Modern Applications Need Modern Security
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Supporting Secure Services on Dynamic Aggregation of Heterogeneous Networks
Supporting Secure Services on Dynamic Aggregation of Heterogeneous Networks SUBMITTED TO UNIVERSITY OF SOUTHERN QUEENSLAND IN PARTIAL FULFILLMENT OF THE REQUIREMENTS FOR THE DEGREE OF DOCTOR OF PHILOSOPHY David Tai Wai Lai July 2010 Certification of Dissertation I certify that the ideas, experimental work, results, analysis, software, and conclusions reported in this dissertation are entirely my own effort, except where otherwise acknowl- edged. I also certify that the work is original and has not been previously submitted for any other award or degree. Signature of Candidate Date Endorsement Signature of Supervisor Date ii I certify that I have read this dissertation and that, in my opin- ion, it is fully adequate in scope and quality as a dissertation for the degree of Doctor of Philosophy. Dr. Zhongwei Zhang (University of Southern Queensland) I certify that I have read this dissertation and that, in my opin- ion, it is fully adequate in scope and quality as a dissertation for the degree of Doctor of Philosophy. Dr. Shan Suthaharan (University of Northern Carolina at Greensboro) iii iv Abstract Sharing of services over IP networks prove to be an effective approach to satisfy the demand of network users when their home network cannot offer the required services. Authenti- cation, authorization and revocation are some of the important challenges in the service sharing services over IP networks. This research address the problem associated with the authentication because it becomes more and more complicated due to the incompatible au- thentication schemes used by individual autonomous networks, privacy of authentication information, and the overhead in establishing the sharing. -

PL-400 Dumps PL-400 Braindumps PL-400 Real Questions PL-400 Practice Test PL-400 Dumps Free
PL-400 Dumps PL-400 Braindumps PL-400 Real Questions PL-400 Practice Test PL-400 dumps free Microsoft PL-400 Microsoft Power Platform Developer http://killexams.com/pass4sure/exam-detail/PL-400 Question: 2 Section 20 Introductory Info Case study - This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided. To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study. At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section. To start the case study - To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. -

Entrevista José Manuel Alarcón Evolución De SQL Server En
Nº46 diciembre 2020 REVISTA ESPECIALIZADA EN TECNOLOGÍAS MICROSOFT Procesando for- Evolución de Troubleshooting Entrevista mularios con SQL Server del networking de José Manuel Form Recognizer en múltiples Azure mediante Alarcón y Azure Func- Network Watcher plataformas tions 1 Contenido 02 03 Editorial 04 Pon un Bot en tu vida… y en 08 Microsoft Teams Staff Power Virtual Agents en Microsoft Teams 12 CompartiMOSS es una pu- Entrevista José Manuel Alarcón blicación independiente de 15 distribución libre en forma Procesando formularios con Form electrónica. Las opiniones Recognizer y Azure Functions 22 aquí expresadas son de es- Troubleshooting del networking de tricto orden personal, cada 25 Azure mediante Network Watcher autor es completamente El módulo de SecretManagement de responsable de su propio PowerShell 29 Microsoft Bookings: Gestión sencilla contenido. de citas en tiempos de pandemia y escenarios de Remote Work 33 Cómo volcar información desde las DIRECCIÓN GENERAL Azure Table Storage a Microsoft Lists • Gustavo Velez usando Logic Apps 39 • Juan Carlos Gonzalez • Fabian Imaz Entrevista Aura • Alberto Diaz 41 Evolución de SQL Server en múltiples plataformas 43 DISEÑO Y DIAGRAMACIÓN Introducción a Synapse Analytics – • Santiago Porras Rodríguez integración con Power BI 46 Ahorrando código: Funcionalidades de C# para no Programar (de) más (pero programar mejor) 53 Desarrollando Microsoft Teams Contacte con Messaging Extensions desde SPFx nosotros [email protected] [email protected] [email protected] [email protected] [email protected] BLOGS http://www.gavd.net https://jcgonzalezmartin.wordpress.com/ http://blog.siderys.com https://adiazcan.github.com REDES SOCIALES Facebook: http://www.facebook.com/group. php?gid=128911147140492 LinkedIn: http://www.linkedin.com/groups/Com- partiMOSS-3776291 Twitter: @CompartiMOSScom 2 03 Editorial Este año que se está terminando quedará marcado en la historia de todos nosotros. -
01-Power Apps Canvas App Lab Manual.Pdf
Power Platform App in a Day Module 1: Power Apps Canvas App Hands-on Lab Step-by-Step February 2020 Contents Power Apps Canvas App ....................................................................................................................................................... 1 Lab Prerequisites ............................................................................................................................................................................................................... 1 Power Apps Canvas Studio Layout ............................................................................................................................................................................. 1 Goals for this lab ............................................................................................................................................................................................................... 2 Introduction: Device Ordering Scenario .................................................................................................................................................................... 2 Solution overview .............................................................................................................................................................................................................. 2 Locale-specific difference in formulas ....................................................................................................................................................................... -

Etsi Tr 133 995 V13.0.1 (2017-04)
ETSI TR 133 995 V13.0.1 (2017-04) TECHNICAL REPORT Universal Mobile Telecommunications System (UMTS); LTE; Study on security aspects of integration of Single Sign-On (SSO) frameworks with 3GPP operator-controlled resources and mechanisms (3GPP TR 33.995 version 13.0.1 Release 13) 3GPP TR 33.995 version 13.0.1 Release 13 1 ETSI TR 133 995 V13.0.1 (2017-04) Reference RTR/TSGS-0333995vd01 Keywords LTE,SECURITY,UMTS ETSI 650 Route des Lucioles F-06921 Sophia Antipolis Cedex - FRANCE Tel.: +33 4 92 94 42 00 Fax: +33 4 93 65 47 16 Siret N° 348 623 562 00017 - NAF 742 C Association à but non lucratif enregistrée à la Sous-Préfecture de Grasse (06) N° 7803/88 Important notice The present document can be downloaded from: http://www.etsi.org/standards-search The present document may be made available in electronic versions and/or in print. The content of any electronic and/or print versions of the present document shall not be modified without the prior written authorization of ETSI. In case of any existing or perceived difference in contents between such versions and/or in print, the only prevailing document is the print of the Portable Document Format (PDF) version kept on a specific network drive within ETSI Secretariat. Users of the present document should be aware that the document may be subject to revision or change of status. Information on the current status of this and other ETSI documents is available at https://portal.etsi.org/TB/ETSIDeliverableStatus.aspx If you find errors in the present document, please send your comment to one of the following services: https://portal.etsi.org/People/CommiteeSupportStaff.aspx Copyright Notification No part may be reproduced or utilized in any form or by any means, electronic or mechanical, including photocopying and microfilm except as authorized by written permission of ETSI. -
Power Platform Adoption Framework
Power Platform Adoption Framework Second Edition April 2020 Adopting, managing, and governing Power Platform at scale Power Platform Adoption Framework, Second Edition Table of Contents • Introduction…………………………………………………...……………………………… 3 • Preface to the Second Edition..………..…………………………………………….. 3 • Our Philosophy…..…..……………………..………………………………………….. 4 • Scalability Matters…..……………………..…………………………………………… 5 • Power Platform……………………………………………………………………………..… 6 • Power Platform Basics……………………..…………………………………………. 6 • Power Platform in Broader Context…..…………………………………………………. 8 • Adopting at Scale………………………..………………………………………………..… 9 • Quick Start………………………………..………………………………………………..… 9 • On Track…………………………………..………………………………………………..… 10 • Going Through a Phase………………..………………………………………………..… 11 • Enterprise Management………………..…………………………………………………. 12 • Pillars of Enterprise Management………..…………………………………………. 12 • Who Owns This?...........………………..………………………………………………..… 13 • Architecting for Scale.........………………..……………………………………….…..… 14 • Center of Excellence Starter Kit……………..………………………………….… 14 • Environmental Architecture Model………..………………………………….….. 15 • Nurturing the Community.........………………..………………………………………… 17 • Shared Developer Community………..………………………………….…………. 17 • Citizen Developers…………….………..………………………………….…………. 17 • Power Platform Developers….………..………………………………….…. 17 • Durable Partnerships…...........………………..…………………………………. 18 • The Big Idea……………...........………………..……………………………………….… 19 • About the Publisher.…...........………………..……………………………………….…. 21 Power Platform -

Upskill with Dynamics 365 and Power Platform Certifications
Upskill with Dynamics 365 and Power Platform certifications Advance your career, earn recognition, and validate your technical expertise for current and future industry job roles with Microsoft Certifications for business applications. Building your confidence in Dynamics 365 and Power Platform solutions can help you bring your customers and business together and turn ideas into impactful solutions with real-time insights that drive results. Visit thecertifications page to get started. Dynamics 365 Fundamentals (CRM) Dynamics 365 Fundamentals (ERP) The customer engagement apps fundamentals certification The finance and operations apps fundamentals certification validates broad exposure to the customer engagement validates broad exposure to the enterprise resource planning capabilities of Dynamics 365, building on a foundational capabilities of Dynamics 365, building on a foundational understanding of business operations, IT, and customer understanding of financial principles and business operations relationship management. Dynamics 365 Finance Functional Dynamics 365 Sales Functional Consultant Associate Consultant Associate Finance functional consultants unify global financials, automate tasks and workflows, and streamline customer ordering, selling, Sales functional consultants implement solutions that support Customer Finance and invoicing, and reporting. a sales lifecycle to meet revenue targets, business strategies, Engagement and company objectives using Microsoft Power Platform. Operations Dynamics 365 Supply Chain (CRM) (ERP) -

State of North Carolina Request for Proposal No
STATE OF NORTH CAROLINA REQUEST FOR PROPOSAL NO. 41-100358-001 Department of Information Technology Offers will be publicly opened: April 29, 2020 at 2:00pm EST Issue Date: March 2, 2020 Refer ALL inquiries regarding this RFP to: Commodity Number: 920 Leroy Kodak] Description: Identity Access Management System [email protected]] Using Agency: Department of Information [919-754-6665] Technology Requisition No.: None OFFER The State solicits offers for Services and/or goods described in this solicitation. All offers and responses received shall be treated as Offers to contract. EXECUTION In compliance with this Request for Proposal, and subject to all the conditions herein, the undersigned offers and agrees to furnish any or all Services or goods upon which prices are offered, at the price(s) offered herein, within the time specified herein. By executing this offer, I certify that this offer is submitted competitively and without collusion. Failure to execute/sign offer prior to submittal shall render offer invalid. Late offers are not acceptable. OFFEROR: STREET ADDRESS: P.O. BOX: ZIP: CITY, STATE & ZIP: TELEPHONE NUMBER: TOLL FREE TEL. NO PRINT NAME & TITLE OF PERSON SIGNING: FAX NUMBER: AUTHORIZED SIGNATURE: DATE: E-MAIL: Offer valid for one hundred twenty (120) days from date of offer opening unless otherwise stated here: ____ days ACCEPTANCE OF OFFER If any or all parts of this offer are accepted, an authorized representative of the Department of Information Technology shall affix their signature hereto and any subsequent Request for Best and Final Offer, if issued. Acceptance shall create a contract having an order of precedence as follows: Best and Final Offers, if any, Special terms and conditions specific to this RFP, Specifications of the RFP, the Department of Information Technology Terms and Conditions, and the agreed portion of the awarded Vendor’s Offer. -

Power Platform Training and Certifications
Power Platform training and certifications aka.ms/PPTrainCertDeck Welcome to How to use this deck Power Platform training and certifications Certification portfolio Our approach to learning Available certifications and associated exams in portfolio. is to develop an inclusive environment for every stage in an individual’s Certification overview career. Identify the right candidate profile with the recommended skills knowledge and experience. This guide has been created to provide training and certification Certification journey options to achieve Recommended steps to earn a certification, including preparation personal success. resources and opportunities for continue learning. Certification learning path Recommended training content to prepare for certification exams, including self-paced training and Microsoft Official Courseware (MOC) delivered by Learning Partners. *Exam in beta Power Platform certifications ^Retires Jun 30, 2021 Role-based ▾ Associate Expand your technical skill set • Power Platform App Maker (PL-100) • Power Platform Functional Consultant (PL-200) • Power Platform Developer (PL-400) • Data Analyst (DA-100) ▾ Expert • Dynamics 365 + Power Platform Solution Architect^ (MB-600) • Power Platform Solution Architect (PL-600)* Fundamentals • Power Platform Fundamentals (PL-900) Master the basics Overview of Microsoft Certified: Get started at Power Platform Fundamentals aka.ms/PowerCerts_Fundamentals Exam details Certification Who is this Products featured PL-900 Pass certification exam PL-900 certification for? Microsoft -

BIG-IP Access Policy Manager
DATA SHEET BIG-IP Access Policy Manager WHAT'S INSIDE Simple, Secure, and Seamless Access to 2 Bridging Secure Any Application, Anywhere Application Access Applications are gateways to your critical and sensitive data. Simple, secure access to 17 BIG-IP APM Features your applications is paramount, but application access today is extremely complex. Apps 19 F5 BIG-IP Platforms can be hosted anywhere—in the public cloud, in a private cloud, on-premises, or in a data center. Ensuring users have secure, authenticated access anytime, anywhere, to only the 19 F5 Support Services applications they are authorized to access is now a significant challenge. There are different application access methods to deal with these complexities. There are also various sources for authorized user identity, as well as dealing with applications that require modern or more traditional authentication and authorization methods, single sign-on (SSO), federation, and more, in addition to ensuring a secure, simple user access experience to support and consider. With digital transformation touching every part of an enterprise today, native cloud and Software as a Service (SaaS) applications are now the enterprise application standard. Many organizations, though, find they’re unable or unwilling to migrate all their applications to the cloud. There may be mission-critical classic or custom applications that cannot or should not support migration to the public cloud or be easily replaced by a SaaS solution. Applications are being hosted in a variety of locations, with differing and many times disparate authentication and authorization methods that are unable to communicate with each other or work seamlessly across existing SSO or federated identity. -
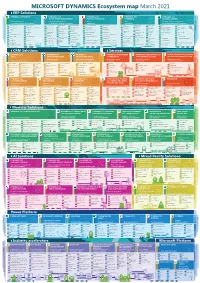
MICROSOFT DYNAMICS Ecosystem Map March 2021
MICROSOFT DYNAMICS Ecosystem map March 2021 ERP Solutions DYNAMICS 365 FINANCE DYNAMICS 365 DYNAMICS 365 DYNAMICS 365 DYNAMICS 365 SUPPLY CHAIN MANAGEMENT PROJECT OPERATIONS COMMERCE BUSINESS CENTRAL Finance management Supply chain management Project Retail Enterprise resource management for medium and large sized companies for medium and large sized companies management management for small and medium sized companies Revenue Recognition Cost management Asset management Procurement and Vendor collaboration Project sales management Resource planning AI product Commerce app Cloud scale unit Planning Treasury sourcing recommendation marketplace Credit management Financials embedded Power BI Master planning Time and attendance Project accounting Schedule table Cloud POS & Warehouse management Inventory management Service management Digital commerce Assortment Modern POS Intercompany Consolidations Self service portal Mixed Reality Inventory-based projects Offer management management Assembly management Workfl ow Cost allocation integration Fraud protection Replenishment Treasury General ledger Retail headquarter Invoice summary page Lead management integration Customer segmentation management Production management Accounts receivable management Sales and marketing Inventory visibility and targeting Organization administration Fixed assets Price list management Time and expense management Pricing Online stores Analytics Budgeting Transportation Questionnaire Cloud & Edge scale unit Product categories Accounts receivable Expense management management -

Oracle Mobile Security a Technical Overview
Oracle Mobile Security A Technical Overview ORACLE WHITE PAPER | MAY 2015 Disclaimer The following is intended to outline our general product direction. It is intended for information purposes only, and may not be incorporated into any contract. It is not a commitment to deliver any material, code, or functionality, and should not be relied upon in making purchasing decisions. The development, release, and timing of any features or functionality described for Oracle’s products remains at the sole discretion of Oracle. ORACLE MOBILE SECURITY Table of Contents Disclaimer 1 Executive Overview 1 Oracle Mobile Security – Address Employee and Consumer use cases 2 Oracle Mobile Security Suite – Enterprise Mobility Management Solution 3 Assembling the Blocks – Core Solution Components 4 Oracle Mobile Security Container 5 Oracle Mobile Security App Containerization Tool 6 Oracle Mobile Security Access Server (MSAS) 6 Oracle Mobile Security Manager 7 Oracle Access Management Mobile and Social 7 OAuth Support 8 Extending Enterprise Security to Mobile Apps 9 Oracle Mobile and Social Client SDKs 16 Conclusion 17 Appendix: The New Mobile Computing Paradigm 18 Mobile App Development Models 18 Oracle Platform Security Services 19 REST 19 JSON 19 JSON Web Token 19 OpenID and OpendID Connect 19 OAuth 20 ORACLE MOBILE SECURITY SAML 22 WS-Security and SOAP 22 ORACLE MOBILE SECURITY Executive Overview Mobile computing gradually allows us to make the elusive “anytime, anywhere access” mantra a reality. More and more employees use their own mobile device in the workplace, a phenomenon known as “Bring Your Own Device” (BYOD), resulting in employees using the same device for personal and business purposes.