2011, Velopment of Software Platforms Techniques
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Return of Private Foundation
l efile GRAPHIC p rint - DO NOT PROCESS As Filed Data - DLN: 93491015004014 Return of Private Foundation OMB No 1545-0052 Form 990 -PF or Section 4947( a)(1) Nonexempt Charitable Trust Treated as a Private Foundation Department of the Treasury 2012 Note . The foundation may be able to use a copy of this return to satisfy state reporting requirements Internal Revenue Service • . For calendar year 2012 , or tax year beginning 06 - 01-2012 , and ending 05-31-2013 Name of foundation A Employer identification number CENTURY 21 ASSOCIATES FOUNDATION INC 22-2412138 O/o RAYMOND GINDI ieiepnone number (see instructions) Number and street (or P 0 box number if mail is not delivered to street address) Room/suite U 22 CORTLANDT STREET Suite City or town, state, and ZIP code C If exemption application is pending, check here F NEW YORK, NY 10007 G Check all that apply r'Initial return r'Initial return of a former public charity D 1. Foreign organizations, check here (- r-Final return r'Amended return 2. Foreign organizations meeting the 85% test, r Address change r'Name change check here and attach computation H Check type of organization FSection 501(c)(3) exempt private foundation r'Section 4947(a)(1) nonexempt charitable trust r'Other taxable private foundation J Accounting method F Cash F Accrual E If private foundation status was terminated I Fair market value of all assets at end und er section 507 ( b )( 1 )( A ), c hec k here F of y e a r (from Part 77, col. (c), Other (specify) _ F If the foundation is in a 60-month termination line 16)x$ 4,783,143 -

Universally Composable Security: a New Paradigm for Cryptographic Protocols∗
Universally Composable Security: A New Paradigm for Cryptographic Protocols∗ Ran Canettiy February 11, 2020 Abstract We present a general framework for describing cryptographic protocols and analyzing their security. The framework allows specifying the security requirements of practically any crypto- graphic task in a unified and systematic way. Furthermore, in this framework the security of protocols is preserved under a general composition operation, called universal composition. The proposed framework with its security-preserving composition operation allows for mod- ular design and analysis of complex cryptographic protocols from simpler building blocks. More- over, within this framework, protocols are guaranteed to maintain their security in any context, even in the presence of an unbounded number of arbitrary protocol sessions that run concur- rently in an adversarially controlled manner. This is a useful guarantee, which allows arguing about the security of cryptographic protocols in complex and unpredictable environments such as modern communication networks. Keywords: cryptographic protocols, security analysis, protocol composition, universal composi- tion. ∗An extended abstract of this work appears in the proceedings of the 42nd Foundations of Computer Science conference, 2001. This is an updated version. While the overall spirit and the structure of the definitions and results in this paper has remained the same, many important details have changed. We point out and motivate the main differences as we go along. Earlier versions of this work appeared in December 2018, July 2013, Decem- ber and January 2005, and October 2001, under the same title, and in December 2000 under the title \A unified framework for analyzing security of protocols". These earlier versions can be found at the ECCC archive, TR 01-16 (http://eccc.uni-trier.de/eccc-reports/2001/TR01-016); however they are not needed for understanding this work and have only historic significance. -
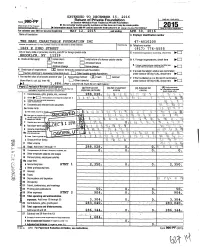
990-PF Return of Private Foundation
I EXTENDED TO DECEMBER 15, 2016 Return of Private Foundation OMB No 1545-0052 Form 990-PF or Section 4947(axl) Trust Treated as Private Foundation Depertrnent or the rreasu y Do not enter social security numbers on this form as it may be made public. 2015 Internal Revenue Service 00, Information about Form 990-PF and its separate Instructions Is at Wt ny rrs. ov/fort en o u is ns ec ion For calendar year 2015 or tax year beginning MAY 12 , 201 5 and ending APR 016 Name of foundation Employer identification number THE MARI CHARI TABLE FOUNDATION INC 47-4010200 Number and street (a P 0 box number if mail is not delivered to street address) RooMswte B Telephone number 1869 E 23RD STREET (917) 776-5555 City or town, state or province, country, and ZIP or foreign postal code C If exemption application is pending , check here ► BROOKLYN, NY 11229 G Check all that apply. XD Initial return initial return of a former public charity D 1. Foreign organizations, check here Final return Amended return 2. Foreign organizations meeting the 85% test, Address chan ge Name chan ge check here and attach computation H Check type of organization: [X Section 501(c)(3) exempt private foundation E If private foundation status was terminated Section 4947(a)( 1 ) nonexem pt charitable trust Other taxable private foundation under section 507(b)(1)(A), check here I Fair market value of all assets at end of year J Accounting method: MX Cash 0 Accrual F If the foundation is in a 60-month termination (from Part II, col. -

Ottenheimer Award Goes to Rabbi Diamond Mickey Heideman Is
Published by the Jewish Community of Louisville, Inc. MAY 27, 2016 Y 19 IYARwww.jewishlouisville.org 5776 Y Community 1 INSIDE Male HS Honors Carl Bensinger STORY ON PG. 17 DC Federation Fetes Emily Benovitz STORY ON PG. 14 Communit■ ■ y FRIDAY VOL. 41, NO. 09 19 IYAR 5776 MAY 27, 2016 Please Join Us for the 2016 JCL Annual Meeting June 15 CELEBRATE OUR AWARD WINNERS INSIDE Carl Bensinger STORIES ON PG. *** Emily Benovitz STORY ON PG. *** Blanche B. Lewis W. Cole Young Josepth J. Kaplan Young Julie E. Linker Community Ron and Marie Arthur S. Kling Award Ottenheimer Award Leadership Award Leadership Award Relations Young Abrams Volunteer Brian Tabler Rabbi Chester B. Diamond Becky Swansburg Laurence Nibur Leadership Award of the Year See story, page 6. See story, this page. see story, page 3. See story, page 3. Derek Pugh Mickey Heideman See story, page 6. See story, this page. Rabbi Chester Diamond PHOTO BY LOUIS J. MOSESON Elsie P. Judah Award Joseph Fink Community Stacey Marks Stuart Pressma Student Ottenheimer Joe Rothstein Service Scholarship Ellen Faye Garmon Award Nisenbaum Award Leadership Award Story available at Jacob Finke Abigail Geller Laina Meyerowitz Daniel Hemmer www.jewishlouisville.org www.jewishlouisville.org See story, page 16. See story, page 15. www.jewishlouisville.org Award Goes to Rabbi Diamond by Shiela Steinman Wallace Editor he Jewish Community of Lou- isville’s prestigious Blanche B. Ottenheimer Award is presented T annually to an individual who Stuart Pressma Student Stuart Pressma Student Stuart Pressma Student Stuart Pressma Student Tony Levitan Awards Tony Levitan Awards has had significant impact for good in Leadership Award Leadership Award Leadership Award Leadership Award Daniel Levine Hillary Reskin Louisville and often throughout the Jesse Hymes Audrey Nussbaum Bradley Schwartz Emily Schulman see story page 16 see story page 16 www.jewishlouisville.org www.jewishlouisville.org www.jewishlouisville.org www.jewishlouisville.org state and beyond. -

By Joseph Scutts
Trump’s plan • Operation Embrace • Arboreal delights The Jerusalem R RFEBRUARY 10, 2020 eporCOVERING ISRAEL, THE MIDDLE EAST & THE JEWISHt WORLD Portrait of a sculptor Varda Yoran’s storied journey took her from China to the US via Israel 7415 המחיר בישראל: ₪21.00 באילת: ₪17.90 NY & North NJ $4.00 Elsewhere in US $5.50 New from Gefen The Longer, Shorter Path • By Moshe “Bogie” Ya’alon [A] must-read for anyone “interested in understanding Israel, Zionism, and the security establishment. —Maj. Gen. (Ret.) Amos Yadlin, Executive Director, Institute for National Security Studies, Tel Aviv University Navigates the paradox of Israel’s strategic predicament with the Palestinians by offering a practical approach that will preserve both Israel’s Jewish and democratic character and the faint but flickering hope for an eventual peace. —Robert Satloff, Executive Director, “ Washington Institute for Near East Policy HC | 536pp | 9789657023006 | $29.95 | 128 NIS Look for us on | Available at Amazon, Steimatzky, Pomeranz, selected bookstores, and Gefen Books NJ ([email protected]). The Jerusalem VIEWPOINTS 6 Planning for a (much) more crowded Israel R by Ben Dansker Report 7 The Wagner Syndrome by Jane Biran 25 All roads lead to Jerusalem by Shoshana Tita 37 Uniqueness and unity in Israel by Ynon Reiner ISRAEL COURTESY VARDA YORAN VARDA COURTESY 16 Leaps of faith by Amotz Asa-El 20 The Jewish journey to Hebron by Bradley Martin 26 Coming alive at the Dead Sea by Robert Hersowitz 28 On the trail by Wendy Blumfield 32 Hydroponic gardening in Baka -

Contentscontents SOME WORDS of ENCOURAGEMENT
CONTENTSContents SOME WORDS OF ENCOURAGEMENT .........................................3 IMPRESSIONS OF A JOURNEY ABROAD.......................................9 THE ROOT OF THE RIGHTEOUS WILL GIVE............................... 16 THE LATEST ACHIEVEMENTS OF OUR TEACHER AND RAV.. ....22 JTHE GAON AND TZADDIK RABBI YITZCHAK KADURI ZT”L....... 24 IS THERE WATER ABOVE THE FIRMAMENT? .............................29 THE NEED TO STUDY THE LAWS OF MODESTY ........................ 30 JERUSALEM HAS LOST A JEWEL ................................................34 THE LESSON OF SELF-SACRIFICE AND ITS IMPORTANCE FOR THE FUTURE.................................................................................36 THE HILLOULA OF RABBI HAIM PINTO ZT”L ............................... 40 A TZADDIK HAS LEFT THIS WORLD THE GAON RABBI NISSIM REBIBO ZATZAL............................................................................46 THE PASSING OF RABBI NATHAN BOKOBZA..............................48 THE DISASTER EFFECTS OF CARELESSNESS..........................49 THE ADMOR OF SATMAR HARAV MOSHE TEITELBAUM ZT”L....50 A FEW GOLDEN RULES................................................................52 DVOR TORAH IN HEBREW...........................................................54 UNDER AEGIS OF RABBI DAVID HANANIA PINTO CHLITA ISRAEL - ASHDOD The Pinto “OROT HAÏM OU MOSHE” REHOV HA-ADMOUR MI-BELZ 41/6 • ASHDOD • ISRAËL Associations around TEL: +972 88 856 125 • FAX: +972 88 563 851 ISRAEL - JERUSALEM the world, along with KOLLEL “OROTH HAIM OU MOSHE” KOLLEL “MISHKAN BETSALEL” Rabbi David Hanania Pinto YÉCHIVAT “NEFESH HAIM” REHOV BAYIT VAGAN 97 • JERUSALEM • ISRAEL Shlita, send you their best TEL: +972 26 433 605 • FAX: +972 26 433 570 U.S.A - CHEVRAT PINTO wishes for an exceptional new 8 MORRIS ROAD - SPRING VALLEY • NY 10977 • U.S.A TEL: 1 845 426 1276 • FAX: 1 845 426 1149 year 5767. Shana Tova! May PARIS - ORH HAÏM VÉMOSHÉ 11, RUE DU PLATEAU - 75019 PARIS • FRANCE we all be inscribed in the TEL: 01 42 08 25 40 - FAX: 01 42 08 50 85 LYON - HEVRAT PINTO Book of Life. -

The Impossibility of Obfuscation with Auxiliary Input Or a Universal Simulator
The Impossibility of Obfuscation with Auxiliary Input or a Universal Simulator Nir Bitansky∗ Ran Canettiy Henry Cohnz Shafi Goldwasserx Yael Tauman Kalai{ Omer Panethk Alon Rosen∗∗ February 9, 2014 Abstract In this paper we show that the existence of general indistinguishability obfuscators conjectured in a few recent works implies, somewhat counterintuitively, strong impossibility results for virtual black box obfuscation. In particular, we show that indistinguishability obfuscation for all circuits implies: • The impossibility of average-case virtual black box obfuscation with auxiliary input for any circuit family with super-polynomial pseudo-entropy. Such circuit families include all pseudo-random function families, and all families of encryption algorithms and randomized digital signatures that generate their required coin flips pseudo-randomly. Impossibility holds even when the auxiliary input depends only on the public circuit family, and not the specific circuit in the family being obfuscated. • The impossibility of average-case virtual black box obfuscation with a universal simulator (with or without any auxiliary input) for any circuit family with super-polynomial pseudo-entropy. These bounds significantly strengthen the impossibility results of Goldwasser and Kalai (STOC 2005). arXiv:1401.0348v3 [cs.CR] 13 Feb 2014 ∗Tel Aviv University, [email protected]. Supported by an IBM Ph.D. Fellowship, and the Check Point Institute for Information Security. yBoston University and Tel Aviv University, [email protected]. Supported by the Check Point Institute for Information Security, an NSF EAGER grant, and an NSF Algorithmic Foundations grant 1218461. zMicrosoft Research, One Memorial Drive, Cambridge, MA 02142, [email protected]. xMIT and the Weizmann Institute of Science, [email protected]. -

November-December 2012 • Cheshvan-Tevet 5773
SINAI NEWS A bi-monthly publication Issue 12, Volume 1 November-December 2012 • Cheshvan-Tevet 5773 Hannah Halaska, In this issue Zoe Styler and Jordan Arenzon Rabbi’s Corner 2 enjoy sufganiyot at the 2011 Latke Reflections, From the Cantor 3 Lunch. Search Committee Join us Lifelong Jewish Learning 4-9 December 9th! Women at Sinai 10 Brotherhood 11 Shabbat & Holiday Schedule Green Team 12 Shabbat Vayera Shabbat Vayeshev Genesis 18:1 - 22:24 Genesis 37:1 - 40:23 Chesed 13 Nov 2 Shabbat Service 6:15 pm Dec 7 Shabbat Service 6:15 pm Nov 3 Torah Study 8 am Dec 8 Torah Study 8 am Social Action Committee 13-14 Morning Minyan 9:30 am Morning Minyan 9:30 am Shabbat Chayei Sara Shabbat Miketz Israel Committee 15 Genesis 23:1 - 25:18 Genesis 41:1 - 44:17 Nov 9 Rockin’ Shabbat Service 6:15 pm Dec 14 Chanukah Shabbat Service 6:15 pm Congregational Dinner 7:15 pm My Sinai 16 Dec 15 Torah Study 8 am Nov 10 Torah Study 8 am Morning Minyan 9:30 am Morning Minyan 9:30 am “Scene” at Sinai 16-18 Shabbat Vayigash Shabbat Toldot Genesis 44:18 - 47:27 Genesis 25:19 - 28:9 Dec 21 Shabbat Service 6:15 pm What’s Happening 19 Nov 16 Shabbat Service 6:15 pm Dec 22 Torah Study 8 am Nov 17 Torah Study 8 am Morning Minyan 9:30 am Supporting Sinai 20-21 Morning Minyan 9:30 am Shabbat Vayechi Shabbat Vayetzei Genesis 47:28 - 50:26 November Calendar 22 Genesis 28:10 - 32:3 Dec 28 Shabbat Service 6:15 pm Nov 23 Shabbat Service 6:15 pm December Calendar 23 Dec 29 Torah Study 8 am Nov 24 Torah Study 8 am Morning Minyan 9:30 am Morning Minyan 9:30 am In the Sinai Family 24 Shabbat Vayishlach Genesis 32:4 - 36:43 Those We Remember 25 Nov 30 Shabbat Service 6:15 pm Dec 1 Torah Study 8 am Contributions 26-28 Morning Minyan 9:30 am Rabbi David B. -

2013 WRJ OR AMI PROGRAMMING AWARDS Or Ami Committee Co-Chair: Sandy Adland, Canton, OH Co-Chair: Linda P
2013 WRJ OR AMI PROGRAMMING AWARDS Or Ami Committee Co-Chair: Sandy Adland, Canton, OH Co-Chair: Linda P. Zoll, Houston, TX Natalie Berhumoglu, Bay Shore, NY Sharon K. Benoff, Newtown, PA Edith Caplan, Fremont, CA Gold Or Ami Award Winners Be The Match – National Bone Marrow Registry Temple Chai Sisterhood, Long Grove, IL, www.templechai.org/programs/sisterhood Project Chair: Lisa Hartman After learning that a bone marrow match can save a life, a match is more likely to come from a donor with similar genetic ancestry, and matches are desperately needed in the Jewish community, this sisterhood held a bone marrow drive along with the organization Be The Match to find a match for a local Jewish girl in need of a transplant. The drive registered 150 people. Child Trafficking in Portland Beth Israel Sisterhood, Portland, OR, www.bethisrael-pdx.org/community/sisterhood Project Chair: Daphna Stadig The city of Portland is a place where child sex trafficking is particularly rampant. Members organized a public forum to learn about the problem and its scope, identify who is at risk, and find out what can be done to help. Speakers included Congresswoman Suzanne Bonamici and representatives from organizations that combat trafficking and aid its victims. Judaica for Joplin WRJ Midwest District, www.wrjmidwest.org Project Chair: Julia Ziev In response to the 2011 Joplin, MO tornado, this District (which does not include Joplin) asked its members to supply four Joplin Jewish families with needed Judaica items including: Shabbat candlesticks, challah covers, mezuzot, kiddush cups, seder plates, chanukiyot, and candles for Shabbat and Chanukah. -

The Random Oracle Methodology, Revisited∗
The Random Oracle Methodology, Revisited∗ Ran Canettiy Oded Goldreichz Shai Halevix August 6, 2002 Abstract We take a critical look at the relationship between the security of cryptographic schemes in the Random Oracle Model, and the security of the schemes that result from implementing the random oracle by so called \cryptographic hash functions". The main result of this paper is a negative one: There exist signature and encryption schemes that are secure in the Random Oracle Model, but for which any implementation of the random oracle results in insecure schemes. In the process of devising the above schemes, we consider possible definitions for the notion of a \good implementation" of a random oracle, pointing out limitations and challenges. Keywords: Correlation Intractability, • Cryptography (Encryption and Signature Schemes, The Random Oracle model); • Complexity Theory (diagonalization, application of CS-Proofs). ∗Extended abstract has appeared in the Proc. of the 30th ACM Symp. on Theory of Computing (STOC), pages 209{218, 1998. yIBM Watson, P.O. Box 704, Yorktown Height, NY 10598, USA. E-mail: [email protected] zDepartment of Computer Science, Weizmann Institute of Science, Rehovot, Israel. E-mail: [email protected]. Work done while visiting LCS, MIT. Partially supported by DARPA grant DABT63- 96-C-0018. xIBM Watson, P.O. Box 704, Yorktown Height, NY 10598, USA. E-mail: [email protected] 1 Contents 1 Introduction 2 1.1 The Setting . 2 1.1.1 The Random Oracle Model . 3 1.1.2 Implementing an ideal system . 3 1.2 Our Results . 5 1.2.1 Correlation intractability . -

Curriculum Vitae
Curriculum Vitae Oded Goldreich January 1, 2021 Current Position: Professor of Computer Science, Weizmann Institute of Science, Rehovot, Israel. Incumbent of the Meyer W. Weisgal Professorial Chair. Personal Data: Born in Israel on February 4th, 1957. Married to Dana Ron. Citizenship: Israeli. Passport number 20663357. Research Interests and Expertise: • Main current focus: Randomness and Computation. In particular, Property Testing, Pseudorandomness, and Probabilistic Proof Systems. • Additional interest: Complexity Theory. • Past expertise: Foundations of Cryptography. • Additional past interest: Distributed Computation. Degrees B.A. in Computer Science (Cum Laude), Technion, Israel. October 1977 through June 1980. M.Sc. in Computer Science, Technion, Israel. October 1980 through February 1982. Thesis ad- viser: Prof. S. Even. Thesis Title: \On the Complexity of Some Edge Testing Problems". D.Sc. in Computer Science, Technion, Israel. March 1982 through June 1983. Thesis adviser: Prof. S. Even. Thesis Title: \On the Security of Cryptographic Protocols and Cryptosystems". i Contents 1 Research Contributions 1 2 Expository Contributions 21 2.1 Books and Lecture Notes . 21 2.2 Survey articles . 23 3 Graduate Student Supervision 26 3.1 Graduate students who completed D.Sc./Ph.D. 26 3.2 Graduate students who completed M.Sc. 28 3.3 Mentoring . 30 4 Postdoctoral fellows hosted 30 5 Teaching Experience 30 5.1 Undergraduate Courses . 30 5.2 Graduate Courses . 31 5.3 Short Courses and Lecture Series . 31 6 Positions 31 7 Fellowships and Honors 32 8 Short Visits 33 9 Special Invitations 34 9.1 Invited Speaker at Conferences . 34 9.2 Participation in Workshops (by invitation) . 34 9.3 Speaker in Special Colloquiums . -

Studies in Secure Multiparty Computation and Applications
Studies in Secure Multiparty Computation and Applications Thesis for the Degree of DOCTOR of PHILOSOPHY by Ran Canetti Department of Computer Science and Applied Mathematics The Weizmann Institute of Science Submitted to the Scientic Council of The Weizmann Institute of Science Rehovot Israel June Revised March i Acknowledgements First a very sp ecial thanks is due to Oded Goldreich my advisor On top of b eing an exp ert on exp erts and a dear friend he is a devoted advisor far b eyond the ordinary Oded has the sp ecial prop erty of always searching for the crux of any matter and disgustedly ridding himself of the rest Once he sets his mind to a particular goal he is thoroughly and uncompromisingly dedicated This together with his sharpness his p eculiar sense of humor and his natural go o dheartedness make him a remarkable p erson indeed My interaction with Oded deeply aected my approach to research and to life in general Time and again his unconventional approach rst lo oks o dd and after some thought it b ecomes clear that his is the direct simple and natural approach It also b ecomes totally unclear how I ever thought otherwise His colorful and creative feedback on my writing style has made each one of my drafts a museum piece His feedback also spiced up my fearful anticipation of their return which has happ ened at an amazing sp eed I am also thankful for the practical training I received in the art of do dging ying sho es During my years of study I have made some sp ecial acquaintances from whom I have learned a lot Among these