Cryptoloop HOWTO
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Stackable File Systems As a Security Tool
Stackable File Systems as a Security Tool Erez Zadok Computer Science Department, Columbia University [email protected] CUCS-036-99 Abstract Programmers often prefer to use existing system security services, such as file system security, rather than im- plement their own in an application. Traditional Unix security is generally considered inadequate and few operating systems offer enhanced security features such as ACLs[24] or immutable files[12]. Additional file system security features are always sought, but implementing them is a difficult task because modifying and porting existing file systems is costly or not possible. We advocate adding new security features using stackable file systems. As a starting point, we propose a portable, stackable template called the wrapper file system or Wrapfs, a minimal file system from which a wide range of file systems can be prototyped. A developer can modify a copy of the template and add only that which is necessary to achieve the desired functionality. The Wrapfs template takes care of kernel internals, freeing the developer from the details of operating system internals. Wrapfs imposes an overhead of only 5–7%. This paper describes the design, implementation, and porting of Wrapfs. We discuss several prototype file sys- tems written using Wrapfs that illustrate the ease with which security features can be implemented. The examples demonstrate security features such as encryption, access control, intrusion detection, intrusion avoidance, and analy- sis. 1 Introduction Security has become and integral part of computing in recent years. To provide the strongest possible security to users, security solutions sometimes consume a large amount of resources, and may inconvenience their users too much. -

Taxonomy of Linux Kernel Vulnerability Solutions
Taxonomy of Linux Kernel Vulnerability Solutions Serguei A. Mokhov Marc-Andre´ Laverdiere` Djamel Benredjem Computer Security Laboratory Computer Security Laboratory Computer Security Laboratory Concordia Institute for Concordia Institute for Concordia Institute for Information Systems Engineering Information Systems Engineering Information Systems Engineering Concordia University, Concordia University, Concordia University, Montreal, Quebec, Canada Montreal, Quebec, Canada Montreal, Quebec, Canada Email: [email protected] Email: ma [email protected] Email: d [email protected] Abstract—This paper presents the results of a case study on C programs in general, as well as statistics on their relative software vulnerability solutions in the Linux kernel. Our major importance. We also introduce a new methodology to track contribution is the introduction of a classification of methods used the patch solving a security issue based only on the contents to solve vulnerabilities. Our research shows that precondition validation, error handling, and redesign are the most used of the security advisory. methods in solving vulnerabilities in the Linux kernel. This The paper is organized as follows: we examine previous contribution is accompanied with statistics on the occurrence work that was done regarding Linux and C security in of the different types of vulnerabilities and their solutions that Section II, followed by a description of the methodology we observed during our case study, combined with example used in order to obtain the solutions to the vulnerabilities in source code patches. We also combine our findings with existing programming guidelines to create the first security-oriented Section III. Afterwards, in Section IV, we show our results, coding guidelines for the Linux kernel. -

A Steganographic File System for the Linux Kernel
A Steganographic File System for the Linux Kernel by Ashley Morgan Anderson The University of Exeter COM3401 Individual Project 11th August 2007 Abstract Encryption is all around us these days, yet the security of private data on home computers is overlooked by many. The presence of cipher-text — in some instances — can make things worse, therefore the only way to overcome this is to hide the data. The Ancient Greeks knew about this risk and as such fabricated some of the most ingenious methods of steganography ever used. However, steganography has come along way in the last 3000 years, and is more important today than ever before (due to tightening restrictions governing encryption). This paper looks at how different mediums have been used to ensure messages and data remain private, as well as proposing a new file system which takes care of hiding files for the user. Whilst not the first, it does include many unique features which are intended to provide a more natural interface. I certify that all material in this project which is not my own work has been identified. ...................................... A.M. Anderson Contents 1 Introduction 1 2 Background 2 2.1 Steganography . 2 2.2 File Systems . 4 2.3 Steganographic File Systems . 6 3 Design 11 3.1 Implemented Design . 11 3.2 Potential Driver Types . 13 3.3 Initial File System . 15 3.4 Encryption . 15 3.5 A Discarded Design . 16 4 Development 17 4.1 The Tools . 17 4.2 The Process . 18 5 Testing 19 5.1 Progressive . 19 5.2 Forensic Analysis . -
Cryptographic File Systems
Cryptographic Filesystems Background and Implementations for Linux and OpenBSD Background ● Loop device primer ● Keys, cipher modes, salting, key hashing ● Journaling file systems and encrypted swap ● Offset, sizelimit, hard/soft block size paramters explained ● Issues with software suspend Loopback Primer /dev/hda1 losetup /dev/loop0 myloop.dat /dev/loop0 /dev/hda2 losetup /dev/loop1 \ /dev/hda2 Filesystem with various /dev/loop1 files and directories Loopback Primer G76g(*gF *^tF0OB( 6g)%)f5( /dev/loop0 *&(*6bP( Dear Bob, this is the message ● The loopback device supports cryptographic transforms ● Knowing the key reveals a filesystem within a normal file (or block device) Keys ● Encryption with user supplied key ● Encryption with hashed key – rmd160, sha256, sha384, sha512, ... ● Using multiple keys (typically 64) – every sector (512b) uses different key Basic block cipher modes ● Currently only ECB (Electronic Code Book) and CBC (Cipher Block Chaining) widely supported ● ECB directly encipher plaintext – Same plaintext block always encrypts to same ciphertext. Is considered weak. ● CBC uses the previous block as IV – Basically solves ECB's dictionary problem – Only provides very limited integrity Key iterations and salt ● Key can be hashed 1000 times – significantly slows down brute force attack on password ● Salt is a string appended to the password – slows down brute force attack on password – poor man's two factor authentication Journaling ● Fine on device backed loop device ● Avoid on file backed loop devices – The VM can write -

Cryptographic File Systems Performance: What You Don't Know Can Hurt You Charles P
Cryptographic File Systems Performance: What You Don't Know Can Hurt You Charles P. Wright, Jay Dave, and Erez Zadok Stony Brook University Appears in the proceedings of the 2003 IEEE Security In Storage Workshop (SISW 2003) Abstract interact with disks, caches, and a variety of other com- plex system components — all having a dramatic effect Securing data is more important than ever, yet cryp- on performance. tographic file systems still have not received wide use. In this paper we perform a real world performance One barrier to the adoption of cryptographic file systems comparison between several systems that are used is that the performance impact is assumed to be too high, to secure file systems on laptops, workstations, and but in fact is largely unknown. In this paper we first moderately-sized file servers. We also emphasize multi- survey available cryptographic file systems. Second, programming workloads, which are not often inves- we perform a performance comparison of a representa- tigated. Multi-programmed workloads are becoming tive set of the systems, emphasizing multiprogrammed more important even for single user machines, in which workloads. Third, we discuss interesting and counterin- Windowing systems are often used to run multiple appli- tuitive results. We show the overhead of cryptographic cations concurrently. We expect cryptographic file sys- file systems can be minimal for many real-world work- tems to become a commodity component of future oper- loads, and suggest potential improvements to existing ating systems. systems. We have observed not only general trends with We present results from a variety of benchmarks, an- each of the cryptographic file systems we compared but alyzing the behavior of file systems for metadata op- also anomalies based on complex interactions with the erations, raw I/O operations, and combined with CPU operating system, disks, CPUs, and ciphers. -

Hello Marte OS Using an Emulator Daniel Sangorrin [email protected]
Hello MaRTE OS using an emulator Daniel Sangorrin [email protected] 2009-3-4 Revision History Revision 1.3 2009-3-4 Revised by: dsl Add mtools for mounting the images. Update installation instructions referencing INSTALL file. Revision 1.2 2007-6-15 Revised by: dsl Added the process to create a FAT16 image file for QEMU Revision 1.1 2007-6-9 Revised by: dsl Updated to MaRTE OS v1.6 snapshot This document tries to introduce people to MaRTE OS in a very simple way. Table of Contents 1. Preface........................................................................................................................................................................2 1.1. Feedback.........................................................................................................................................................2 2. Let’s see MaRTE OS running!.................................................................................................................................2 2.1. Install the emulator QEMU............................................................................................................................2 2.2. ...and run these MaRTE OS Demos! ..............................................................................................................2 3. Hello MaRTE! ...........................................................................................................................................................3 3.1. The compiler GNAT-GPL ..............................................................................................................................3 -

Linux Based Live CD on Optical Disks
Pobrane z czasopisma Annales AI- Informatica http://ai.annales.umcs.pl Data: 26/09/2021 15:23:08 Annales UMCS Annales UMCS Informatica AI 5 (2006) 29-36 Informatica Lublin-Polonia Sectio AI http://www.annales.umcs.lublin.pl/ Linux based Live CD on optical disks 1 2* Michał Chromiak , Andrzej Góźdź 1Institute of Mathematics, Maria Curie-Skłodowska University, Pl. M.Curie-Skłodowskiej 1, 20-031 Lublin, Poland 2Institute of Physics, Maria Curie-Skłodowska University, Pl. M.Curie-Skłodowskiej 1, 20-031 Lublin, Poland Abstract We present an introduction to LiveCD system remastering based on a prospective UnionFS filesystem. 1. Introduction Regarding increasing popularity of the LiveCD distributions1 of a Linux system we compile the essential knowledge of how the LiveCD works (based on many rather scattered documents [1-8]) to facilitate preparation of the specialized distributions of systems based on this idea. We describe one of the most efficient ways of system architecture managing using UnionFS. All steps of the procedure were tested using laptops which have often more exotic hardware than desktopUMCS computers. The possibility of booting a PC from a CD/DVD ROM has raised several possibilities, including the most important one, namely, the possibility of running the required system or programs independently of the actual operational system, configuration, and resources of the PC. The self-configuring CD/DVD ROMs can be also useful for administrative purposes and as the rescue disks. The LiveCD distributions allow for cheap and effective use of the PCs as the special servers, routers and other active elements over the network. This idea of the LiveCD systems is based on the possibility opened by the El Torito extension to the standard ISO 9660 system and the Linux kernel capabilities. -

New Methods in Hard Disk Encryption
New Methods in Hard Disk Encryption Clemens Fruhwirth <[email protected]> Institute for Computer Languages Theory and Logic Group Vienna University of Technology July 18, 2005 Abstract This work investigates the state of the art in hard disk cryptography. As the choice of the cipher mode is essential for the security of hard disk data, we discuss the recent cipher mode developments at two standardisation bodies, NIST and IEEE. It is a necessity to consider new developments, as the most common cipher mode – namely CBC – has many security problems. This work devotes a chapter to the analysis of CBC weaknesses. Next to others, the main contributions of this work are (1) efficient algorithms for series of multiplications in a finite field (Galois Field), (2) analysis of the security of password-based cryptography with respect to low entropy attacks and (3) a design template for secure key management, namely TKS1. For the latter, it is assumed that key management has to be done on regular user hardware in the absence of any special security hardware like key tokens. We solve the problems arising from magnetic storage by introducing a method called anti-forensic information splitter. This work is complemented by the presentation of a system implementing a variant of TKS1. It is called LUKS and it was developed and implemented by the author of this work. Contents Preface v 1 Introduction 1 2 Design ingredients 3 2.1 The many faces of n ........................ 3 2.2 Galois Field arithmetic . 4 2.3 Algorithms for GF(2η)....................... 9 2.4 Sequences of multiplications in GF(2η) . -

Efficient Cache Attacks on AES, and Countermeasures
J. Cryptol. (2010) 23: 37–71 DOI: 10.1007/s00145-009-9049-y Efficient Cache Attacks on AES, and Countermeasures Eran Tromer Computer Science and Artificial Intelligence Laboratory, Massachusetts Institute of Technology, 32 Vassar Street, G682, Cambridge, MA 02139, USA [email protected] and Department of Computer Science and Applied Mathematics, Weizmann Institute of Science, Rehovot 76100, Israel Dag Arne Osvik Laboratory for Cryptologic Algorithms, Station 14, École Polytechnique Fédérale de Lausanne, 1015 Lausanne, Switzerland dagarne.osvik@epfl.ch Adi Shamir Department of Computer Science and Applied Mathematics, Weizmann Institute of Science, Rehovot 76100, Israel [email protected] Communicated by Lars R. Knudsen Received 20 July 2007 and revised 25 June 2009 Online publication 23 July 2009 Abstract. We describe several software side-channel attacks based on inter-process leakage through the state of the CPU’s memory cache. This leakage reveals memory access patterns, which can be used for cryptanalysis of cryptographic primitives that employ data-dependent table lookups. The attacks allow an unprivileged process to attack other processes running in parallel on the same processor, despite partitioning methods such as memory protection, sandboxing, and virtualization. Some of our meth- ods require only the ability to trigger services that perform encryption or MAC using the unknown key, such as encrypted disk partitions or secure network links. Moreover, we demonstrate an extremely strong type of attack, which requires knowledge of nei- ther the specific plaintexts nor ciphertexts and works by merely monitoring the effect of the cryptographic process on the cache. We discuss in detail several attacks on AES and experimentally demonstrate their applicability to real systems, such as OpenSSL and Linux’s dm-crypt encrypted partitions (in the latter case, the full key was recov- ered after just 800 writes to the partition, taking 65 milliseconds). -

E:\Ghcstop\AESOP Ghcstop Doc\Kernel\Ramdisk Howto\060405-Aesop2440-Ramdisk-Howto.Txt 200 06-04-06, 12:43:53오후 Aesop 2440 Kernel 2.6.13 Ramdisk Howto
파일: E:\ghcstop\AESOP_ghcstop_doc\kernel\ramdisk_howto\060405-aesop2440-ramdisk-howto.txt 200 06-04-06, 12:43:53오후 aesop 2440 kernel 2.6.13 ramdisk howto - 20060406(까먹고 민방위 못간날...^^) by godori 1. kernel설정을 다음과 같이 바꾼다. Device Drivers -> Block device쪽을 보시면.... Linux Kernel v2.6.13-h1940-aesop2440 Configuration qqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqq lqqqqqqqqqqqqqqqqqqqqqqqqqqqqqq Block devices qqqqqqqqqqqqqqqqqqqqqqqqqqqqqqk x Arrow keys navigate the menu. <Enter> selects submenus --->. x x Highlighted letters are hotkeys. Pressing <Y> includes, <N> excludes, x x <M> modularizes features. Press <Esc><Esc> to exit, <?> for Help, </> x x for Search. Legend: [*] built-in [ ] excluded <M> module < > module x x lqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqk x x x < > XT hard disk support x x x x <*> Loopback device support x x x x < > Cryptoloop Support x x x x <*> Network block device support x x x x < > Low Performance USB Block driver x x x x <*> RAM disk support x x x x (8) Default number of RAM disks x x x x (8192) Default RAM disk size (kbytes) x x x x [*] Initial RAM disk (initrd) support x x x x () Initramfs source file(s) x x x x < > Packet writing on CD/DVD media x x x x IO Schedulers ---> x x x x < > ATA over Ethernet support x x x x x x x x x x x x x x x x x x x mqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqj x tqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqu x <Select> < Exit > < Help > x mqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqj 여기서 8192 는 ramdisk size 입니다 . 만드는 ramdisk 크기에 맞게끔 바꿔주시고... File systems쪽에서 Linux Kernel v2.6.13-h1940-aesop2440 Configuration qqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqq lqqqqqqqqqqqqqqqqqqqqqqqqqqqqqq File systems qqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqk x Arrow keys navigate the menu. -
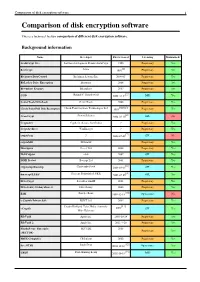
Comparison of Disk Encryption Software 1 Comparison of Disk Encryption Software
Comparison of disk encryption software 1 Comparison of disk encryption software This is a technical feature comparison of different disk encryption software. Background information Name Developer First released Licensing Maintained? ArchiCrypt Live Softwaredevelopment Remus ArchiCrypt 1998 Proprietary Yes [1] BestCrypt Jetico 1993 Proprietary Yes BitArmor DataControl BitArmor Systems Inc. 2008-05 Proprietary Yes BitLocker Drive Encryption Microsoft 2006 Proprietary Yes Bloombase Keyparc Bloombase 2007 Proprietary Yes [2] CGD Roland C. Dowdeswell 2002-10-04 BSD Yes CenterTools DriveLock CenterTools 2008 Proprietary Yes [3][4][5] Check Point Full Disk Encryption Check Point Software Technologies Ltd 1999 Proprietary Yes [6] CrossCrypt Steven Scherrer 2004-02-10 GPL No Cryptainer Cypherix (Secure-Soft India) ? Proprietary Yes CryptArchiver WinEncrypt ? Proprietary Yes [7] cryptoloop ? 2003-07-02 GPL No cryptoMill SEAhawk Proprietary Yes Discryptor Cosect Ltd. 2008 Proprietary Yes DiskCryptor ntldr 2007 GPL Yes DISK Protect Becrypt Ltd 2001 Proprietary Yes [8] cryptsetup/dmsetup Christophe Saout 2004-03-11 GPL Yes [9] dm-crypt/LUKS Clemens Fruhwirth (LUKS) 2005-02-05 GPL Yes DriveCrypt SecurStar GmbH 2001 Proprietary Yes DriveSentry GoAnywhere 2 DriveSentry 2008 Proprietary Yes [10] E4M Paul Le Roux 1998-12-18 Open source No e-Capsule Private Safe EISST Ltd. 2005 Proprietary Yes Dustin Kirkland, Tyler Hicks, (formerly [11] eCryptfs 2005 GPL Yes Mike Halcrow) FileVault Apple Inc. 2003-10-24 Proprietary Yes FileVault 2 Apple Inc. 2011-7-20 Proprietary -
Block Devices and Volume Management in Linux
Block devices and volume management in Linux Krzysztof Lichota [email protected] L i n u x b l o c k d e v i c e s l a y e r ● Linux block devices layer is pretty flexible and allows for some interesting features: – Pluggable I/O schedulers – I/O prioritizing (needs support from I/O scheduler) – Remapping of disk requests (Device Mapper) – RAID – Various tricks (multipath, fault injection) – I/O tracing (blktrace) s t r u c t b i o ● Basic block of I/O submission and completion ● Can represent large contiguous memory regions for I/O but also scattered regions ● Scattered regions can be passed directly to disks capable of scatter/gather ● bios can be split, merged with other requests by various levels of block layer (e.g. split by RAID, merged in disk driver with other disk requests) s t r u c t b i o f i e l d s ● bi_sector – start sector of I/O ● bi_size – size of I/O ● bi_bdev – device to which I/O is sent ● bi_flags – I/O flags ● bi_rw – read/write flags and priority ● bi_io_vec – memory scatter/gather vector ● bi_end_io - function called when I/O is completed ● bi_destructor – function called when bio is to be destroyed s t r u c t b i o u s a g e ● Allocate bio using bio_alloc() or similar function ● Fill in necessary fields (start, device, ...) ● Initialize bio vector ● Fill in end I/O function to be notified when bio completes ● Call submit_bio()/generic_make_request() ● Example: process_read() in dm-crypt O t h e r I / O s u b m i s s i o n f u n c t i o n s ● Older interfaces for submitting I/O are supported (but deprecated),