Technology Integrated Systems Laboratory and Electrical Engineering Zurich Algorithms without any cryptological issues Algorithms which are not likely to get updates Once these are completed, look for additional algorithms that seem easy to implement. Implementing eSTREAM Candidates eSTREAM candidates (12) ABC Achterbahn CryptMT/Fubuki DECIM DICING DRAGON Edon80 F-FCSR Frogbit Grain HC-256 Hermes8 LEX MAG MICKEY Mir-1 MOSQUITO NLS Phelix Polar Bear POMARANCH Py Rabbit Salsa20 SFINKS SOSEMANUK SSS TRBDK3 YAEA Trivium TSC-3 VEST WG Yamb ZK-Crypt Algorithms that support only Profile-II 3 / 28 Department of Information Technology Integrated Systems Laboratory and Electrical Engineering Zurich Algorithms which are not likely to get updates Once these are completed, look for additional algorithms that seem easy to implement. -

Copyright by Gokhan Sayilar 2014 the Thesis Committee for Gokhan Sayilar Certifies That This Is the Approved Version of the Following Thesis
Copyright by Gokhan Sayilar 2014 The Thesis Committee for Gokhan Sayilar Certifies that this is the approved version of the following thesis: Cryptoraptor: High Throughput Reconfigurable Cryptographic Processor for Symmetric Key Encryption and Cryptographic Hash Functions APPROVED BY SUPERVISING COMMITTEE: Derek Chiou, Supervisor Mohit Tiwari Cryptoraptor: High Throughput Reconfigurable Cryptographic Processor for Symmetric Key Encryption and Cryptographic Hash Functions by Gokhan Sayilar, B.S. THESIS Presented to the Faculty of the Graduate School of The University of Texas at Austin in Partial Fulfillment of the Requirements for the Degree of MASTER OF SCIENCE IN ENGINEERING THE UNIVERSITY OF TEXAS AT AUSTIN December 2014 To my family and many friends... Acknowledgments A major research project like this is never the work of anyone alone. I would like to extend my appreciation especially to the following. First and foremost I offer my sincerest gratitude to my supervisor, Dr. Derek Chiou, for his excellent guidance, caring, and patience. I would also like to thank him for being an open person to ideas, encouraging and helping me to shape my interest and ideas, and giving me the freedom to work in my own way. He’s the funniest advisor and one of the smartest people I know. Besides my advisor, I would like to thank to my second reader, Dr. Mohit Tiwari, for his advises and insightful comments. I am also thankful to my friends in US, Turkey, and other parts of the World for being sources of laughter, joy, and support. Last but not least, I would like to thank my parents and my brother for their continuous love and unconditional support in any decision that I make. -

Classification of Cryptographic Libraries
Institute of Software Technology University of Stuttgart Universitätsstraße 38 D–70569 Stuttgart Fachstudie Classification of cryptographic libraries Andreas Poppele, Rebecca Eichler, Roland Jäger Course of Study: Softwaretechnik Examiner: Prof. Dr. rer. nat. Stefan Wagner Supervisor: Kai Mindermann, M.Sc. Commenced: 2017/03/07 Completed: 2017/09/07 CR-Classification: A.1, A.2 Declaration 2/186 Zusammenfassung Bei der Umsetzung von Sicherheitskonzepten stehen Softwareentwickler vor der Heraus- forderung eine passende kryptografische Bibliothek zu finden. Es gibt eine Vielzahl von kryptographischen Bibliotheken für verschiedene Programmiersprachen, ohne dass es eine standardisierte Auffassung von verschiedenen Eigenschaften dieser kryptographischen Bibliotheken gibt. Dieser Bericht liefert eine Klassifizierung von über 700 kryptograph- ischen Bibliotheken. Die Bibliotheken wurden in Bezug auf Aktualität und Beliebtheit ausgewählt. Um einen standardisierten Überblick zu liefern, wurden die wichtigsten Merkmale dieser Bibliotheken gesammelt und definiert. Die Datenerhebung zu diesen Merkmalen wurde sowohl manuell als auch automatisiert durchgeführt. Die Klassifizier- ung enthält Informationen, die erfahrenen und unerfahrenen Entwicklern im kryptografis- chen Bereich helfen, eine Bibliothek zu finden, die ihren Fähigkeiten und Anforderungen entspricht. Darüber hinaus kann sie als Grundlage für Studien über jede Form der Verbesserung dieser Bibliotheken und vieles mehr verwendet werden. Abstract Software developers today are faced with choosing cryptographic libraries in order to implement security concepts. There is a large variety of cryptographic libraries for diverse programming languages, without there being a standardized conception of different properties of these cryptographic libraries. This report provides a classification of over 700 cryptographic libraries. The libraries were chosen pertaining to currentness and popularity. In order to provide a standardized overview the most important traits and characteristics of these libraries were gathered and defined.