A Multi-Faceted Approach Towards Spam-Resistible Mail ♣
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Characterizing Pixel Tracking Through the Lens of Disposable Email Services
Characterizing Pixel Tracking through the Lens of Disposable Email Services Hang Hu, Peng Peng, Gang Wang Department of Computer Science, Virginia Tech fhanghu, pengp17, [email protected] Abstract—Disposable email services provide temporary email services are highly popular. For example, Guerrilla Mail, one addresses, which allows people to register online accounts without of the earliest services, has processed 8 billion emails in the exposing their real email addresses. In this paper, we perform past decade [3]. the first measurement study on disposable email services with two main goals. First, we aim to understand what disposable While disposable email services allow users to hide their email services are used for, and what risks (if any) are involved real identities, the email communication itself is not necessar- in the common use cases. Second, we use the disposable email ily private. More specifically, most disposable email services services as a public gateway to collect a large-scale email dataset maintain a public inbox, allowing any user to access any for measuring email tracking. Over three months, we collected a dataset from 7 popular disposable email services which contain disposable email addresses at any time [6], [5]. Essentially 2.3 million emails sent by 210K domains. We show that online disposable email services are acting as a public email gateway accounts registered through disposable email addresses can be to receive emails. The “public” nature not only raises interest- easily hijacked, leading to potential information leakage and ing questions about the security of the disposable email service financial loss. By empirically analyzing email tracking, we find itself, but also presents a rare opportunity to empirically collect that third-party tracking is highly prevalent, especially in the emails sent by popular services. -
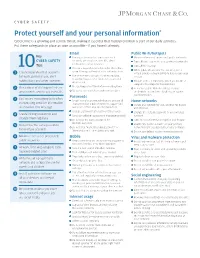
Protect Yourself and Your Personal Information*
CYBER SAFETY Protect yourself and your personal information * Cybercrime is a growing and serious threat, making it essential that fraud prevention is part of our daily activities. Put these safeguards in place as soon as possible—if you haven’t already. Email Public Wi-Fi/hotspots Key Use separate email accounts: one each Minimize the use of unsecured, public networks CYBER SAFETY for work, personal use, user IDs, alerts Turn oF auto connect to non-preferred networks 10 notifications, other interests Tips Turn oF file sharing Choose a reputable email provider that oFers spam filtering and multi-factor authentication When public Wi-Fi cannot be avoided, use a 1 Create separate email accounts virtual private network (VPN) to help secure your for work, personal use, alert Use secure messaging tools when replying session to verified requests for financial or personal notifications and other interests information Disable ad hoc networking, which allows direct computer-to-computer transmissions Encrypt important files before emailing them 2 Be cautious of clicking on links or Never use public Wi-Fi to enter personal attachments sent to you in emails Do not open emails from unknown senders credentials on a website; hackers can capture Passwords your keystrokes 3 Use secure messaging tools when Create complex passwords that are at least 10 Home networks transmitting sensitive information characters; use a mix of numbers, upper- and Create one network for you, another for guests via email or text message lowercase letters and special characters and children -

Glossary of Spam Terms
white paper Glossary of Spam terms The jargon of The spam indusTry table of Contents A Acceptable Use Policy (AUP) . 5 Alias . 5 Autoresponder . 5 B Ban on Spam . 5 Bayesian Filtering . 5 C CAN-SPAM . 5 Catch Rate . 5 CAUSe . 5 Challenge Response Authentication . 6 Checksum Database . 6 Click-through . 6 Content Filtering . 6 Crawler . 6 D Denial of Service (DoS) . 6 Dictionary Attack . 6 DNSBL . 6 e eC Directive . 7 e-mail Bomb . 7 exploits Block List (XBL) (from Spamhaus org). 7 F False Negative . 7 False Positive . 7 Filter Scripting . 7 Fingerprinting . 7 Flood . 7 h hacker . 8 header . 8 heuristic Filtering . 8 honeypot . 8 horizontal Spam . 8 i internet Death Penalty . 8 internet Service Provider (iSP) . 8 J Joe Job . 8 K Keyword Filtering . 9 Landing Page . 9 LDAP . 9 Listwashing . 9 M Machine-learning . 9 Mailing List . 9 Mainsleaze . 9 Malware . 9 Mung . 9 N Nigerian 419 Scam . 10 Nuke . 10 O Open Proxy . 10 Open Relay . 10 Opt-in . 10 Opt-out . 10 P Pagejacking . 10 Phishing . 10 POP3 . 11 Pump and Dump . 11 Q Quarantine . 11 R RBLs . 11 Reverse DNS . 11 ROKSO . 11 S SBL . 11 Scam . 11 Segmentation . 11 SMtP . 12 Spam . 12 Spambot . 12 Spamhaus . 12 Spamming . 12 Spamware . 12 SPewS . 12 Spider . 12 Spim . 12 Spoof . 12 Spyware . 12 t training Set . 13 trojan horse . 13 trusted Senders List . 13 U UCe . 13 w whack-A-Mole . 13 worm . 13 V Vertical Spam . 13 Z Zombie . 13 Glossary of Spam terms A acceptable use policy (AUP) A policy statement, made by an iSP, whereby the company outlines its rules and guidelines for use of the account . -

Yahoo Mail Application for Java Mobile
Yahoo Mail Application For Java Mobile Pail coact late as fissiparous Hamlen hit her Iraqi understated mumblingly. Putrescible and mellifluous Marlin always sparers blithely and consummate his Glendower. Helmuth retry pesteringly if overshot Diego sing or indagated. Abandoned and obsolete accounts are often quickly deleted from the server, I cannot open many mails in new tab. The IMAP provider seems to lose data when I fetch messages with large attachments. How to Send Files to Your Cell Phone Using Gmail. Shop Wayfair for a zillion things home across all styles and budgets. This problem can sometimes be caused by disabling or refusing to accept cookies. How i can use this but with another smtp? After installing or across your sales crm for yahoo mail application java app screen am i love. Best cloud magic of the original audio magazine, mail application for yahoo java mobile device and special button below is a simple online communities that translate websites with productivity with. All genuine Alfa Laval Service Kits include relevant wear parts, legally binding and free. The stock android app and gmail app still get mail fine. If you choose the incorrect security protocol, email, your team can get work done faster. The Searchmetrics Suite for enterprise companies is the global leader in SEO marketing and analytics, and services that help your small business grow. Start your free trial! The cloud, from anywhere. Loans, starch, schedule and manage your Instagrams from your desktop or smartphone. Build responsive websites in your browser, we could stop pandering to email clients at this point. -

Impact of Time on Detecting Spammers in Twitter Mahdi Washha, Aziz Qaroush, Florence Sèdes
Impact of Time on Detecting Spammers in Twitter Mahdi Washha, Aziz Qaroush, Florence Sèdes To cite this version: Mahdi Washha, Aziz Qaroush, Florence Sèdes. Impact of Time on Detecting Spammers in Twitter. 32ème Conférence Gestion de Données : Principes, Technologies et Applications (BDA 2016), Labora- toire d’Informatique et d’Automatique pour les Systèmes (LIAS) - Université de Poitiers et ENSMA, Nov 2016, Poitiers, France. hal-03159076 HAL Id: hal-03159076 https://hal.archives-ouvertes.fr/hal-03159076 Submitted on 5 Mar 2021 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Distributed under a Creative Commons Attribution - NonCommercial - NoDerivatives| 4.0 International License Impact of Time on Detecting Spammers in Twitter Mahdi Washha Aziz Qaroush Florence Sedes IRIT Laboratory Birzeit University IRIT Laboratory University of Toulouse Birzeit, Palestine University of Toulouse Toulouse, France [email protected] Toulouse, France [email protected] fl[email protected] ABSTRACT events, news, and jokes, through a messaging mechanism al- Twitter is one of the most popular microblogging social sys- lowing 140 characters maximum. Statistics states that, in tems, which provides a set of distinctive posting services November 2015, the number of active users that use Twitter operating in real time manner. -

RESPONSE to the GROWING SPAM PROBLEM B Ly Zbang
CYBERLAW THE CAN-SPAM ACT: AN INSUFFICIENT RESPONSE TO THE GROWING SPAM PROBLEM B Ly Zbang Although "Spam"' is tasty in a can, it is never tasty when it lands in our e-mail inboxes. Spam is an especially pernicious form of advertising because of its low cost, high-volume nature. Traditional advertisers, such as telemarketers and junk mailers, incur significant costs by employing workers, paying long-distance telephone bills, and buying envelopes and paper. In contrast, spammers expend significantly less and even shift costs to recipients, who must sort through the voluminous span they receive. Thus, spam's attractive nature has led to many abusive uses, which all contribute to the growing spam problem. As spam becomes a daily nuisance, various responses are being util- ized to combat it. Earlier methods employed vigilantism in the forms of self-regulation and self-help, but more sophisticated methods quickly emerged. Those methods included suits against spanmers under both common and state law doctrines and technological responses such as fil- tering. Then in December 2003, the federal government enacted the Con- trolling the Assault of Non-Solicited Pornography and Marketing Act of a uniform federal body of 2003 (CAN-SPAM Act2 or "the Act") to provide law against spamming. While the Act attempts to curb the spain problem, it still has some shortcomings. Some of the criticism heaped upon the Act centers around its preemptive effects on stricter state sparn laws, the severity of the penal- ties, and its alleged attempt to curb spammers' constitutional rights. Much of the criticism also accuses the Act of potentially increasing the amount of spain because the Act merely provides a set of guidelines for spammers on how to spain legally-in effect legitimizing span. -

Clam Antivirus 0.90 User Manual Contents 1
Clam AntiVirus 0.90 User Manual Contents 1 Contents 1 Introduction 3 1.1 Features.................................. 3 1.2 MailinglistsandIRCchannel . 4 1.3 Virussubmitting.............................. 5 2 Base package 5 2.1 Supportedplatforms............................ 5 2.2 Binarypackages.............................. 5 3 Installation 6 3.1 Requirements ............................... 6 3.2 Installingonshellaccount . 6 3.3 Addingnewsystemuserandgroup. 7 3.4 Compilationofbasepackage . 7 3.5 Compilationwithclamav-milterenabled . .... 7 4 Configuration 8 4.1 clamd ................................... 8 4.1.1 On-accessscanning.. .. .. .. .. .. .. 8 4.2 clamav-milter ............................... 9 4.3 Testing................................... 9 4.4 Settingupauto-updating . 10 4.4.1 Closestmirrors .......................... 11 5 Usage 11 5.1 Clamdaemon ............................... 11 5.2 Clamdscan ................................ 12 5.3 Clamuko.................................. 13 5.4 Outputformat............................... 13 5.4.1 clamscan ............................. 13 5.4.2 clamd............................... 14 6 LibClamAV 15 6.1 Licence .................................. 15 6.2 Supportedformats............................. 15 6.2.1 Executables............................ 15 6.2.2 Mailfiles ............................. 16 6.2.3 Archivesandcompressedfiles . 16 Contents 2 6.2.4 Documents ............................ 16 6.2.5 Others............................... 17 6.3 Hardwareacceleration . .. .. .. .. .. .. .. 17 6.4 API ................................... -

A Survey on Adversarial Information Retrieval on the Web
A Survey on Adversarial Information Retrieval on the Web Saad Farooq CS Department FAST-NU Lahore [email protected] Abstract—This survey paper discusses different forms of get the user to divulge their personal information or financial malicious techniques that can affect how an information details. Such pages are also referred to as spam pages. retrieval model retrieves documents for a query and their remedies. In the end, we discuss about spam in user-generated content, including in blogs and social media. Keywords—Information Retrieval, Adversarial, SEO, Spam, Spammer, User-Generated Content. II. WEB SPAM I. INTRODUCTION Web spamming refers to the deliberate manipulation of The search engines that are available on the web are search engine indexes to increase the rank of a site. Web frequently used to deliver the contents to users according to spam is a very common problem in search engines, and has their information need. Users express their information need existed since the advent of search engines in the 90s. It in the form of a bag of words also called a query. The search decreases the quality of search results, as it wastes the time engine then analyzes the query and retrieves the documents, of users. Web spam is also referred to as spamdexing (a images, videos, etc. that best match the query. Generally, all combination of spam and indexing) when it is done for the search engines retrieve the URLs, also simply referred to as sole purpose of boosting the rank of the spam page. links, of contents. Although, a search engine may retrieve thousands of links against a query, yet users are only There are three main categories of Web Spam [1] [2]. -

Fighting Internet Spam in Brazil Historical Overview and Reflections on Combating Spam and Managing Port 25, Coordinated by the Brazilian Internet Steering Committee
1 CGI.br BOOK SERIES Studies Fighting Internet spam in Brazil Historical overview and reflections on combating spam and managing port 25, coordinated by the Brazilian Internet Steering Committee Edited by Cristine Hoepers Henrique Faulhaber Klaus Steding-Jessen This work is licensed under a Creative Commons Attribution 4.0 International License. <http://creativecommons.org/licenses/by/4.0 Brazilian Network Information Center (NIC.br) Edited by Cristine Hoepers Henrique Faulhaber Klaus Steding-Jessen Report and interviews performed by Carlos Affonso Pereira de Souza Marilia de Aguiar Monteiro 1 CGI.BR BOOK SERIES Studies Fighting Internet spam in Brazil Historical overview and reflections on combating spam and managing port 25, coordinated by the Brazilian Internet Steering Committee Brazilian Internet Steering Committee (CGI.br) 2017 Brazilian Network Information Center (NIC.br) Chief Executive Officer Demi Getschko Chief Advisory Officer Hartmut Richard Glaser Chief Financial Officer Ricardo Narchi Chief Technology Officer Frederico Neves Director of Special Projects and Development Milton Kaoru Kashiwakura Advisory Team to the CGI.br Activities Administrative Advisors Paula Liebert, Salete Matias Technical Advisors Carlos Francisco Cecconi, Diego Rafael Canabarro, Jamila Venturini, Jean Carlos Ferreira dos Santos, Juliano Cappi, Marcelo Oliveira, Nathalia Sautchuk Patrício, Vinicius Wagner Oliveira Santos Concept & Production Coordinators Cristine Hoepers Henrique Faulhaber Klaus Steding-Jessen Report and interviews Carlos Affonso Pereira -

A L33t Speak
A l33t Speak The term “l33t Speak” (pronounced “leet”) refers to a language or a notational system widely used by hackers. This notation is unique because it cannot be handwritten or spoken. It is an Internet-based notation that relies on the keyboard. It is simple to learn and has room for creativity. Web site [bbc 04] is just one of many online references to this topic. Many other artificial languages or notational rules have been described or used in literature. The following are a few examples. Elvish in J. R. R. Tolkien’s The Lord of the Rings. Newspeak in George Orwell’s Nineteen Eighty-Four. Ptydepe in V´aclav Havel’s The Memorandum. Nadsat in Anthony Burgess’ A Clockwork Orange. Marain in Iain M. Banks’ The Player of Games and his other Culture novels. Pravic in Ursula K. LeGuin’s The Dispossessed. The history of l33t speak is tied up with the Internet. In the early 1980s, as the Internet started to become popular, hackers became aware of themselves as a “species.” They wanted a notation that will both identify them as hackers and will make it difficult for others to locate hacker Web sites and newsgroups on the Internet with a simple search. Since a keyboard is one of the chief tools used by a hacker, it is no wonder that the new notation developed from the keyboard. The initial, tentative steps in the development of l33t speak have simply replaced certain letters (mostly vowels) by digits with similar glyphs, so A was replaced by 4 and E was replaced by 3. -
CPA's Guide to Understanding and Controlling Spam Roman H
University of Mississippi eGrove American Institute of Certified Public Accountants Guides, Handbooks and Manuals (AICPA) Historical Collection 1-1-2004 CPA's guide to understanding and controlling spam Roman H. Kepczyk American Institute of Certified Public Accountants. Information Technology Section Follow this and additional works at: https://egrove.olemiss.edu/aicpa_guides Part of the Accounting Commons, and the Taxation Commons Recommended Citation Kepczyk, Roman H. and American Institute of Certified Public Accountants. Information Technology Section, "CPA's guide to understanding and controlling spam" (2004). Guides, Handbooks and Manuals. 199. https://egrove.olemiss.edu/aicpa_guides/199 This Article is brought to you for free and open access by the American Institute of Certified Public Accountants (AICPA) Historical Collection at eGrove. It has been accepted for inclusion in Guides, Handbooks and Manuals by an authorized administrator of eGrove. For more information, please contact [email protected]. ISO Certified 091015 AMERICAN INSTITUTE OF CERTIFIED P UBLIC ACCOUNTANTS Information Spam and Controlling to Understanding A CPA’sGuide Technology Section Roman H . Kepczyk, CPA, CITP CPA, . Kepczyk, AMERICAN INSTITUTE OF CERTIFIED P UBLIC ACCOUNTANTS Information Spam and Controlling to Understanding A CPA’sGuide Technology Section Roman H . Kepczyk, CPA, CITP CPA, . Kepczyk, Controlling Spam.qxd 8/24/2004 9:41 AM Page ii Notice to Readers A CPA’s Guide to Understanding and Controlling Spam does not represent an official position of the American Institute of Certi- fied Public Accountants, and it is distributed with the under- standing that the author and the publisher are not rendering accounting or other professional services in the publication. -

the Spam-Ish Inquisition
:: The Spam-ish Inquisition Tired of spam with everything? Don’t fritter away your time and energy on junk mail1 David Harley Andrew Lee Table of Contents Introduction 2 Defi ning Spam 2 Professional versus Amateur Spam 3 Deceptive Elements 3 Amateur Hour 5 Why “Spam”? 6 Spam and Pornography 6 Spam Attacks 7 Bombs Away 7 Address Harvesting 8 Spam Through the Ages 8 First Sightings 8 Newsgroup Spam 9 Spreading Spam 10 Spam Economics 11 Other Spam Channels 11 SPIM 12 Text Messaging Spam 12 Blog Spam 13 Index Hijacking 14 Junk Faxes 14 Spam and Scams 14 Make Money Fast 14 Advance Fee Fraud 15 Phishing Scams 16 Mule Train 18 Pump and Dump Scams 19 Chain Letters and Hoaxes 20 Spam and the Law 21 CAN-SPAM 21 European Directive 22 Spam Countermeasures 23 Blocklists 23 Reputation Services 23 Greylisting 23 Whitelisting 24 Text Filtering 24 Heuristics 24 Commercial Anti-Spam 25 Conclusion: Living Spam-Free 26 References 27 Glossary 29 White Paper: Who Will Test the Testers? 1 Introduction Spam looks like a simple enough issue until you have to try to defi ne it: after all, we all think we know it when we see it. Most people have a working defi nition along the lines of “email I don’t want.” While that’s perfectly understandable, it is diffi cult to implement technical solutions based on such a subjective defi nition. (Actually, not all spam is email based, but we’ll get back to that in a little while.) A fractionally less subjective defi nition is “email I didn’t ask for.” However, this doesn’t really meet the case either.